Security patches are supposed to close vulnerabilities. But in practice, many patches only close the specific exploit that was reported, not the vulnerability itself.
That distinction matters.
Because attackers do not stop once a CVE is patched. In fact, a patch often becomes the starting point for deeper exploitation research.
A patch reveals:
where the vulnerability existed
how the developers attempted to fix it
what assumptions the fix relies on
From an attacker’s perspective, this is incredibly valuable information. It narrows the search space dramatically. Instead of auditing millions of lines of code, an attacker can start with a single commit diff and ask one question:
Did the patch actually solve the problem, or only the exact input used in the original exploit?
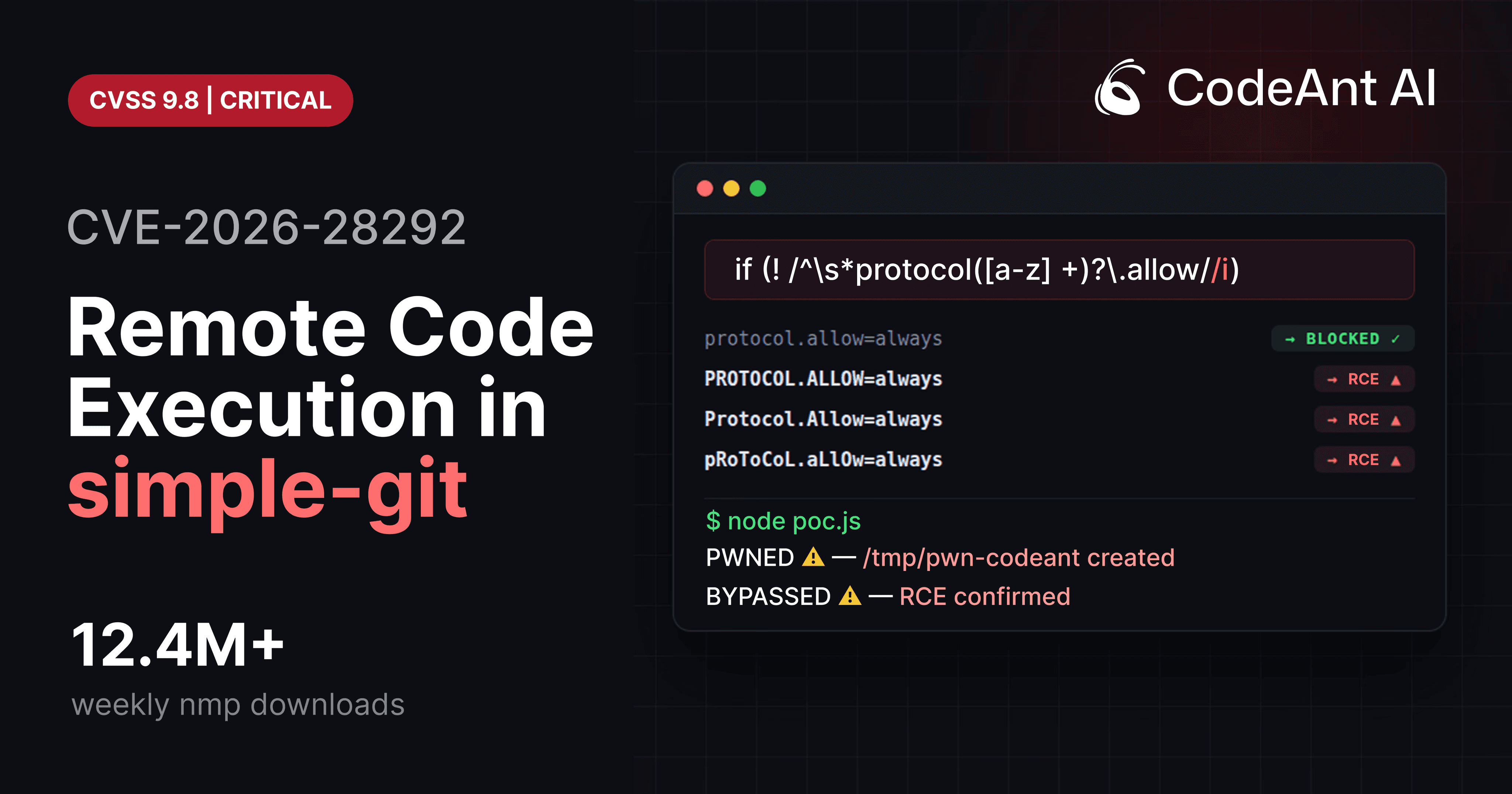
This exact dynamic played out in CVE-2026-28292, a critical remote code execution vulnerability affecting the Node.js package simple-git, used in millions of applications.
The vulnerability was discovered while analyzing the patch logic of two prior CVEs affecting the same code path.
What researchers found was not a new vulnerability. It was a bypass of the previous fixes. And that pattern is far more common than most developers realize.
The Security Patch Illusion
When a vulnerability is reported, developers typically reproduce the exploit and implement a fix that prevents that behavior. A simplified patch cycle looks like this:
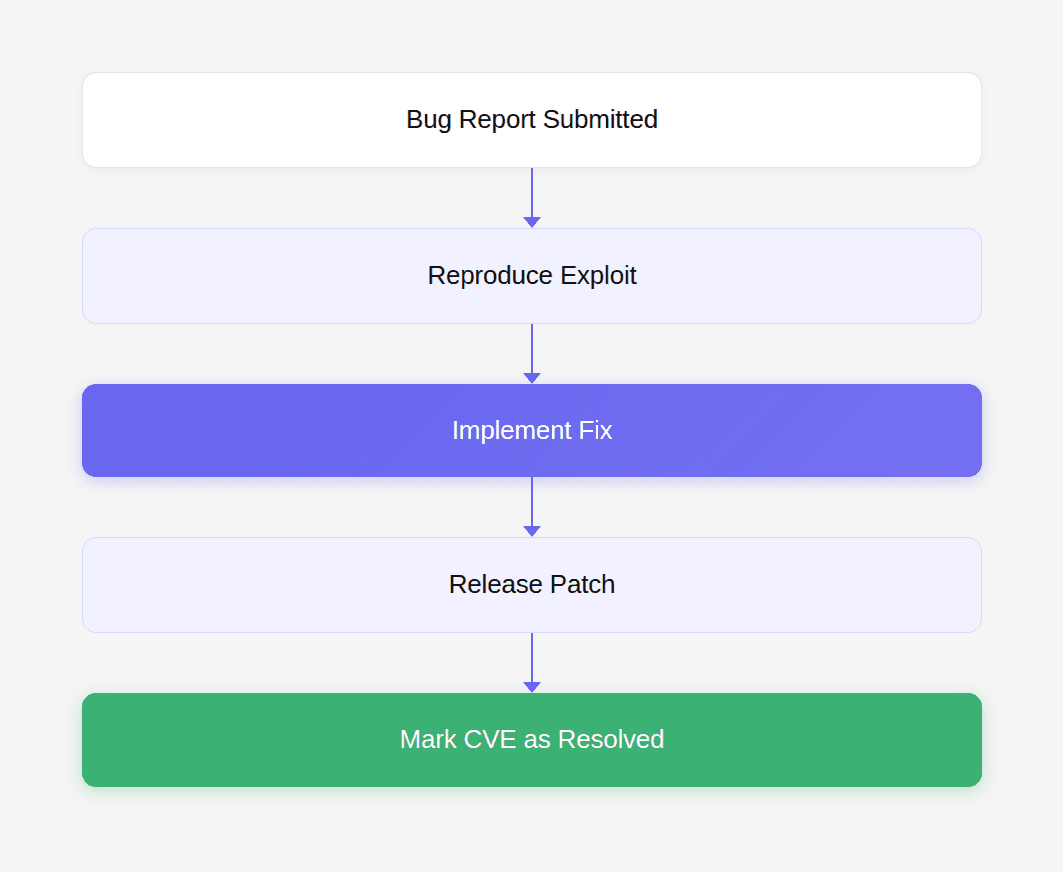
But attackers do not stop here. They analyze the patch and test variations of the original exploit. A more realistic lifecycle looks like this:
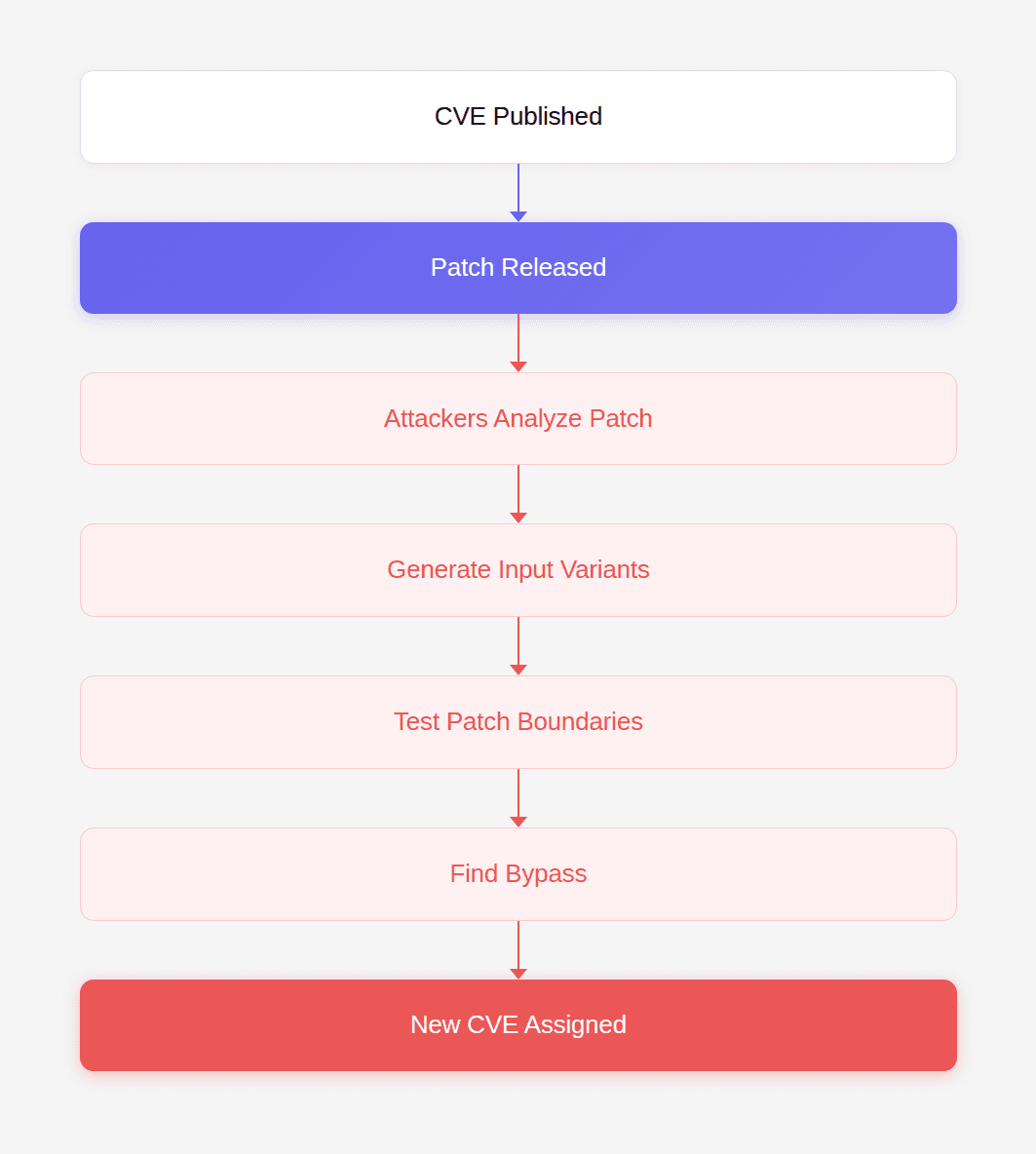
This phenomenon has produced countless follow-up vulnerabilities. And it highlights a structural weakness in how many patches are written. Developers often fix the exploit, not the vulnerability class.
Why Security Patches Often Miss the Real Problem
There are several reasons why CVE fixes get bypassed.
1. Time Pressure
Security patches often ship under extreme time pressure. Maintainers need to:
reproduce the exploit
implement a fix
release a patch quickly
notify users
Under these conditions, developers focus on stopping the reported exploit. Comprehensive threat modeling rarely happens.
2. Incomplete Input Space
Most exploits represent only one possible input. Attackers can often generate hundreds of variations.
Example:
If the patch blocks only the first variant, the vulnerability still exists.
3. Security Filters vs System Behavior
Many vulnerabilities occur when a security filter behaves differently from the system it protects.
Examples:
Security Filter | Target System |
|---|---|
Case-sensitive regex | Case-insensitive parser |
String comparison | Unicode normalization |
Path filter | Filesystem canonicalization |
Whenever these behaviors diverge, bypasses appear.
CVE-2026-28292: A Case Study in Patch Bypass
The vulnerability discovered in simple-git demonstrates this pattern perfectly. The library previously patched two vulnerabilities involving Git’s dangerous ext:: protocol. To prevent attackers from enabling that protocol, the maintainers added a plugin that inspected command arguments.
The core protection looked like this:
At first glance, this appears correct. The filter attempts to block configuration options such as:
These settings allow Git to execute external commands. Blocking them should prevent exploitation. But the filter contained a subtle flaw.
The Case Sensitivity Gap
Git treats configuration keys as case-insensitive.
Example:
Git normalizes the key internally:
But the regex used in the security filter was case-sensitive. That means it matched only lowercase input. Attackers could bypass the filter by changing the casing.
Example:
The filter would not match it. Git would still honor it. And the dangerous protocol would be enabled. This allowed attackers to execute arbitrary commands via the ext:: protocol. That bypass became CVE-2026-28292.
Patch Diff Analysis: How the Bug Slipped Through
Security researchers frequently start their analysis with the patch diff.
Example patch concept:
The fix expanded the regex to catch more variants. But it did not consider case sensitivity. A robust fix would have included:
Or normalized the input before validation. Instead, the patch assumed attackers would use lowercase input. That assumption was incorrect.
Why Attackers Love Security Patches
Security patches reduce the search space dramatically. Imagine auditing a large codebase. There may be hundreds of thousands of lines of code. But a patch highlights the exact area where developers believed a vulnerability existed.
Attackers start by asking:
What does this patch try to block?
What assumptions does it make?
What inputs were not considered?
They then generate variations.
For example:
This simple technique often bypasses naive filters.
The Patch-Analysis Mindset
Security researchers approach patches differently from developers.
Developers ask:
Does this fix the bug?
Researchers ask:
What assumptions does this fix rely on?
That difference in mindset leads to bypass discoveries.
The Role of AI in Patch Analysis
Patch analysis is time-consuming. Large ecosystems contain thousands of CVEs. Manually reviewing every patch is impractical. This is where AI-assisted analysis becomes powerful. Instead of matching patterns, AI systems can reason about:
data flow
system behavior
semantic mismatches
During internal research, CodeAnt AI’s code reviewer flagged the regex used in simple-git because it protected a case-insensitive system using a case-sensitive filter. That observation triggered deeper analysis. Within an hour, researchers confirmed a full remote code execution exploit. This demonstrates how AI-assisted code review is evolving beyond stylistic feedback toward security reasoning.
You can read the full research case here: https://www.codeant.ai/security-research/simple-git-remote-code-execution-cve-2026-28292
Real-World Examples of Patch Bypasses
CVE-2026-28292 is not unique. History contains many examples of vulnerabilities reappearing after patches.
Apache Struts (Equifax breach)
The infamous Equifax breach occurred because a vulnerability in Apache Struts was not fully addressed. Attackers exploited a variation of the vulnerability to execute commands on the server.
Log4Shell follow-up CVEs
The original Log4Shell vulnerability led to several follow-up CVEs. Attackers discovered ways to bypass the initial mitigations. Each patch addressed a specific bypass.
Path traversal vulnerabilities
Many path traversal fixes initially block:
But attackers bypass them using:
Each variant exploits assumptions about input encoding.
Designing Patches That Actually Work
The most reliable security patches follow several principles.
1. Fix the Vulnerability Class
Instead of blocking specific inputs, developers should address the root cause.
Example:
Bad fix:
Better fix:
2. Normalize Input First
Normalization prevents bypasses.
Example:
3. Use Allowlists
Blocklists rarely scale.
Better pattern:
4. Threat Model the System
Developers should ask:
what assumptions does this fix rely on?
what alternate inputs exist?
how does the underlying system interpret input?
Security Testing for Patch Robustness
When reviewing a patch, engineers should test variations.
Example checklist:
Test casing variations
Test encoding variations
Test whitespace
Test Unicode normalization.
These tests frequently expose incomplete fixes.
Why Code Review Must Evolve
The deeper lesson of CVE-2026-28292 is not just about regex. It is about the limitations of traditional code review. Most automated review tools today focus on:
style suggestions
formatting improvements
refactoring hints
But those are not the moments where code review truly matters. The real value appears when a system catches a critical security flaw before it reaches production. The vulnerability described here existed after two previous patches.
The code looked correct.
Static analysis tools saw nothing unusual.
Yet the underlying security assumption was wrong. This is exactly the type of flaw AI-assisted reasoning can uncover. Instead of looking for predefined patterns, modern analysis systems must understand how code interacts with the systems around it.
That shift is already happening. And vulnerabilities like CVE-2026-28292 illustrate why it matters.
Conclusion: Why Patch Bypass Research Matters
Security patches are often treated as the end of the story. But in reality they are often the beginning of the next vulnerability discovery. A patch tells researchers where the vulnerability lived.
It reveals how developers attempted to fix it.
And it exposes the assumptions behind the fix.
When those assumptions are wrong, bypasses emerge. CVE-2026-28292 is a perfect example. Two prior patches attempted to block protocol override attacks. Both succeeded in blocking the specific exploit they were designed to stop. But neither addressed the deeper issue. A case-sensitive filter protecting a case-insensitive system. That mismatch allowed attackers to bypass the security control with a single uppercase string. The discovery of this vulnerability during internal research using CodeAnt AI’s code reviewer highlights where automated code analysis is heading.
The future of code review is not about better formatting suggestions.
It is about detecting the subtle security assumptions that break under real-world input.
Because the most valuable code review comment is not:
“rename this variable.”
It is:
“this patch doesn’t actually fix the vulnerability.”
FAQs
Why do many CVE fixes get bypassed?
What made CVE-2026-28292 a patch bypass rather than a new vulnerability?
Why are patch bypasses dangerous for software ecosystems?
How can developers ensure their security patches are robust?
What role does AI play in detecting patch bypass vulnerabilities?