Walk into any mid-size or enterprise engineering organization and you will find a familiar pattern: SonarQube for code quality, Snyk or Checkmarx for security scanning, and a manual process (or a separate tool) for code review. Each tool has its own dashboard, its own alert stream, its own pricing contract, and its own set of findings that developers must context-switch between. This is not a design, it is an accumulation. Each tool was adopted to solve a specific problem, and nobody went back to ask whether the problems could be solved by one platform instead of three.
Tool consolidation in application security replaces these fragmented toolchains with a unified platform that combines code review, code quality, and security scanning in a single workflow. This guide makes the business case for consolidation, identifies the three functions most amenable to it, and provides an evaluation framework for deciding whether consolidation is right for your team. For a broader view of the SAST landscape, see the full SAST tools comparison.
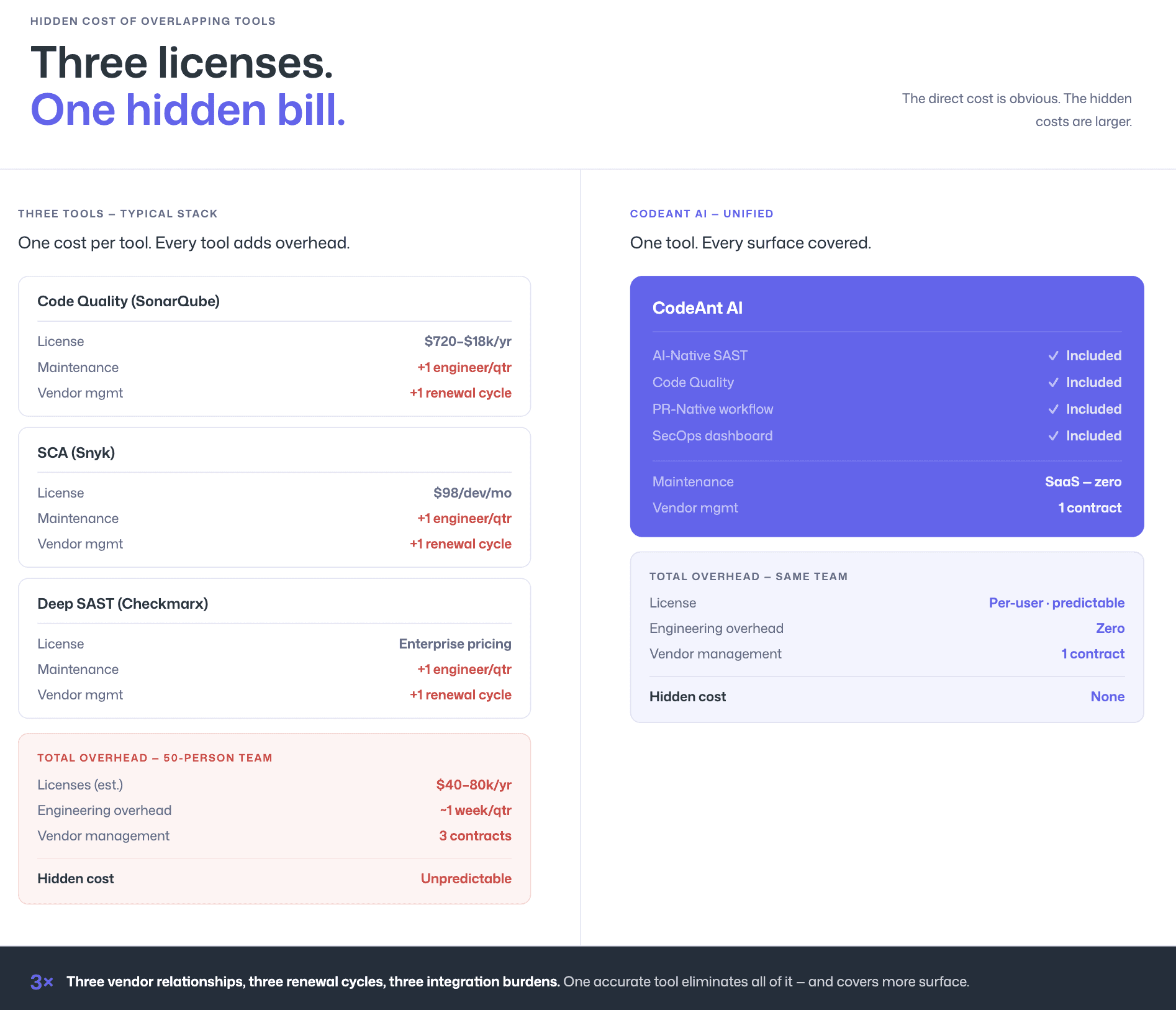
The Hidden Cost of Running 3–5 Overlapping Security Tools
The direct cost of multiple tools is obvious: three license contracts instead of one. But the hidden costs are larger and harder to measure.
Context-switching destroys developer productivity
When a developer opens a pull request, they may receive findings from a code review tool, a code quality scanner, and a security scanner, in three different formats, across three different interfaces. Each tool has its own severity taxonomy, its own prioritization logic, and its own remediation workflow. Gartner’s Innovation Insight for Application Security Posture Management highlights this exact problem: as security tools and responsibilities span multiple groups, visibility into the overall security posture becomes fragmented, complicating efforts to assess, measure, and prioritize risk.
Overlapping findings create duplicate noise
SonarQube and a dedicated SAST tool will both flag the same SQL injection. The developer sees two alerts for one vulnerability, from different tools, with different severity labels, requiring different triage workflows. This is not twice the coverage; it is twice the noise. Teams that run multiple overlapping scanners consistently report higher alert fatigue than teams that run a single, accurate tool.
Procurement and vendor management compound costs
Three tools mean three vendor relationships, three renewal cycles, three contract negotiations, three security reviews during procurement, and three integration maintenance burdens. For a 50-person engineering team, the procurement overhead alone can consume a full workweek per quarter from the engineering manager or VP Engineering who owns the toolchain.
Inconsistent coverage creates false confidence
Each tool covers a slightly different surface. SonarQube catches code quality issues and basic SAST findings.
Snyk covers SCA and some SAST
Checkmarx covers deep SAST but not code quality
Nobody has a clear picture of what is covered and what falls through the gaps between tools.
The assumption is “more tools = more coverage.” The reality is often “more tools = more gaps in the spaces between tools.”
What “Tool Consolidation” Actually Means in AppSec
Tool consolidation does not mean running one scanner that does everything poorly. It means identifying the functions that overlap across your current toolchain and replacing them with a single platform that covers all of those functions at equivalent or better depth.
The consolidation opportunity in application security is driven by a market-wide shift. Gartner’s ASPM research identifies fragmented tooling as a core challenge: organizations struggle to prioritize security issues that should be addressed holistically when findings are scattered across multiple unconnected tools. The ASPM market, projected to grow at over 30% annually, exists precisely because enterprises need to unify the output of their fragmented security stacks.
But tool consolidation is different from ASPM. ASPM is an orchestration layer that sits on top of your existing tools and correlates their output. Consolidation replaces the tools themselves. For teams running 3–5 overlapping scanners, consolidation eliminates the need for an orchestration layer by reducing the toolchain to a single source of truth.
The three functions most amenable to consolidation are AI code review, code quality analysis, and security scanning. Most engineering teams currently run separate tools for each.
The 3 Functions You Can Consolidate
AI Code Review (Replacing Manual Review Burden)
Code review is the most time-intensive quality gate in modern development. Senior engineers often spend 20–30% of their time reviewing pull requests for:
Correctness
Maintainability
Security
Style compliance
Much of this work is repetitive pattern-matching. AI can automate:
Dead code detection
Common anti-patterns
Error handling gaps
Obvious security flaws
AI code review tools like CodeAnt AI handle this first pass automatically, adding inline comments directly in the PR. This does not replace human review, it improves it. Engineers focus on architecture and business logic instead of null checks and string concatenation mistakes.
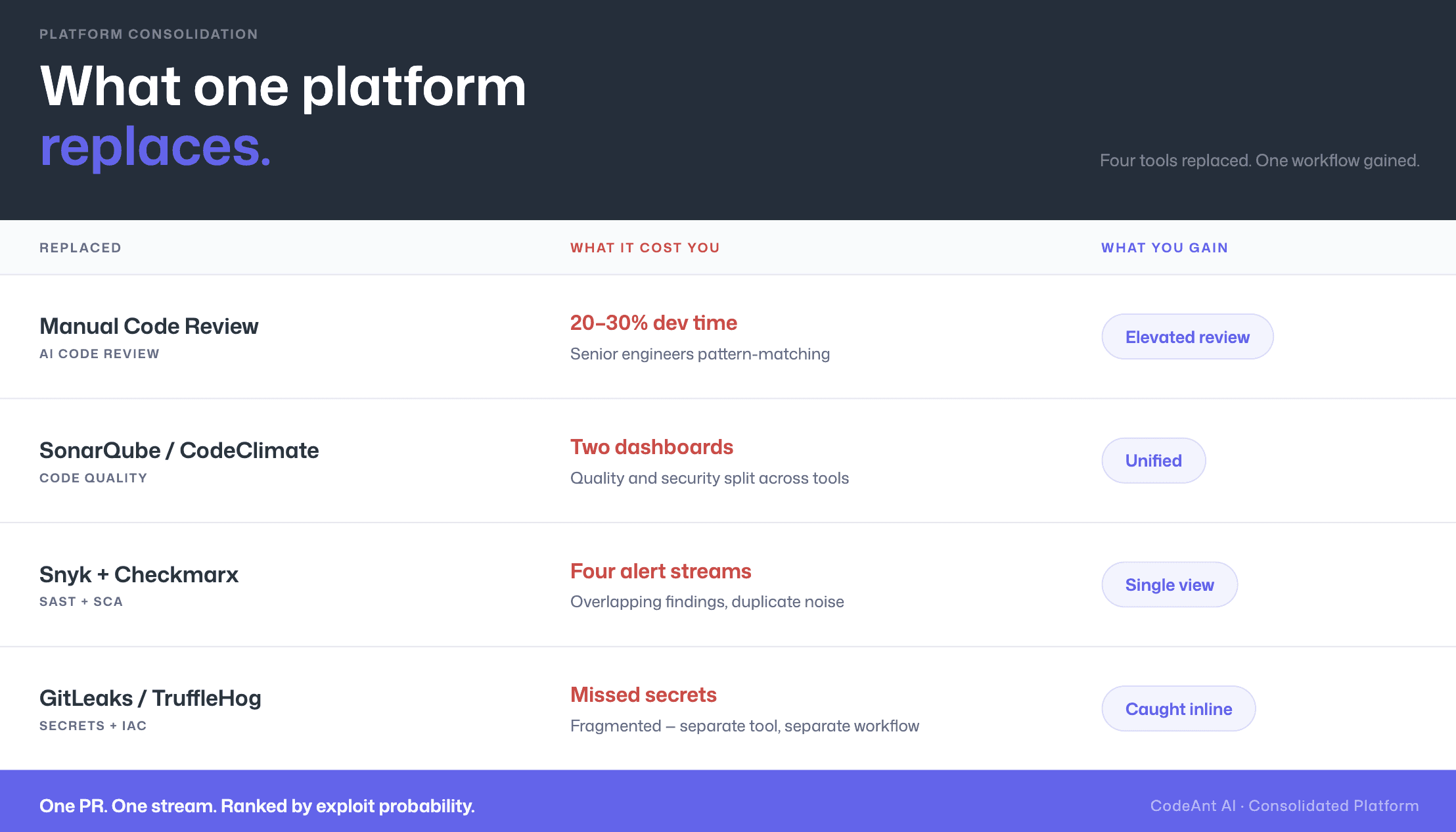
Consolidation becomes even more important as AI coding assistants like GitHub Copilot and Cursor increase code volume. More AI-generated code means more review burden, and AI-generated code often carries subtle security risks that reviewers may overlook.
A platform that combines AI code review and security scanning evaluates quality and vulnerabilities together, instead of requiring a second, separate security scan later.
If your team relies on manual review or a standalone review tool, this function can be consolidated.
Code Quality Analysis (Replacing SonarQube/CodeClimate)
Code quality tools track:
The consolidation opportunity exists because quality analysis and security scanning:
Operate on the same codebase
Use similar AST and data-flow analysis
Produce findings consumed in the same workflow
Running them separately creates multiple dashboards and fragmented triage.
A consolidated platform delivers code quality and security findings together, inline in the pull request. Developers evaluate both in a single prioritized view instead of switching between SonarQube and a separate security tool.
If you are running SonarQube primarily for quality tracking, this function can be absorbed into a unified platform.
Security Scanning: SAST + SCA + Secrets (Replacing Snyk/Checkmarx)
Security scanning typically includes:
SAST: first-party code vulnerabilities
SCA: third-party dependency CVEs
Secrets detection: hardcoded keys and tokens
IaC scanning: infrastructure misconfigurations
Many teams use separate tools for each. The result:
Multiple alert streams
Duplicate findings
Fragmented prioritization
Consolidated platforms combine all four into a single scan and a single PR workflow.
Developers see:
Application vulnerabilities
Dependency risks
Exposed credentials
Infrastructure issues
All in one view. Prioritized by exploit risk, not by which scanner produced them.
This is where consolidation delivers the biggest impact. The question shifts from “Which tool found this?” to “What is the highest-risk issue in this PR?”
That is the right question.
Evaluation Framework for Consolidation
What to Gain (Cost, Speed, Developer Adoption)
1. Cost reduction
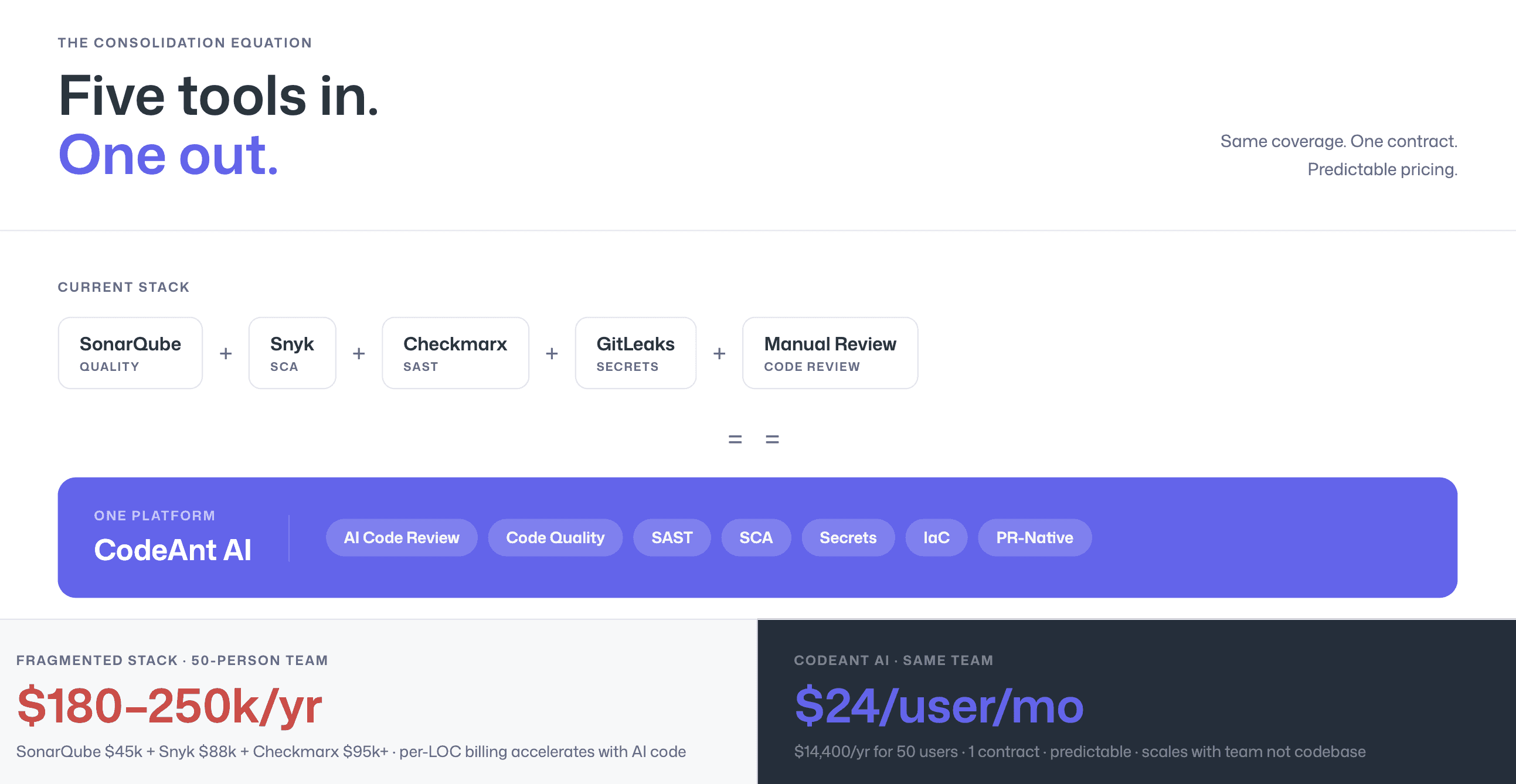
The direct savings are substantial. SonarQube is priced per instance based on lines of code, Enterprise Edition at 5 million LOC lists at approximately $35,000/year, and many mid-to-large companies exceed 10 million lines, pushing costs considerably higher.
Add SonarQube’s Advanced Security add-on for SAST depth and the annual bill can approach $70,000.
Snyk Enterprise for a 50-developer team runs $35,000–$50,000/year based on negotiated per-developer pricing.
A code review tool or automation layer adds another $10,000–$20,000.
For a 50-person engineering team, the fragmented toolchain can easily total $80,000–$140,000 annually in licensing alone, before accounting for procurement overhead, integration maintenance, and the infrastructure costs of self-hosted tools like SonarQube Server.
2. Speed
A single scan per PR replaces three sequential or parallel scans. Findings arrive in one set of inline comments instead of three separate notification channels. Triage happens once, not three times. The time from “PR opened” to “all findings reviewed” compresses from hours to minutes.
3. Developer adoption
This is the most important gain. Developers are more likely to engage with one tool that provides all feedback in one place than with three tools that each provide a partial view. When findings from code review, code quality, and security all appear as inline comments in the same PR, with consistent severity labels, consistent prioritization, and consistent fix suggestions, developers build a single habit rather than managing three separate workflows.
Forrester’s application security research consistently emphasizes that developer experience is the primary driver of AppSec tool adoption, teams that consolidate into developer-friendly workflows see measurably higher remediation rates than teams that force developers to navigate multiple dashboards.
4. Reduced alert fatigue
With three tools, a developer may see 15 findings per PR, 5 from each tool, with 3 of those being duplicates flagged by multiple scanners. A consolidated platform deduplicates automatically. The same PR might surface 9 unique findings in a single prioritized list, with the highest-risk issues at the top. Fewer alerts, higher signal, faster triage.
What to Watch For (Depth Tradeoffs, Vendor Lock-in)
1. Detection depth tradeoffs
The risk of consolidation is that a single platform may not match the depth of the best-in-class tool in every category. SonarQube’s code quality analysis is deeper than most security-first tools provide. Checkmarx’s SAST detection depth may exceed what a consolidated platform offers for specific language/framework combinations.
Before consolidating, run a parallel scan to verify that the consolidated tool’s detection in each category meets your minimum requirements.
Specifically: scan the same codebase with both your current tools and the consolidated alternative, then compare findings in three dimensions.
First, check coverage: does the consolidated tool catch everything your current tools catch?
Second, check precision: does it produce fewer false positives?
Third, check for net-new findings: does it catch vulnerabilities your current tools missed?
If the consolidated tool matches or exceeds your current stack across all three dimensions, the depth tradeoff concern is resolved. If it falls short in a specific category, quantify the gap and decide whether the consolidation benefits outweigh the detection delta.
2. Vendor lock-in
Moving from three vendors to one creates a single point of dependency. Mitigate this by ensuring the consolidated platform uses standard output formats (SARIF for security findings, standard quality metrics) that allow you to switch tools in the future without losing historical data. Also verify that the platform supports your current development stack, GitHub, GitLab, Azure DevOps, or Bitbucket, without requiring migration.
3. Organizational inertia
Different teams may own different tools. The security team owns Checkmarx; the platform team owns SonarQube; developers own the code review tool. Consolidation requires cross-functional alignment on a single tool, which requires executive sponsorship and a clear business case.
How CodeAnt AI Combines All Three
CodeAnt AI is purpose-built for consolidation. It combines three functions that most teams currently run separate tools for:
AI code review
code quality analysis
security scanning (SAST + SCA + secrets detection + IaC scanning)
… in a single PR-native platform. This replaces the common enterprise stack of SonarQube + Snyk/Checkmarx + manual code review with one tool, one dashboard, and one pricing contract.
AI code review
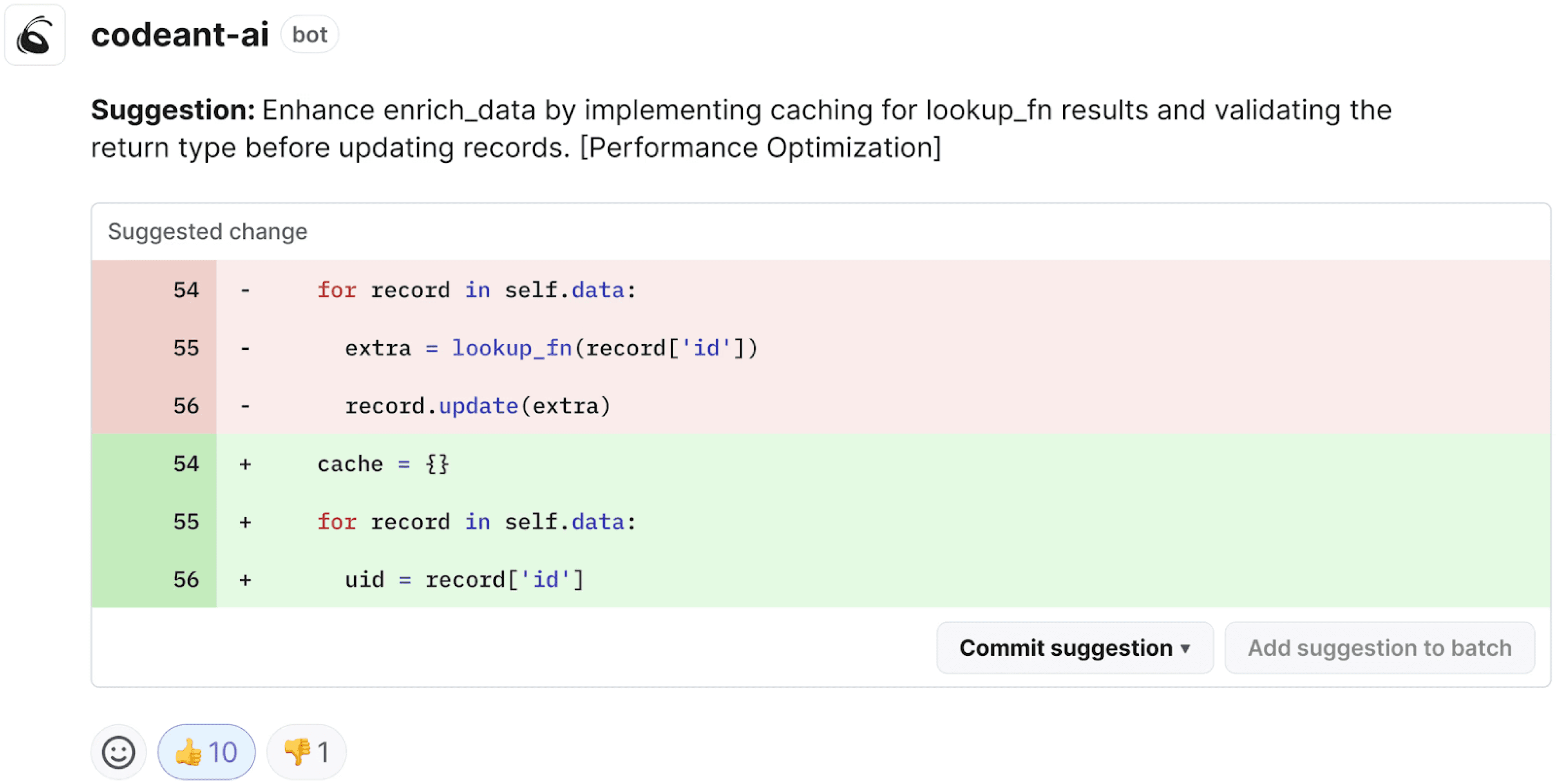
CodeAnt AI reviews every pull request line-by-line, providing inline comments on correctness, maintainability, security, and style. This automates the initial review pass that senior developers currently perform manually, freeing them for higher-value architectural review.
Code quality
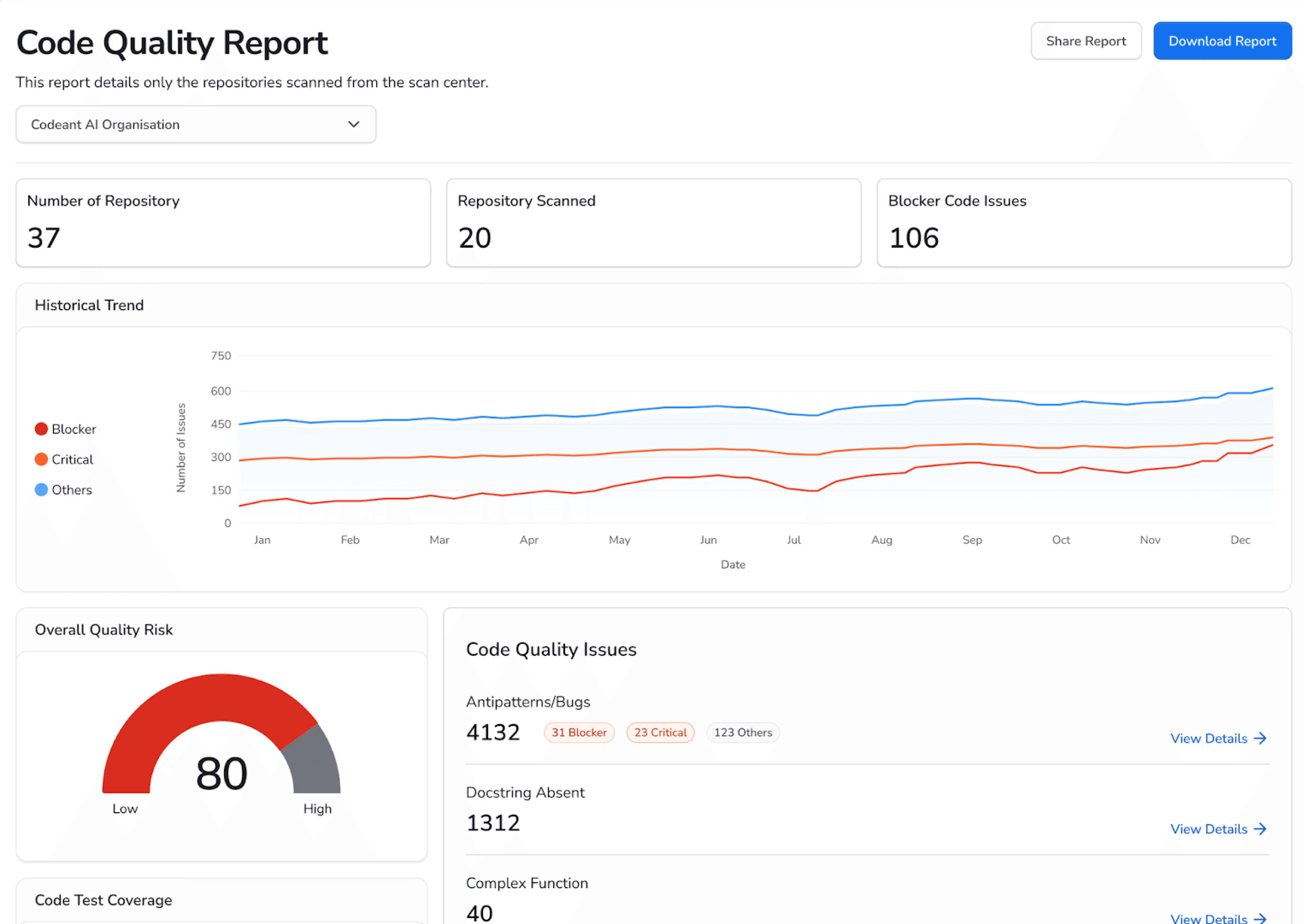
Complexity analysis, duplication detection, and dead code identification, the core metrics teams currently track in SonarQube, are built into every scan. Findings appear alongside security findings in the same PR, prioritized together.
Security scanning
SAST, SCA, secrets detection, and IaC scanning run in a single pass. Every security finding includes the full attack path, EPSS exploit probability scoring, Steps of Reproduction (the exact conditions to trigger the vulnerability), and a one-click AI-generated fix the developer can apply directly in the PR.
PR-native delivery across all four platforms
Every finding, code review, quality, security, appears as an inline comment in the pull request, across GitHub, GitLab, Azure DevOps, or Bitbucket. One interface, one set of findings, one triage workflow.
CodeAnt AI is already delivering consolidation results at enterprise scale. Commvault’s 800-developer team replaced their fragmented review workflow with CodeAnt AI and reduced time-to-first-review-comment from 3.5 days to under one minute, with 25% of their 17,000+ merge requests now reviewed entirely by AI (full case study). A VP of IT at a mid-market retail company noted on Gartner Peer Insights that CodeAnt AI “tightened our pull request workflow and reduced review back and forth” with “inline comments [that] are clear and actionable,” after evaluating CodeRabbit and GitHub as alternatives.
Conclusion: Consolidate or Keep Paying the Tax
Running three overlapping tools is not stronger security. It is duplicated cost, duplicated alerts, and duplicated workflow friction.
Tool consolidation works when one platform matches or exceeds the depth of your current stack while delivering findings in a single developer-native workflow. That means fewer dashboards, fewer duplicate alerts, fewer vendor contracts, and higher fix rates.
The only way to evaluate consolidation properly is side-by-side testing.
Run a parallel scan. Compare coverage. Compare false positives. Compare developer experience. If one platform replaces three without sacrificing depth, the decision becomes obvious.
Start consolidating: Explore CodeAnt AI’s unified platform, or start a 14-day trial and measure the difference on your own repositories.
FAQs
What is SAST tool consolidation?
Is it safe to replace SonarQube and Snyk with one tool?
Does consolidating security tools reduce detection depth?
How much can companies save by consolidating SAST tools?
When should a team consider consolidating its AppSec stack?















