Cloud misconfigurations do not become critical because they exist. They become critical when they connect.
A public bucket, weak IAM permission, exposed API, leaked CI/CD secret, or SSRF bug may look isolated during a posture scan. But attackers do not think in isolated findings. They think in paths.
That is why cloud attack path testing is becoming one of the most important parts of modern AI pentesting for AWS, Azure, and GCP.
This guide walks through practical cloud exploit chains, how to validate them safely, what evidence to collect, and how automated penetration testing platforms should prove real risk instead of only reporting misconfigurations.
Cloud Attack Path Testing Vs Cloud Posture Scanning
Cloud posture scanning asks:
Is this bucket public?
Is this role over-permissioned?
Is this service exposed?
Is this security group too open?
Cloud attack path testing asks:
Can this exposure be exploited?
What identity can the attacker reach?
What data becomes accessible?
Can this issue chain with another weakness?
What is the proof of impact?
Area | Cloud posture scanning | Cloud attack path testing |
|---|---|---|
Focus | Misconfiguration detection | Exploitability validation |
Output | Alerts | Proof of attack path |
Context | Asset-level | System-level |
Severity | Rule-based | Impact-based |
Best use | Baseline hygiene | Real risk validation |
Attack Path 1: SSRF To Cloud Metadata Credentials
This is one of the strongest technical sections.
Scenario
A web application has an SSRF vulnerability that allows requests to internal metadata services.
AWS example
If IMDSv1 is enabled or metadata protections are weak, the attacker may retrieve role names.
The response may expose temporary credentials.
Why this matters
The SSRF alone is not the full issue. The real risk depends on what the attached role can access.
Validation step
Finding table
Evidence | Result |
|---|---|
SSRF endpoint | Confirmed |
Metadata access | Confirmed |
Temporary credentials retrieved | Confirmed |
Role permissions validated | Confirmed |
Business impact | Depends on reachable data |
Remediation
Also reduce instance role permissions to least privilege.
Attack Path 2: Public Storage Bucket To Customer Data Exposure
Scenario
A storage bucket is publicly readable and contains customer exports.
AWS test
Azure test
For anonymous access testing, check public blob URLs without credentials.
GCP test
What proof should include
Do not reproduce sensitive data unnecessarily. Evidence should describe exposure safely.
Evidence type | Safe reporting approach |
|---|---|
File names | Include limited examples |
Customer data | Describe fields, do not dump records |
Access level | Public read confirmed |
Impact | Customer export exposure |
Remediation | Remove public access and rotate links |
Remediation example
For AWS S3:
Attack Path 3: CI/CD Secret Exposure To Cloud Account Access
Scenario
A CI/CD environment leaks a cloud access key through logs, environment variables, or build artifacts.
Example leaked .env:
Validation
Why AI pentesting helps
AI-powered testing can correlate:
exposed build artifacts
Git history
CI/CD logs
cloud permissions
reachable production assets
Manual testers can do this too, but AI-assisted workflows can repeat it continuously across deployments.
Remediation
Revoke exposed key
Rotate all dependent secrets
Remove secrets from CI logs
Use OIDC-based short-lived credentials
Add secret scanning in CI/CD
Example GitHub Actions OIDC direction:
Attack Path 4: Over-Permissioned IAM Role To Privilege Escalation
Scenario
A role has permissions that allow it to pass or attach higher-privilege roles.
Risky AWS policy example:
Exploit concept
An attacker creates a Lambda function and attaches a privileged role to it.
Validation checklist
Can the identity pass roles?
Which roles can be passed?
Can it create compute resources?
Can it invoke those resources?
What permissions do those resources inherit?
Safer remediation
Restrict iam:PassRole to specific approved roles.
Attack Path 5: Public Kubernetes Endpoint To Secret Access
Scenario
A Kubernetes API server or dashboard is exposed.
Discovery
Risk indicators
Public API server
Weak RBAC
Exposed dashboard
Service account token abuse
Secrets mounted into pods
Validation
Remediation
Restrict API server access
Enforce RBAC least privilege
Disable anonymous access
Rotate service account tokens
Limit secret mounting
Use private clusters where possible
How CodeAnt AI Would Validate Cloud Attack Paths
CodeAnt AI is a defensive plus offensive security platform.
For cloud attack path testing, that matters because cloud exploits often move across layers:
code
APIs
CI/CD
identities
cloud services
external exposure
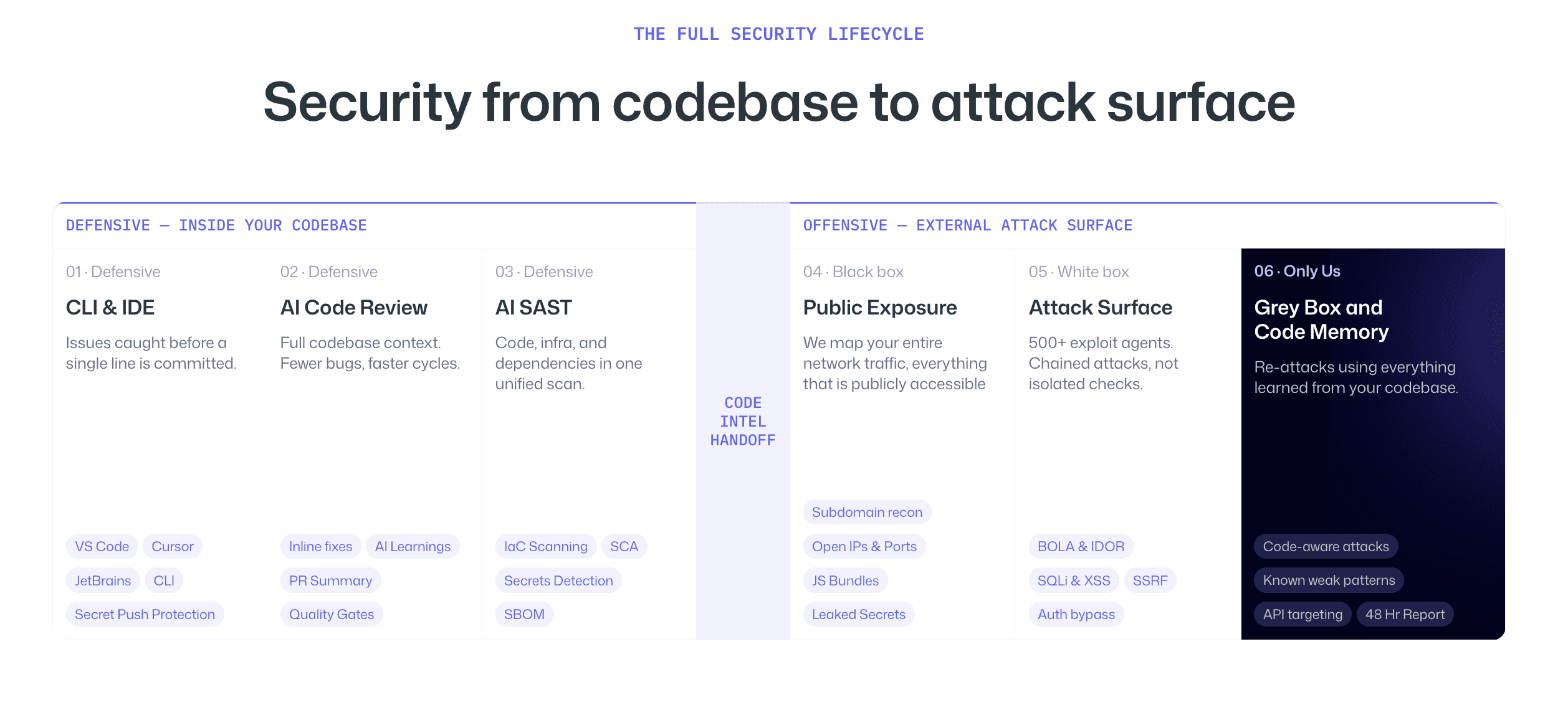
On the defensive side, CodeAnt reviews code in IDEs, CLI workflows, pull requests, and CI/CD pipelines. It detects insecure patterns, exposed secrets, risky API calls, and code paths that may create cloud exposure.
On the offensive side, CodeAnt maps the public attack surface, uses code intelligence to guide gray box testing, validates exploitability, and constructs attack chains.
The core advantage is:
The same platform that reviews your code for insecure patterns in CI/CD is the one conducting reconnaissance against your external cloud surface, testing from the outside with inside knowledge.
That makes the attack path validation deeper than external-only cloud scanning.
What A Cloud Attack Path Finding Should Look Like
Field | Details |
|---|---|
Finding | SSRF to AWS role credential exposure |
Severity | Critical |
Affected asset |
|
Cloud provider | AWS |
Initial weakness | SSRF |
Chained weakness | Metadata credential access |
Impact | Temporary cloud credentials retrieved |
Proof |
|
Business risk | Possible access to production storage and secrets |
Remediation | Enforce IMDSv2, patch SSRF, reduce role permissions |
Retest status | Pending / Passed |
Conclusion: Validate Cloud Attack Paths, Not Just Cloud Misconfigurations
Cloud security testing becomes meaningful only when it proves what an attacker can actually do.
A public bucket, exposed endpoint, weak IAM role, or leaked CI/CD secret may look like an isolated issue in a posture report. But real cloud breaches happen when those issues connect into an attack path.
That is why technical cloud attack path testing matters. It validates whether an attacker can move from an application flaw to cloud credentials, from a leaked secret to production access, or from an exposed service to sensitive data.
Modern AI pentesting and automated penetration testing help security teams move faster by correlating cloud exposure, identity permissions, code context, and exploit evidence across AWS, Azure, and GCP.
This is where CodeAnt’s defensive plus offensive model is especially valuable. The same platform that reviews code and CI/CD patterns also tests the external cloud surface with inside knowledge, helping teams prove real risk and fix the root cause.
If your current cloud security process only reports misconfigurations, the next step is to validate which ones can actually become breaches.
FAQs
What Is Cloud Attack Path Testing?
How Is AI Pentesting Different From Cloud Security Posture Management?
What Are Common AWS Cloud Attack Paths?
Can Automated Penetration Testing Validate Cloud Exploit Chains?
What Evidence Should A Cloud Pentest Report Include?