Modern developer tools rely heavily on Git automation.
CI/CD pipelines clone repositories.
Developer platforms analyze codebases.
Internal tools fetch repositories dynamically.
Libraries like simple-git make these operations easy by providing a clean Node.js interface to Git commands.
But convenience layers around system tools come with risk.
In early 2026, researchers identified CVE-2026-28292, a critical remote code execution vulnerability affecting the simple-git library. The vulnerability allowed attackers to bypass a security control and enable Git’s dangerous ext transport protocol, resulting in arbitrary command execution on the host system.
While patching the library resolves the immediate issue, the deeper lesson is that any application that exposes Git functionality to user input carries inherent security risk.
This article focuses on how developers can secure applications that rely on simple-git, prevent similar vulnerabilities, and design Git integrations that remain safe even if underlying libraries fail.
Why Git Integrations Are Security-Sensitive
Git itself is a powerful command-line tool.
When applications interact with Git programmatically, they are effectively executing shell commands on behalf of user-controlled workflows.
A simple clone operation becomes:
But if an attacker controls the repository URL or arguments, the command can become something far more dangerous.
For example:
That command executes arbitrary shell code.
The root issue is that Git supports transport protocols capable of running commands locally.
The Attack Surface in Git Automation
Any application that uses simple-git typically exposes one or more of the following surfaces:
Feature | Risk |
|---|---|
Repository cloning | Command injection |
Dynamic repository URLs | Protocol abuse |
User-controlled Git arguments | Configuration override |
CI pipelines | Supply chain execution |
Plugin ecosystems | Untrusted code execution |
These surfaces become particularly dangerous when user input flows directly into Git commands.
Where CVE-2026-28292 Fits Into This Risk Model
CVE-2026-28292 allowed attackers to bypass simple-git’s internal protection mechanism by exploiting a case sensitivity mismatch.
Once bypassed, attackers could enable Git’s ext protocol, which executes arbitrary commands.
The vulnerability is important not only because of the specific bug but because it demonstrates a broader security reality:
Even when libraries attempt to enforce security controls, those controls may fail.
Applications should therefore implement defense-in-depth protections.
Secure Architecture for Git-Enabled Applications
The safest Git integration architecture separates user input from system execution.
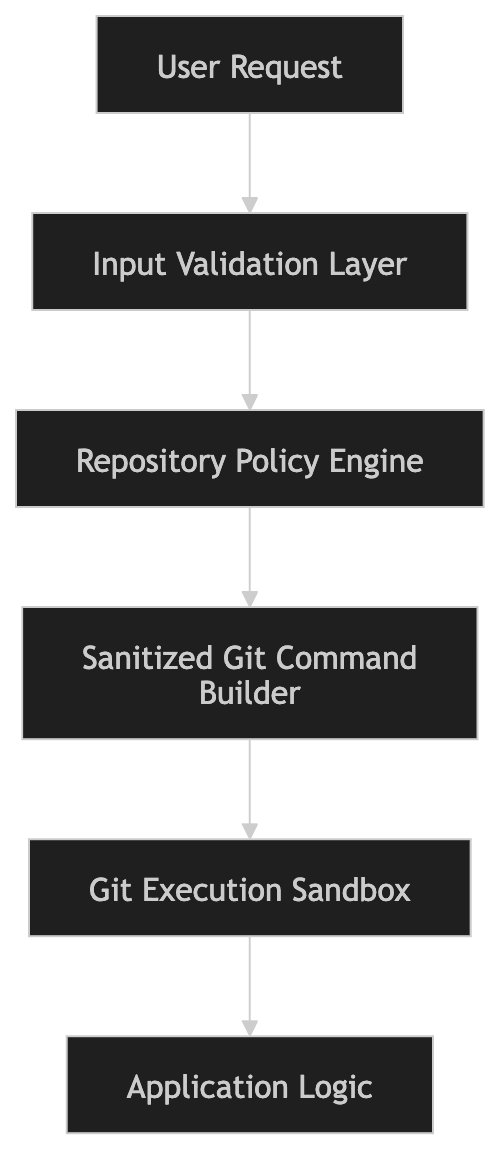
Each layer prevents a different class of attack.
Layer 1: Strict Repository URL Validation
Applications should never accept arbitrary repository URLs.
Instead, validate them against an allowlist.
Example implementation:
This prevents attackers from supplying malicious transport protocols.
Layer 2: Block Dangerous Git Protocols
Git supports multiple protocols.
Not all are safe for automated environments.
Safe protocols typically include:
Dangerous protocols include:
Implement protocol validation:
This prevents entire classes of attacks.
Layer 3: Never Accept Raw Git Arguments
One of the most common security mistakes is passing user input directly into Git arguments.
Example vulnerable pattern:
If userArgs is attacker-controlled, attackers can modify Git behavior.
Safer design:
Applications should define arguments internally rather than accepting them from users.
Layer 4: Normalize Inputs Before Validation
CVE-2026-28292 occurred because a filter expected lowercase values.
A reliable defensive pattern is input normalization.
Example:
Normalization eliminates many bypass techniques.
Layer 5: Execute Git in a Sandbox
Even with validation, Git commands should run inside isolated environments.
Example architecture:
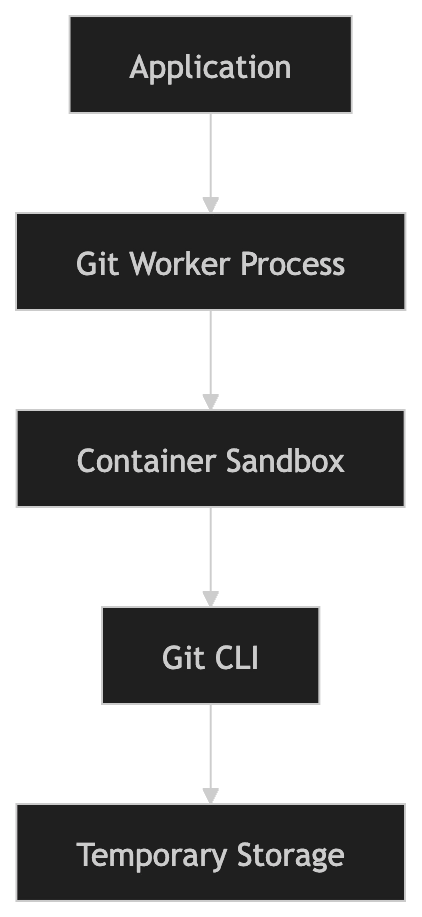
This prevents attackers from accessing the main application environment.
Recommended sandbox approaches:
Docker containers
Firejail
Kubernetes isolated jobs
ephemeral build environments
Example Secure Git Worker
Example architecture used by many CI platforms:
The clone occurs inside an isolated worker container.
Even if the command fails, the host system remains protected.
Layer 6: Use Least Privilege Execution
Git processes should never run with high privileges.
Best practice:
Example container security settings:
Layer 7: Monitor Git Execution
Logging Git operations helps detect abuse.
Example logging:
Combine this with anomaly detection:
unusual repository URLs
unexpected protocol usage
repeated clone failures
Why Library Patches Are Not Enough
Upgrading simple-git fixes CVE-2026-28292.
But patching alone does not eliminate risk.
Security patches solve specific vulnerabilities.
Applications must protect against entire classes of vulnerabilities.
That means implementing architectural safeguards like:
input validation
protocol enforcement
sandboxing
least privilege execution
Why This Matters for Code Review
Security issues like CVE-2026-28292 highlight an uncomfortable reality.
The vulnerability existed inside a security control.
The code looked correct.
The patch had already been applied once before.
And yet a subtle logic mismatch still enabled remote code execution.
These are exactly the kinds of vulnerabilities developers rarely notice during manual review.
Most automated review tools today focus on surface-level suggestions:
code style
formatting
complexity hints
But those are not the moments when developers truly appreciate a review gate.
The real value appears when a tool identifies a vulnerability that nobody knew existed.
During internal research, CodeAnt AI’s code reviewer identified the mismatch between a case-sensitive regex and Git’s case-insensitive configuration behavior, which ultimately led to the discovery of CVE-2026-28292.
This reflects a broader shift in code review tooling.
Instead of simply improving code quality, AI systems are beginning to detect deep security flaws hidden inside complex logic paths.
That’s the direction automated code review is moving toward.
Secure Deployment Checklist
If your application uses simple-git, follow this checklist.
Immediate action
Upgrade:
Minimum safe version:
Security hardening
validate repository URLs
block dangerous protocols
remove user-controlled Git arguments
normalize input values
run Git in isolated containers
restrict process privileges
monitor Git execution logs
Following these practices dramatically reduces risk.
Conclusion
CVE-2026-28292 illustrates how small logic mismatches can lead to serious security consequences.
A single assumption about case sensitivity was enough to bypass a security control and enable remote code execution.
But the bigger lesson is not about regex filters or Git configuration behavior.
It’s about how modern software systems manage risk.
Libraries will always contain vulnerabilities.
Security patches will sometimes miss edge cases.
And attackers will continue looking for subtle ways to bypass controls.
That’s why secure systems rely on multiple layers of defense, not just individual patches.
Input validation.
Sandboxed execution.
Least-privilege environments.
Strict command construction.
These architectural practices ensure that even if one layer fails, the system remains protected.
And they also illustrate something about the future of code review.
Developers don’t really need another tool that tells them to rename a variable.
They need systems capable of identifying the rare but catastrophic bugs that slip past human reviewers.
CVE-2026-28292 is one example of that kind of vulnerability.
And discovering it required reasoning about how different systems interpret input — something traditional static rules struggle to capture.
During security research, CodeAnt AI’s code reviewer flagged the semantic mismatch that ultimately revealed this vulnerability, demonstrating how AI-assisted analysis can uncover deep security flaws that would otherwise remain hidden.
That is the direction modern code review is moving toward.
Not just better code style.
But better software security.
FAQs
What applications are most at risk from CVE-2026-28292?
Does upgrading simple-git completely eliminate the risk?
Why is the Git ext protocol dangerous?
What defensive patterns help prevent Git-related command injection?
How can developers detect similar vulnerabilities in other tools?