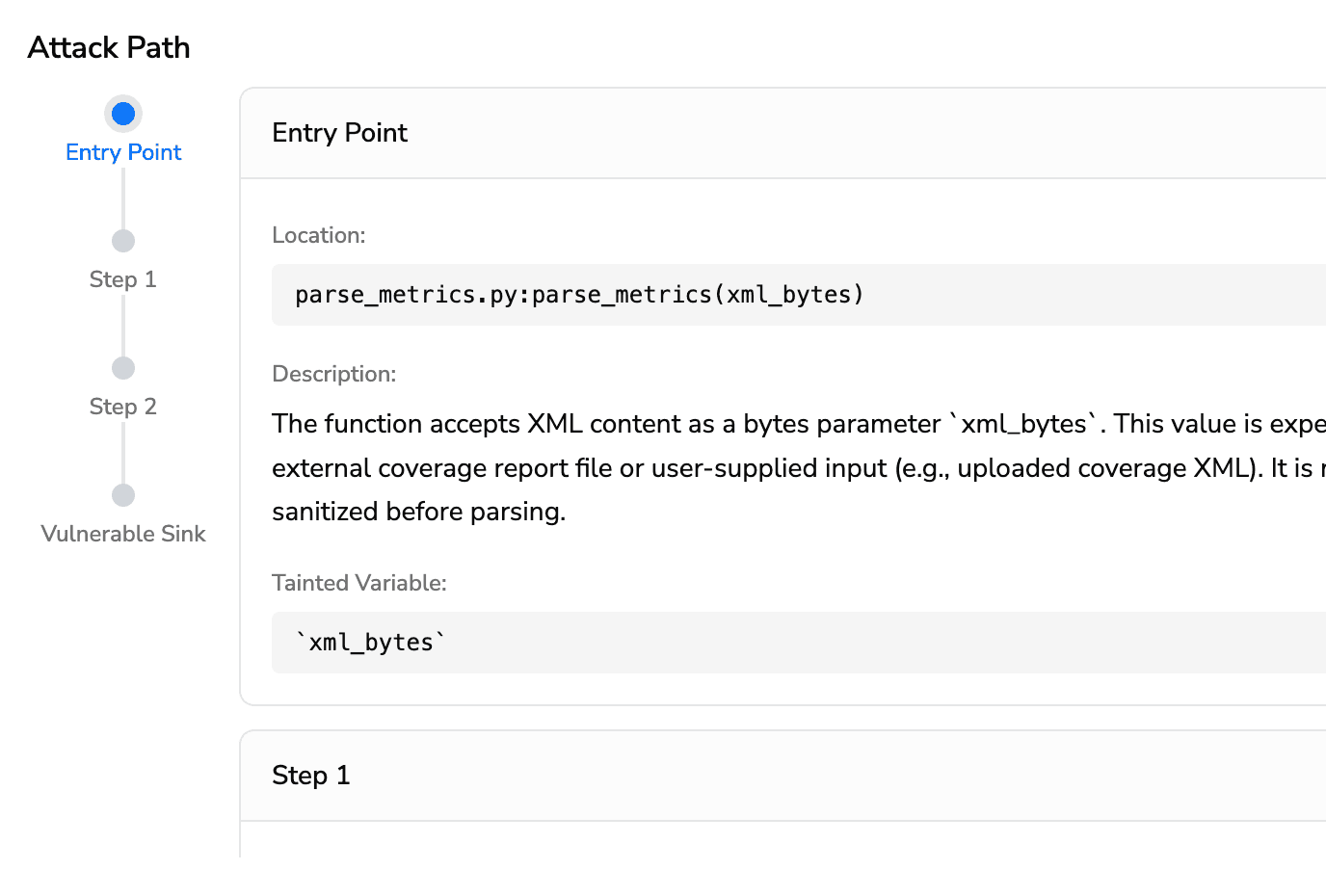
Attack Path Analysis
Trusted by Startups to Fortune 500
Know the Exploit Before the Attacker Does
From entry point to exploit, every step mapped
See exactly where untrusted data enters and where it causes damage — no file hunting.
Every hop, function call, and vulnerable sink shown in one clear flow.
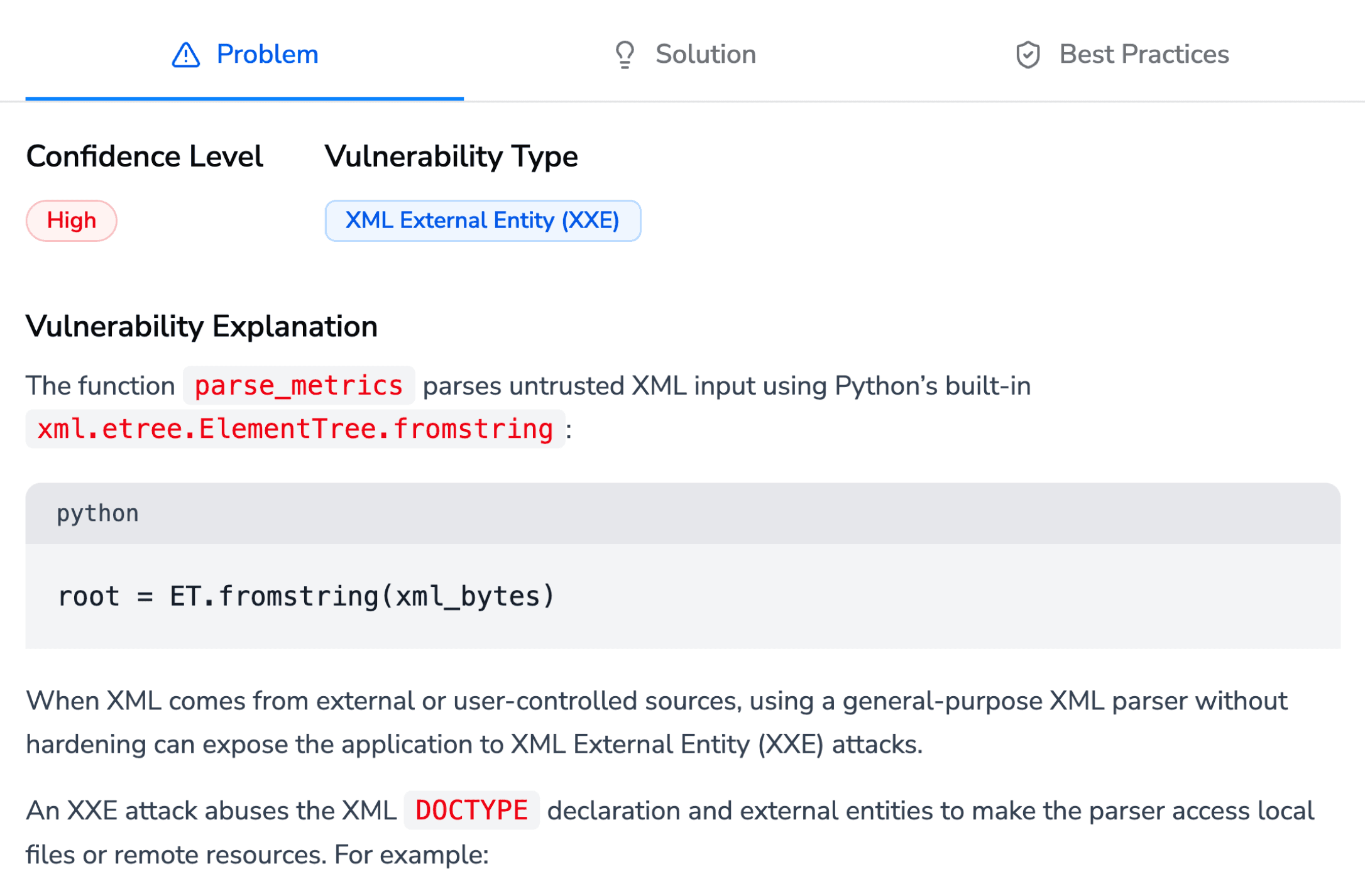
AI Security Analysis
Know the vulnerability type, confidence, and blast radius, instantly
Understand what an attacker can actually do with it, in plain English.
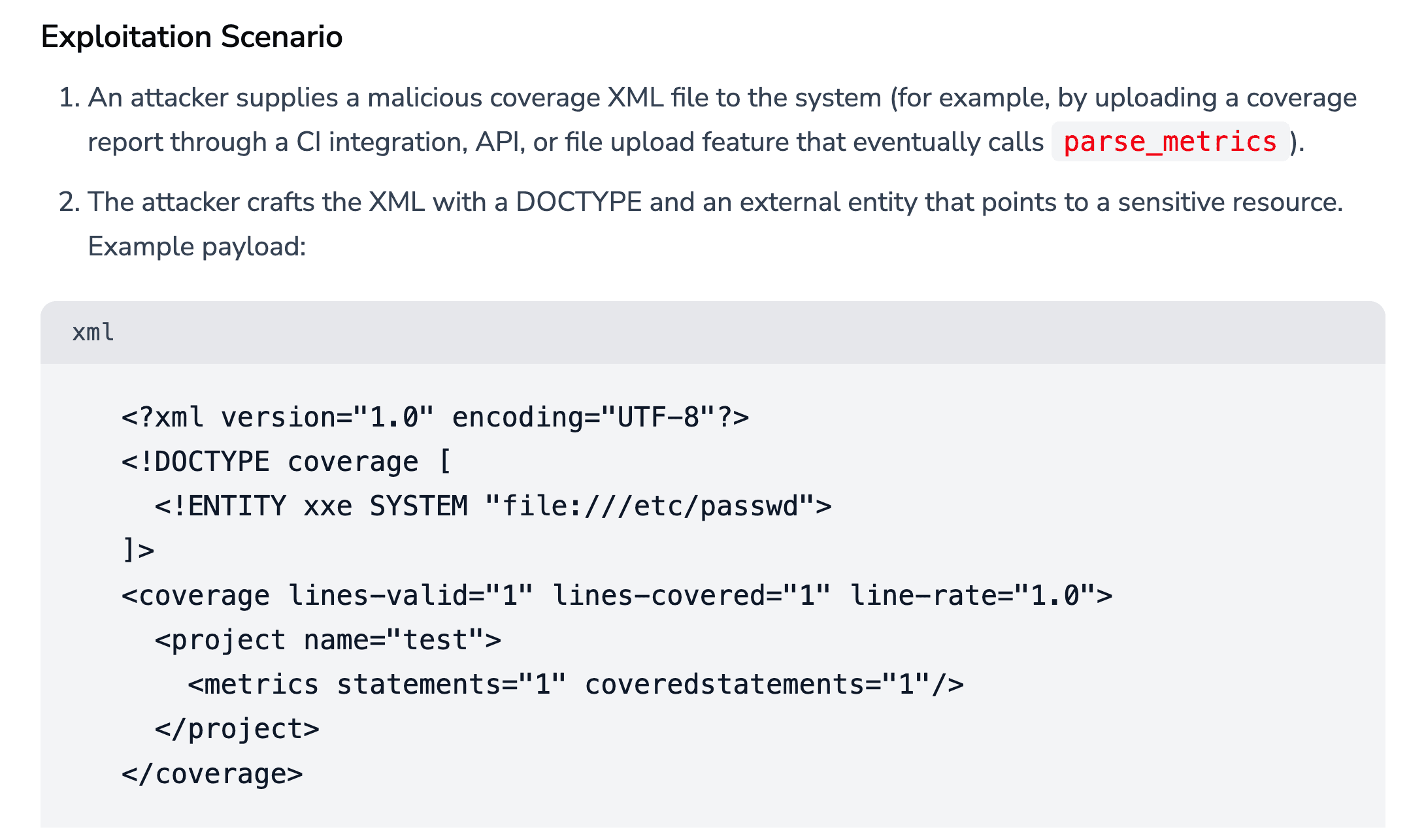
Real-World Exploit Scenarios
See a step-by-step attacker playbook, from payload injection to data exfiltration.
Patch with full context, not assumptions.
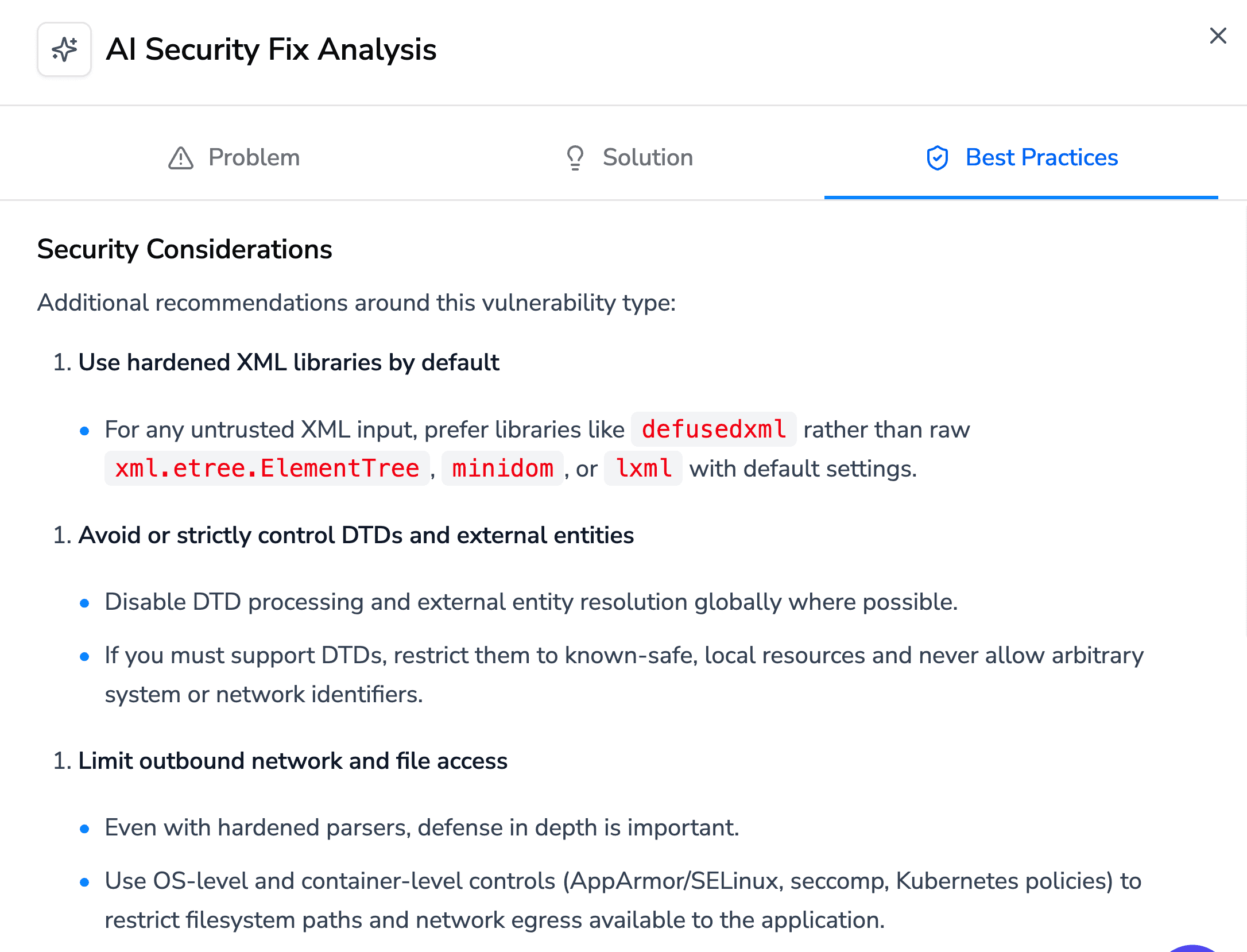
Built-in Security Best Practices
Every fix comes with the "why", secure libraries, dependency tips, and proven patterns.
One fix teaches the whole team, not just the developer who wrote the bug.
Fix It, Don't Flag It
Generates production-ready remediation, hardened parsers, sanitized inputs, secure rewrites, not just a warning comment.
See a clean before/after diff inline; go from vulnerable to patched in minutes, not sprints.

Why Best Teams Love CodeAnt AI
FAQs
How is Attack Path different from a regular SAST finding?
Does it work across multiple files and functions?
What vulnerability types are covered?
Can I see the fix alongside the path?
Does it integrate with our existing PR workflow?