Every major vulnerability raises two different kinds of questions.
The first kind is tactical.
What caused the bug?
How does the exploit work?
How do we patch it?
Those questions are important, but they are also temporary. Once a patch is released and systems are updated, those answers fade into the background.
The second kind of questions are structural.
They are the questions that expose weaknesses in how software is written, reviewed, and secured.
Questions like:
Why did this vulnerability survive previous patches?
Why didn’t existing security tools detect it?
Why did the vulnerability remain invisible across millions of installations?
And what does this incident reveal about how modern code review actually works?
The discovery of CVE-2026-28292, a critical remote code execution vulnerability in the widely used Node.js library simple-git, raises exactly those kinds of questions.
The vulnerability itself was deceptively simple.
A case-sensitive regex attempted to block dangerous Git configuration overrides, but Git treats configuration keys as case-insensitive.
That mismatch allowed attackers to bypass the security filter and execute arbitrary commands on the host machine.
A single missing /i flag in a regex ultimately led to remote code execution across a dependency used millions of times per week.
But the deeper story is not about the regex.
The deeper story is about why this kind of bug survived two previous fixes, why security tools missed it, and why the future of automated code review will likely look very different from what most tools do today.
This article explores twelve questions that incidents like CVE-2026-28292 force the software industry to confront.
1. Why Did Two Previous Fixes Fail to Fully Solve the Vulnerability?
One of the most striking aspects of CVE-2026-28292 is that it was not the first attempt to fix the issue.
Earlier vulnerabilities related to Git protocol overrides had already been patched.
Yet a bypass remained.
This reveals a common pattern in security engineering:
Patches often fix the exploit, not the vulnerability class.
The original exploit path involved configuration overrides like:
The patch introduced a filter designed to block those values.
Simplified logic:
The filter appeared to work.
But it assumed that configuration keys would appear in lowercase.
Git itself does not enforce this assumption.
Example:
Git normalizes configuration keys internally.
Which means uppercase or mixed-case variants bypassed the filter.
The vulnerability remained hidden not because developers ignored the bug, but because the patch addressed the specific exploit payload, not the system behavior that made the exploit possible.
2. Why Do Security Patches Often Focus on the Exploit Instead of the Root Cause?
Security patches are usually developed under intense time pressure.
When a vulnerability report arrives, maintainers follow a typical process:
This approach is practical but incomplete.
Attackers do not reproduce the exploit.
Attackers analyze the assumptions behind the patch.
In the case of CVE-2026-28292, the assumption was simple:
configuration keys will be lowercase
Attackers violated that assumption.
The exploit succeeded.
3. What Does This Incident Reveal About Security Assumptions in Software?
Security controls frequently embed assumptions that developers do not consciously recognize.
These assumptions often include:
Assumption | Reality |
|---|---|
input format predictable | attackers vary format |
case sensitivity consistent | systems normalize case |
input encoding stable | multiple encodings exist |
paths canonicalized | alternate representations exist |
CVE-2026-28292 exists because of one such assumption.
The filter assumed a case-sensitive environment.
The system behaved differently.
4. How Do System-Filter Mismatches Create Vulnerabilities?
A useful way to think about this vulnerability is through the concept of system-filter mismatch.
Security filters operate at one layer of the stack.
The system they protect often behaves differently.
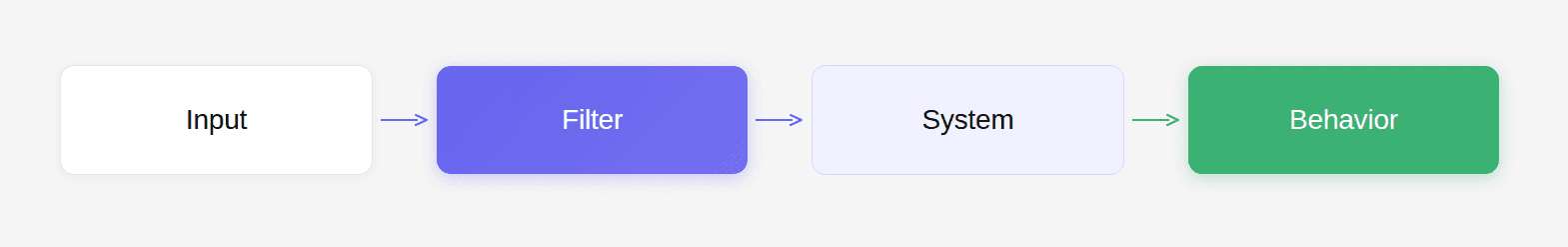
If the filter and the system interpret input differently, attackers can exploit the gap.
Examples include:
Filter | System |
|---|---|
case sensitive regex | case insensitive config |
path sanitization | filesystem normalization |
HTML filter | browser parsing |
URL validator | server routing |
The vulnerability in CVE-2026-28292 is a textbook example.
5. Why Did Traditional Security Tools Fail to Detect the Bug?
When researchers tested common security tools against the vulnerability, none detected it.
Examples:
Tool | Detection |
|---|---|
npm audit | no |
Snyk | no |
Dependabot | no |
Semgrep | no |
SonarQube | no |
This is not surprising.
Most security tools operate using one of two approaches:
signature matching
known vulnerability databases
Neither approach can detect a vulnerability that:
has no CVE yet
involves complex semantic reasoning
spans multiple layers of logic
Detecting the flaw in CVE-2026-28292 required understanding:
regex behavior
Git configuration semantics
protocol overrides
command execution paths
This is a reasoning problem.
Not a pattern-matching problem.
6. Why Do Dependency Ecosystems Remain Vulnerable After Fixes?
Even after a patch is released, many systems remain vulnerable for months.
This occurs for several reasons.
delayed advisory publication
Security databases take time to update.
automated tools depend on databases
If a CVE is not yet published, scanners remain silent.
dependency upgrade inertia
Many projects upgrade dependencies slowly.
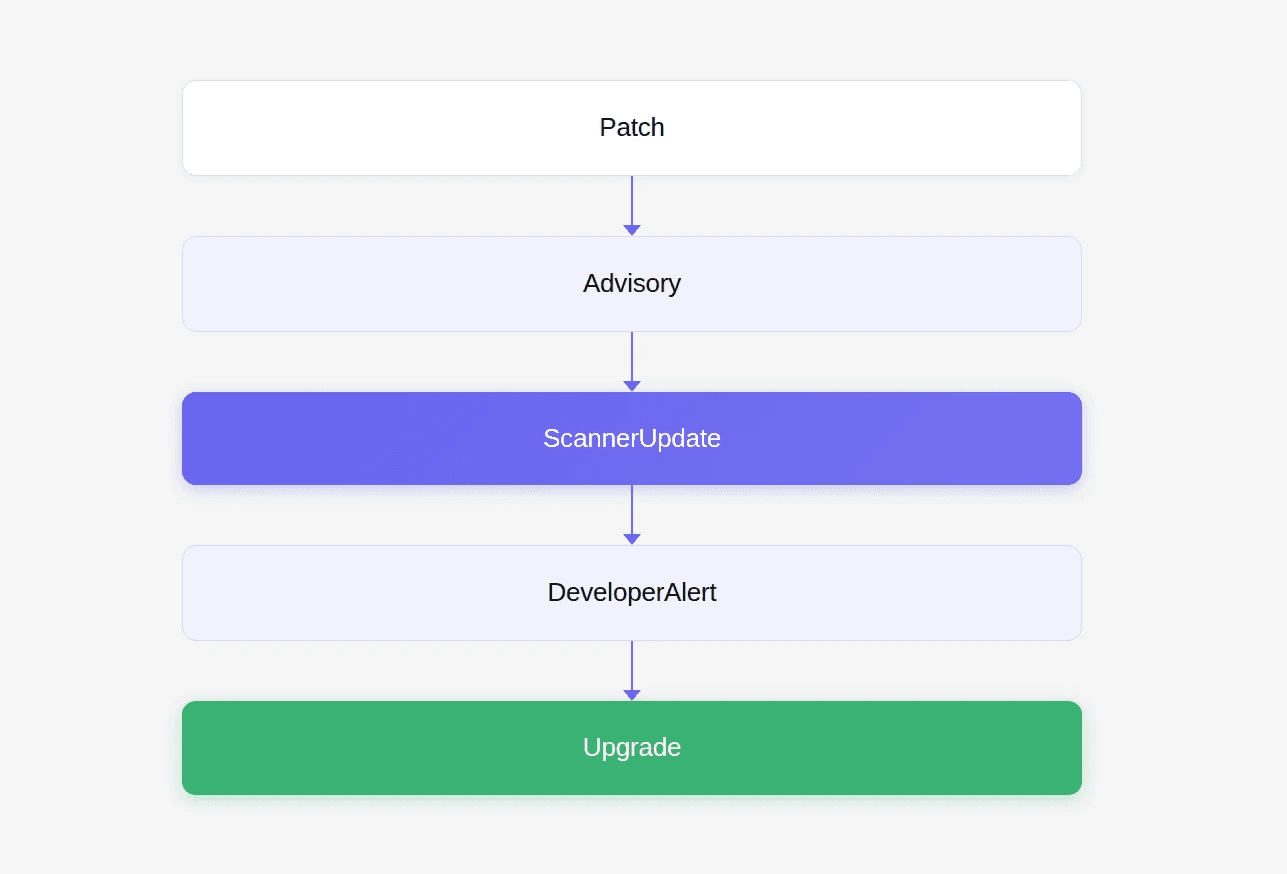
Any delay in this chain leaves systems exposed.
7. What Does This Vulnerability Reveal About Modern Supply Chains?
Modern software is built on enormous dependency graphs.
One small library can affect thousands of projects.
Example dependency tree:
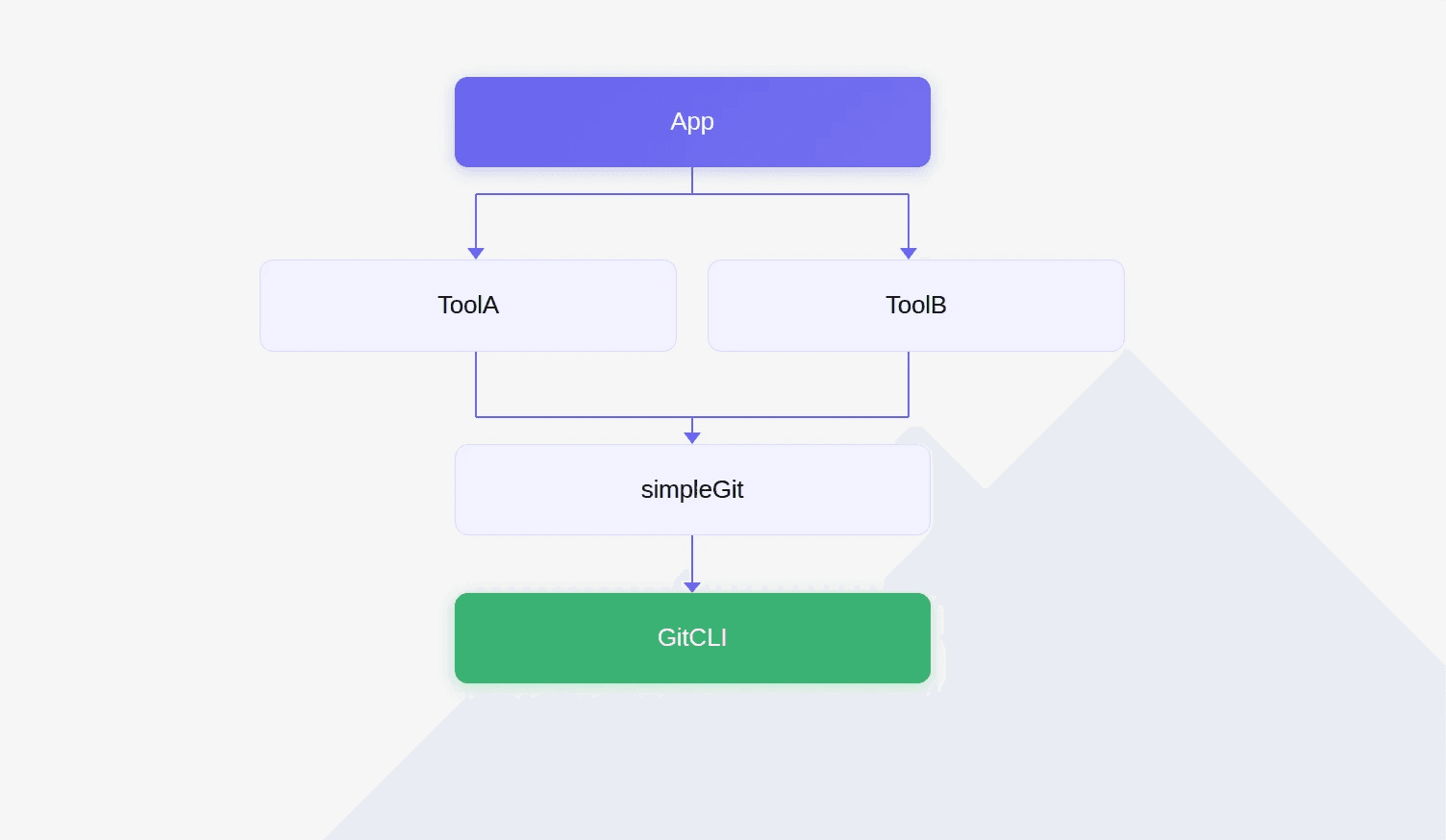
A vulnerability in simple-git therefore propagates widely.
This is why even subtle bugs can become large ecosystem risks.
8. Why Are Variant Attacks So Common in Security Vulnerabilities?
Variant attacks occur when attackers slightly modify an exploit to bypass a patch.
Common techniques include:
case variation
encoding changes
alternate syntax
parameter reordering
Example fuzzing helper:
Testing filters with randomized case frequently reveals bypasses.
The exploit behind CVE-2026-28292 is effectively a variant attack.
9. Why Do Code Reviews Often Miss Security Logic Flaws?
Human code review works well for:
readability
architecture
obvious bugs
But security logic flaws are harder to detect.
Especially when the code appears reasonable.
The vulnerable regex looked correct.
Reviewers saw a filter.
The exploit required understanding Git’s internal behavior.
This kind of reasoning is easy to miss during normal review cycles.
10. What Should Automated Code Review Tools Actually Optimize For?
Most AI code review tools today optimize for developer productivity.
Typical suggestions include:
style fixes
refactoring hints
naming improvements
complexity warnings
These improvements are helpful.
But they are not the reason code review gates exist.
Developers rarely thank a tool for blocking a pull request because of formatting.
They do thank a tool when it prevents a critical vulnerability from shipping.
That moment defines the real value of automated review.
11. How Can AI Improve Security Analysis in Code Reviews?
The discovery of CVE-2026-28292 highlights how AI-assisted analysis can examine relationships between different components of a system.
Instead of scanning for patterns, AI systems can reason about interactions.
For example:
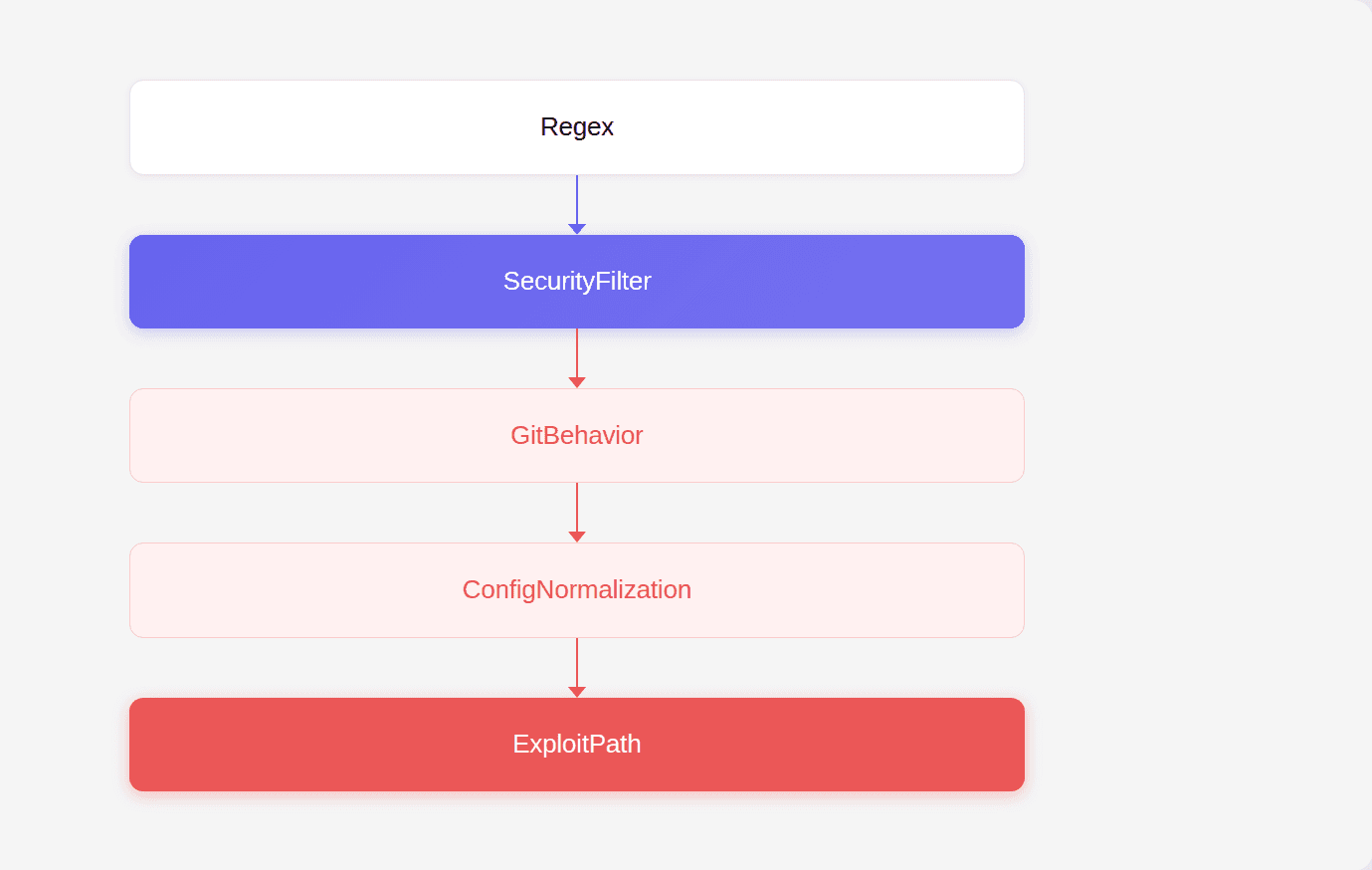
By analyzing these relationships, AI can identify inconsistencies that traditional tools miss.
During internal research, CodeAnt AI’s code reviewer flagged the regex guarding a case-insensitive system, which led to the discovery of the vulnerability.
12. What Should the Future of Code Review Look Like?
The lesson of CVE-2026-28292 is not that developers should write better regex.
The lesson is that modern software ecosystems require new approaches to detecting complex security flaws.
The future of code review will likely involve tools that:
reason about system behavior
detect semantic inconsistencies
analyze patch logic
identify variant attack paths
This is where AI-assisted analysis becomes valuable.
Not for suggesting variable names.
But for catching the vulnerability that no one else has noticed yet.
Conclusion
At first glance, CVE-2026-28292 appears to be a small bug. A missing /i flag in a regex. But the real significance of the vulnerability lies in the questions it raises.
Questions about how security patches are written.
Questions about why automated security tools fail to detect subtle logic flaws.
Questions about why code review processes sometimes overlook vulnerabilities hiding in plain sight.
And most importantly, questions about what automated code review tools should actually be designed to catch.
The vulnerability existed because the patch fixed the exploit, not the vulnerability class. The exploit succeeded because the security filter and the system it protected interpreted input differently.
And the vulnerability was discovered not through traditional scanning tools, but through deeper reasoning about how those pieces interacted. That shift, from pattern matching to reasoning about system behavior, is likely to shape the next generation of security tooling.
Because in the end, the most valuable code review tool is not the one that helps developers write prettier code. It is the one that catches the catastrophic bug before anyone else realizes it exists.
FAQs
What is CVE-2026-28292?
Why did earlier patches fail to fully resolve the vulnerability?
Why did security tools fail to detect the vulnerability?
What is a variant attack and how does it relate to this vulnerability?
How can developers prevent vulnerabilities like CVE-2026-28292?