When a vulnerability disclosure appears in a popular open-source library, most engineers ask a predictable set of questions.
What version is vulnerable?
Is my system affected?
How do I upgrade?
Those questions matter, but they only scratch the surface.
Every security vulnerability also raises deeper questions, questions about how the bug survived code review, why existing security tools failed to detect it, and what it reveals about the software ecosystem that allowed it to exist.
The discovery of CVE-2026-28292, a critical remote code execution vulnerability in the Node.js library simple-git, is one of those cases where the vulnerability itself is only part of the story.
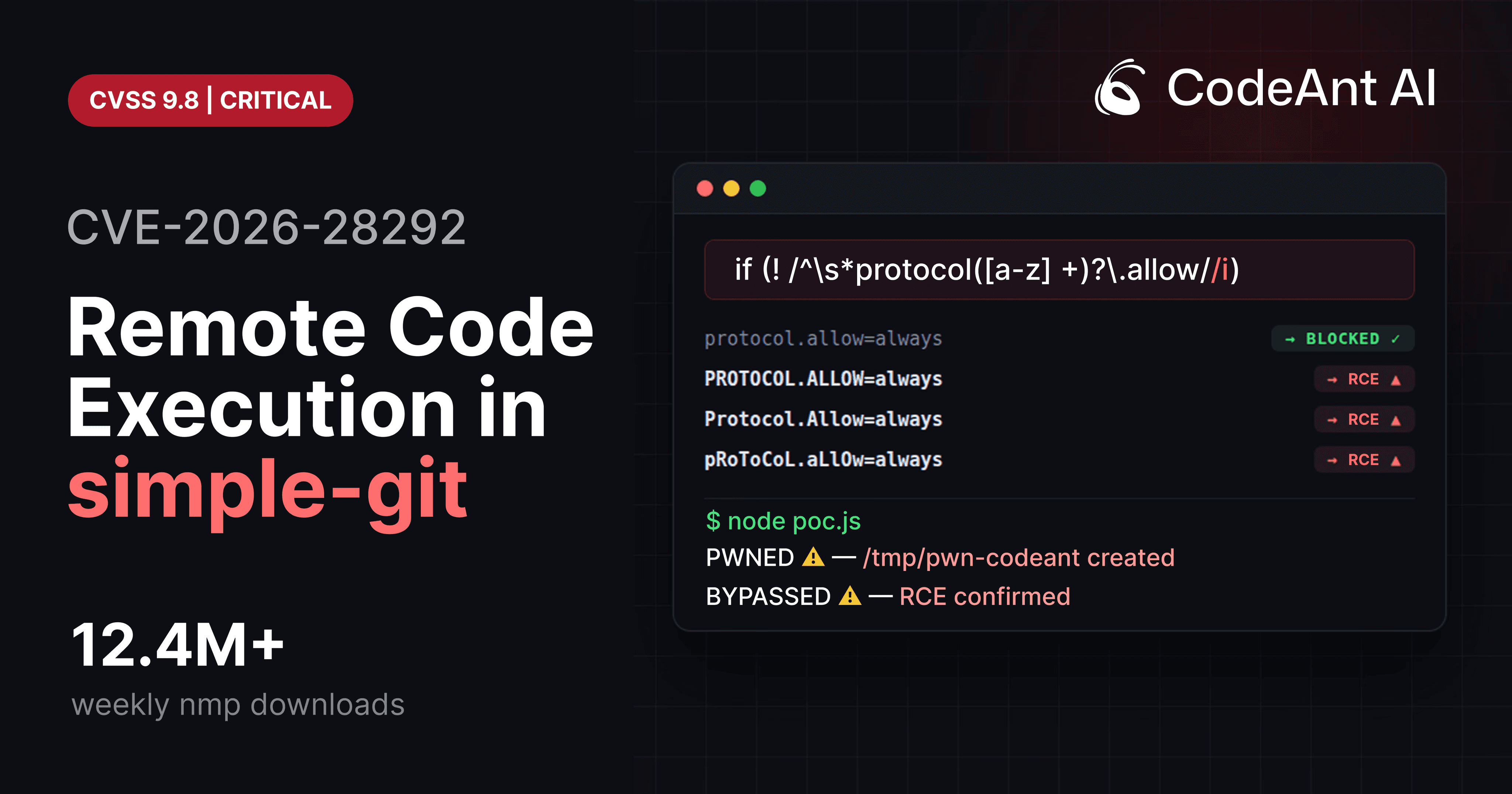
At first glance, the bug appears trivial:
A case-sensitive regex filter attempted to block Git configuration overrides, but Git treats configuration keys as case-insensitive.
That mismatch allowed attackers to bypass the filter and enable Git’s ext:: protocol, which can execute arbitrary shell commands.
But once researchers began analyzing the vulnerability, the investigation quickly expanded into much larger questions about:
patch reliability
vulnerability detection
security testing strategies
and the role of automated reasoning in modern code review.
This article explores some of the most important questions that CVE-2026-28292 forces security researchers and engineering teams to ask.
1. What Exactly Was the Security Control Trying to Prevent?
The first question in any vulnerability investigation is deceptively simple:
What was the security control supposed to do?
In the case of simple-git, the goal of the security plugin was to block configuration overrides that enable dangerous Git protocols.
The most important of these protocols is ext transport, which allows arbitrary command execution.
Example Git URL:
When Git encounters an ext:: URL, it executes the command embedded in the transport string.
To prevent this behavior, the library attempted to detect configuration arguments such as:
The filter attempted to block these values using a regex:
The intention was correct.
The implementation contained a subtle flaw.
2. What System Behavior Did the Security Filter Assume?
Every security control is based on assumptions about the system it protects.
In this case the assumption was:
configuration keys will appear in lowercase
The regex used:
Which matches only lowercase characters.
But Git configuration keys are case-insensitive.
Example:
Output:
Git normalizes configuration keys internally.
This means attackers could bypass the filter simply by changing the casing of the key.
This bypass became CVE-2026-28292.
3. Why Didn’t Code Review Catch the Bug?
One of the most important questions raised by this vulnerability is why the bug survived code review.
The vulnerable regex looks reasonable at first glance.
To a reviewer scanning the code, the presence of a filter suggests the security problem has already been addressed.
But security vulnerabilities often hide in the assumptions behind the code, not the code itself.
Reviewers must understand both:
the filter logic
the behavior of the protected system
The exploit required understanding that Git configuration is case-insensitive.
Without that knowledge, the regex appears safe.
This is exactly the type of issue that traditional code review frequently misses.
4. Why Did Security Scanners Fail to Detect the Vulnerability?
Another important question is why automated security tools failed to detect the issue.
Common security scanners rely on two techniques:
known vulnerability databases
Tools like npm audit compare dependency versions against published CVEs.
rule-based static analysis
Tools like Semgrep or SonarQube detect patterns associated with known vulnerability classes.
But the flaw in CVE-2026-28292 was neither a known vulnerability nor a known pattern.
It required understanding a chain of relationships:
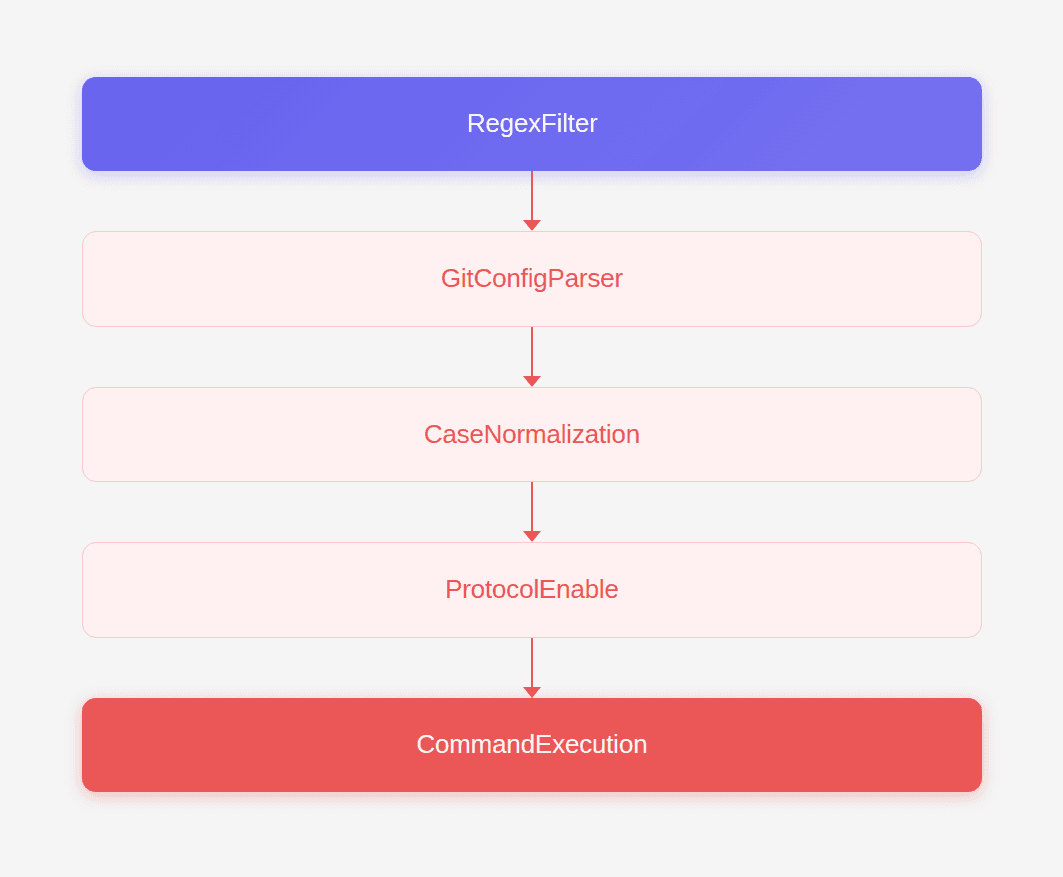
This kind of multi-layer reasoning is difficult for traditional static analysis tools.
5. How Did Researchers Identify the Vulnerability?
The vulnerability was discovered during an investigation into the quality of patches applied to previously reported CVEs.
The research question was simple:
when a vulnerability is patched, does the patch actually fix the problem?
The analysis involved examining patch diffs across popular open-source packages.
During this process, an AI-assisted code reviewer flagged the following pattern:
regex filter
guarding security-sensitive configuration
protecting a system known to normalize input
That combination raised suspicion.
Further manual analysis confirmed that the regex filter was case-sensitive.
This led directly to the discovery of CVE-2026-28292.
You can read the full research case here.
6. How Can Researchers Systematically Look for Similar Bugs?
Once a vulnerability like this is discovered, researchers often ask whether similar bugs exist elsewhere.
One effective strategy is to search for security filters implemented with case-sensitive regex patterns.
Example code search query:
Then compare the filter behavior with the semantics of the underlying system.
Potential targets include:
system | normalization behavior |
|---|---|
HTTP headers | case insensitive |
Windows paths | case insensitive |
Git config keys | case insensitive |
SQL identifiers | often case insensitive |
If the filter and the system interpret case differently, a bypass may exist.
7. What Makes Variant Attacks So Effective?
The exploit behind CVE-2026-28292 is an example of a variant attack.
Variant attacks modify the original exploit slightly to bypass patches.
Common variant strategies include:
case changes
encoding variations
alternate syntax
parameter ordering
Example case variation generator:
Testing filters against variant inputs frequently reveals bypasses.
8. How Should Security Teams Test Patches for Bypass Conditions?
Testing a patch requires more than verifying that the original exploit no longer works.
Security teams should ask:
what variations of the exploit might still succeed?
Recommended testing steps:
Example bypass test:
If command execution occurs, the patch failed.
9. Why Are Security Filters So Difficult to Implement Correctly?
Security filters are deceptively complex.
They must account for:
syntax variations
encoding differences
normalization behavior
platform semantics
A filter that appears correct in isolation may fail when interacting with the underlying system.
This complexity is why modern security engineering often prefers allowlists and normalization over complex regex filters.
10. What Does This Vulnerability Reveal About Code Review Priorities?
The discovery of CVE-2026-28292 raises an important question about the priorities of automated code review tools.
Many tools today focus on issues like:
style consistency
formatting
naming conventions
code complexity
While useful, these improvements rarely prevent catastrophic failures.
The vulnerability described here demonstrates the kind of bug that actually matters:
A subtle logic flaw that allows attackers to bypass a security control and execute arbitrary commands.
Catching this type of issue is far more valuable than flagging minor stylistic inconsistencies.
Conclusion
At first glance, CVE-2026-28292 looks like a small mistake. A missing /i flag in a regex.
But the vulnerability reveals something much deeper about how software security works.
It shows how security patches can leave hidden attack paths behind.
It demonstrates how subtle assumptions about system behavior can undermine otherwise reasonable protections.
And it highlights the limits of both traditional static analysis and conventional code review when dealing with complex security logic.
The vulnerability was ultimately discovered through a combination of automated reasoning and human analysis.
An AI-assisted code reviewer flagged the suspicious pattern.
A security engineer investigated the underlying behavior.
The result was the discovery of a critical vulnerability affecting millions of installations.
Incidents like this suggest that the future of automated code review will not be defined by formatting suggestions or minor refactoring hints.
It will be defined by the ability to detect the rare, high-impact vulnerabilities that traditional tools overlook.
Because in the end, the most valuable code review tool is the one that stops the catastrophic bug before anyone else notices it exists.
FAQs
What is CVE-2026-28292?
Why did the regex filter fail to block the exploit?
How can developers detect similar vulnerabilities in their own code?
What is a variant attack?
How can AI improve vulnerability discovery in code review?