When a vulnerability receives a CVSS score of 10.0, it represents the maximum severity classification under the Common Vulnerability Scoring System.
This rating is reserved for vulnerabilities that satisfy the most dangerous set of conditions simultaneously:
network exploitable
no authentication required
no user interaction required
complete compromise of confidentiality, integrity, and availability
In practice, vulnerabilities meeting these criteria are rare.
But when they appear, they tend to reshape how the security community thinks about software architecture.
Some of the most consequential examples include:
Apache Struts OGNL injection (CVE-2017-5638)
Log4Shell (CVE-2021-44228)
identity token delegation flaws in cloud identity systems
authentication bypasses in token validation frameworks
Each vulnerability demonstrates a deeper architectural issue: a system trusting unverified input at a critical boundary.
Recently, another vulnerability joined this category:
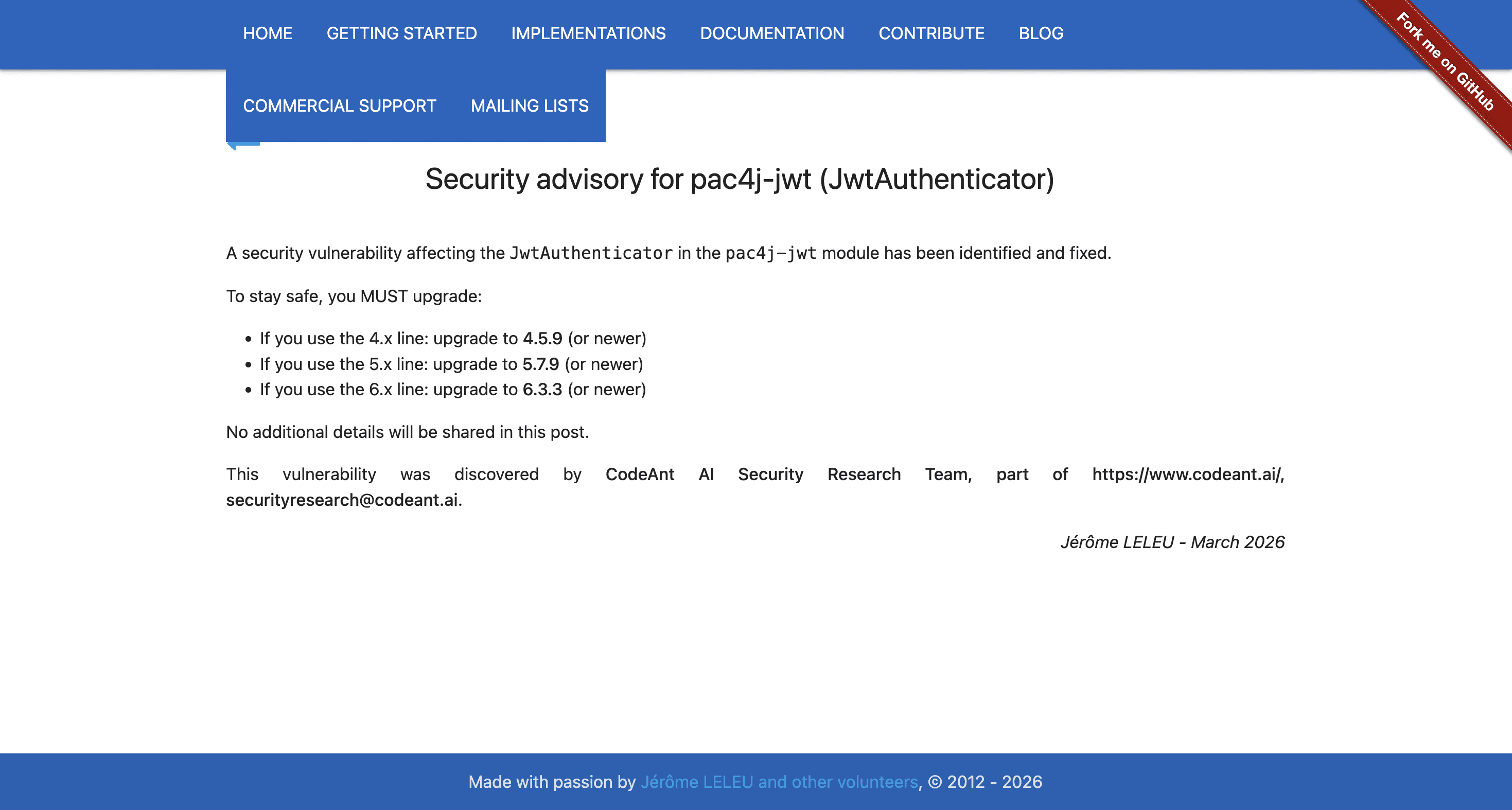
CVE-2026-29000 - a JWT authentication bypass discovered in the pac4j authentication framework.
Full technical details are available in the original research disclosure:
https://www.codeant.ai/security-research/pac4j-jwt-authentication-bypass-public-key
To understand why these vulnerabilities are so dangerous, we need to analyze them not individually but structurally.
What CVSS-10 Actually Represents
The CVSS scoring model evaluates vulnerabilities using multiple metrics.
The most important are:
A score of 10.0 typically indicates:
In plain terms:
the attacker can exploit the vulnerability remotely
the exploit requires little complexity
the attacker needs no credentials
the victim does not need to perform any action
the vulnerability impacts the entire system
When those conditions align, exploitation becomes trivial and impact becomes catastrophic.
Case Study: Apache Struts OGNL Injection
One of the most widely known CVSS-10 vulnerabilities occurred in Apache Struts.
The vulnerability, CVE-2017-5638, allowed attackers to inject malicious expressions into HTTP headers processed by the framework’s multipart request parser.
Details:
https://nvd.nist.gov/vuln/detail/CVE-2017-5638
The vulnerability exploited how Struts evaluated OGNL expressions embedded in error messages.
An attacker could send a crafted request containing something like:
The request would pass through Struts' error handling pipeline.
During processing, the OGNL interpreter evaluated the injected expression.
Which meant user-controlled data became executable code.
This allowed remote command execution on the server.
The exploit chain looked like this:
The vulnerability ultimately enabled the Equifax breach, exposing personal data belonging to over 147 million people.
The architectural flaw was simple:
Case Study: Log4Shell
Another vulnerability that reached maximum severity was Log4Shell.
CVE-2021-44228 affected the widely used Java logging framework Log4j.
Technical details:
https://nvd.nist.gov/vuln/detail/CVE-2021-44228
Log4j supported a feature called lookup substitution, allowing dynamic evaluation of expressions inside log messages.
For example:
But the feature also supported JNDI lookups.
An attacker could submit input containing:
When logged by the application, Log4j would attempt to resolve the lookup.
Under certain configurations this caused the application to load remote Java classes.
Which meant simply logging attacker-controlled input could lead to remote code execution.
The attack path:
Even Minecraft servers were vulnerable because chat messages were logged using Log4j.
The trust boundary failure here was subtle:
Identity Systems: Token Authority Failures
Another category of CVSS-10 vulnerabilities involves identity tokens.
Modern authentication systems frequently rely on signed tokens to represent user identities.
Examples include:
OAuth tokens
OpenID Connect ID tokens
SAML assertions
JWT tokens
Because these tokens represent identity, any flaw in token validation can result in complete authentication bypass.
A notable example is the Entra ID actor token vulnerability described by Dirk-Jan Mollema.
https://dirkjanm.io/obtaining-global-admin-in-every-entra-id-tenant-with-actor-tokens/
The vulnerability was later tracked as:
https://msrc.microsoft.com/update-guide/vulnerability/CVE-2025-55241
Actor tokens represent delegated actions performed by one identity on behalf of another.
But the system occasionally treated these tokens as fully authoritative identities.
Which meant attackers could escalate privileges across tenants.
The failure:
CVE-2026-29000: JWT Authentication Bypass
Another example of a trust boundary failure appeared in the pac4j authentication framework.
The vulnerability affects pac4j-jwt, a library used for validating encrypted and signed JSON Web Tokens.
Original research:
https://www.codeant.ai/security-research/pac4j-jwt-authentication-bypass-public-key
The vulnerability occurs in the JwtAuthenticator component responsible for validating tokens.
The intended validation flow is:
But the implementation introduced a subtle control-flow condition.
The code attempted to parse the decrypted payload using:
If the payload contained a signed token, the method returned the parsed object.
If the payload contained an unsigned JWT, the method returned null.
Signature verification occurred only when the parsed token was not null.
Which created the following path:
An attacker could exploit this by embedding an unsigned JWT inside an encrypted wrapper.
Because the encryption layer succeeded, the system trusted the token.
And because signature verification never executed, the claims were accepted.
The attacker could impersonate any user.
Why These Vulnerabilities Are Structurally Similar
Despite targeting different technologies, these vulnerabilities share a common structure.
Vulnerability | Broken Trust Boundary |
|---|---|
Apache Struts | input interpreted as executable expression |
Log4Shell | logged input interpreted as lookup instruction |
Entra actor tokens | delegated identity interpreted as authoritative identity |
JWT bypass | encrypted token interpreted as authenticated token |
Each system assumed something about its inputs that the specification did not guarantee.
Attackers exploited that assumption.
Why CVSS-10 Vulnerabilities Are Increasing in Identity Systems
Over the past decade, the software industry has shifted from session-based authentication to token-based identity systems.
Modern applications frequently rely on identity artifacts such as:
OAuth access tokens
OpenID Connect ID tokens
SAML assertions
JSON Web Tokens (JWTs)
These tokens act as portable identity credentials.
Instead of verifying a user directly, systems trust the claims embedded inside the token.
Which means authentication effectively becomes:
This architectural shift creates a new category of high-impact vulnerabilities.
If an attacker can manipulate how a system validates identity tokens, they can often bypass authentication entirely.
Several recent vulnerabilities illustrate this pattern:
Vulnerability | Identity Failure |
|---|---|
Entra ID actor tokens | delegated token treated as authoritative identity |
JWT algorithm confusion | public key interpreted as HMAC secret |
JWT | unsigned tokens accepted as valid |
pac4j JWT flaw | encrypted token interpreted as authenticated token |
In each case, the vulnerability does not allow arbitrary code execution.
Instead it allows something more subtle:
identity forgery.
And because identity tokens are used across distributed systems, the impact can cascade across multiple services.
This is why identity validation bugs increasingly receive CVSS-10 classifications.
They allow attackers to impersonate any user without credentials, without user interaction, and often across network boundaries.
In modern cloud architectures, that can mean full control of entire application environments.
The Rise of Composition Vulnerabilities
Modern software relies heavily on layered frameworks and libraries.
As a result, many vulnerabilities today are not caused by a single faulty component.
Instead they arise from interactions between components.
For example:
a parser returns unexpected data
a validation step assumes a specific format
a downstream component trusts the output
Each component behaves correctly.
But the system as a whole becomes vulnerable.
These are known as composition vulnerabilities.
Why This Matters for Security Engineering
The lesson from these CVSS-10 vulnerabilities is not simply that severe bugs exist.
It is that the most catastrophic bugs tend to occur at architectural boundaries:
input parsing
deserialization
authentication
identity delegation
logging infrastructure
Code operating at these boundaries must be treated as critical infrastructure.
Because if it fails, everything behind it becomes reachable.
FAQs
What does a CVSS score of 10 mean?
Why are CVSS 10 vulnerabilities rare?
What are examples of CVSS 10 vulnerabilities?
Why do authentication systems often produce critical vulnerabilities?
What are composition vulnerabilities in software security?















