Software security vulnerabilities often follow a predictable lifecycle.
A vulnerability is discovered.
A fix is implemented.
A CVE is assigned.
The patch is released.
Everyone assumes the problem is solved.
But in practice, the story rarely ends there.
Security history is full of vulnerabilities that were patched multiple times before they were truly fixed. The first patch fixes the reported exploit. The second patch fixes a bypass. The third patch finally addresses the root cause.
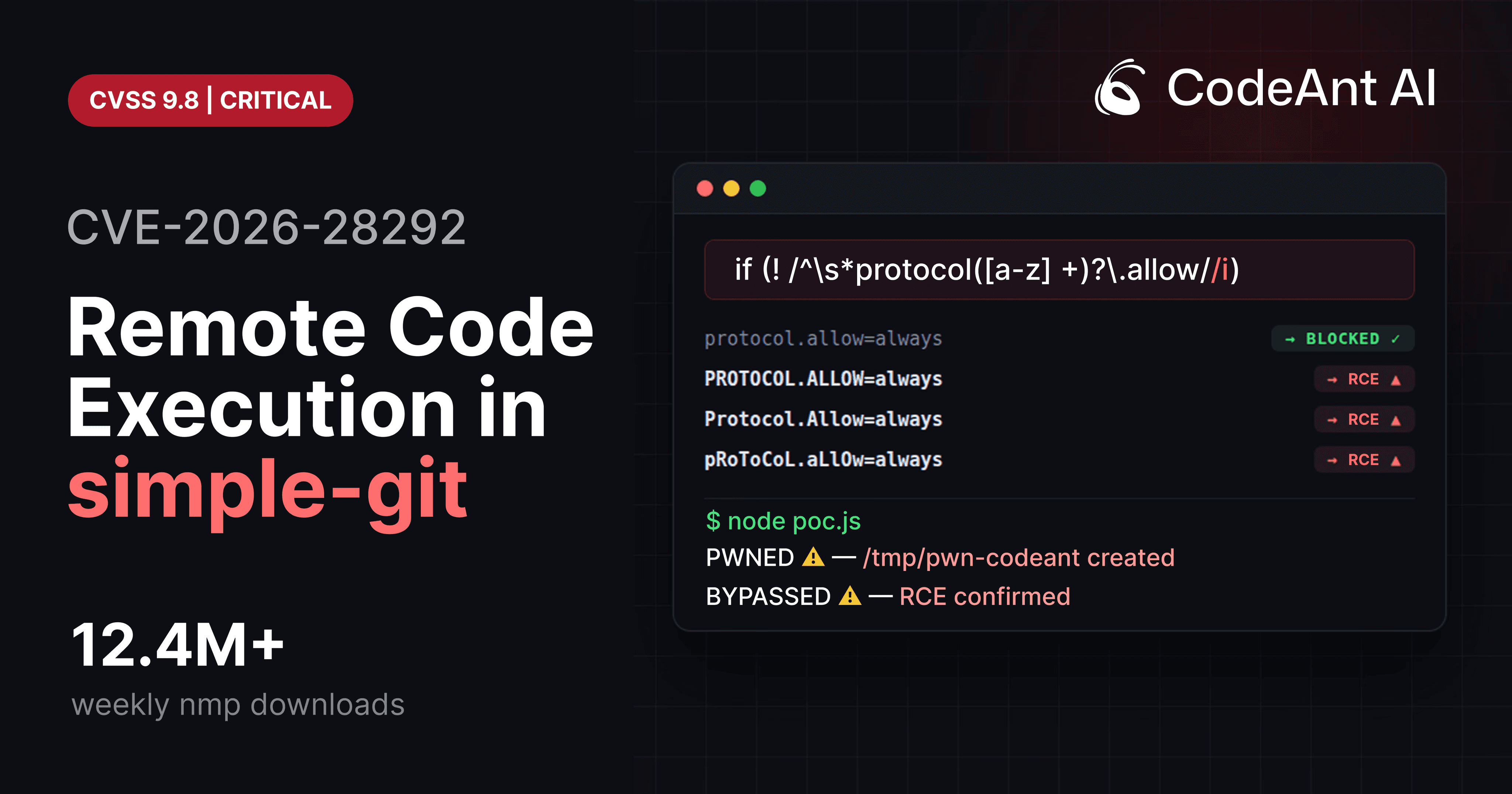
The vulnerability CVE-2026-28292, discovered in the Node.js library simple-git, is a perfect example of this pattern. The library had already patched a critical remote code execution vulnerability twice. Yet a subtle flaw remained in the security control, allowing attackers to bypass the protection entirely and achieve full command execution on the host system.
The bug itself was small: a case-sensitive regex protecting a case-insensitive system.
But the real lesson is much larger.
Security patches often fail because they fix the exploit, not the vulnerability.
Understanding why that happens is essential for developers, security engineers, and anyone responsible for maintaining modern software supply chains.
The Patch That Looked Correct
To understand the failure in CVE-2026-28292, we need to look at the patch that was originally supposed to prevent the attack. The vulnerability involved Git’s ext transport protocol, which allows Git to execute arbitrary commands.
Example:
This command causes Git to execute the shell command inside the transport string. Because this feature is dangerous when user input is involved, the maintainers of simple-git added a protection layer. The filter attempted to block configuration overrides that enable dangerous protocols.
Simplified version:
At first glance this looks correct. It checks for configuration keys such as:
If detected, the operation is blocked. But there is a problem hiding inside the regex.
The Root Cause of CVE-2026-28292
The regex used the character class:
Which means it only matches lowercase characters. Git configuration keys, however, are case insensitive. This means Git treats these values as identical:
The filter only caught the first. Everything else bypassed it. This mismatch created the bypass exploited in CVE-2026-28292.
Visualizing the Patch Failure
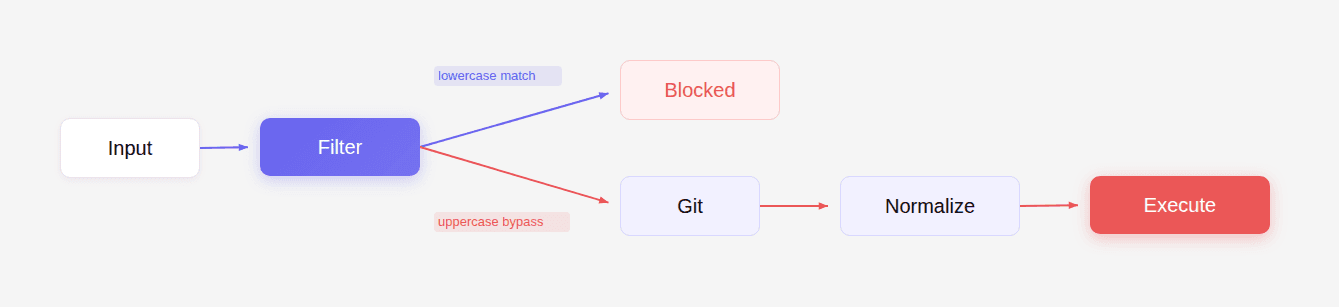
The filter assumed lowercase.
Git normalized input internally.
Attackers exploited the difference.
Why Patch Failures Are So Common
The failure seen in CVE-2026-28292 is not unusual. Security patches fail frequently because developers focus on reproducing the reported exploit, not on analyzing the full vulnerability class. When a vulnerability report arrives, developers typically follow this process:
But attackers think differently.
Attackers ask:
What assumptions does the patch make?
How can those assumptions be violated?
This difference in mindset leads to bypasses.
The Patch-Exploit Cycle
Security patches often go through several stages.
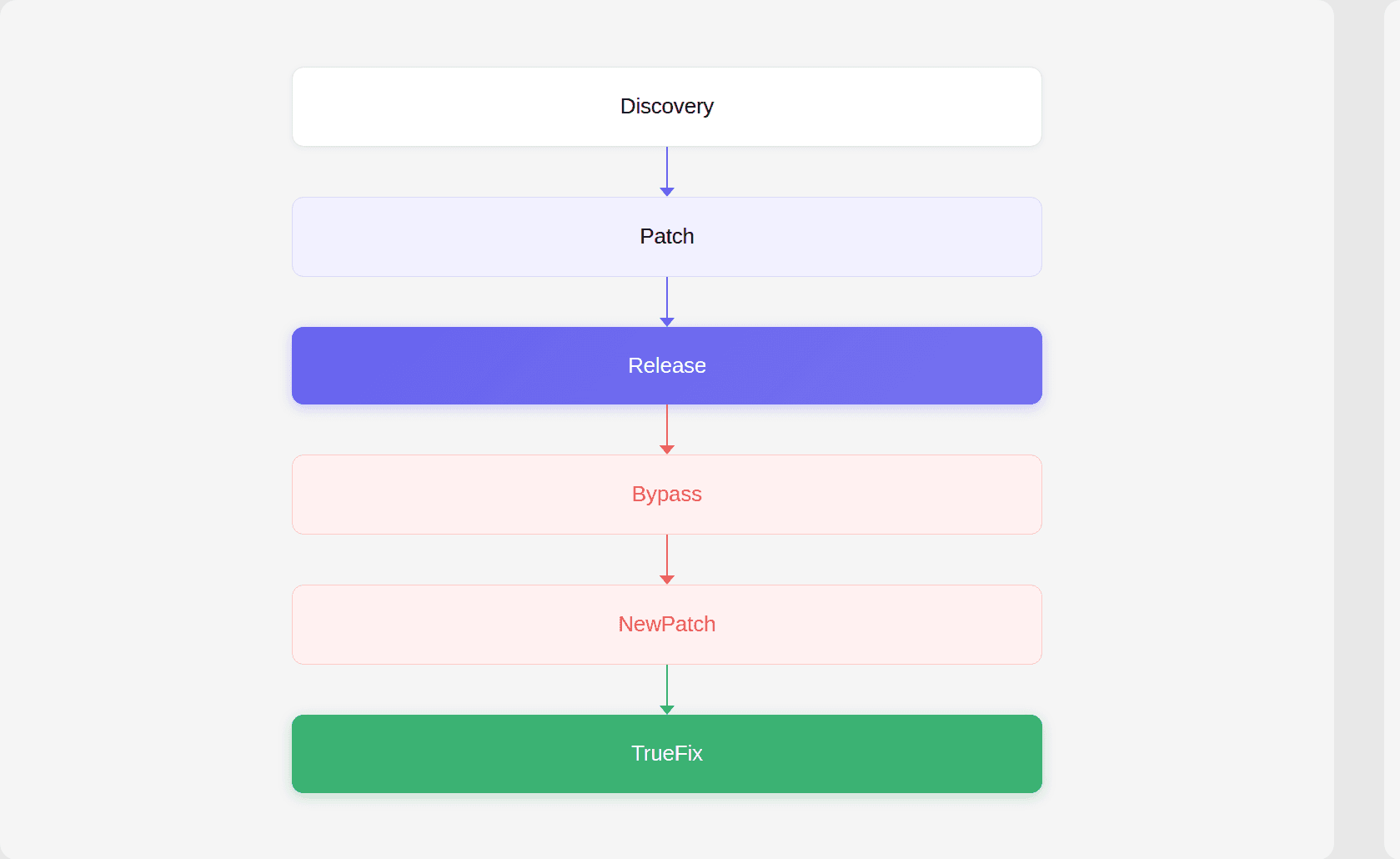
This cycle appears repeatedly across the security landscape.
Apache Struts (Equifax breach)
The famous Equifax breach originated from a vulnerability in Apache Struts.
The vulnerability involved unsafe handling of OGNL expressions.
Multiple patches were released before the issue was fully understood.
The patch addressed the original exploit but did not block all ways of triggering expression evaluation.
Attackers discovered alternative payloads.
Eventually the vulnerability resulted in one of the largest data breaches in history.
Log4Shell
The Log4j Log4Shell vulnerability also demonstrated patch failure.
Initial patch:
The patch disabled some lookup patterns. Researchers quickly discovered bypasses. Follow-up patches were released:
Each patch addressed additional attack vectors. The root cause involved unsafe lookup functionality embedded deep in the logging framework.
sudo Baron Samedit vulnerability
The sudo vulnerability CVE-2021-3156 also experienced patch bypasses during early mitigation attempts. The issue involved heap overflow conditions triggered by argument parsing. Early mitigations attempted to sanitize inputs without addressing the deeper memory handling flaw.
The Pattern: Fixing the Exploit Instead of the Bug
These examples reveal a recurring pattern.
Security patches frequently fix the specific exploit payload rather than the underlying vulnerability class.
This happens because:
Security reports typically include a working exploit.
Developers focus on reproducing that exploit.
The patch blocks the exploit path.
Other attack paths remain.
In the case of CVE-2026-28292, the exploit path involved lowercase configuration keys. The patch protected against lowercase input. But it did not consider that Git treats configuration keys as case-insensitive.
The Deeper Problem: Security Assumptions
Security patches often fail because they embed implicit assumptions.
Common assumptions include:
input will use a specific format
values will be lowercase
encoding will be predictable
paths will follow expected structure
Attackers deliberately violate these assumptions. For example:
Assumption | Attacker bypass |
|---|---|
input lowercase | uppercase |
normalized paths | alternate separators |
ASCII input | unicode |
single encoding | double encoding |
The vulnerability in CVE-2026-28292 emerged from exactly this type of assumption. Wanna deep dive? Check our full research case here.
Security Filters vs System Behavior
Another way to understand patch failures is through system-filter mismatch. Security filters often operate at the application level, while the underlying system behaves differently.
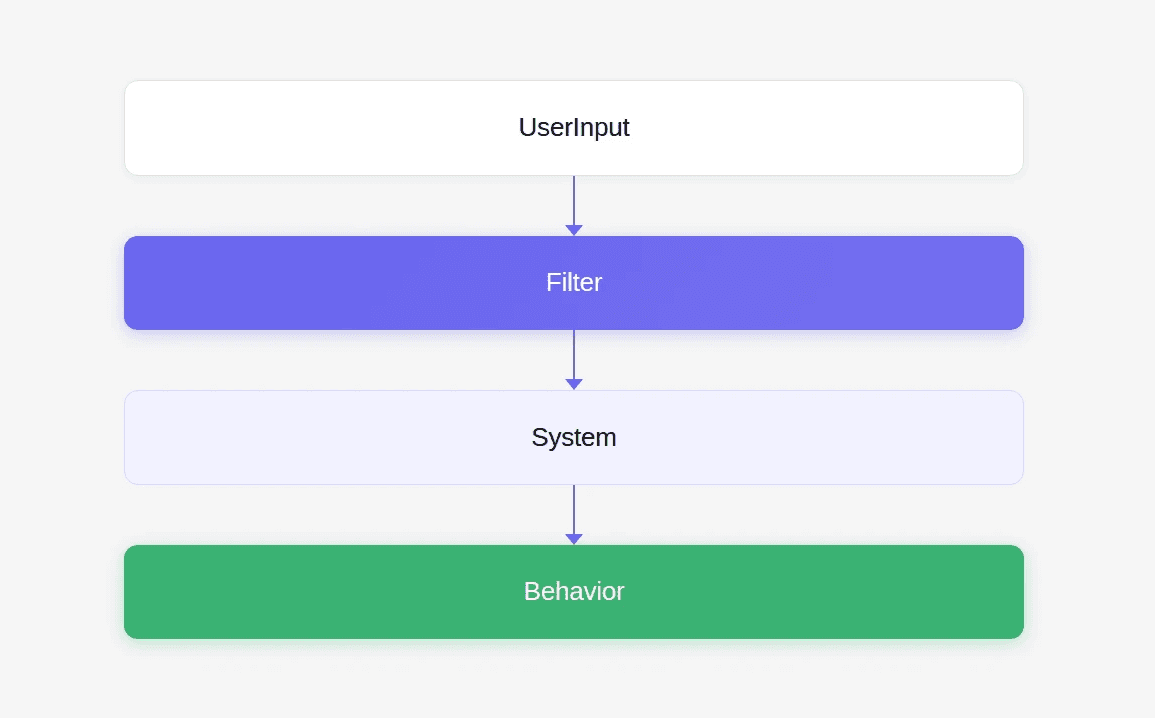
If the filter assumes different semantics than the system, bypasses become possible.
Examples:
Filter | System |
|---|---|
case sensitive regex | case insensitive config |
path sanitization | filesystem normalization |
HTML filter | browser parsing |
URL validation | server routing |
These mismatches create security gaps.
Why Traditional Security Tools Miss Patch Failures
Static analysis tools typically rely on predefined rules. For example:
But patch failures often involve contextual logic flaws, not unsafe APIs. The vulnerability in CVE-2026-28292 required understanding:
Git configuration semantics
regex case sensitivity
argument injection
protocol enablement
command execution
Most rule-based tools cannot reason across these layers. This is where AI-assisted code analysis becomes useful. During internal research, CodeAnt AI’s code reviewer analyzed patch diffs and surrounding code paths, identifying semantic inconsistencies that traditional tools overlooked.
The AI flagged the regex because it protected a case-insensitive system using a case-sensitive filter. That observation led directly to the discovery of CVE-2026-28292.
How to Audit Security Patches Properly
Developers and security engineers can avoid patch failures by following a more rigorous analysis process.
Instead of asking:
Does the patch block the exploit?
Ask:
Does the patch eliminate the vulnerability class?
Patch Review Framework
A useful framework for auditing patches is:
Step 1: Identify the Security Boundary
Determine what the patch is protecting.
Examples:
In CVE-2026-28292, the boundary was protocol override protection.
Step 2: Analyze the Patch Logic
Study the patch implementation.
Example regex filter:
Look for potential weaknesses:
case sensitivity
partial matches
encoding assumptions
string manipulation
Step 3: Compare with System Semantics
Understand how the protected system behaves.
Example:
Mismatch identified.
Step 4: Generate Variant Inputs
Test alternative inputs:
This step would reveal the bypass used in CVE-2026-28292.
Step 5: Attempt Exploit Reconstruction
Attempt to recreate the exploit path.
Example PoC:
If command execution occurs, the patch failed.
Why AI Helps With Patch Analysis
Patch analysis is extremely time consuming. Large ecosystems contain millions of packages and thousands of CVEs. Manually reviewing every patch is impossible. AI-assisted code analysis allows researchers to:
scan patch diffs
analyze surrounding code paths
detect logical inconsistencies
surface suspicious security patterns
In the research that uncovered CVE-2026-28292, AI was used to analyze packages with prior CVEs and identify patches that might still contain bypasses.
This approach revealed a surprising pattern:
Many patches fixed the reported exploit but left variant attack paths open.
The Future of Code Review
This observation leads to a broader point about the future of code review. Today, many AI code review tools focus on developer productivity:
style fixes
formatting suggestions
refactoring hints
These improvements are helpful but not transformational. The true value of code review lies in catching high-impact vulnerabilities before they ship. The moment a code review tool blocks a pull request because it detected a critical logic flaw is the moment developers truly appreciate it.
The discovery of CVE-2026-28292 demonstrates how automated reasoning tools can analyze patch logic and identify vulnerabilities that humans and rule-based scanners might miss.
That capability will become increasingly important as software supply chains continue to grow in complexity.
The Real Lesson of CVE-2026-28292
The vulnerability itself was simple. A missing /i flag. But the implications are profound. A security control existed. A patch had already been applied. Yet the vulnerability remained exploitable.
This is the core problem with many modern security workflows. We assume that once a patch is released, the vulnerability is solved. In reality, the first patch is often just the beginning.
The real fix comes when someone steps back and asks a different question: Did we fix the exploit, or did we fix the vulnerability?
FAQs
Why do security patches frequently fail to fully fix vulnerabilities?
How did CVE-2026-28292 bypass previous security patches?
Why didn’t traditional security tools detect the vulnerability?
What can developers do to prevent patch bypass vulnerabilities?
How does AI-assisted code analysis help detect vulnerabilities like CVE-2026-28292?