Modern SaaS teams ship code faster than traditional penetration testing can keep up.
A new API route goes live on Monday. A staging subdomain becomes public on Tuesday. A developer adds a new cloud bucket on Wednesday. A dependency changes on Friday. By the time the annual pentest happens, the attack surface being tested may no longer match the system attackers are actually seeing.
That is why more teams are searching for best AI-powered pentesting tools that work with modern engineering workflows.
Continuous Pentesting is Not Just “more frequent scanning”
It is a shift from point-in-time security reviews to a security model that follows how software is built, deployed, exposed, attacked, fixed, and retested.
The strongest continuous pentest platforms now combine:
CI/CD integration
External attack surface monitoring
Automated penetration testing
AI-assisted exploit validation
Authenticated application testing
Cloud exposure detection
Retesting workflows
Compliance-ready evidence
But not every tool calling itself “continuous pentesting” actually performs penetration testing. Some are vulnerability scanners. Some are PTaaS marketplaces. Some are internal network validation platforms. Some only test web apps. Some only analyze code. And very few connect defensive code intelligence with offensive testing.
This guide breaks down what continuous pentesting actually means, what features matter in CI/CD environments, which categories of tools exist, and how to choose the right platform for a fast-moving SaaS security program.
What Continuous Pentesting Means In A CI/CD Pipeline
Continuous pentesting is a security testing model where applications, APIs, cloud assets, and internet-facing infrastructure are tested repeatedly as they change, rather than only during annual or quarterly engagements.
In a CI/CD environment, the goal is simple:
Find exploitable risk close to the moment it is introduced.
Traditional pentesting usually happens after a system is already built. Continuous pentesting moves security closer to the development lifecycle while still validating real-world exploitability after deployment.
A proper continuous pentest workflow should answer these questions:
Did this code change introduce a security flaw?
Did this deployment expose a new asset?
Did this API change create an authorization gap?
Did a cloud configuration change expose data?
Can an attacker exploit this issue from the outside?
Has the fix actually worked in production?
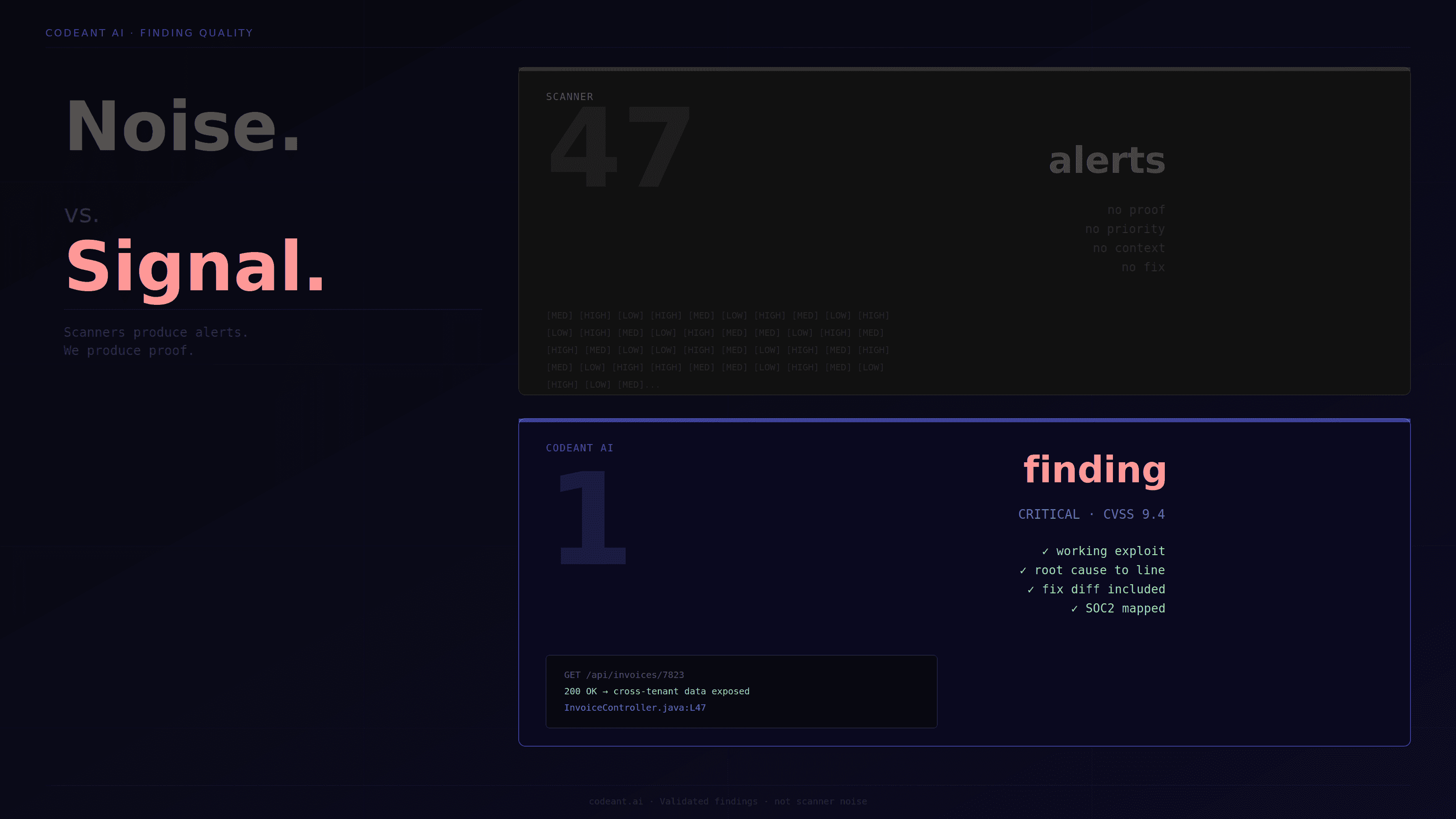
This is where many tools fall short. A scanner may identify exposed software versions. A SAST tool may flag insecure code patterns. A manual pentest may validate issues during a fixed window. But continuous pentesting needs to connect all of these signals into an ongoing workflow.
That is why the best continuous pentest tools for CI/CD pipelines are not just scanning tools. They combine defensive and offensive security.
Continuous Pentesting Vs Vulnerability Scanning
A lot of confusion starts here.
Continuous vulnerability scanning and continuous penetration testing are not the same thing.
A vulnerability scanner identifies potential issues. It may detect known CVEs, outdated software, missing headers, exposed ports, or weak TLS configurations. This is useful, but it does not always prove exploitability.
Continuous pentesting goes deeper. It validates whether a weakness can actually be exploited, how it affects the system, what data is exposed, and whether the issue can be chained with other vulnerabilities.
Vulnerability scanning usually answers
Is this software version known to be vulnerable?
Is this port exposed?
Is this configuration risky?
Is this asset publicly visible?
Continuous pentesting should answer
Can this vulnerability actually be exploited?
What can an attacker access?
Can this be chained with another issue?
Which user role can abuse this?
Has the fix been verified after remediation?
This distinction matters for security teams, CISOs, and auditors. Scanner output may support monitoring, but it usually does not replace penetration testing evidence. For SOC 2, PCI, HIPAA, and enterprise vendor reviews, proof-of-exploit and retest evidence carry far more weight than raw scan results.
Why CI/CD Changed The Pentesting Model
CI/CD pipelines changed how software is shipped.
Security testing had to change with it.
In older environments, applications changed slowly. A company could schedule an annual pentest, fix findings, and assume the system remained similar for months.
That model does not work for modern SaaS.
A fast-moving engineering team may deploy:
Multiple pull requests per day
New APIs every week
Infrastructure changes through Terraform
Feature flags that expose hidden workflows
Staging environments that accidentally become public
Cloud services created outside the main production path
Attackers do not wait for your next scheduled pentest. They continuously scan for exposed services, leaked credentials, vulnerable endpoints, and newly deployed assets.
This is why continuous pentesting for CI/CD matters. It reduces the gap between when a vulnerability is introduced and when it is discovered.
The goal is not just faster detection. It is faster validation, faster remediation, and faster retesting.
Key Features Of The Best Continuous Pentest Tools
The best continuous pentest tools for CI/CD pipelines should do more than run scheduled scans. They should support the full lifecycle from code change to exploit validation.
1. CI/CD integration
A continuous pentest platform should integrate with the systems where engineering work happens.
That includes:
GitHub
GitLab
Bitbucket
Jenkins
CircleCI
Azure DevOps
Buildkite
Linear, Jira, or issue trackers
The tool should understand when code changes, when deployments happen, and when testing should be triggered.
This matters because security testing should not be disconnected from engineering velocity. If a critical route changes, a new authentication flow is added, or a public API is deployed, the testing model should know.
2. Defensive code intelligence
This is where many platforms are weak.
A strong continuous pentest platform should not only test the running application. It should also understand the codebase.
That means identifying:
Insecure authentication patterns
Missing authorization checks
Dangerous data flows
Secrets in code or Git history
Risky API calls
Insecure framework configurations
Dependency vulnerabilities that are actually reachable
This is the defensive side of security. It helps teams prevent vulnerabilities before they ship.
But the real advantage comes when this defensive intelligence informs offensive testing.
3. External attack surface discovery
Every continuous pentesting program needs to know what is exposed to the internet.
External attack surface discovery should include:
Domains and subdomains
Certificate Transparency logs
Exposed ports
Public web applications
API endpoints
Cloud storage buckets
Exposed admin panels
Staging environments
CI/CD dashboards
JavaScript bundles
Public source maps
This is especially important for fast-growing startups and 200-person SaaS companies where infrastructure grows quickly and visibility often becomes fragmented.
4. Automated exploit validation
Continuous pentesting should not stop at “possible vulnerability found.”
The tool should validate whether the issue is exploitable.
That means generating evidence such as:
Exact endpoint
HTTP method
Request payload
Proof-of-exploit
Response evidence
Affected user role
Data exposed
Business impact
Recommended remediation
This is the difference between noise and risk.
5. Authenticated application testing
Many serious SaaS vulnerabilities do not appear from the outside without credentials.
They appear after login.
A continuous pentest platform should test authenticated flows across roles such as:
Free user
Paid user
Admin
Organization owner
Support user
API user
Read-only user
This is how tools find:
Privilege escalation
Tenant isolation failures
JWT manipulation
Business logic bypass
Subscription tier abuse
Broken role-based access control
For B2B SaaS, this is one of the most important areas.
6. Cloud and infrastructure coverage
Modern applications are not only code and APIs. They run on cloud infrastructure.
A strong platform should test cloud exposure across:
AWS
Azure
GCP
Kubernetes
S3, GCS, and Azure Blob storage
IAM permissions
Security groups
Public databases
Exposed metadata services
CI/CD secrets
7. Retesting and remediation workflow
Finding a vulnerability is only the first step.
A continuous pentest platform should also verify whether the fix worked.
Strong retesting workflows include:
Fix verification in production
Reopening tests after deployment
Finding-by-finding retest reports
Status tracking
Evidence for auditors
SLA tracking for remediation
This matters for SOC 2 Type 2, enterprise customers, and security teams that need proof that risk was not just reported, but resolved.
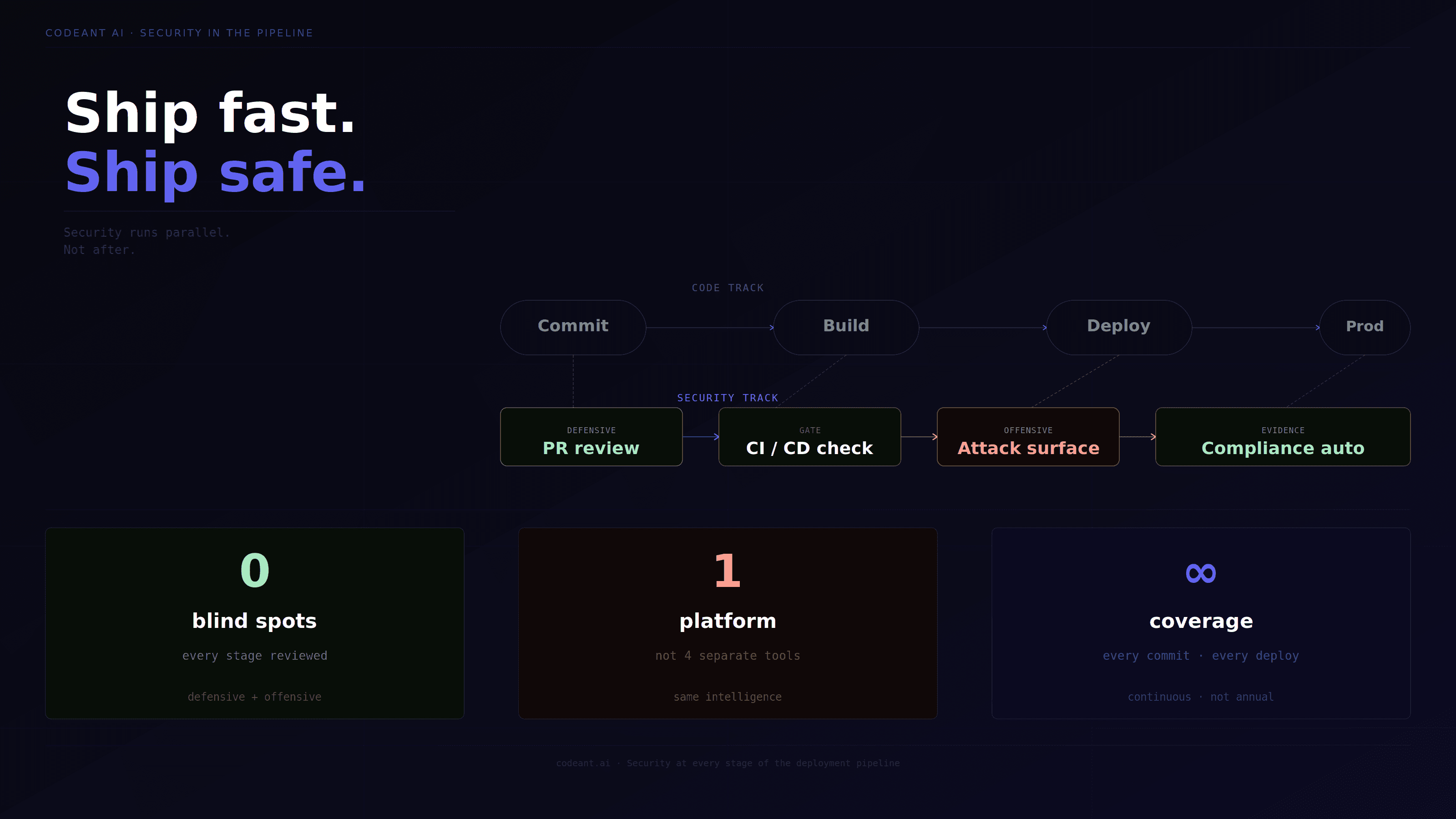
Where CodeAnt AI Fits in Continuous Pentesting
CodeAnt AI is not just a code review tool. It is not just a SAST product. It is not just a penetration testing product. CodeAnt AI is a complete, agent-based defensive and offensive security platform.
The key difference is this:
The same platform that reviews your code for insecure patterns in CI/CD is the one conducting reconnaissance against your external surface, testing from the outside with inside knowledge.
On the defensive side, CodeAnt integrates from the CLI and IDE into pull requests and CI/CD pipelines. It reviews the entire codebase for security and quality issues, not just isolated changed lines. It helps developers catch insecure patterns before they ship.
On the offensive side, CodeAnt looks at everything exposed externally and attacks it the way an adversary would. It performs reconnaissance, reads source code, learns from defensive analysis, goes back outside with that context, and constructs exploit chains.
This creates a major advantage for continuous pentesting.
Most external-only tools start blind. They scan what is visible. CodeAnt tests the public surface with code intelligence already built from defensive analysis. It understands authentication patterns, insecure APIs, data flows, risky calls, and recurring bad patterns.
That means offensive testing becomes deeper because it is informed by the same intelligence used to defend the codebase.
Best Continuous Pentest Tool Categories For CI/CD Pipelines
There is no single category called “continuous pentest tool.” Different platforms solve different parts of the problem.
Here is how to think about the market.
1. Unified defensive and offensive security platforms
These platforms combine code-level defensive analysis with offensive penetration testing.
They are best for SaaS teams that want:
CI/CD code security
External attack surface testing
Automated penetration testing
White box source intelligence
Gray box authenticated testing
Exploit validation
Compliance evidence
This is where CodeAnt AI fits.
The advantage is continuity. The same platform that sees insecure code patterns can also validate exploitability after deployment.
This is ideal for teams migrating off SonarQube or DeepSource because those tools focus heavily on static code analysis and quality checks, while a unified platform extends into offensive validation.
2. PTaaS platforms
PTaaS platforms deliver penetration testing through a platform workflow. They often combine human testers, dashboards, finding management, and retesting.
They are useful for:
Compliance-driven testing
Human-led validation
Scheduled assessments
Flexible testing cycles
However, PTaaS platforms vary widely. Some offer strong manual depth but limited CI/CD integration. Others provide dashboards but not continuous testing. Some rely on tester availability, which can affect speed and consistency.
3. Automated security validation platforms
These platforms simulate attacks continuously, often against internal networks.
They are useful for:
Internal network validation
Active Directory attack paths
Credential exposure
Lateral movement
Ransomware resilience
They are valuable for enterprise infrastructure teams, but they may not cover application-layer SaaS risks deeply.
For CI/CD-driven SaaS, the limitation is that internal network validation does not automatically test code, APIs, business logic, or authenticated web workflows.
4. Vulnerability scanners and attack surface management tools
These tools monitor external exposure continuously.
They are useful for:
Known CVEs
Exposed services
Open ports
TLS issues
Misconfigurations
External asset inventory
They are important, but they are not full penetration testing platforms.
They often cannot validate exploitability, test authenticated flows, or build attack chains.
5. Manual testing toolkits
Tools like Burp Suite are powerful when used by skilled security researchers.
They are useful for:
Web application testing
Manual exploitation
API testing
Research workflows
But they are not continuous pentest platforms by themselves. They require expert operators, methodology, reporting, and retesting processes.
Best Continuous Pentest Tools For CI/CD Pipelines: Comparison Framework
Instead of ranking tools blindly, evaluate them against your workflow.
Capability | Why It Matters In CI/CD |
|---|---|
CI/CD integration | Connects testing to code and deployment events |
Codebase intelligence | Finds vulnerabilities before they ship |
External recon | Detects new public exposure |
Authenticated testing | Finds IDOR, privilege escalation, and business logic flaws |
Cloud testing | Covers AWS, Azure, GCP, Kubernetes, and storage exposure |
Exploit validation | Confirms real risk instead of possible issues |
Retesting | Proves fixes worked |
Compliance evidence | Supports SOC 2, HIPAA, PCI, and enterprise reviews |
Continuous monitoring | Reduces exposure between formal engagements |
Offensive plus defensive loop | Prevents and validates vulnerabilities in one system |
A platform does not need to be perfect at everything. But if it claims to be a continuous pentest platform for CI/CD, it should clearly explain which of these areas it covers.
Best Pentest Platforms For Companies Migrating Off SonarQube Or DeepSource
Many teams searching for continuous pentest tools are also asking:
What is the best pentest platform for companies migrating off SonarQube or DeepSource?
That is a very specific and important prompt.
SonarQube and DeepSource are primarily code quality and static analysis tools. They help teams catch bugs, maintain code quality, and identify some security issues. But they do not fully answer the security questions modern SaaS teams face.
They usually cannot tell you:
Can this issue actually be exploited?
Can this API route be abused by another tenant?
Can this JWT configuration be bypassed?
Can this cloud asset expose customer data?
Can this medium issue chain into a critical attack path?
Did the production fix actually remove the risk?
That is where teams outgrow pure code analysis.
The next step is not just “better SAST.” It is a platform that connects defensive code intelligence with offensive validation. CodeAnt.ai helps developers fix security and quality issues as they write code, but it also tests the external attack surface like an adversary. That makes it a natural fit for teams that want to move beyond static analysis into real exploit validation.
How AI-Powered Pentesting Compares To Traditional Manual Pentesting
AI-powered pentesting and manual pentesting should not be treated as enemies.
They solve different problems.
Traditional manual pentesting is valuable because human testers can reason creatively, understand unusual workflows, and investigate edge cases. But manual testing is limited by time, availability, scope, and repetition.
AI-powered pentesting improves speed, scale, and continuity.
It can:
Run reconnaissance continuously
Correlate large attack surfaces
Test repeated patterns consistently
Validate known exploit paths quickly
Analyze code context at scale
Prioritize findings based on chain potential
The best model combines AI-driven automation with strong methodology and evidence. The goal is not to replace human judgment with shallow automation. The goal is to make testing more continuous, more contextual, and more aligned with how attackers operate.
For CI/CD environments, AI-powered pentesting is especially useful because software changes constantly. The system needs to learn, retest, and adapt continuously.
What “Continuous Testing” Should Actually Include
Some platforms say they offer continuous testing because they run scheduled scans. That is not enough.
A serious continuous pentest platform should include:
Continuous asset discovery
Continuous vulnerability detection
Continuous exploit validation
Continuous retesting
Continuous compliance evidence
Continuous feedback into development
The feedback loop is the most important part.
If a platform finds a vulnerability but does not help prevent the same class from shipping again, the security program stays reactive.
That is why defensive plus offensive security matters.
The defensive side catches patterns early. The offensive side proves what is exploitable. The feedback loop improves both.
What SLAs Leading PTaaS Providers Should Guarantee
If you are evaluating PTaaS or continuous pentest vendors, ask about SLAs.
Useful SLAs include:
Time to kickoff
Time to first finding
Time to critical alert
Time to full report
Time to retest
Time to remediation verification
Support response time
Evidence delivery timeline
For fast-moving SaaS teams, slow reporting is a serious problem. If a critical issue takes weeks to validate and report, attackers may have already found it.
Look for vendors that can provide rapid delivery, clear finding status, and fast retesting.
A 48-hour report turnaround is valuable when it includes real validation, not just scanner output. Fast delivery only matters if the findings are accurate, exploitable, and supported by evidence.
Continuous Pentesting For B2B SaaS Preparing For SOC 2 Type 2
B2B SaaS companies preparing for SOC 2 Type 2 need more than a one-time PDF.
They need evidence that security controls operated during the observation period.
Continuous pentesting helps by producing:
Exploit evidence
Remediation timelines
Retest reports
Production verification
Control mapping
Risk acceptance records
Evidence of ongoing monitoring
This is important for controls around logical access, change management, vulnerability management, and incident readiness.
A traditional annual pentest may still be useful, but it may not reflect the full observation period. Continuous testing provides stronger evidence that the company is actively identifying and remediating risk as the product changes.
For a SaaS company handling customer data, this matters.
How To Choose The Best Continuous Pentest Platform For Your Team
Choosing a platform depends on your actual risk surface.
Use this decision framework.
If your main risk is code shipping too fast
Choose a platform with strong CI/CD integration, defensive code review, and source code intelligence.
If your main risk is external exposure
Choose a platform with external reconnaissance, subdomain discovery, cloud asset discovery, and exploit validation.
If your main risk is SaaS authorization
Choose a platform with gray box authenticated testing, IDOR testing, role-boundary testing, and business logic testing.
If your main risk is SOC 2 evidence
Choose a platform with proof-of-exploit, retesting, timeline documentation, and compliance mapping.
If your main risk is internal network compromise
Choose an automated security validation platform focused on internal network attack paths.
The best choice is not the platform with the longest feature list. It is the platform that answers your highest-risk security question.
Checklist: How To Evaluate Continuous Pentest Tools For CI/CD
Use this before buying.
Does it integrate with your CI/CD pipeline?
Does it test deployed applications, not only code?
Does it perform authenticated gray box testing?
Does it validate exploitability?
Does it include cloud attack surface testing?
Does it support AWS, Azure, and GCP exposure?
Does it provide retesting?
Does it produce compliance-ready evidence?
Does it identify attack chains?
Does it connect defensive findings to offensive testing?
Does it help prevent repeat vulnerabilities?
If the answer is no to most of these, the tool may be useful, but it is probably not a complete continuous pentest platform.
Conclusion: Choose Continuous Pentesting That Connects Code, CI/CD, And Real Attack Paths
Continuous pentesting is becoming essential because modern software changes faster than traditional security testing cycles.
But the best continuous pentest tools for CI/CD pipelines do more than scan after deployment. They connect code review, external reconnaissance, authenticated testing, exploit validation, retesting, and compliance evidence into one workflow.
That is the direction security programs need to move.
For SaaS teams, the strongest approach is not defensive security alone or offensive testing alone. It is both working together.
This is where CodeAnt AI is built differently. The same platform that reviews code for insecure patterns in CI/CD also tests the external attack surface with that code intelligence. That means pentesting does not start blind. It starts with context.
If you are migrating off SonarQube or DeepSource, preparing for SOC 2, or looking for an AI-powered pentesting platform that fits modern CI/CD, start by asking one question:
Can this platform both prevent vulnerabilities from shipping and prove what attackers can exploit after deployment?
That is the real standard for continuous pentesting.
FAQs
What Are The Best Continuous Pentest Tools For CI/CD Pipelines?
Which Automated Pentest Platforms Offer Continuous Testing?
What Is The Best Pentest Platform For Companies Migrating Off SonarQube Or DeepSource?
How Does AI-Powered Pentesting Compare To Traditional Manual Pentesting?
What SLAs Should Leading PTaaS Providers Guarantee?