In software security, there is a subtle but critical difference between:
fixing an exploit
and
fixing the vulnerability that made the exploit possible.
Many patches address only the exact payload that triggered the bug report, not the broader class of behavior that allowed the exploit to exist.
For attackers, this creates a predictable opportunity:
Once a patch is published, the vulnerability becomes easier to exploit, not harder.
Because the patch itself reveals where the security boundary exists.
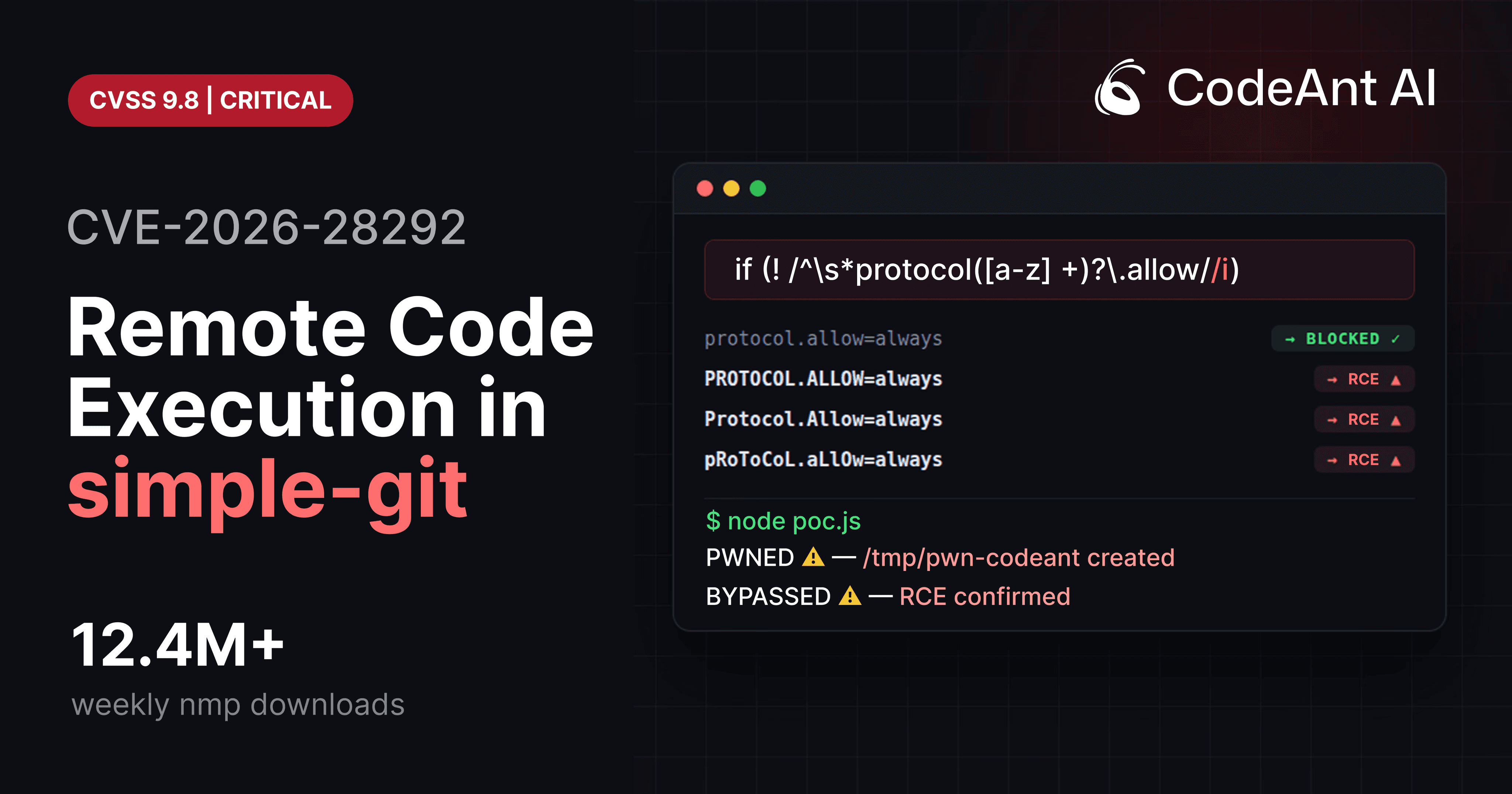
The remote code execution vulnerability CVE-2026-28292 in simple-git is a perfect illustration of this phenomenon.
The issue appeared in a library used by over 12 million weekly npm installations, and it bypassed two prior CVE patches intended to solve the same problem.
But the deeper story behind this vulnerability isn’t just about a missing regex flag.
It’s about how security patches are written, how attackers analyze them, and why most vulnerability fixes only close the exact door that was reported.
Understanding that dynamic is essential for building secure systems.
And it’s also one of the areas where AI-assisted code review is starting to reshape how vulnerabilities are discovered.
The Security Lifecycle of a Vulnerability
To understand why CVE-2026-28292 existed, we need to look at the timeline of fixes that preceded it.
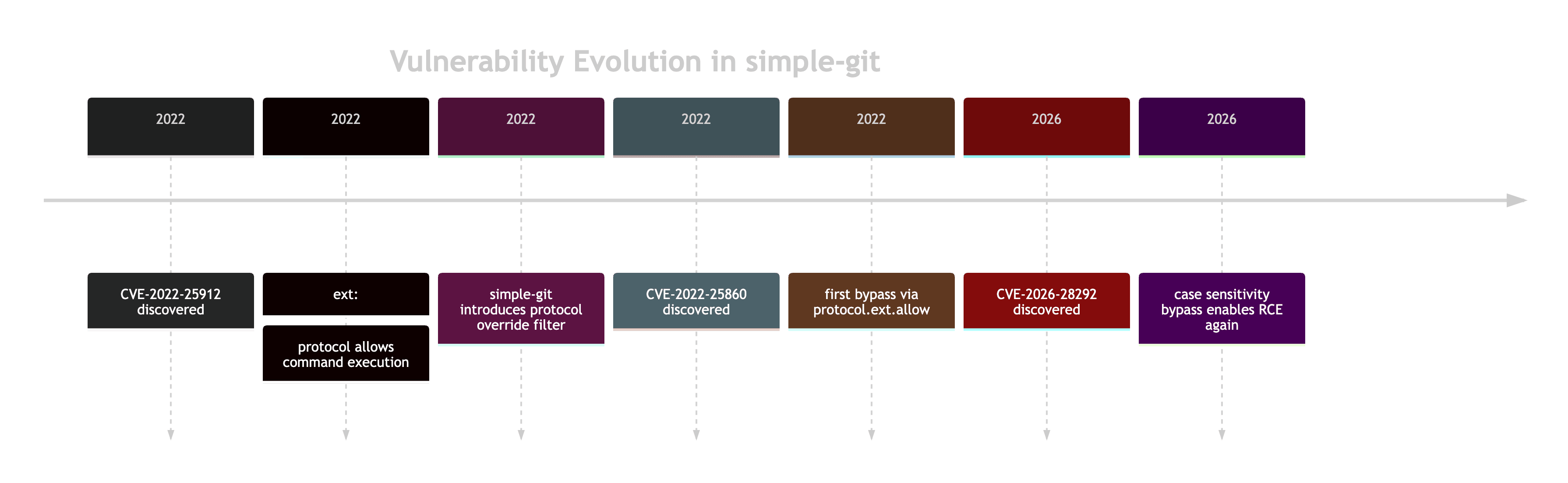
Each step followed the same pattern:
An exploit is discovered.
A patch blocks that specific exploit.
A slightly modified input bypasses the patch.
The vulnerability itself was never fully addressed.
Only the reported payloads were.
What the Original Security Patch Tried to Do
The simple-git maintainers introduced a plugin designed to prevent dangerous Git configuration overrides.
Simplified code:
The goal was to block arguments such as:
These configurations enable Git’s ext transport protocol, which allows command execution.
The patch worked for the exact payload that triggered the original CVE.
But the security control contained an assumption that turned out to be false.
The Assumption That Broke the Patch
The filter assumed Git configuration keys would appear in lowercase form.
The regex specifically matched:
But Git treats configuration keys as case-insensitive.
Example:
Git internally converts the key to lowercase.
So all of these are equivalent:
The regex only blocked the first.
This meant attackers could bypass the filter simply by changing the casing of the configuration key.
The Security Boundary Failure
The vulnerability arises from a mismatch between:
the security control
and
the system it protects
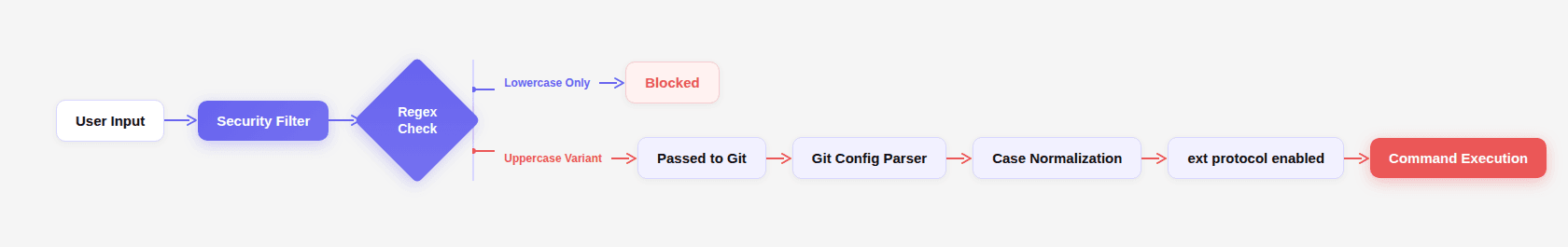
Because the filter assumed lowercase input, it failed to protect against alternate representations of the same configuration key.
This is a classic CWE-178: Improper Handling of Case Sensitivity vulnerability.
But the real lesson goes deeper.
How Attackers Actually Analyze Security Patches
When a security patch is released, attackers don’t just test the original exploit.
They analyze the patch itself.
The attacker workflow looks something like this:
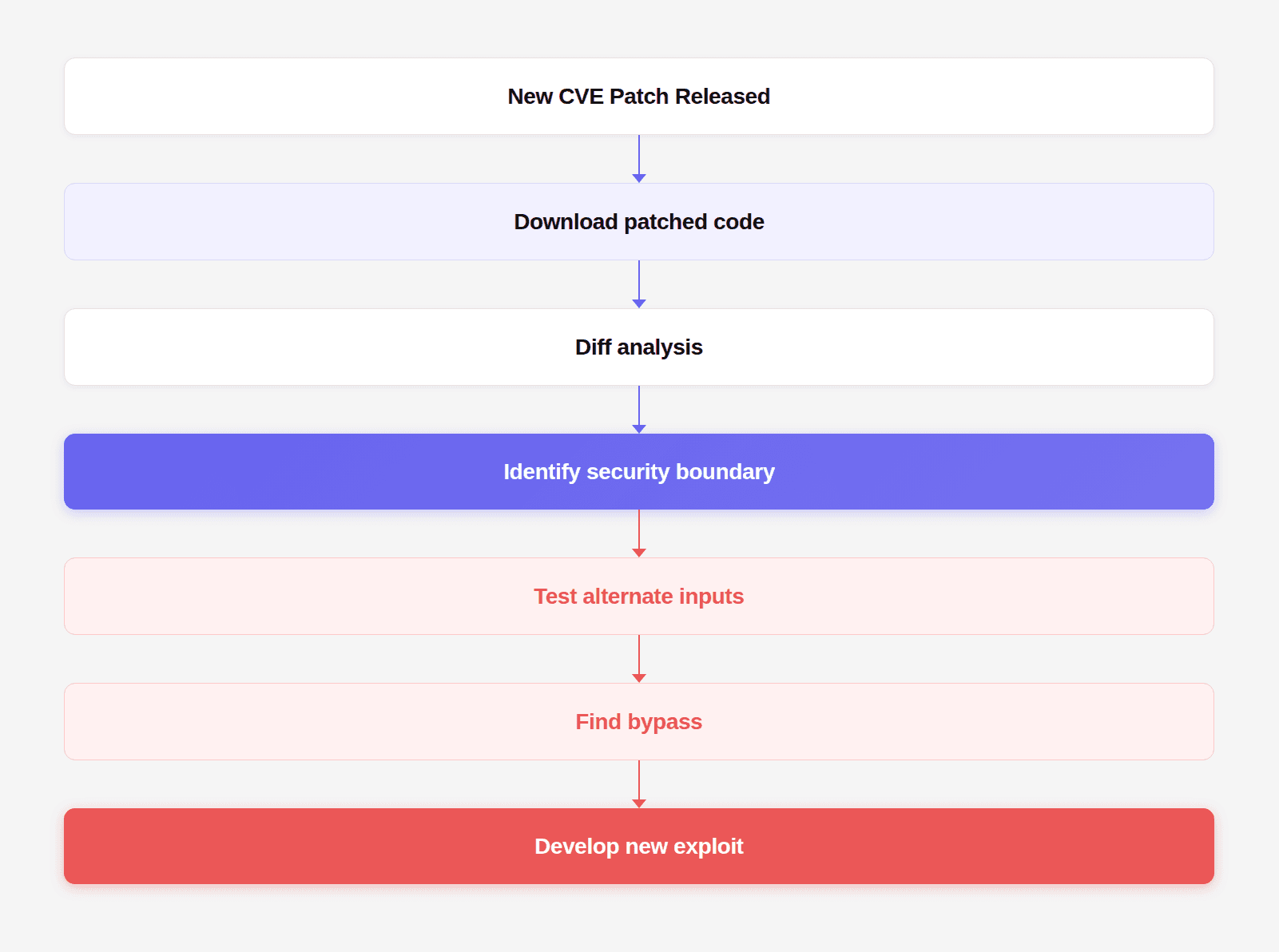
This process is called patch diffing, and it is one of the most common ways new vulnerabilities are discovered.
The moment a patch is released, the location of the security control becomes visible.
Attackers now know exactly where to probe.
Why Patches Often Only Fix the Reported Payload
Security patches are typically written under significant time pressure.
Maintainers need to:
protect users quickly
release a fix immediately
minimize breaking changes
So the patch usually targets the specific exploit demonstrated in the report.
Example:
Reported exploit:
Patch response:
Add filter blocking protocol.ext.allow.
But attackers rarely repeat the exact exploit.
They mutate the input.
Example mutations:
If the patch blocks only one representation of the input, the vulnerability remains.
The Difference Between Exploit Fixes and Vulnerability Fixes
A helpful way to understand this distinction is through the concept of attack surface reduction.
Exploit Fix
Blocks the exact payload.
Example:
Vulnerability Fix
Eliminates the entire class of behavior.
Example:
Or:
This difference is illustrated below.
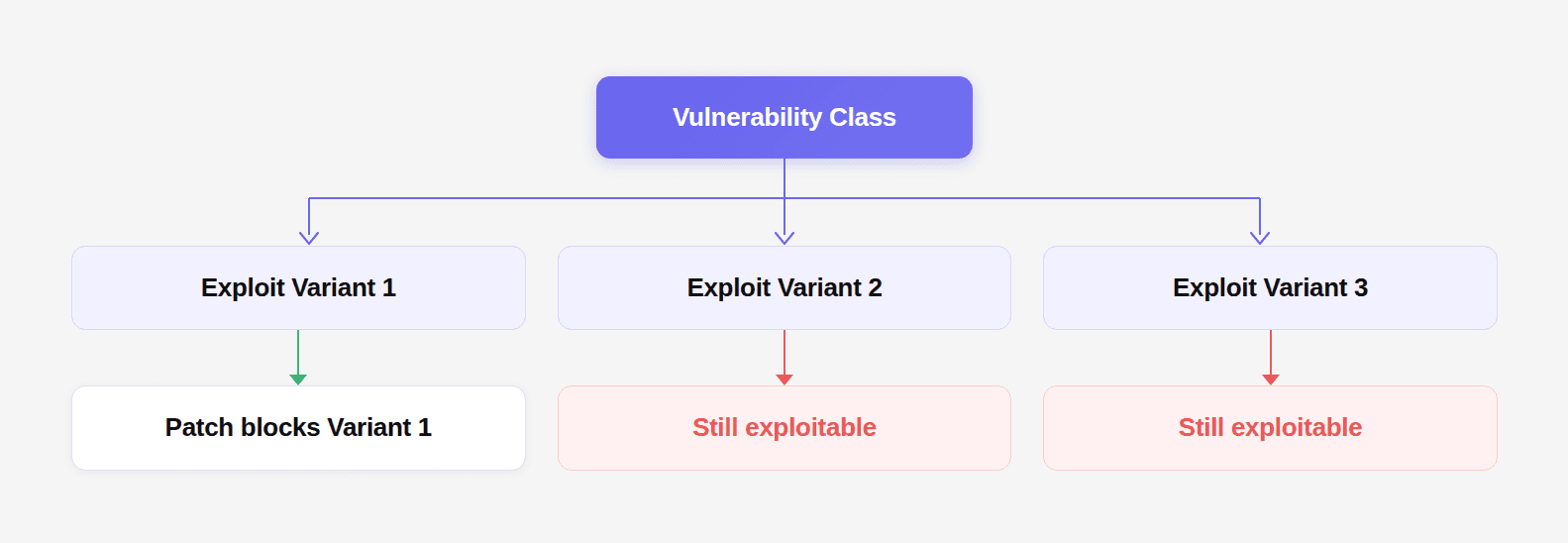
Fixing the exploit removes one branch.
Fixing the vulnerability removes the root.
The Real Root Cause of CVE-2026-28292
The actual vulnerability was not the missing /i flag.
It was the assumption that a regex filter could safely guard a security boundary without understanding the behavior of the system it protected.
Git configuration parsing includes:
case normalization
flexible key syntax
multiple configuration scopes
A regex filter guarding this system must account for all those behaviors.
Otherwise bypasses become inevitable.
Why Traditional Security Tools Miss These Bugs
Traditional SAST and SCA tools rely heavily on pattern detection.
They look for things like:
unsafe function calls
injection patterns
vulnerable dependencies
But CVE-2026-28292 required reasoning about:
regex semantics
Git configuration behavior
command execution paths
security boundary assumptions
This kind of vulnerability does not appear as a simple static pattern.
It emerges from how multiple components interact.
During internal research, CodeAnt AI’s code reviewer flagged the regex because it was protecting a case-insensitive system using a case-sensitive pattern, a subtle semantic mismatch that rule-based analysis tools typically cannot detect.
Read the full case here: https://www.codeant.ai/security-research/simple-git-remote-code-execution-cve-2026-28292
That observation ultimately led to the discovery of CVE-2026-28292.
This highlights a shift in what automated code review is starting to become.
Not just syntax checking.
But security reasoning across code paths.
How Developers Should Write Security Patches
The safest approach is to eliminate ambiguity entirely.
Example secure implementation:
Better still:
Avoid user-controlled Git arguments altogether.
Never pass untrusted input into:
A Safer Security Design Pattern
Security filters should follow a strict design pattern:
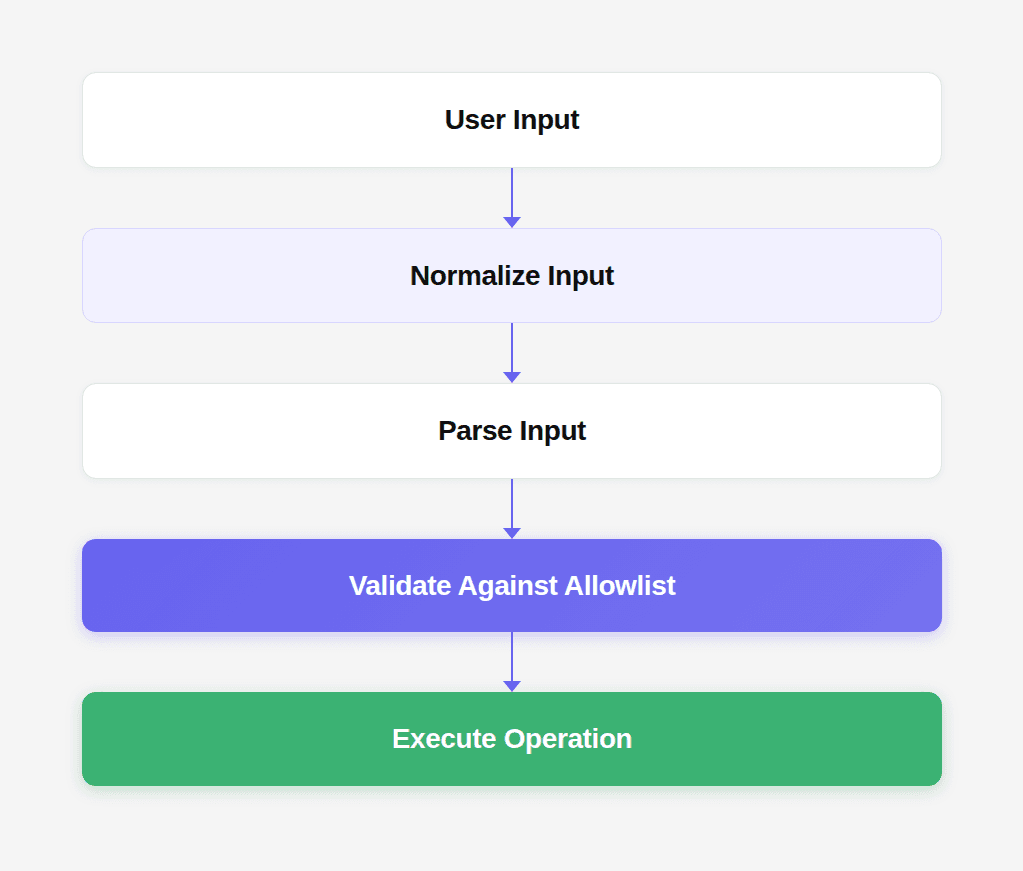
Key rule:
normalize first, validate second.
This prevents bypasses caused by alternate representations of the same input.
Why This Pattern Appears Everywhere
Case-sensitivity mismatches appear in many security systems.
Examples include:
System | Vulnerability Pattern |
|---|---|
Web filters |
|
File systems |
|
Auth systems |
|
HTTP headers |
|
In every case, the vulnerability exists because the security control and the underlying system treat input differently.
Why This Changes How Code Review Should Work
Most code review tools today optimize for developer productivity.
They suggest:
formatting improvements
refactoring opportunities
code simplifications
Those suggestions can be helpful.
But they rarely justify blocking a pull request.
The real value of a code review gate appears when it catches something much more serious:
an authentication bypass
a privilege escalation
a command injection
a security boundary failure
The kind of bug that would quietly ship to production if nobody noticed it.
The discovery of CVE-2026-28292 came from analyzing a patch and asking a deeper question:
does this security control actually work under all valid inputs?
That kind of reasoning is exactly where AI-assisted code analysis is beginning to change the landscape.
Instead of only matching patterns, systems like CodeAnt AI’s code reviewer evaluate whether security logic truly enforces the boundary it claims to protect.
And sometimes that reasoning reveals vulnerabilities that have already been patched, but not actually fixed.
Conclusion
The story of CVE-2026-28292 is not just about a missing /i flag. It’s about how vulnerabilities survive even after patches are released.
Security fixes often focus on the exploit that triggered the report. But attackers rarely repeat the exact exploit.
They mutate the input.
They analyze the patch.
They search for alternate paths around the control.
And when the patch blocks only the reported payload instead of addressing the underlying vulnerability class, the system remains exploitable.
This dynamic explains why vulnerabilities frequently appear as bypasses of earlier fixes. It also highlights why the next generation of automated code review tools must move beyond stylistic suggestions and surface-level analysis.
The real value of a code review gate is not catching naming conventions or formatting issues.
It’s catching the vulnerability nobody has documented yet.
The one hidden behind an assumption.
The one buried inside a security patch that looks correct at first glance.
Because when a single regex flag can separate a secure system from remote code execution across millions of installations, the difference between helpful feedback and truly valuable code review becomes very clear.
FAQs
Why do security patches often introduce bypasses?
What is patch diffing and why do attackers use it?
What is the core lesson from CVE-2026-28292?
How can developers avoid patch bypass vulnerabilities?
Why are AI-assisted code review tools better at detecting these issues?