The Paradox at the Center of Red Team Authorization
A red team engagement tests whether an organization's security team can detect and respond to a real attack. For the test to be valid, the security team being tested, the blue team, cannot know the test is happening.
This creates an authorization paradox: the people who would normally review, approve, and sign the authorization letter are exactly the people who must be kept in the dark.
Solve this wrong and one of two things happens. Either the blue team finds out (test is ruined), or no one with adequate authority knows the engagement is authorized (testers face legal exposure if caught). Both outcomes defeat the purpose of the engagement.
Red team authorization letters solve this through compartmentalization — a restricted knowledge model where authorization flows from a small number of executive-level stakeholders who are explicitly not part of the blue team.
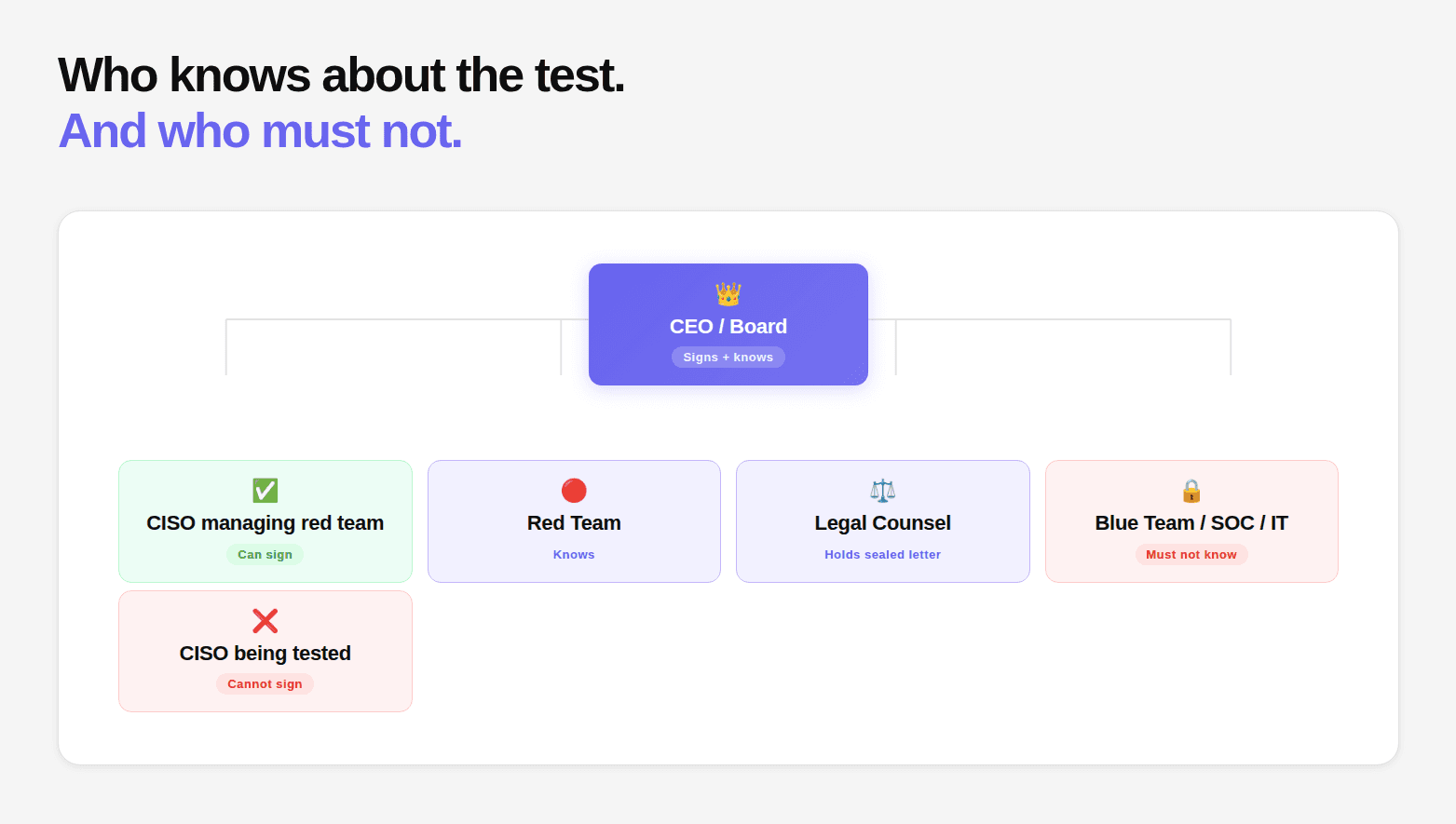
Who Can Sign: The Compartmentalization Problem
Standard penetration test authorization letters are typically signed by the CISO or CTO. Red team engagements cannot follow this pattern if the CISO is being evaluated.
The signing authority rule for red teams:
The authorization letter must be signed by someone who is not part of the group being tested. Specifically:
If the CISO manages the SOC being tested → CISO cannot sign
If the entire security team is being evaluated → must go to CEO or board level
If the security team manages but doesn't operate the test target → CISO may sign if operationally separate from the blue team
In practice, most red team authorizations require CEO or board-level signature because the whole point of the engagement is to test the security function. The CISO who manages that function cannot objectively authorize their own team's evaluation.
The Sealed Envelope Approach
For organizations where legal, timing, or organizational dynamics make it difficult to get executive signatures at engagement start, the sealed envelope approach provides a practical solution.
The full authorization letter is prepared before the engagement. The envelope is sealed. It is held by a neutral party, typically Legal Counsel, who has been briefed on the engagement.
The envelope is opened only if:
A legal issue arises during the engagement
Law enforcement becomes involved
The organization faces an inquiry requiring documented authorization
This approach allows the engagement to proceed with strict compartmentalization while ensuring documented authorization exists and can be produced if needed.
The Get-Out-of-Jail Card
Every person conducting a red team engagement, particularly physical components, must carry a physical "get-out-of-jail" card. This is separate from the full authorization letter (which may be sealed) and serves as immediate verification during a law enforcement or security encounter.
Critical requirements for the card:
Must reference a 24/7-reachable phone number, not an office number
Must include an authentication code the contact can verify
Contact named must be the executive sponsor, not the security team
Every individual operating in the field must carry one
Cards must be printed, not stored on a phone that might be seized
Handling Blue Team Detection and Response
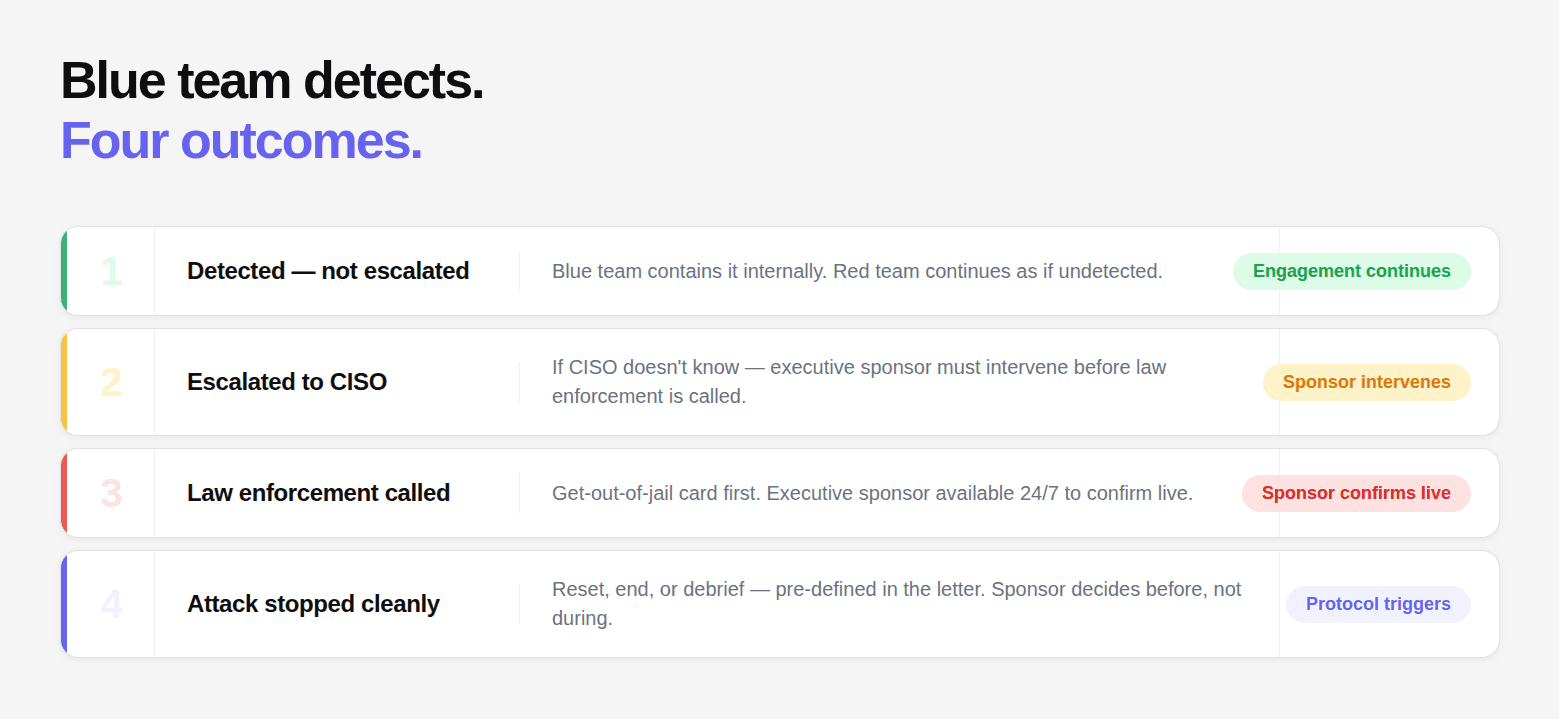
The authorization letter must address what happens when the blue team detects the red team and escalates. This is one of the most important scenarios that standard penetration test letters don't cover.
Scenario 1: Blue team detects activity but doesn't escalate to law enforcement Define whether red team should "break character." Most engagements specify that if the blue team detects and contains the attack without law enforcement, the red team continues as if undetected unless told to stop by the executive sponsor.
Scenario 2: Blue team escalates to internal security leadership (CISO) Define whether the CISO is in the "knows" group or the "doesn't know" group. If the CISO doesn't know, they may escalate to law enforcement thinking it's a real attack. The authorization letter must include a procedure for the executive sponsor to intervene at this point.
Scenario 3: Blue team calls law enforcement This is the Coalfire scenario. Law enforcement arrives. Red teamers are detained. The get-out-of-jail card is the first line of resolution. The executive sponsor contact is the second. The letter must specify that the executive sponsor is available 24/7 to confirm the engagement directly to law enforcement.
Scenario 4: Blue team successfully detects and stops the attack Define what happens to the engagement. Does it reset? Does testing end? Is a debrief triggered? The authorization letter should set the parameters so the executive sponsor doesn't have to make this decision under pressure.
What the Red Team Letter Must Include That Standard Letters Don't
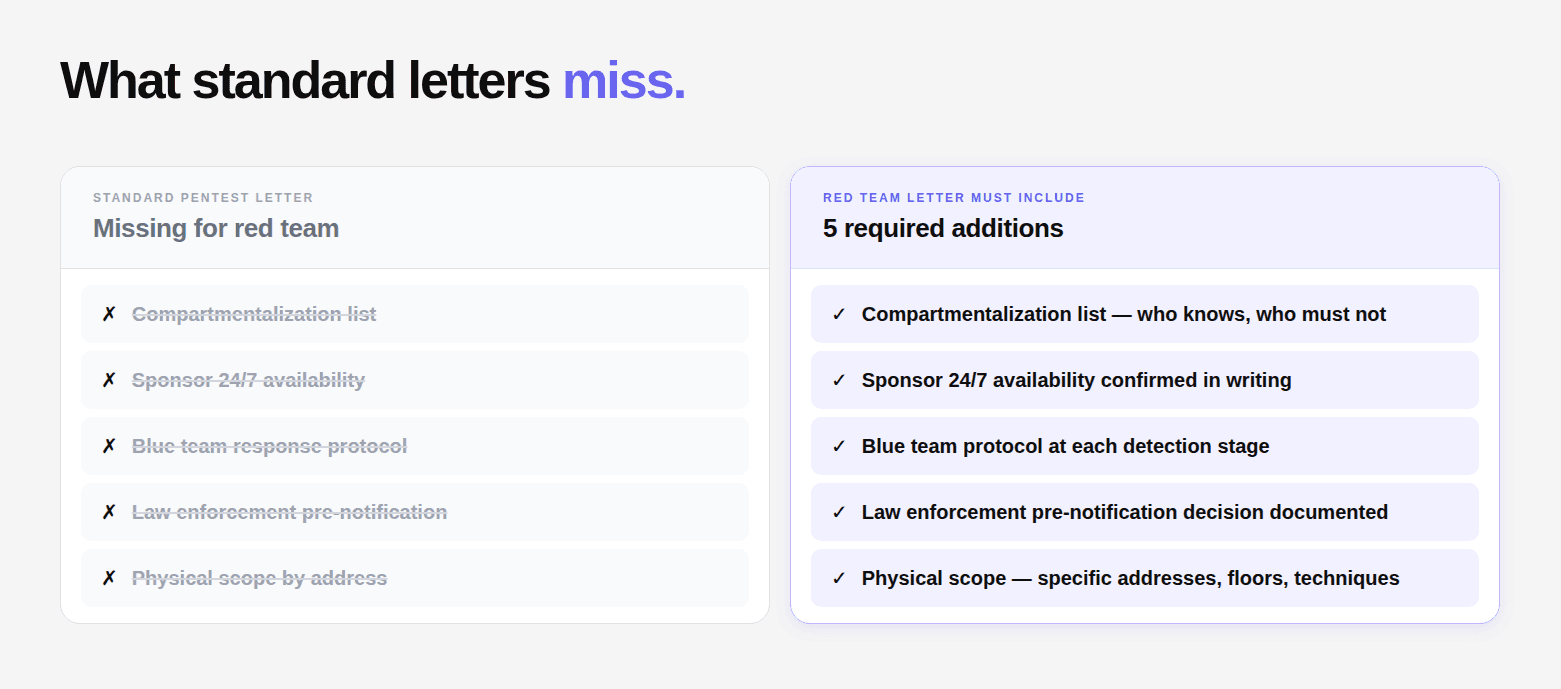
Compartmentalization section: Explicitly list who knows the engagement is occurring and who must not be informed. Named individuals in each category. This protects both the engagement validity and the organization if the blue team later claims they weren't properly notified.
Executive sponsor 24/7 availability confirmation: The executive sponsor must confirm in writing that they will be reachable throughout the engagement window. Unlike standard engagements where emergency contact is a secondary concern, in red team this is a primary operational requirement.
Blue team response protocol: What should happen at each stage of blue team detection — continue, pause, stop, debrief. Without this, the executive sponsor faces real-time decisions they shouldn't have to make without prior guidance.
Law enforcement pre-notification decision: Some organizations choose to pre-notify local law enforcement that a red team is operating. This is the single most effective measure for preventing arrest scenarios. Document whether this was done and who was notified.
Physical access scope, precision matters: Physical red team engagements require the most precise scope definition of any engagement type. "The company's offices" is not sufficient. List specific addresses, floors, access types, and whether tailgating, badge cloning, and other physical techniques are in scope.
Red Team Authorization Is About Control Without Visibility
A standard penetration test is about permission. A red team engagement is about permission under controlled secrecy. That difference changes everything.
Authorization cannot be broad. It cannot be assumed. It cannot follow the same structure used for standard testing. Because the moment the wrong people know about the engagement, the test loses its value. And the moment the right people do not formally authorize it, the engagement carries real legal risk.
This is the balance red team authorization must achieve. Limited awareness. Explicit authority. Clear escalation paths. The organizations that do this well treat authorization as part of the engagement design, not as documentation that comes after. They define who knows, who does not, and who can intervene before testing begins.
If you get this right, the engagement runs exactly as intended. Realistic, controlled, and defensible.
If you get it wrong, you either lose the test or expose your team.
And in red team engagements, there is no middle ground.
FAQs
Why can’t the CISO always sign a red team authorization letter?
What is the purpose of a sealed authorization letter in red team engagements?
Is a get-out-of-jail card legally sufficient on its own?
Should law enforcement be notified before a red team engagement?
What makes red team authorization more complex than standard penetration testing?