Software security failures rarely happen because developers do not care about security.
Most vulnerabilities emerge in codebases written by experienced engineers, reviewed by multiple developers, and protected by static analysis tools and dependency scanners.
Yet critical vulnerabilities still slip through.
Sometimes they persist for years.
One recent example illustrates this phenomenon clearly: CVE-2026-28292, a remote code execution vulnerability discovered in the widely used Node.js Git library simple-git.
The bug was not hidden deep inside a complex algorithm.
It was not buried in thousands of lines of obscure code.
It was sitting inside a single regular expression in a security filter.
The code had already been reviewed.
It had already been patched twice in response to earlier CVEs.
And yet the vulnerability remained exploitable.
The reason is not simply a missing character in a regex.
The deeper explanation is that security bugs often hide in places where the code appears correct at first glance.
Understanding why that happens is critical for both developers and security engineers.
The Vulnerability That Looked Correct
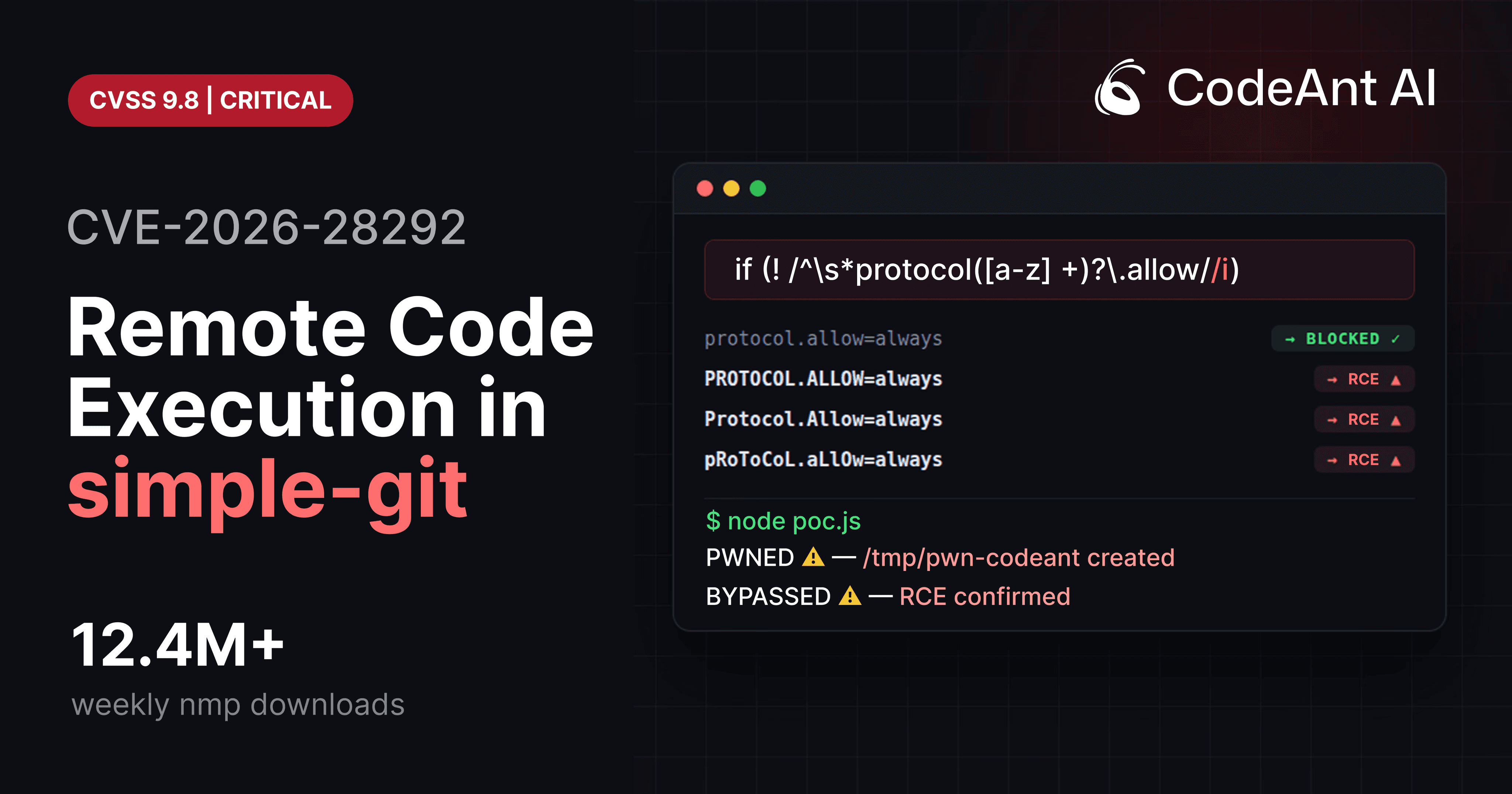
The root cause of CVE-2026-28292 was a regular expression used to block dangerous Git protocol overrides.
Simplified version of the filter:
The purpose of this check was to block configuration overrides like:
These settings enable Git’s ext transport protocol, which allows arbitrary command execution.
The filter seemed reasonable.
It matched the expected configuration keys and blocked them.
But the filter had one subtle problem.
Git configuration keys are case-insensitive.
The regex was case-sensitive.
That mismatch created a bypass.
An attacker could simply write:
The regex would not match.
Git would normalize the key internally and apply it.
The dangerous protocol would be enabled.
And a malicious ext:: URL could execute arbitrary commands.
This vulnerability ultimately became CVE-2026-28292, affecting a library with more than 12 million weekly downloads.
But the interesting question is not how the bug worked.
The interesting question is why nobody noticed it earlier.
Why Security Bugs Look Safe
Security bugs often appear safe because they satisfy the developer’s mental model of the system.
Developers write validation logic based on assumptions about how inputs behave.
But those assumptions may not match the behavior of the underlying system.
When that happens, the code may look perfectly correct while still being exploitable.
This pattern appears across many classes of vulnerabilities.
Mismatched System Semantics
In CVE-2026-28292, the developer assumed configuration keys would appear exactly as written.
But Git interprets configuration keys differently.
Diagram of the mismatch:

The filter and the system did not agree about how inputs should be interpreted.
This type of bug is extremely common in security engineering.
The Psychology of Security Blind Spots
The reason these vulnerabilities persist often has more to do with human cognition than with code complexity.
Developers reviewing security controls often focus on whether the check exists, not whether the check fully covers the problem.
When reading the regex in the simple-git plugin, most reviewers likely saw something like this:
It clearly matches protocol.allow.
It clearly matches protocol.ext.allow.
At first glance, it looks correct.
Once the brain forms that conclusion, reviewers often stop questioning the assumption.
This phenomenon is known as cognitive closure.
When developers believe they have understood a piece of code, they stop searching for alternative interpretations.
Security Bugs Thrive in Familiar Patterns
Another reason vulnerabilities hide in plain sight is that they appear inside familiar coding patterns.
Regex-based filters are extremely common in application security.
Examples include:
path traversal filters
SQL injection filters
HTML sanitization rules
command injection filters
Because developers see these patterns frequently, they often assume they are correct.
But regex-based security controls are notoriously fragile.
Even small variations in input can bypass them.
Example:
Matches only lowercase characters.
But the system being protected may treat uppercase characters identically.
The filter appears to cover the attack surface.
In reality, it does not.
The Problem with Patch-Driven Security
Another reason vulnerabilities like CVE-2026-28292 persist is the way security patches are typically written.
When a vulnerability is reported, the maintainer focuses on reproducing the attack.
Once the reproduction case is blocked, the fix is considered complete.
But attackers rarely stop at the first exploit.
They explore variations.
Diagram of the typical patch lifecycle:
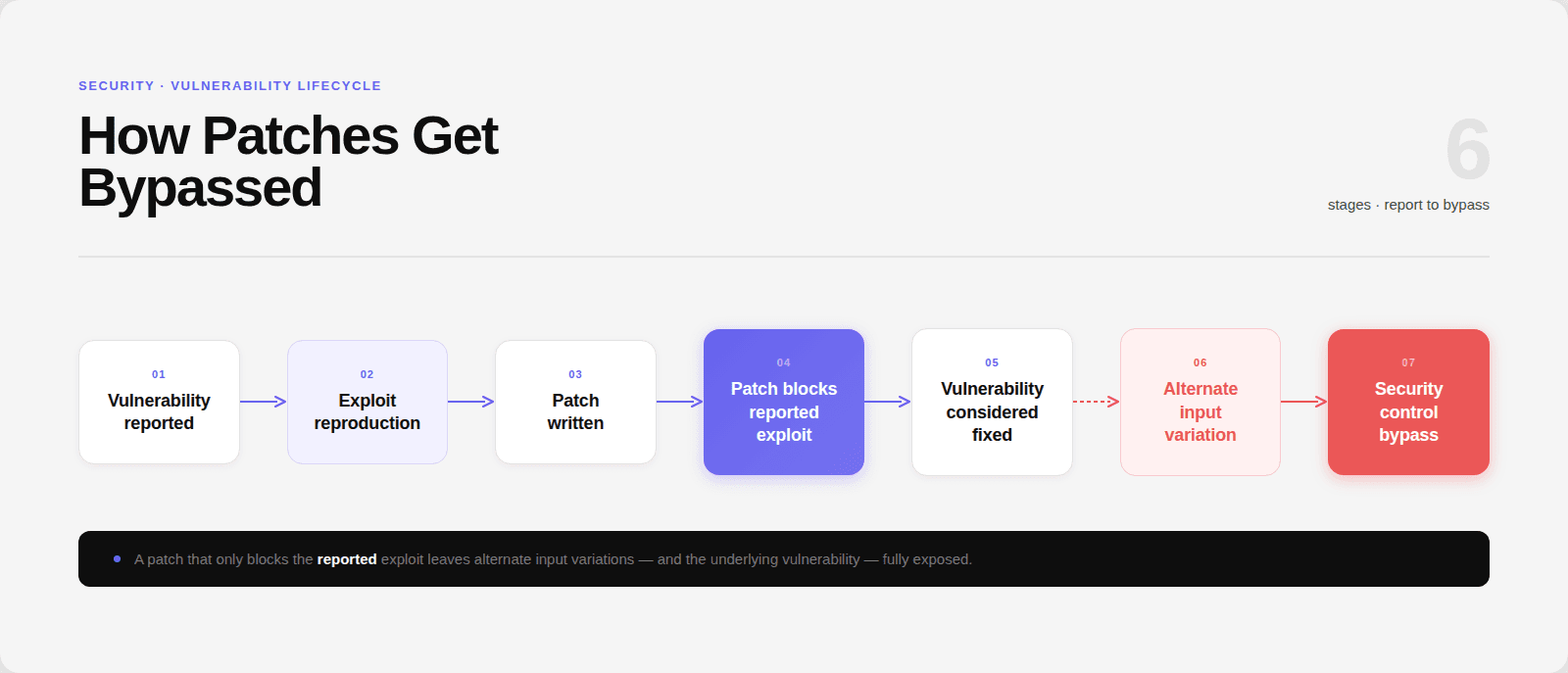
In the case of simple-git, two earlier CVEs had already attempted to block the dangerous protocol override.
But the patch focused on specific input patterns, not the underlying security property.
The regex blocked lowercase input.
But uppercase variants remained valid.
When Security Tools Miss the Problem
Modern development pipelines rely heavily on automated security tools.
These tools are extremely effective at detecting known issues.
But they often struggle with semantic vulnerabilities.
For example:
Tool | Detection result |
|---|---|
npm audit | No detection |
Dependabot | No detection |
Snyk | No detection |
Semgrep | No detection |
SonarQube | No detection |
These tools failed to detect CVE-2026-28292 for a simple reason.
They are designed to detect known patterns.
But this vulnerability required reasoning about several interacting concepts:
Git configuration parsing
case sensitivity
regex filtering
protocol overrides
command execution
That chain of reasoning is difficult for traditional static analysis.
Why AI Code Review Changes the Equation
This vulnerability was discovered during internal security research using CodeAnt AI’s code reviewer, which analyzes code not only for patterns but also for semantic inconsistencies in security logic.
The AI reviewer flagged the regex because it recognized that:
the regex used
[a-z]the filter guarded a Git configuration key
Git configuration keys are case-insensitive
That combination created a logical mismatch.
The tool did not recognize a known vulnerability signature.
Instead, it identified a security assumption that did not hold true.
This is precisely the type of reasoning that traditional code review tools struggle with.
For years, most automated code review tools have focused on small improvements such as style suggestions or refactoring hints.
But developers do not rely on code review tools to improve indentation.
They rely on them to catch the rare bug that could compromise an entire system.
The discovery of CVE-2026-28292 illustrates what happens when code review tools start focusing on that deeper goal.
Why These Vulnerabilities Are Increasing
As software ecosystems grow more complex, vulnerabilities increasingly emerge from interactions between components, not from obvious coding errors.
Modern systems combine:
third-party libraries
language runtimes
command-line tools
configuration systems
container environments
Each component may interpret inputs differently. Diagram of the modern attack surface:
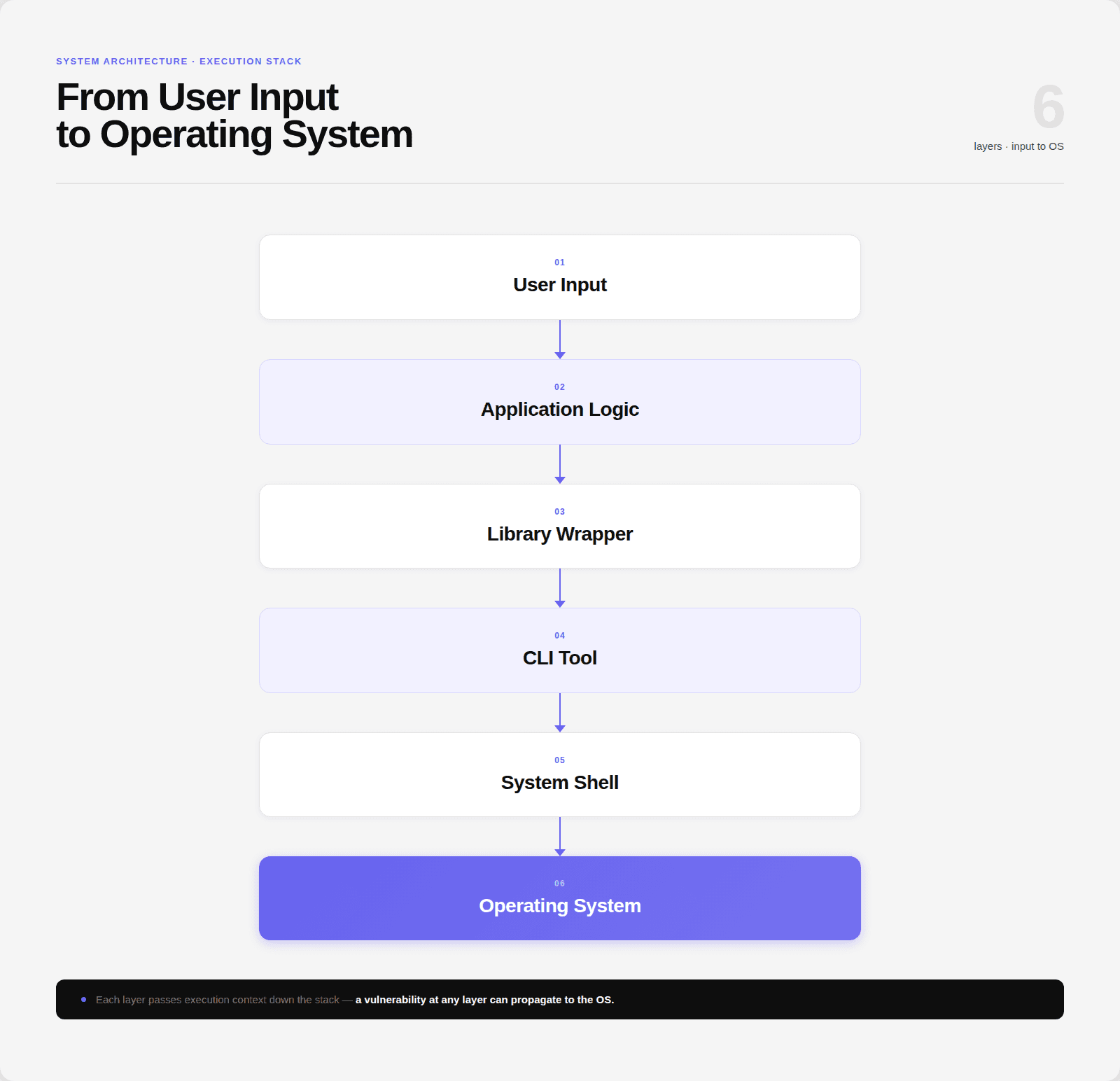
Security controls implemented at one layer may fail if the next layer behaves differently.
That is exactly what happened in the simple-git vulnerability.
Practical Lessons for Developers
The story of CVE-2026-28292 offers several practical lessons for developers building security-sensitive systems.
Normalize inputs before validation
Always normalize inputs before applying security checks.
Example:
Normalization removes ambiguity.
Avoid regex-only security filters
Regex can be useful, but relying on it alone for security controls is risky.
Explicit parsing and strict allowlists are safer.
Understand the behavior of underlying systems
If your code interacts with external systems such as Git, shells, or databases, you must understand how those systems interpret inputs.
Differences in parsing rules frequently lead to vulnerabilities.
Test security controls with input variations
Always test filters with:
uppercase input
mixed-case input
encoded characters
alternate syntax
These variations often reveal bypasses.
Conclusion: The Bugs That Matter Most
Security vulnerabilities rarely appear in places where developers expect them.
They hide in code that looks correct.
They hide in assumptions that nobody questions.
And they hide in subtle differences between how systems interpret inputs.
The vulnerability behind CVE-2026-28292 was not a complex exploit chain. It was a tiny mismatch between a security filter and the system it protected. Yet that mismatch allowed remote code execution across millions of installations.
This is precisely the kind of vulnerability that code review is supposed to catch.
Not formatting issues.
Not naming conventions.
But the one bug that could compromise an entire system.
During internal research, CodeAnt AI’s code reviewer identified the semantic mismatch that led to CVE-2026-28292, demonstrating how AI-assisted code analysis can uncover vulnerabilities that rule-based tools overlook.
As software systems grow more complex, the future of code review will likely depend less on stylistic suggestions and more on identifying deep security flaws hidden inside otherwise correct code.
Because the most dangerous vulnerabilities are rarely the ones that look suspicious.
They are the ones that look perfectly safe.
FAQs
What makes CVE-2026-28292 a particularly dangerous vulnerability?
Why do vulnerabilities like this remain undiscovered for so long?
Are regex-based security filters inherently insecure?
Why didn’t automated security tools detect CVE-2026-28292?
How can AI code review help detect hidden vulnerabilities like this?