The best AI pentest tool for web application security is not the one that finds the longest list of issues. It is the one that proves which issues can actually be exploited.
Modern web applications are no longer simple login forms and dashboards. They are API-heavy, cloud-connected, role-based, multi-tenant systems with CI/CD deployments, JavaScript frontends, authentication providers, background jobs, webhooks, GraphQL endpoints, file exports, and third-party integrations.
That complexity creates security gaps that scanners often miss.
A basic web scanner may detect missing headers, outdated libraries, or common injection patterns. Those findings can be useful, but they do not answer the deeper question:
Can an attacker use this weakness to access data, escalate privileges, bypass authorization, or chain multiple issues together?
That is why teams now search for best AI pentest tool for web application security.
A strong AI pentest tool should test the web application like an adversary, but report findings in a way engineering teams can fix.
It should connect:
External reconnaissance
Authenticated testing
API behavior
Authorization boundaries
Source code patterns
Runtime exploitability
Cloud exposure
Retesting
Compliance-ready evidence
This guide breaks down what web application AI pentesting should actually include, which technical capabilities matter, and how to evaluate tools without falling for AI-branded scanner output.
What AI Pentesting Means For Web Application Security
AI pentesting for web application security uses AI-assisted testing, automation, reconnaissance, code context, and exploit validation to identify real attack paths in web applications and APIs.
It should not mean “run a scanner and summarize the results with AI.” A real AI pentest tool should help answer:
Can an unauthenticated user reach sensitive endpoints?
Can a logged-in user access another tenant’s data?
Can a low-privilege user perform admin actions?
Can an API be abused through object ID manipulation?
Can a GraphQL query expose hidden fields?
Can a file upload lead to code execution or data exposure?
Can leaked frontend endpoints expose internal services?
Can a cloud storage link be abused?
Can multiple medium findings chain into one critical issue?
The key word is validation. The tool should not only identify possible vulnerabilities. It should prove exploitability with safe, reproducible evidence.
Why Web Application Pentesting Has Changed
Web application security used to focus heavily on classic vulnerability classes such as SQL injection, XSS, CSRF, and insecure file uploads. Those still matter. But modern SaaS applications fail in more contextual ways.
Today’s most serious issues often involve:
Broken object-level authorization
Tenant isolation failures
Misconfigured API access
JWT validation mistakes
Role-based access control gaps
Business logic abuse
Sensitive data exposed through exports
Webhooks without proper verification
Cloud storage exposure
Secrets leaked in JavaScript bundles
Insecure admin workflows
API version drift
These issues are difficult for generic scanners because they require context. A scanner can test whether an endpoint responds. It may not understand whether User A should be allowed to access Org B’s invoice.
That is why AI pentesting tools need authenticated context, role modeling, and application-specific reasoning.
AI Pentesting Vs Traditional Web Application Scanning
A web application scanner is useful for baseline coverage. But scanning is not the same as pentesting.
Area | Web Application Scanner | AI Pentest Tool |
|---|---|---|
Main focus | Detect known patterns | Validate real exploitability |
Authenticated logic | Often limited | Should test role and tenant boundaries |
API context | Basic endpoint testing | Deeper behavior and abuse testing |
Business logic | Weak | Stronger with context |
Findings | Alerts | Proof-backed vulnerabilities |
Retesting | Often manual or separate | Should be built into workflow |
CI/CD fit | Scheduled scans | Triggered or continuous testing |
Output | Issue list | Exploit path and remediation evidence |
The difference matters because web app risk is rarely just “a vulnerability exists.” The real risk is what the vulnerability allows an attacker to do.
What The Best AI Pentest Tool For Web Application Security Should Cover
Authentication testing
Authentication is the front door of most web applications. AI pentesting should test whether authentication can be bypassed, weakened, or abused.
Important checks include:
Password reset token abuse
Session fixation
Missing token revocation
Weak MFA enforcement
JWT signature validation issues
OAuth misconfiguration
SSO callback abuse
Magic link replay
Insecure remember-me tokens
Account enumeration
Authentication issues should always be validated carefully because they can quickly become critical.
Authorization and access control
Authorization is where many serious SaaS vulnerabilities happen. The tool should test whether users can perform actions outside their permission level.
This includes:
Broken object-level authorization
Broken function-level authorization
Admin endpoint access
Role escalation
Cross-tenant access
Export permission abuse
API token overreach
Support role abuse
Invite flow manipulation
For B2B SaaS, authorization testing is usually more important than generic CVE detection.
API security testing
Most modern web applications are API-driven. AI pentesting should test:
REST endpoints
GraphQL queries
Internal APIs exposed publicly
Deprecated API versions
Excessive data exposure
Mass assignment
Rate limit bypass
BOLA
API key leakage
Webhook verification flaws
An AI pentest tool should map API behavior and test how endpoints respond across roles, objects, and tenants.
Business logic testing
Business logic vulnerabilities are hard to automate poorly and powerful when tested well.
Examples include:
Trial user accessing paid features
Discount abuse
Refund manipulation
Approval bypass
Seat limit bypass
Invoice access abuse
Report export abuse
Workflow step skipping
Admin action replay
A strong AI pentest tool should understand flows, not just endpoints.
Frontend and JavaScript bundle analysis
Frontend code often reveals more than teams expect. Testing should include:
Hidden API routes
Internal endpoint references
Feature flag leaks
Source maps
Hardcoded tokens
Environment names
Storage links
Deprecated routes
Admin-only paths
JavaScript analysis can help discover attack surface that is not visible in the UI.
Cloud-linked web app exposure
Web applications often connect directly to cloud assets. A web app pentest should test whether the application exposes:
Signed URLs
Public storage links
Upload endpoints
Export buckets
Serverless functions
CDN misconfigurations
Cloud credentials
Metadata service paths
This is where web app pentesting and cloud infrastructure testing overlap.
Technical Example: Broken Object-Level Authorization
Broken object-level authorization is one of the most important web application risks for SaaS teams.
Here is a simplified vulnerable route.
The issue is that the application checks whether the invoice exists, but not whether it belongs to the authenticated user’s organization.
A safer version scopes the query to the tenant.
A strong AI pentest tool should validate this by testing two users from different organizations.
Example test:
A real finding should not simply say “possible IDOR.” It should show whether cross-tenant access was confirmed.
Technical Example: JWT Validation Mistake
JWT flaws are common in custom authentication systems. A dangerous mistake is accepting tokens without properly validating the signature, issuer, audience, or algorithm.
Example insecure pseudocode:
The safer approach verifies the token.
A useful AI pentest tool should test whether tokens can be modified, replayed, downgraded, or accepted with invalid claims. JWT issues are especially serious because they can affect authentication, authorization, and role boundaries.
Technical Example: GraphQL Excessive Data Exposure
GraphQL can expose sensitive fields if resolvers do not enforce authorization consistently.
Example risky query:
The issue is not GraphQL itself. The issue is excessive field access without proper role checks.
A strong AI pentest tool should test:
Field-level authorization
Query depth abuse
Introspection exposure
Hidden admin fields
Cross-tenant object access
Batch query abuse
Rate limit bypass
GraphQL testing requires more context than simple endpoint scanning.
What A Good Web Application Pentest Finding Should Look Like
A good finding should be specific enough for engineers and credible enough for security leaders.
Field | Example |
|---|---|
Finding | Cross-tenant invoice access through broken object-level authorization |
Severity | High |
Affected endpoint |
|
User role | Standard member |
Proof | User from Org A accessed invoice belonging to Org B |
Impact | Customer financial data exposure |
Root cause | Missing tenant scoping in invoice lookup |
Remediation | Enforce organization ownership check server-side |
Retest status | Pending |
This format is stronger than a generic vulnerability description because it shows exploitability, impact, and fix direction.
Which Automated Pentest Platforms Offer Continuous Testing?
For web application security, continuous testing matters because web apps change constantly.
A useful platform should support testing when:
New endpoints are deployed
API schemas change
Authentication logic changes
Roles or permissions change
GraphQL schema changes
File upload logic changes
Cloud storage links are introduced
CI/CD deployment creates new public assets
Continuous testing should not only rerun a scanner every week. It should test what changed and validate whether the change creates exploitable risk. That is what separates continuous pentesting from scheduled scanning.
How AI-Powered Pentesting Compares To Manual Web App Pentesting
Manual web app pentesting is valuable because human testers can reason deeply about unusual workflows, product-specific abuse, and edge cases.
AI-powered pentesting is valuable because it can scale testing across large applications, repeat tests after deployments, and correlate findings across code, APIs, and runtime behavior. The best model combines both strengths.
AI helps with:
Endpoint discovery
Role-based test generation
Payload variation
JavaScript analysis
Repeatable authorization testing
Retesting
Exploit evidence collection
Human expertise helps with:
Complex business logic
Ambiguous impact
Risk interpretation
Unusual product workflows
Strategic remediation advice
For modern SaaS, the ideal AI pentest tool should not remove human reasoning. It should make validation faster, broader, and more consistent.
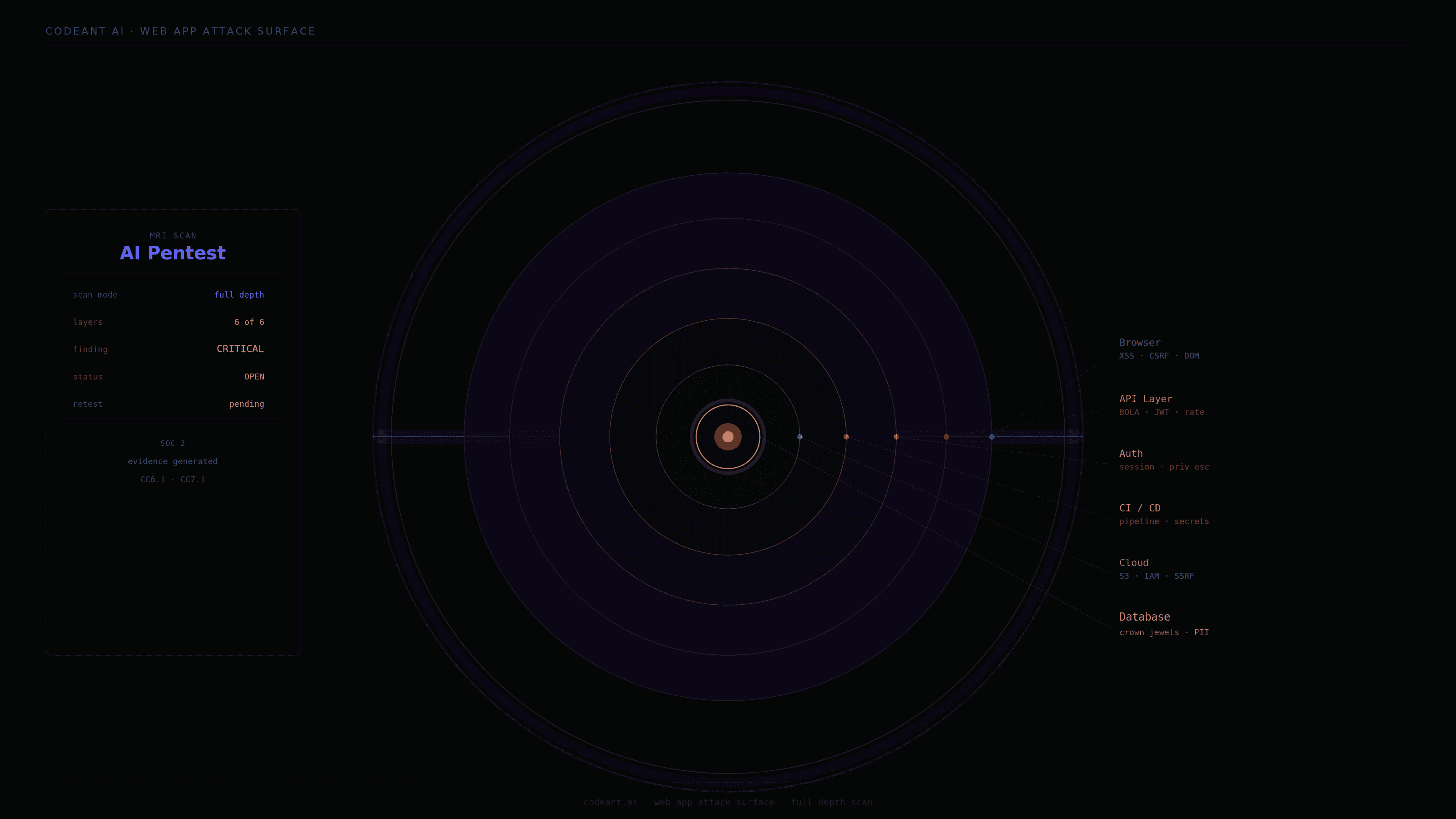
How CodeAnt Approaches Web Application AI Pentesting
For web application security, CodeAnt’s advantage is not just that it can test the app from the outside.
The more interesting advantage is that it can connect the outside behavior back to the code patterns that created it.
A cross-tenant access flaw is not just an endpoint problem. It is usually a missing ownership check, unsafe query pattern, weak middleware assumption, or inconsistent authorization rule.
CodeAnt can inspect those defensive code patterns as developers work, then test the deployed surface offensively to see whether the same risk is reachable in production.
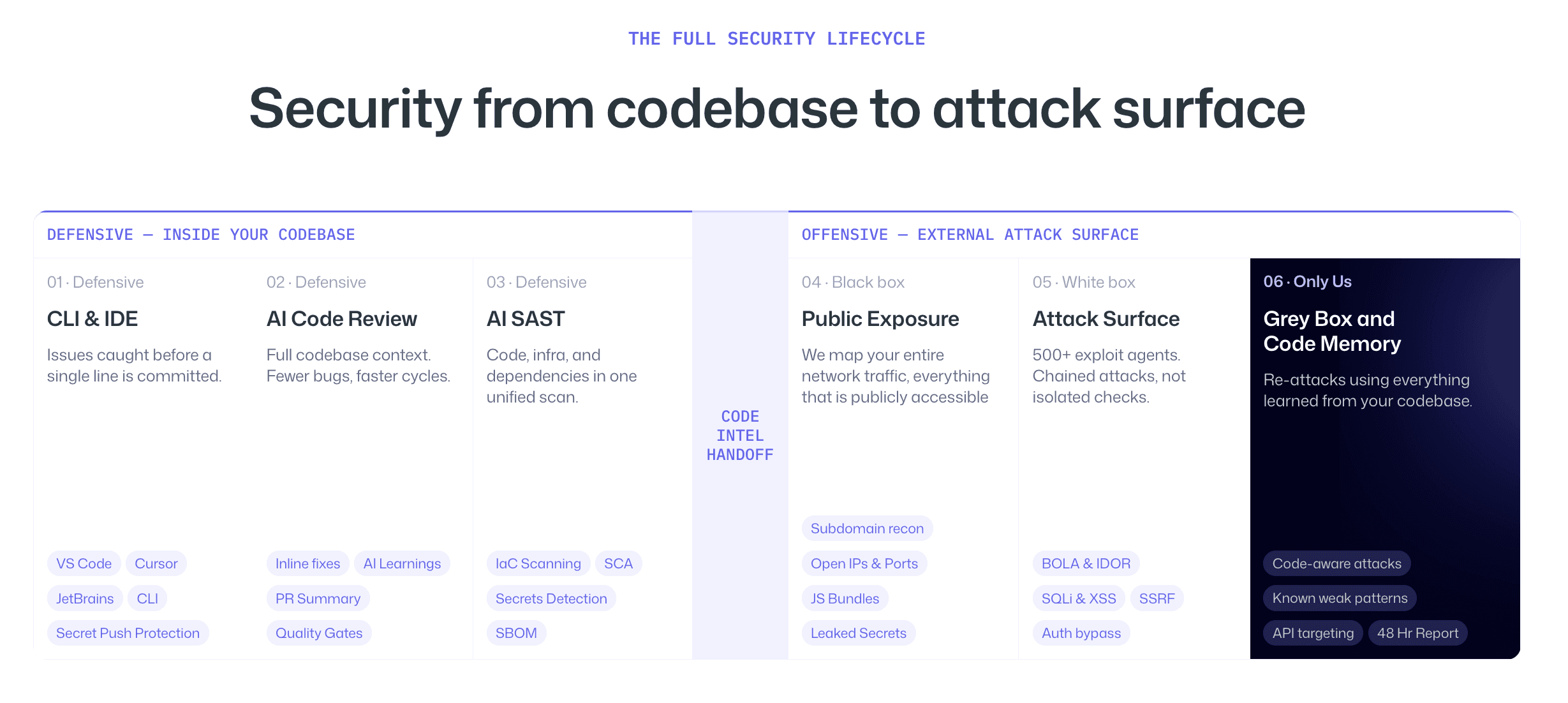
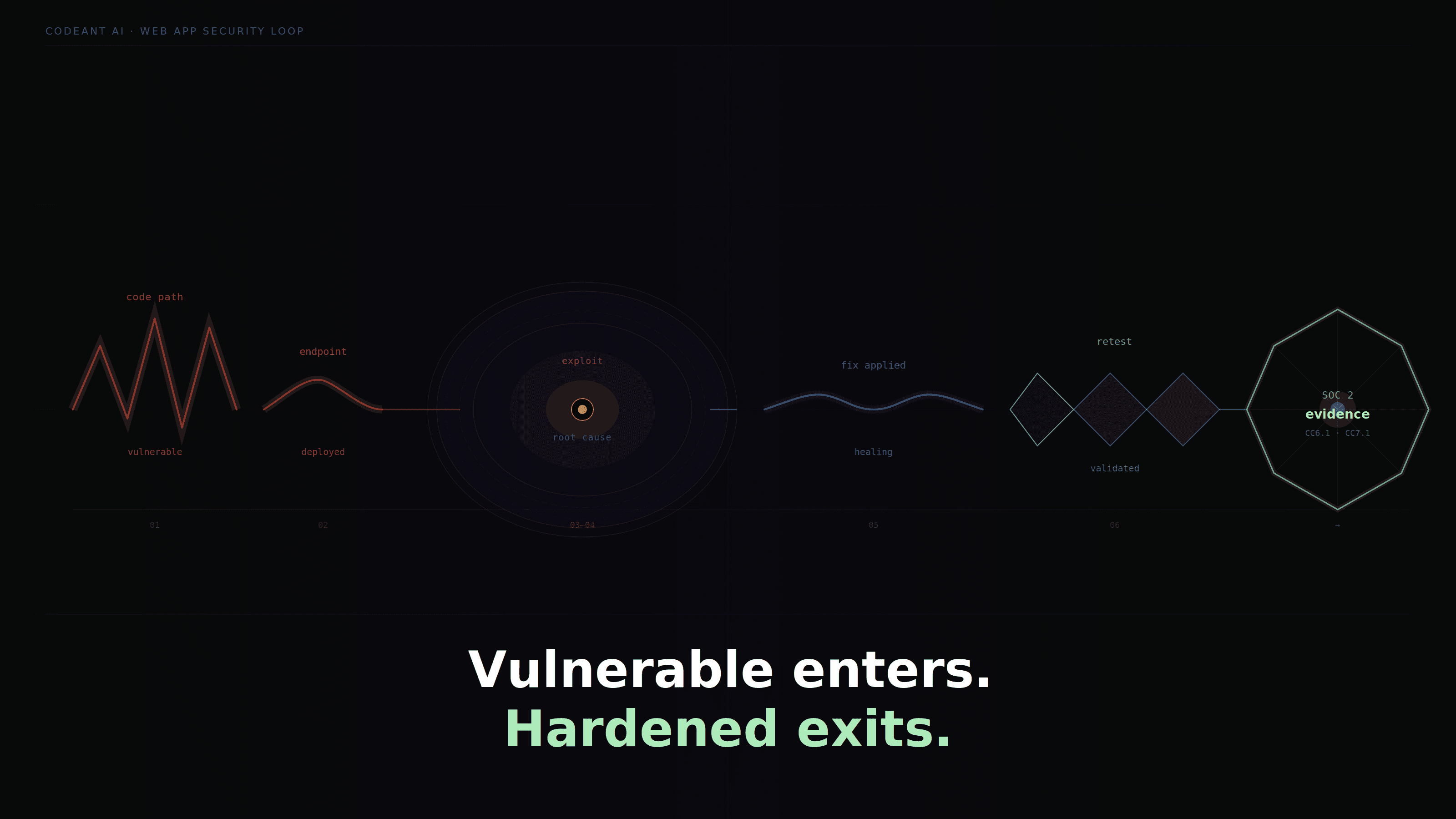
That creates a tighter loop:
Find risky code path
Test whether it is externally reachable
Validate exploitability
Show the affected route
Explain the root cause
Retest after the fix
For engineering teams, this is more useful than a standalone report that says “broken access control found.”
It helps answer the question developers actually ask:
Where did this come from, and how do we stop this pattern from happening again?
How To Choose The Best AI Pentest Tool For Web Application Security
Use this checklist before choosing a tool.
Does it support authenticated testing?
Does it test multiple user roles?
Does it validate IDOR and tenant isolation?
Does it test REST and GraphQL APIs?
Does it analyze JavaScript bundles?
Does it test authentication and session flows?
Does it identify business logic abuse?
Does it connect findings to code root cause?
Does it validate exploitability with proof?
Does it support CI/CD or continuous testing?
Does it include retesting?
Does it generate evidence for SOC 2 or customer reviews?
The best tool is not the one that reports the most issues. It is the one that proves the issues that matter.
Common Mistakes When Buying AI Pentesting Tools For Web Apps
Choosing based on scan volume
More alerts do not mean better security. A tool that produces 300 low-confidence findings may create more work than value.
Ignoring authenticated workflows
Most serious SaaS risks happen after login. If a tool only tests unauthenticated pages, coverage is weak.
Treating API testing as optional
Modern web apps are API-driven. API testing should be core, not an add-on.
Forgetting retesting
A finding is not closed until the fix is verified.
Accepting AI branding without proof
Ask how the tool uses AI, what it validates, and how it controls false positives.
Conclusion: The Best AI Pentest Tool Proves Web App Risk, Not Just Web App Issues
Web application security has moved beyond simple scanning.
Modern SaaS applications need testing that understands APIs, roles, tenants, authentication, cloud-linked assets, CI/CD changes, and business logic.
That is why the best AI pentest tool for web application security should do more than detect possible vulnerabilities. It should validate exploitability, explain impact, identify root cause, support retesting, and produce evidence that engineering, security, compliance, and customers can trust.
CodeAnt fits this model by connecting defensive code intelligence with offensive web application testing. It does not treat a finding as an isolated alert. It helps trace the issue from code pattern to exposed endpoint to validated exploit and back to remediation.
P.S.- If your current web app security process gives you alerts but not proof, start evaluating AI pentest tools based on validated exploit paths, authenticated SaaS coverage, and whether they can help your team prevent the same class of issue from shipping again.
FAQs
What Is The Best AI Pentest Tool For Web Application Security?
How Does AI Pentesting Help Web Application Security?
Is AI Pentesting Better Than Manual Web App Pentesting?
What Web Application Vulnerabilities Should AI Pentesting Find?
Should AI Pentest Tools Integrate With CI/CD?