Security patches are supposed to close vulnerabilities.
But sometimes they do something far more dangerous.
They create the illusion of security while leaving the underlying flaw intact.
This is one of the most common patterns security researchers encounter when reviewing open-source patches: the patch fixes the exact exploit reported in the bug report, but it does not fix the vulnerability class.
Attackers don’t care about the specific exploit.
They care about the root weakness.
And if that weakness remains, the patch simply becomes the starting point for the next exploit.
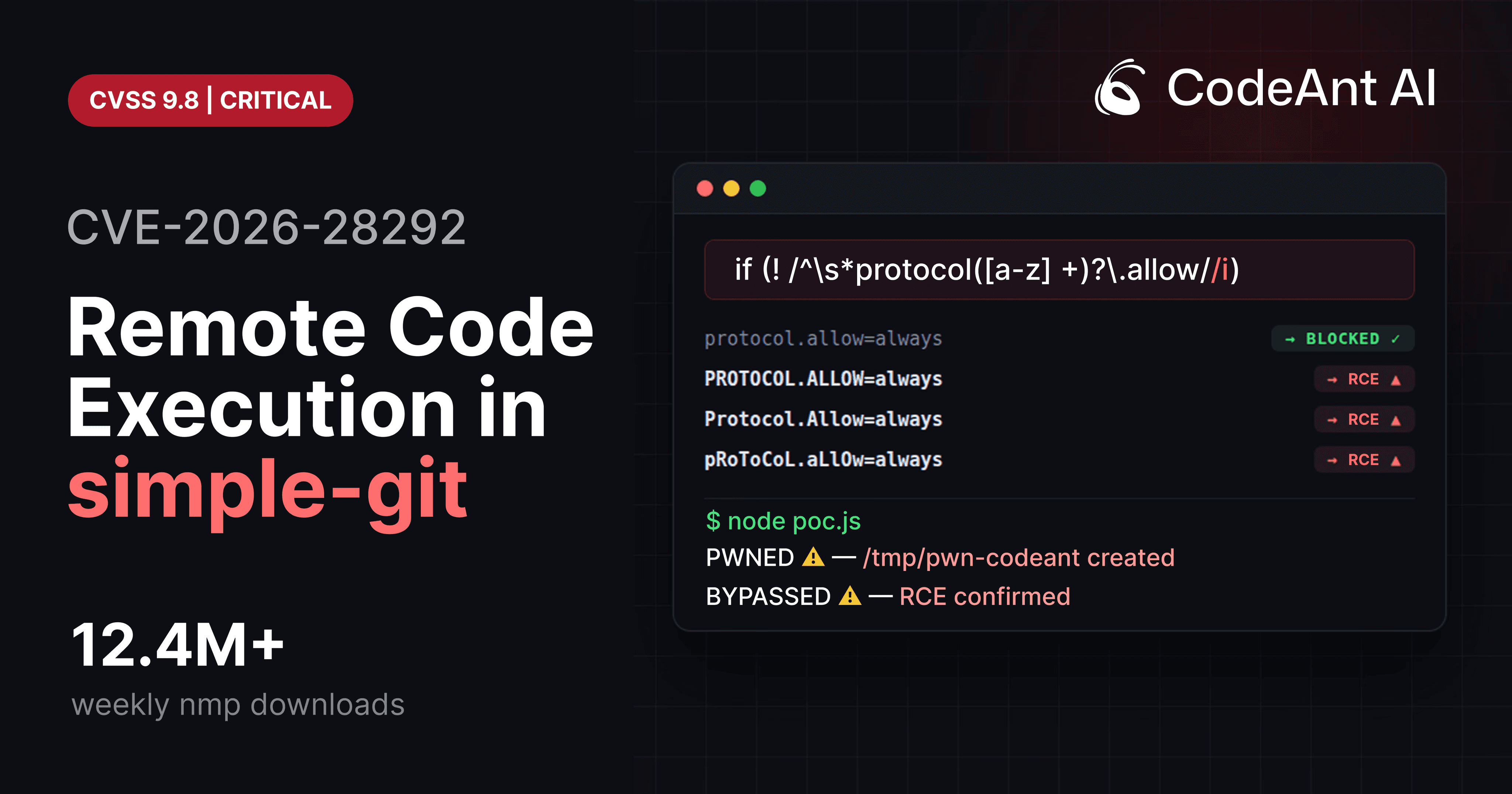
That exact situation occurred in CVE-2026-28292, a critical remote code execution vulnerability discovered in the Node.js library simple-git, which sees more than 12 million weekly downloads.
The patch history for this vulnerability tells a story that appears again and again across the software ecosystem:
A vulnerability is discovered.
A patch is released.
Attackers find a slightly different input that bypasses the patch.
Understanding how this happens, and how to detect it before attackers do, is becoming one of the most important skills in modern application security.
And increasingly, it’s an area where AI-assisted code review is beginning to outperform traditional tooling.
The Hidden Weakness in Security Patches
When developers receive a vulnerability report, the natural instinct is to reproduce the exploit and then block it.
The patch is written specifically to stop that input.
For example:
So the developer adds a filter that detects that exact pattern.
But attackers never use exactly the same payload twice.
They mutate it.
And if the patch only blocks one representation of the attack, the vulnerability remains exploitable.
Security researchers sometimes call this phenomenon:
Patch-driven exploit development.
Instead of discovering a vulnerability from scratch, attackers analyze patches and search for alternative ways to trigger the same underlying flaw.
The Patch History Behind CVE-2026-28292
The vulnerability that became CVE-2026-28292 was not the first issue in this code path.
It was actually the third vulnerability affecting the same logic.
Timeline:
Year | Event |
|---|---|
2022 | CVE-2022-25912 discovered (Git ext protocol RCE) |
2022 | CVE-2022-25860 bypass discovered |
2026 | CVE-2026-28292 discovered |
Each patch addressed the specific exploit that had been reported.
But the underlying assumption remained unchanged.
The security control attempted to detect dangerous Git configuration overrides using a regex.
The original filter looked like this:
At first glance, the logic appears correct.
But the vulnerability appears when we examine how Git processes configuration keys.
The Root Cause: Semantic Mismatch
Git treats configuration keys as case-insensitive.
This means:
are all interpreted identically.
But the security filter was implemented with a case-sensitive regex.
That difference created a bypass.
The vulnerability that became CVE-2026-28292 was simply the realization that the filter did not match uppercase variants.
Example bypass:
The regex did not detect it.
Git accepted it.
The ext protocol was enabled.
And arbitrary commands executed.
Visualizing the Patch Failure
Below is a simplified view of what happened.
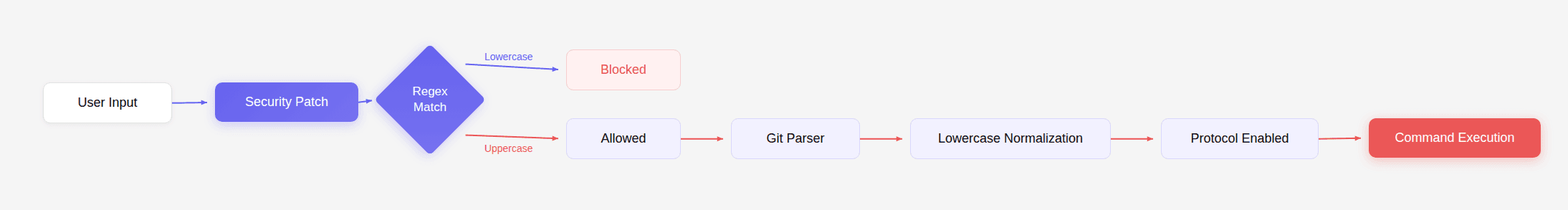
The patch blocked one representation of the attack but allowed another.
From Git’s perspective, both inputs were identical.
Why Patch Auditing Matters
Most vulnerability scanning tools focus on known vulnerabilities.
They match dependency versions against CVE databases.
But patch bypasses exist in a strange gray zone.
They occur:
after a vulnerability has been fixed
before a new CVE is published
During that window, every automated security scanner will report that the system is safe.
But attackers can still exploit it.
This is exactly what happened in the case of CVE-2026-28292.
Traditional scanners missed it because:
the vulnerability was not yet published
the code appeared patched
no rule existed for the specific logic flaw
This is why patch auditing is becoming an increasingly important part of security research.
The Patch Auditing Workflow
Security researchers often follow a structured workflow when auditing patches.
Step 1: Identify the Security Boundary
The first step is to identify the code responsible for enforcing a security control.
In the case of simple-git, that boundary was the plugin responsible for blocking dangerous Git protocols.
This function determines whether untrusted input reaches Git.
Step 2: Examine Assumptions
Next, researchers look for implicit assumptions in the code.
Examples:
case sensitivity
encoding assumptions
normalization behavior
alternate input formats
For CVE-2026-28292, the assumption was that configuration keys would appear in lowercase.
But Git makes no such guarantee.
Step 3: Generate Variants
Researchers then mutate the original exploit.
Example transformations:
Original | Variant |
|---|---|
protocol.allow | PROTOCOL.ALLOW |
protocol.ext.allow | Protocol.Ext.Allow |
protocol.allow | pRoToCoL.aLlOw |
The goal is to discover alternative representations that bypass the patch.
Step 4: Observe System Behavior
If the mutated input passes the filter but still reaches the dangerous code path, the patch has failed.
In this case:
passed the filter and enabled Git’s ext protocol.
A Practical Patch Auditing Example
Below is a minimal reproduction environment for analyzing this vulnerability.
Install the vulnerable library:
Test the original exploit:
Result:
Now test the variant:
Result:
The patch fails.
This is the essence of patch auditing.
The Patch Analysis Mindset
One of the most powerful techniques in vulnerability research is asking a simple question:
What assumption does this patch rely on?
In the case of CVE-2026-28292, the assumption was:
configuration keys will appear in lowercase.
Once that assumption is broken, the patch collapses.
Attackers constantly search for ways to violate assumptions in security controls.
This is why patch auditing is such an effective research strategy.
Why Traditional Code Review Often Misses This
Traditional code review processes focus on readability and correctness.
A reviewer reading the following code might think:
looks reasonable.
The code compiles.
The test cases pass.
The exploit in the bug report is blocked.
But security vulnerabilities rarely hide in obvious errors.
They hide in subtle differences between how systems interpret data.
In this case:
the filter used regex rules
Git used case-insensitive configuration parsing
The reviewer must understand both systems simultaneously to detect the flaw.
That kind of reasoning is exactly where automated code review has historically struggled.
Why AI Code Review Changes Patch Auditing
Modern AI code review tools are beginning to shift toward semantic reasoning.
Instead of searching for predefined patterns, they analyze relationships between:
input validation
system behavior
data transformations
security boundaries
During internal security research, CodeAnt AI’s code reviewer flagged the regex used in simple-git because it was guarding a system known to be case-insensitive.
That observation triggered deeper analysis by a security engineer.
Within an hour, the team confirmed full remote code execution and reported the issue that became CVE-2026-28292.
This type of discovery highlights the future direction of automated code review.
Not better formatting suggestions.
Not more stylistic comments.
But the ability to detect deep security flaws hiding inside otherwise reasonable code.
Defensive Engineering Lessons
There are several important lessons developers can take from this vulnerability.
Normalize Input
Always normalize data before validating it.
This prevents case-based bypasses.
Avoid Regex Security Filters
Regexes are fragile when used as security controls.
Prefer explicit parsing logic whenever possible.
Test Alternate Representations
Security tests should include:
uppercase variants
mixed case
encoding tricks
whitespace variations
Attackers will test these inputs even if developers do not.
Audit Security Patches
If your application depends on an open-source library that recently fixed a vulnerability, it is worth examining the patch carefully.
Sometimes the fix blocks only one exploit variant.
Conclusion: The Most Important Question in Patch Review
Every security patch should be evaluated with one critical question: Did this patch fix the vulnerability, or did it only fix the exploit?
If the underlying weakness still exists, attackers will eventually find another way to trigger it. That is exactly what happened with CVE-2026-28292.
Two previous patches blocked specific exploit payloads.
But the underlying flaw, a mismatch between a case-sensitive filter and a case-insensitive system, remained untouched.
Once that mismatch was identified, bypassing the patch required nothing more than changing a few letters to uppercase. This pattern appears again and again across modern software systems.
Security patches fix the reproduction case in the bug report, but they rarely explore every variation an attacker might try.
That gap is where vulnerabilities hide.
And increasingly, closing that gap is becoming the real purpose of automated code review. Tools that optimize for formatting suggestions or style improvements help developers write cleaner code.
But the tools that truly matter are the ones that catch the catastrophic vulnerability nobody knew existed yet. The discovery of CVE-2026-28292 during internal research with CodeAnt AI’s code reviewer highlights exactly that shift.
The future of code review isn’t about catching minor issues. It’s about identifying the hidden assumptions that turn small bugs into critical vulnerabilities.
FAQs
What is patch bypassing in software security?
Why did CVE-2026-28292 occur even after previous vulnerabilities were patched?
How do attackers discover patch bypasses?
Why do traditional security tools miss patch bypass vulnerabilities?
How can developers audit security patches effectively?