From Code Review to CVE Feeds: The Lifecycle of CVE-2026-29000
Modern software security is no longer defined solely by the discovery of vulnerabilities. Discovery is only the first step in a much larger process that transforms a technical finding into actionable intelligence for thousands of organizations worldwide.
A vulnerability discovered by a researcher must propagate through an entire ecosystem before it reaches the engineers responsible for fixing systems in production.
That ecosystem includes maintainers, vulnerability databases, threat intelligence feeds, national cybersecurity agencies, security media, and automated vulnerability scanners.
Understanding how this pipeline works is increasingly important because organizations today rely heavily on automated systems to monitor the security posture of their software supply chains.
A useful example of this process is CVE-2026-29000, a critical authentication bypass discovered in the Java authentication framework pac4j-jwt.
The vulnerability allows attackers to forge encrypted JWT tokens using only a public key and authenticate as arbitrary users.
The original technical disclosure of this vulnerability is available here:
https://www.codeant.ai/security-research/pac4j-jwt-authentication-bypass-public-key
Within days of the disclosure, the vulnerability appeared across multiple vulnerability intelligence platforms, security advisories, and community discussions. Observing how the information moved across these systems provides insight into the mechanics of modern vulnerability intelligence.
Stage 1: Discovery
Every vulnerability lifecycle begins with discovery.
In many cases discovery occurs through one of several common channels:
internal security research
• bug bounty programs
• penetration testing engagements
• automated security analysis tools
• incident response investigations
In the case of CVE-2026-29000, the vulnerability was identified during an internal research initiative focused on analyzing how open-source packages implement authentication and token validation.
The investigation examined the behavior of the JwtAuthenticator component used by the pac4j security framework to validate encrypted JSON Web Tokens.
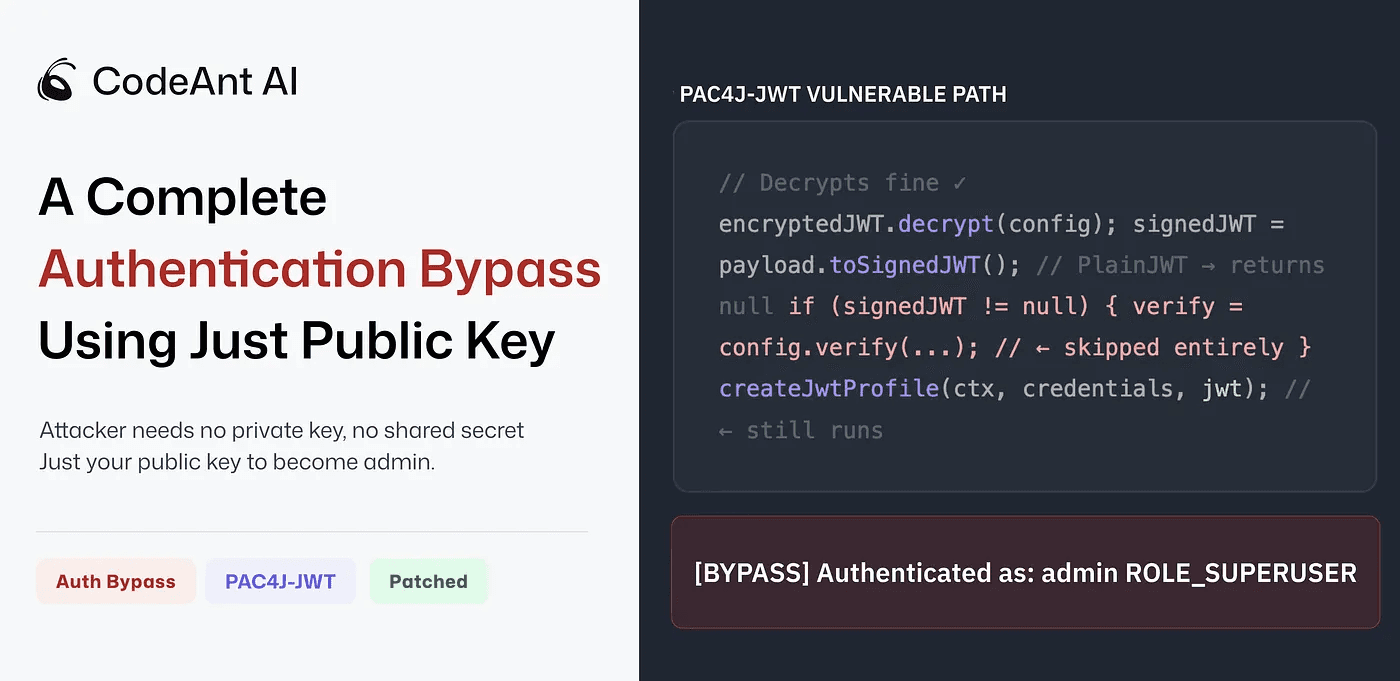
The vulnerability arose from a subtle control flow condition during token validation. When the system decrypted an encrypted JWT and attempted to parse the inner payload as a signed token, it relied on a helper function from the Nimbus JOSE+JWT library.
If the payload contained an unsigned JWT (PlainJWT), the parser returned null. The pac4j authentication logic only executed signature verification when the parsed token object was not null. As a result, authentication could proceed without verifying a cryptographic signature.
This allowed attackers to construct a malicious token by embedding an unsigned JWT inside an encrypted wrapper generated using the server’s public RSA key. Because the encryption layer succeeded, the system trusted the token and accepted the claims without performing signature verification.
The full technical breakdown of the exploit path is described in the original research article:
https://www.codeant.ai/security-research/pac4j-jwt-authentication-bypass-public-key
Once the vulnerability was confirmed and a proof-of-concept exploit was built, the next step was responsible disclosure.
Stage 2: Responsible Disclosure
Responsible disclosure ensures that vulnerabilities are reported privately to maintainers before public release. This allows maintainers time to verify the issue and produce patches before attackers can exploit the vulnerability widely.
In this case, the maintainers of the pac4j project were contacted with a detailed report describing the vulnerability, including:
the affected code path
• a proof-of-concept exploit
• suggested remediation steps
The maintainers confirmed the vulnerability and released patched versions of the pac4j-jwt module addressing the issue.
Once the patch was available, the vulnerability could be publicly disclosed and assigned a CVE identifier.
Stage 3: CVE Assignment
The Common Vulnerabilities and Exposures (CVE) system provides a standardized identifier for publicly disclosed vulnerabilities. Each CVE entry includes metadata describing the affected software, vulnerability type, severity, and references.
The vulnerability was assigned the identifier:
CVE-2026-29000
Once assigned, the vulnerability became visible through multiple vulnerability databases.
Examples include:
https://cvefeed.io/vuln/detail/CVE-2026-29000
https://vulnerability.circl.lu/vuln/cve-2026-29000
https://app.opencve.io/cve/CVE-2026-29000
These databases aggregate vulnerability information from the CVE program and provide additional context such as severity metrics, exploit details, and affected software versions.
At this stage the vulnerability transitions from a research finding into structured vulnerability intelligence.
Stage 4: Threat Intelligence Platforms
Threat intelligence platforms provide enriched vulnerability data to security teams and automated monitoring systems.
These platforms aggregate CVE information and supplement it with additional data including:
vulnerability classification (CWE mapping)
• exploit indicators
• attack patterns
• vendor advisories
For example, CVE-2026-29000 appears in threat intelligence platforms such as:
https://radar.offseq.com/threat/cve-2026-29000-cwe-347-improper-verification-of-cr-c33a53b1
This entry classifies the vulnerability under CWE-347: Improper Verification of Cryptographic Signature.
CWE classification helps security teams understand the root cause category of vulnerabilities and identify similar issues in other systems.
Another example is the EU vulnerability database maintained by ENISA:
https://euvd.enisa.europa.eu/enisa/EUVD-2026-9505
These platforms are particularly important because they feed vulnerability information into security tools used by enterprises worldwide.
Stage 5: National CERT Advisories
Many countries operate national cybersecurity agencies responsible for monitoring critical vulnerabilities affecting public and private infrastructure.
When severe vulnerabilities are disclosed, these agencies often publish advisories notifying organizations of potential risk.
For example, the Spanish cybersecurity agency INCIBE published an advisory referencing CVE-2026-29000:
https://www.incibe.es/incibe-cert/alerta-temprana/vulnerabilidades/cve-2026-29000
Advisories like these help organizations monitor vulnerabilities that may affect government services, financial systems, and critical infrastructure.
The presence of a vulnerability in national CERT advisories indicates that it has reached a level of significance where governments consider it relevant for defensive monitoring.
Stage 6: Security Media Coverage
Once a vulnerability appears in CVE databases and threat intelligence platforms, it often attracts attention from security journalists and researchers who analyze new vulnerabilities for broader audiences.
Security publications translate technical disclosures into accessible explanations that allow security teams to understand the potential impact.
Coverage of CVE-2026-29000 appeared in several outlets, including:
https://securityonline.info/critical-10-0-cvss-flaw-in-pac4j-jwt-lets-hackers-forge-admin-tokens/
https://www.thehackerwire.com/pac4j-jwt-authentication-bypass-via-forged-encrypted-jwts/
These articles summarize the vulnerability, describe the affected software, and provide guidance on mitigation.
Media coverage plays an important role because many organizations rely on curated security news sources rather than monitoring raw CVE feeds.
Stage 7: Vulnerability Aggregation Platforms
Security professionals frequently rely on vulnerability aggregation platforms to track newly disclosed vulnerabilities affecting their technology stacks.
Examples include:
https://vulners.com/cvelist/CVELIST:CVE-2026-29000
These platforms aggregate information from multiple vulnerability databases and provide searchable interfaces that allow security teams to monitor new vulnerabilities across thousands of software packages.
Some platforms also provide APIs that integrate directly with vulnerability scanners and SIEM systems.
This allows organizations to automatically detect when newly disclosed vulnerabilities affect their infrastructure.
Stage 8: Social and Community Amplification
Once a vulnerability has been published and referenced by security media, it often spreads through developer and security communities via social media and discussion forums.
For example, CVE announcements frequently appear on platforms such as:
https://bsky.app/profile/cve.skyfleet.blue/post/3mgbkx4u4ue2v
These discussions often include deeper technical analysis by security engineers who evaluate how the vulnerability affects real-world systems.
Community discourse plays an important role in vulnerability awareness because it often surfaces additional insights, exploit scenarios, or mitigation strategies.
Stage 9: Vulnerability Intelligence Feeds
Many security teams rely on automated vulnerability feeds that aggregate information from multiple sources and deliver updates in near real-time.
One example is Feedly’s vulnerability intelligence dashboard:
https://radar.offseq.com/threat/cve-2026-29000-cwe-347-improper-verification-of-cr-c33a53b1
These systems collect data from vulnerability databases, security advisories, and threat intelligence sources.
Organizations integrate these feeds into internal security monitoring systems to automatically detect when new vulnerabilities affect software dependencies.
Why This Pipeline Matters
The journey from vulnerability discovery to global security awareness highlights an important reality of modern cybersecurity.
Security research alone does not protect systems.
Protection depends on how quickly and effectively vulnerability information propagates through the ecosystem.
The vulnerability lifecycle typically follows this path:
Each stage ensures that the information reaches different audiences responsible for maintaining secure systems.
Lessons from CVE-2026-29000
The propagation of CVE-2026-29000 illustrates several broader trends in modern software security.
First, vulnerabilities in authentication frameworks can have particularly high impact because they affect identity verification mechanisms used across distributed systems.
Second, the speed at which vulnerability information spreads has increased significantly due to automated intelligence feeds and real-time security monitoring tools.
Third, the modern software supply chain relies heavily on open-source components, making it critical for organizations to track vulnerabilities across dependencies.
Finally, security research plays a foundational role in this ecosystem by identifying vulnerabilities before attackers exploit them at scale.
The Future of Vulnerability Intelligence
As software ecosystems continue to grow more complex, vulnerability intelligence systems will play an increasingly important role in defending infrastructure.
Future improvements may include:
automated vulnerability correlation across dependencies
• improved exploit detection signals
• machine-readable patch analysis
• automated risk prioritization based on runtime exposure
These capabilities will help organizations move beyond simple vulnerability detection toward more intelligent security posture management.
Final Take!
The lifecycle of CVE-2026-29000 illustrates how a single vulnerability discovered during security research can quickly become global security intelligence.
From the initial research disclosure to CVE assignment, vulnerability databases, threat intelligence platforms, national advisories, media coverage, and community discussions, the vulnerability information propagated through an interconnected ecosystem designed to alert organizations to emerging risks.
Understanding this pipeline is essential for security engineers responsible for maintaining the security of modern software systems.
Because in today’s interconnected world, the discovery of a vulnerability is only the beginning of the story.
Detect Vulnerabilities Before They Become CVEs
Security teams increasingly rely on automated tools to detect vulnerabilities before they reach the disclosure stage.
CodeAnt AI analyzes pull requests and codebases to identify security vulnerabilities, dependency risks, and insecure patterns before they reach production.
By catching vulnerabilities during development, engineering teams can fix issues long before they propagate through the global vulnerability intelligence ecosystem.
👉 Explore CodeAnt AI security analysis today!
FAQs
What is the vulnerability lifecycle in cybersecurity?
How does a vulnerability get a CVE identifier?
Why do vulnerabilities appear on multiple security platforms?
What role do threat intelligence platforms play in vulnerability management?
Why is responsible disclosure important for security research?















