Modern software systems integrate with Git far more often than most developers realize.
CI/CD pipelines clone repositories during builds.
Dev platforms analyze code from remote repositories.
Automation systems pull repositories based on user input.
Developer tools create pull requests, fetch branches, and sync forks.
In many of these systems, Git operations are executed programmatically through libraries such as simple-git, nodegit, or direct shell commands.
This creates a subtle but dangerous security boundary.
Git is not just a version control system.
It is also a command execution interface.
And if user input reaches Git commands without strict validation, the result can be command injection and full remote code execution.
The discovery of CVE-2026-28292, a critical remote code execution vulnerability in the widely used simple-git Node.js library, demonstrates exactly how fragile these boundaries can be.
In that case, a single case-sensitivity mismatch inside a regex filter allowed attackers to bypass a security control and enable Git’s dangerous ext:: transport protocol, ultimately executing arbitrary shell commands.
But the deeper lesson goes far beyond a single vulnerability.
It reveals how many Git integrations rely on assumptions about input validation that do not actually hold in practice.
This article explores:
how command injection occurs in Git integrations
why security filters frequently fail
how CVE-2026-28292 exposed structural weaknesses
how developers can design safer Git automation systems
And perhaps most importantly, why modern code review tools must focus on security reasoning instead of stylistic suggestions.
Because the real value of code review is not catching naming conventions.
It is catching the one vulnerability that could compromise an entire system before it ships.
Why Git Integrations Are High-Risk
When developers think about command injection, they usually think about shell commands such as:
Git integrations rarely look this dangerous.
A typical implementation might look harmless:
But Git itself executes external processes.
Internally, this code becomes:
If the repoUrl or additional Git arguments are influenced by user input, the attacker may control how Git executes.
That is the boundary attackers exploit.
Where Command Injection Happens in Git Workflows
Most Git integrations expose several input surfaces.
These are the most common ones:
Input Surface | Risk |
|---|---|
Repository URLs | malicious protocols |
Custom arguments | configuration injection |
Branch names | command expansion |
File paths | path traversal |
Environment variables | execution context manipulation |
The most dangerous scenario occurs when multiple inputs combine into one command execution path.
Example Attack Surface
Consider a service that allows users to analyze repositories.
If repo is attacker-controlled, the attacker may attempt to pass a malicious Git transport.
Example payload:
Git interprets this as:
Which results in full system compromise.
The Dangerous Git Feature: ext:: Protocol
Git’s ext:: transport allows arbitrary commands to execute as part of repository access.
Example:
Git internally executes:
This feature exists for legitimate custom transport mechanisms.
But when exposed to user input, it becomes a command execution primitive.
How CVE-2026-28292 Bypassed the Protection
The simple-git library attempted to block protocol overrides.
Security check:
The filter expected configuration keys such as:
But the regex was case-sensitive.
Git configuration keys are case-insensitive.
This meant attackers could bypass the filter with:
Once the override passed through, Git allowed ext:: transport.
Which allowed arbitrary command execution.
Attack Chain Visualization
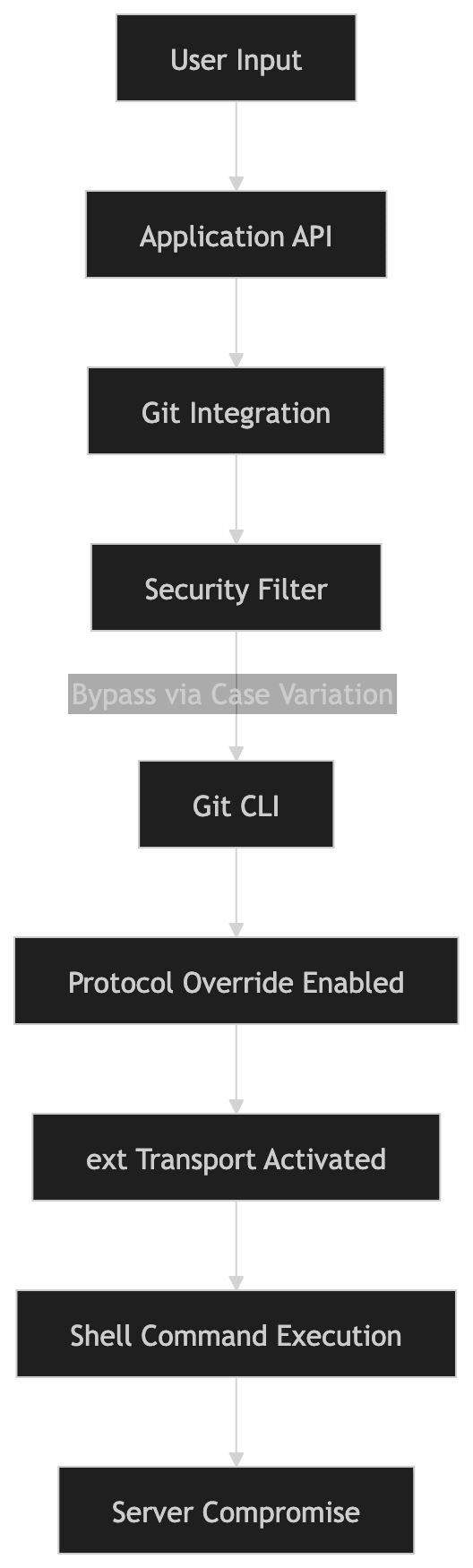
This chain demonstrates why seemingly small validation mistakes can escalate into critical vulnerabilities.
Why Security Filters Fail
Developers often rely on filters such as:
regex checks
string comparisons
simple blacklists
But these approaches frequently fail because the system being protected behaves differently than the filter expects.
Example mismatches include:
Filter Assumption | System Behavior |
|---|---|
case-sensitive check | case-insensitive system |
exact string match | normalized input |
blocked keyword | alternate encoding |
sanitized path | symbolic links |
CVE-2026-28292 is a perfect example of this pattern.
The regex assumed lowercase.
Git did not.
Safer Architecture for Git Integrations
Instead of relying on fragile filters, a safer design is to treat Git execution as a restricted interface.
The safest model follows three rules.
1. Strict Protocol Allowlist
Allow only known safe protocols.
Example:
This prevents dangerous protocols like:
2. Remove User-Controlled Arguments
Never allow users to pass raw Git arguments.
Bad example:
Safe alternative:
Arguments should always be defined by the application.
3. Run Git in a Sandboxed Environment
Even with validation, Git commands should not run with full system privileges.
Safer architecture:
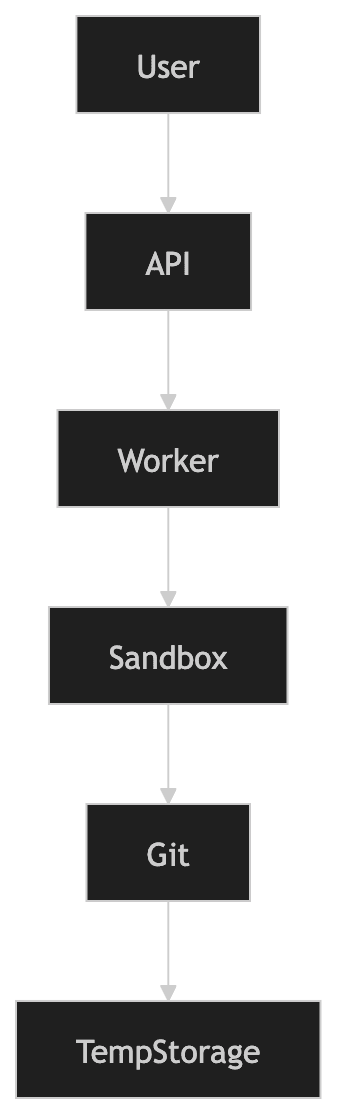
Use:
containers
restricted permissions
temporary environments
This limits the blast radius of any potential vulnerability.
Hardening Git Execution
Additional defensive controls include:
Disable dangerous protocols
Restrict environment variables
Git commands should not inherit untrusted environment variables.
Use ephemeral execution environments
Containers or short-lived VMs significantly reduce persistence risk.
Secure Implementation Example
A hardened Git clone workflow:
Security guarantees:
protocol validation
no user arguments
controlled execution environment
Why Code Review Often Misses These Bugs
Most code reviews focus on readability and maintainability.
Example comments:
rename variable
simplify loop
remove duplicate code
Important improvements, but not the reason review gates exist.
The real value of code review is catching rare but catastrophic failures.
The vulnerability behind CVE-2026-28292 existed despite multiple prior patches.
The code looked correct.
The regex looked reasonable.
Yet the security control failed.
During internal research, CodeAnt AI’s code reviewer flagged the regex because it was protecting a case-insensitive system with a case-sensitive check.
That small observation led directly to the discovery of a critical RCE vulnerability affecting millions of installations.
This is exactly where AI code review is starting to change the landscape.
Instead of focusing on style issues, advanced analysis tools can reason about semantic inconsistencies in security logic.
And those inconsistencies are where many of the most dangerous vulnerabilities hide.
Defensive Security Checklist
When building Git integrations:
Validate repository URLs
Allow only HTTPS or SSH.
Disallow custom Git arguments
Never allow raw CLI options from users.
Disable dangerous protocols
Explicitly block ext::.
Sandbox execution
Run Git in containers or isolated environments.
Normalize inputs
Convert values to canonical forms before validation.
Audit dependencies
Ensure Git libraries are patched.
Conclusion: The Kind of Bug Code Review Must Catch
The vulnerability behind CVE-2026-28292 did not require advanced exploitation techniques.
It did not rely on memory corruption or cryptographic flaws.
It was a subtle logic mismatch hiding inside a validation rule.
A security control assumed lowercase input.
The system it protected did not.
That single mismatch created a bypass large enough to enable remote code execution across millions of installations.
And that is exactly the type of issue code review systems are supposed to catch.
Not style violations.
Not naming suggestions.
But the rare security flaw that could compromise an entire application before it reaches production.
During internal research, CodeAnt AI’s code reviewer surfaced this flaw by reasoning about the relationship between the filter and the underlying Git behavior, leading to the discovery of CVE-2026-28292.
That kind of detection represents a shift in how automated code review is evolving.
From surface-level feedback toward identifying deep security issues that traditional tools miss.
Because when a single uppercase string can bypass a security control, the difference between a helpful code review tool and a critical one comes down to a simple question:
Can it find the bug nobody else has noticed yet?
FAQs
What is command injection in Git integrations?
Why was CVE-2026-28292 considered critical?
Are Git integrations inherently dangerous?
How can developers safely allow user-provided repository URLs?
Why are AI-assisted code review tools becoming important for security?