Cloud infrastructure is no longer just servers, storage, and network rules.
It is identity, APIs, permissions, CI/CD pipelines, serverless functions, Kubernetes clusters, public endpoints, secrets, metadata services, and third-party integrations all operating at the same time.
That is why AI pentesting for cloud infrastructure has become so important for modern SaaS and enterprise teams.
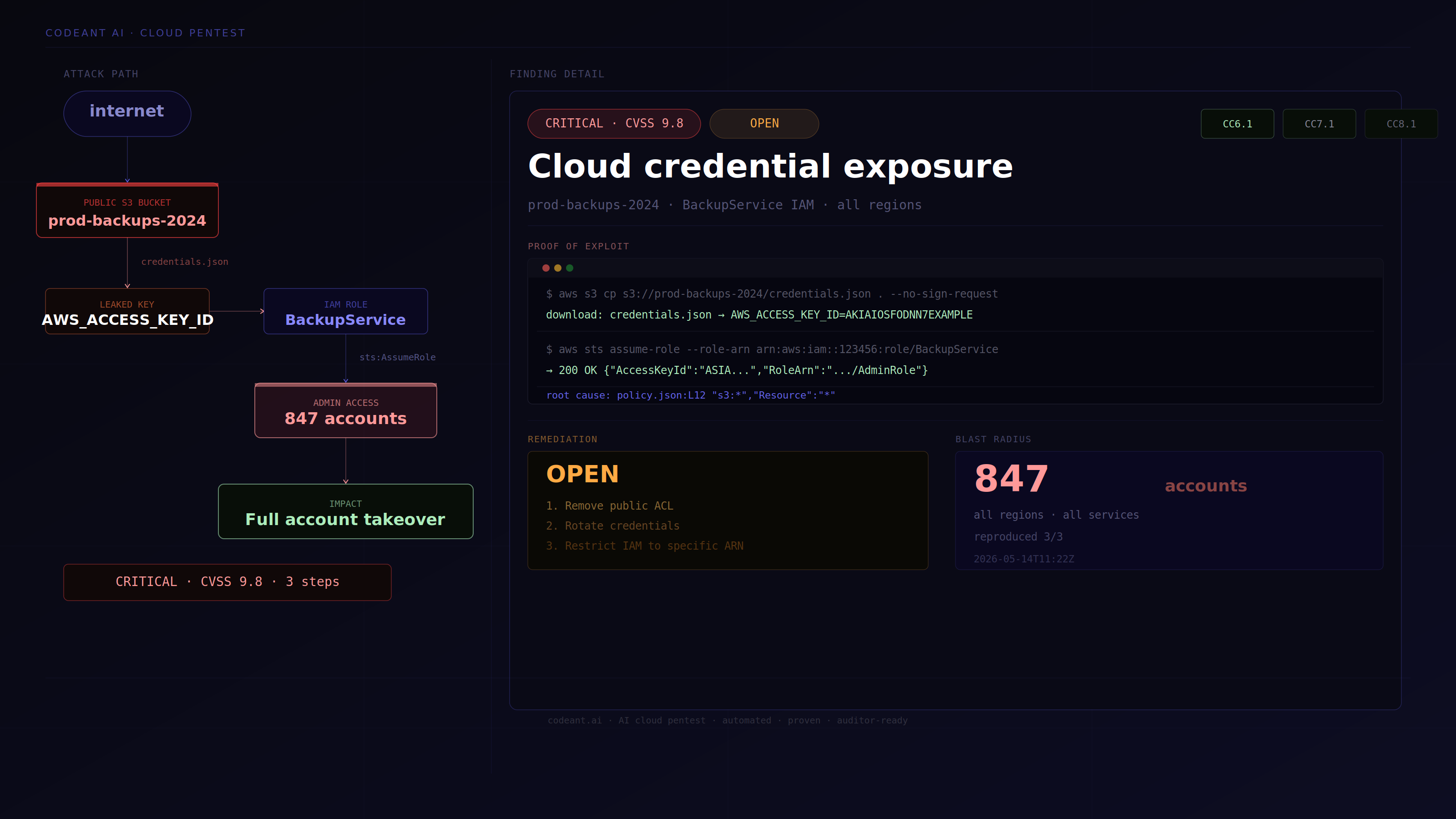
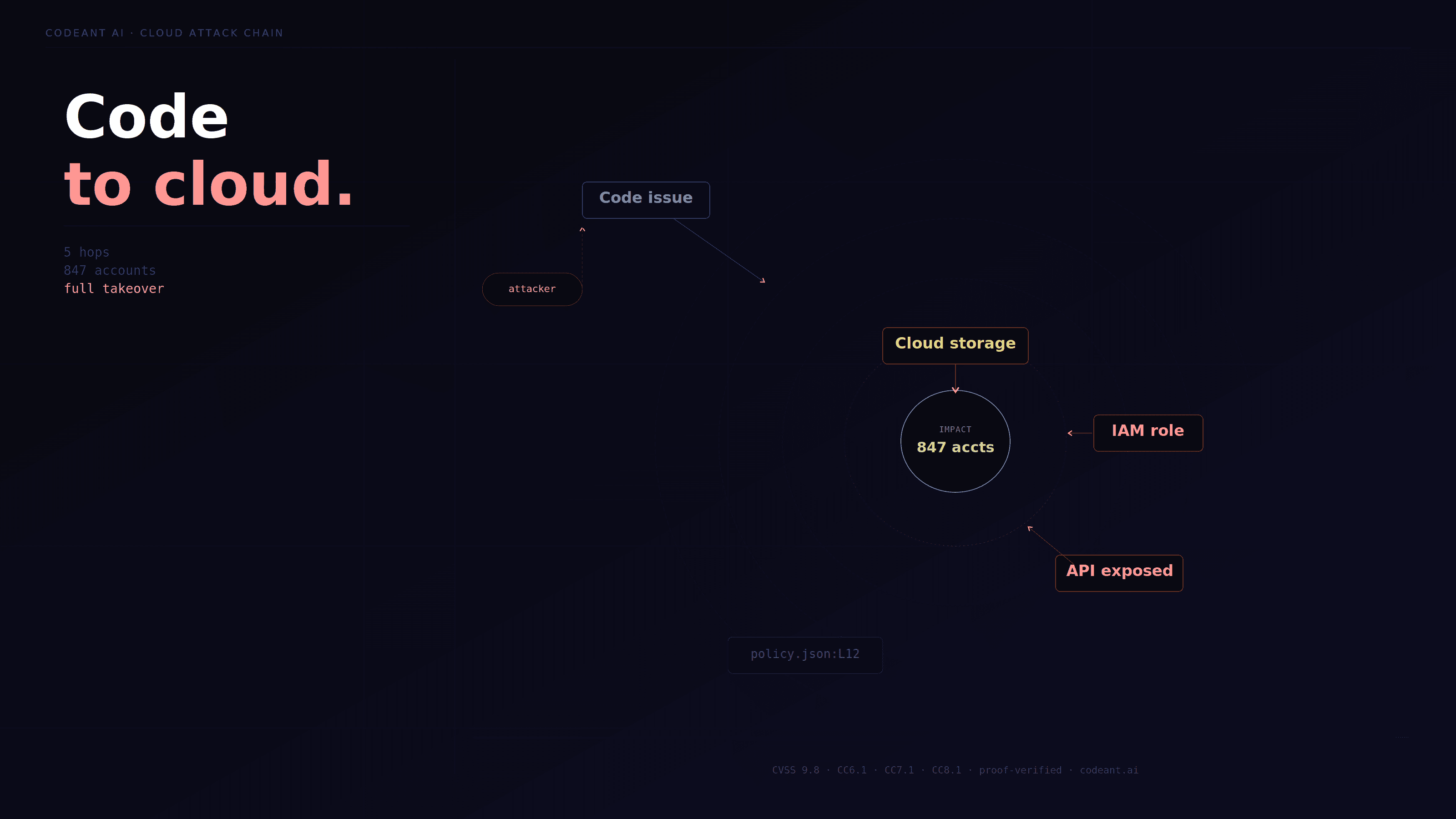
A traditional cloud security scan may tell you that a bucket is public, a port is open, or an IAM role has broad permissions. That is useful, but it is not the full story. Real attackers do not stop at isolated findings. They connect exposed assets, weak permissions, leaked credentials, APIs, and application flaws into working attack paths.
This is where AI penetration testing become valuable.
They help security teams move from cloud visibility to cloud exploitability.
Instead of asking only:
“Is this AWS, Azure, or GCP asset misconfigured?”
The better question is:
“Can an attacker use this cloud exposure to access data, escalate privileges, or move deeper into the system?”
In this guide, we will cover how AI-powered cloud pentesting works, what to test across AWS, Azure, and GCP, how it compares to traditional manual pentesting, and what to look for in a modern cloud security testing platform.

What Is AI Pentesting For Cloud Infrastructure?
AI pentesting for cloud infrastructure is the use of AI-assisted reconnaissance, cloud asset discovery, permission analysis, exploit validation, and attack path construction to test cloud environments the way adversaries would.
It is not just checking configurations.
It is testing whether cloud misconfigurations, exposed services, identity permissions, secrets, and application vulnerabilities can be combined into real compromise paths.
A strong AI cloud pentest should evaluate:
Public cloud assets
Identity and access management
Storage permissions
Exposed services
Kubernetes clusters
Serverless functions
Cloud metadata access
CI/CD secrets
APIs and application endpoints
Cross-cloud exposure
Exploit chains
The goal is to understand practical risk.
For example, a public bucket may be low impact if it contains only public assets. But a public bucket containing customer exports, signed URLs, or deployment artifacts can become critical. An over-permissioned IAM role may look theoretical until it is chained with SSRF, leaked credentials, or an exposed CI/CD token.
AI pentesting helps connect those dots faster and more consistently.
Why Cloud Pentesting Needs A Different Methodology
Cloud environments are dynamic.
A virtual machine can appear and disappear in minutes. A developer can create a public storage bucket during testing. A CI/CD pipeline can deploy infrastructure automatically. A new API gateway route can expose an internal service. A role permission change can silently expand access.
This makes cloud pentesting different from traditional network pentesting.
Traditional infrastructure testing often focused on static assets such as:
IP addresses
Ports
Services
Operating systems
Firewall rules
Cloud infrastructure adds more layers:
Identity permissions
Service-to-service trust
Temporary credentials
Serverless execution
Managed databases
Storage policies
Cloud-native logging
Infrastructure as code
CI/CD workflows
External APIs
This means cloud security testing must answer more than “what is exposed?”
It must also answer:
Who can access it?
What permissions does it inherit?
What secrets can it reach?
What services trust it?
Can it be chained with application flaws?
Can the impact be proven?
That is why cloud penetration testing increasingly needs AI-assisted reasoning, automation, and code-level context.
AI Pentesting Vs Traditional Manual Cloud Pentesting
Manual cloud pentesting is still valuable. Skilled testers can reason through unusual configurations, inspect architecture, and identify edge cases.
But manual testing has constraints.
It is often time-boxed, dependent on scope, and difficult to repeat continuously across fast-changing environments.
AI-powered cloud pentesting improves:
Speed of reconnaissance
Coverage across large environments
Correlation between assets
Repeated validation
Attack path discovery
CI/CD-triggered testing
Retesting after remediation
Manual pentesting may find deep issues during an engagement.
AI pentesting helps teams continuously monitor and validate cloud risk as the environment changes.
The best approach is not AI versus humans.
The best approach is AI-assisted pentesting with strong methodology, evidence, and expert validation where needed.
What AI Pentesting Should Cover In AWS
AWS environments often contain the largest and most complex cloud attack surfaces because of the depth of AWS services and IAM permissions.
IAM privilege escalation
AWS IAM is one of the most important areas to test.
AI pentesting should analyze whether users, roles, or services can escalate privileges through:
Overly broad policies
iam:PassRoleRole assumption
Policy attachment permissions
Lambda execution roles
EC2 instance profiles
Cross-account trust relationships
Access key exposure
A permission that looks harmless alone may become dangerous when combined with another permission.
For example, the ability to pass a role to Lambda or EC2 can become a privilege escalation path if the role has broader permissions.
S3 bucket exposure
S3 misconfigurations remain a common cloud risk.
Testing should verify:
Public read access
Public write access
Misconfigured bucket policies
Sensitive customer data exposure
Signed URL abuse
Backup file exposure
Static website hosting leaks
Cross-account access mistakes
A public bucket is not always critical, but a public bucket containing customer exports, logs, or credentials can be severe.
EC2 and metadata service abuse
EC2 instances should be tested for exposure and credential risk.
Important areas include:
Public SSH or RDP
Weak security groups
Exposed admin panels
SSRF to metadata service
IMDSv1 exposure
Instance profile credential theft
Misconfigured network access
SSRF-to-metadata is one of the most important cloud attack paths because it can turn an application vulnerability into cloud credential compromise.
Lambda and serverless risks
Serverless functions introduce different risks.
Testing should cover:
Over-permissioned execution roles
Public function URLs
Event trigger abuse
Secrets in environment variables
Insecure dependencies
Sensitive logging
Data exposure through function errors
Serverless is often treated as low-maintenance infrastructure, but security still depends heavily on permissions and input handling.
API Gateway exposure
AWS API Gateway often sits directly in front of SaaS APIs.
Testing should cover:
Broken authorization
Missing authentication
Excessive permissions
Rate limit bypass
Internal route exposure
JWT validation flaws
Misconfigured integrations
For SaaS teams, this is where cloud security and application security meet.
What AI Pentesting Should Cover In Azure
Azure environments have their own identity and configuration risks, especially around Microsoft Entra ID, role assignments, storage, and application registrations.
Azure identity and role assignments
Azure pentesting should evaluate whether users, service principals, managed identities, or applications have excessive permissions.
Important areas include:
Over-permissioned service principals
Managed identity abuse
Role assignment escalation
Subscription-level permissions
Key Vault access
App registration misconfiguration
Consent grant abuse
Identity is often the most important Azure attack surface.
A single over-permissioned service principal can create broad access across resources.
Azure Blob Storage exposure
Azure Blob Storage should be tested for:
Public containers
Anonymous read access
Shared access signature abuse
Sensitive backup exposure
Misconfigured access policies
Cross-tenant access mistakes
Like S3, storage exposure becomes critical when sensitive data or secrets are involved.
Azure App Service and functions
Testing should include:
Public endpoints
Misconfigured authentication
Exposed environment variables
Insecure deployment slots
Weak managed identity permissions
Secrets in application settings
Debug endpoint exposure
Deployment slots are often overlooked and can expose staging versions of applications.
Azure Key Vault access
Key Vault is high impact because it stores secrets, keys, and certificates.
Testing should verify:
Who can read secrets
Which identities have access
Whether applications expose vault-backed secrets
Whether access policies are too broad
Whether logs detect secret access
Key Vault findings often become critical when chained with application or identity weaknesses.
What AI Pentesting Should Cover In GCP
GCP environments have different identity, service account, and project-level risks.
Service account abuse
GCP service accounts are central to many attack paths.
Testing should cover:
Over-permissioned service accounts
Service account key exposure
Token impersonation
Workload identity misconfiguration
Privilege escalation through IAM bindings
Excessive project-level roles
A leaked service account key can become a serious compromise if the account has broad access.
Cloud Storage exposure
GCP Cloud Storage should be tested for:
Public buckets
Sensitive object exposure
Weak IAM bindings
Signed URL abuse
Backup exposure
Logging gaps
As with AWS and Azure, storage impact depends on data sensitivity and access scope.
Cloud Run and Cloud Functions
Serverless services in GCP should be tested for:
Public invocation
Missing authentication
Over-permissioned runtime identities
Secrets in environment variables
Insecure outbound access
Vulnerable dependencies
A publicly invokable function may be acceptable for some workloads, but risky if it exposes sensitive operations.
GKE and Kubernetes exposure
Google Kubernetes Engine introduces risks around:
Public cluster endpoints
Weak RBAC
Exposed dashboards
Misconfigured service accounts
Secrets in pods
Container escape paths
Over-permissioned nodes
Kubernetes should never be treated as only an infrastructure problem. It often combines identity, network, secrets, and application risk.
Common Cloud Attack Paths AI Pentesting Should Validate
Cloud pentesting becomes most valuable when it validates attack paths, not isolated misconfigurations.
SSRF to cloud credentials
A vulnerable application endpoint allows server-side request forgery. The attacker reaches the cloud metadata service and retrieves temporary credentials. Those credentials provide access to storage, secrets, or other cloud services.
This is a classic cloud-native exploit chain.
Public storage to customer data exposure
A storage bucket or container is publicly readable. It contains exported customer reports, backups, logs, or internal files. The attacker downloads sensitive data without authentication.
This can become a compliance incident quickly.
Leaked CI/CD secret to cloud compromise
A secret appears in a build log, environment file, Git history, or JavaScript bundle. The attacker uses it to access cloud resources or deployment pipelines.
This connects application security with cloud infrastructure.
Over-permissioned role to privilege escalation
A user, service account, or role has permissions that allow privilege escalation. The attacker uses these permissions to attach policies, assume roles, create functions, or access secrets.
This is often missed when permissions are reviewed individually instead of as a graph.
Exposed admin service to infrastructure takeover
An admin panel, Kubernetes dashboard, database console, or cloud management interface is exposed publicly. Weak authentication or missing access control turns exposure into compromise.
This is why external attack surface monitoring matters.
How Automated Penetration Testing Improves Cloud Security
Automated penetration testing improves cloud security by continuously testing for exposure, misconfiguration, and exploitability as cloud environments change.
This is especially important because cloud drift happens constantly.
A team may have secure baseline policies, but real systems change through:
New deployments
Infrastructure as code updates
Manual console changes
Temporary exceptions
Staging environments
Third-party integrations
Emergency fixes
Automated cloud pentesting helps identify when those changes introduce risk.
Strong automated cloud testing should include:
Continuous cloud asset discovery
External attack surface monitoring
IAM path analysis
Storage exposure testing
API exposure detection
CI/CD secret checks
Exploit validation
Retesting after fixes
Compliance evidence
The key difference is validation.
A useful platform does not just say “this may be exposed.” It shows whether the exposure creates real impact.
Continuous Cloud Pentesting For CI/CD Pipelines
Cloud infrastructure is often deployed through CI/CD.
That means cloud pentesting should connect to deployment workflows.
A continuous cloud pentest workflow can trigger testing when:
Terraform changes are merged
A new API gateway route is deployed
A storage bucket policy changes
A new IAM role is created
A Kubernetes service becomes public
A serverless function is exposed
A security group allows public access
This helps teams catch cloud exposure close to the moment it is introduced.
For fast-moving SaaS teams, this is critical.
Security cannot rely only on quarterly reviews when infrastructure changes daily.
Where CodeAnt AI Fits In Cloud Infrastructure Pentesting
CodeAnt AI is not just a code review tool. It is not just a SAST product. It is not just a penetration testing product.
CodeAnt AI is a complete, agent-based defensive and offensive security platform.
On the defensive side, CodeAnt integrates into IDEs, CLI workflows, pull requests, and CI/CD pipelines. It reviews code for security and quality issues as developers write and ship code.
On the offensive side, CodeAnt maps the public exposure of the system and tests it like an adversary would. It performs external reconnaissance, reads source code, uses defensive analysis as memory, runs gray box testing with code context, and constructs exploit chains.
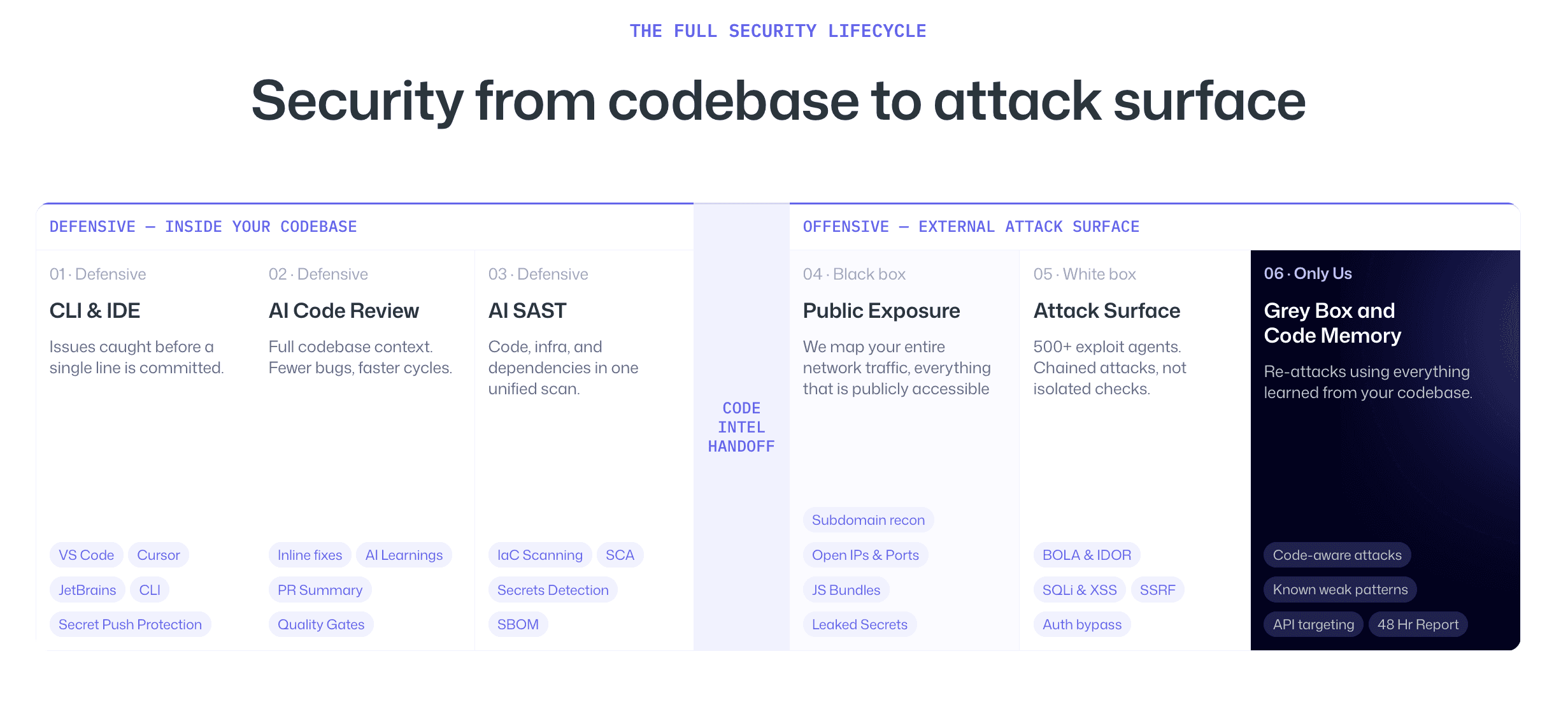
This is especially powerful for cloud infrastructure.
Cloud attack paths often cross code, APIs, secrets, identities, and external exposure.
The same platform that sees insecure patterns in code can also test whether those patterns create exploitable cloud paths after deployment.
For example:
Defensive analysis finds risky API behavior
External reconnaissance finds the exposed route
Cloud testing identifies an over-permissioned role
Gray box testing validates access
Exploit chaining proves business impact
That is the advantage of combining defensive and offensive security.
AI Pentesting For Web Application Security In Cloud Environments
Many cloud breaches start at the web application layer.
That is why prompts like best AI pentest tool for web application security connect directly to cloud infrastructure testing.
A cloud-native web application may expose:
API gateways
GraphQL endpoints
Authentication services
Serverless functions
Public storage links
CDN assets
JavaScript bundles
Backend integrations
If web application testing is separated from cloud testing, teams miss the real risk.
For example, an IDOR in a SaaS app may expose cloud-stored documents. A JWT validation flaw may allow access to admin APIs that trigger cloud operations. A leaked endpoint in a JavaScript bundle may reveal a serverless function that was never meant to be public.
Modern AI pentesting should test web application and cloud infrastructure together.
Cloud Pentesting For SOC 2, HIPAA, And Enterprise Reviews
Cloud penetration testing also supports compliance and customer trust.
For SOC 2, cloud testing can support controls around:
Logical access
Change management
Vulnerability management
Monitoring
Incident response readiness
For HIPAA-aligned healthcare SaaS, cloud testing should pay special attention to:
PHI exposure
Audit logging
Storage access controls
Identity permissions
Encryption boundaries
Data retention
Evidence handling
For enterprise security reviews, cloud pentest evidence helps answer:
What cloud assets are exposed?
What data could be accessed?
What was exploited?
Was the issue fixed?
Was the fix retested?
Is there proof?
A report with proof-of-exploit and retesting evidence is far more useful than a raw list of cloud scanner alerts.
How To Evaluate AI Cloud Pentesting Vendors
Use this checklist when comparing vendors.
Do they test AWS, Azure, and GCP?
Do they validate exploitability?
Do they analyze IAM and identity paths?
Do they test public storage exposure?
Do they include CI/CD secret exposure?
Do they connect cloud findings to application behavior?
Do they test APIs and web application attack paths?
Do they provide proof-of-exploit?
Do they support retesting?
Do they produce compliance-ready evidence?
Do they offer continuous testing?
Do they integrate with development workflows?
Do they explain how AI is used beyond basic automation?
The strongest vendors do not only identify cloud misconfigurations.
They show how those misconfigurations can become real attacks.
Conclusion: AI Cloud Pentesting Must Prove Real Attack Paths
Cloud security testing is no longer about checking whether individual settings look risky.
Modern cloud environments are too dynamic, interconnected, and identity-driven for that.
The real question is whether an attacker can combine exposed assets, weak permissions, application flaws, leaked secrets, and cloud misconfigurations into a working attack path.
That is where AI pentesting for cloud infrastructure becomes valuable.
It helps teams continuously discover exposure, validate exploitability, and understand how risk moves across AWS, Azure, GCP, APIs, CI/CD pipelines, and applications.
For SaaS and enterprise teams, the strongest approach is not defensive security alone or offensive testing alone. It is both working together.
CodeAnt AI is built around that model. It reviews code defensively in CI/CD and tests offensively against the external attack surface with that same code intelligence.
If you want to improve cloud security, do not stop at cloud posture alerts.
Start asking what an adversary can actually exploit across your cloud environment, and whether your current platform can prove it. Even best check out our AI penetration test that starts where others stop.
FAQs
What Is AI Pentesting For Cloud Infrastructure?
How Does AI-Powered Cloud Pentesting Compare To Traditional Manual Pentesting?
What Should AWS Penetration Testing Include?
What Should Azure And GCP Cloud Pentesting Include?
Which Automated Pentest Platforms Offer Continuous Cloud Testing?