Snyk and CodeAnt AI are both developer-first security platforms that use AI in their detection engines, but they use AI differently, cover different capabilities, and are built around different architectural assumptions. Snyk started as an SCA (software composition analysis) platform for open-source dependency scanning and expanded into SAST, container security, and IaC analysis. CodeAnt AI was built from the ground up as an AI-native platform combining code review, code quality, and security scanning into a single workflow that covers every stage of the development lifecycle, from pre-commit hooks that block secrets before they enter Git through the SecOps dashboard that proves compliance to auditors.
This blog compares both tools across the same six-dimension evaluation framework used in our full SAST tools comparison.
CodeAnt AI vs Snyk Code: Quick Summary

Dimension | Snyk Code | CodeAnt AI |
Primary Strength | Unified SCA + SAST + container + IaC platform | Unified AI code review + quality + security |
AI Tier | AI-Assisted | AI-Native |
Detection Engine | Proprietary AI (DeepCode) + rule engine | AI as primary detection engine |
Steps of Reproduction | ✗ (data flow visualization + priority scoring) | ✓ (every finding) |
Auto-Fix | AI-assisted (Snyk Fix, opens separate fix PR) | AI-generated one-click fixes in existing PR |
Security Coverage | SAST + SCA + Container + IaC + Secrets | SAST + SCA + Secrets + IaC + SBOMs |
Code Quality | ✗ | ✓ (complexity, duplication, dead code) |
Code Review | ✗ | ✓ (AI code review with inline comments) |
Container Scanning | ✓ genuine differentiator | ✗ |
Workflow Integration | CLI, IDE, PR, CI/CD, Dashboard | CLI → IDE → PR → CI/CD → SecOps |
IDE Support | VS Code, IntelliJ, Eclipse, Visual Studio | VS Code, JetBrains, Visual Studio, Cursor, Windsurf |
Pre-Commit / CLI | CLI scanning (no pre-commit secret blocking) | ✓ (blocks secrets, credentials, SAST/SCA issues before commit) |
SecOps Dashboard | Security posture dashboard | ✓ (vulnerability trends, OWASP/CWE/CVE, team risk, Jira/Azure Boards) |
SCM Support | GitHub, GitLab, Bitbucket, Azure DevOps + broad ecosystem | GitHub, GitLab, Bitbucket, Azure DevOps |
Deployment | Cloud + Snyk Broker (hybrid proxy) | Customer DC (air-gapped), Customer Cloud, CodeAnt Cloud |
Compliance | SOC 2 Type II | SOC 2 Type II, HIPAA, zero data retention |
Pricing Model | Per contributing developer | Per user ($20/user/month Code Security) |
Free Tier | Yes (limited tests per month; up to 5 users) | 14-day free trial |
Languages | 20+ languages | 30+ languages, 85+ frameworks |
Comparison verified against Snyk documentation and CodeAnt AI documentation as of February 2026. Features change, verify with both vendors before purchasing.
Where Snyk Code Excels
Snyk has built one of the most widely adopted developer security platforms in the market. Any honest comparison starts with what Snyk does well.
Broad Developer Ecosystem (CLI, IDE, CI/CD)
Snyk’s integration breadth is a genuine competitive advantage.
It provides:
A CLI for local scanning
IDE plugins for VS Code, IntelliJ, Eclipse, and Visual Studio
Native integrations with GitHub, GitLab, Azure DevOps, and Bitbucket
CI/CD integrations including Jenkins, CircleCI, and Travis CI
A well-documented API for custom workflows
This ecosystem maturity means Snyk can deliver findings wherever developers work, inside the IDE, via CLI, in pull requests, or in CI pipelines.
For teams with heterogeneous environments or IDE-first security preferences, Snyk’s integration coverage is difficult to match.
SCA + SAST + Container Scanning in One Platform
Snyk’s deepest strength is Software Composition Analysis (SCA). It scans open-source dependencies for known vulnerabilities using one of the most comprehensive vulnerability databases in the industry, covering:
npm
PyPI
Maven
NuGet
Dozens of additional ecosystems
Beyond SCA, Snyk extends coverage with:
Snyk Code (SAST) for first-party application code
Snyk Container for container image scanning
Snyk IaC for infrastructure-as-code configuration analysis
For teams primarily concerned with open-source dependency risk, and who prefer a single vendor for SCA, SAST, container, and IaC scanning, Snyk’s unified platform is a strong option.
A key advantage is centralized visibility: first-party and third-party vulnerabilities appear in a single dashboard, alongside license compliance tracking for open-source packages.
Container scanning is an area where Snyk provides coverage that CodeAnt AI does not currently offer. Teams with significant container infrastructure should weigh this difference carefully.
Large Community and Documentation
Snyk has a substantial developer community.
Its vulnerability database is publicly accessible and widely referenced. Documentation is detailed and includes tutorials, configuration examples, and integration guides for most common environments.
For evaluation and onboarding, community size matters. A large ecosystem means:
More Stack Overflow discussions
More blog posts from practitioners
More public reference architectures
This reduces adoption friction and shortens time to production.
Where CodeAnt AI Goes Further
CodeAnt AI addresses several gaps in the SAST experience that teams encounter with Snyk Code, particularly around AI detection depth, evidence-based findings, and the expansion from security scanning into code review and quality.
AI-Native vs. AI-Assisted Detection
Both Snyk Code and CodeAnt AI use AI in their detection engines, but the architecture differs.
In the AI tier taxonomy referenced in our SAST pillar:
Snyk Code is classified as AI-Assisted (Tier 2). It uses its proprietary engine (DeepCode, acquired in 2020) alongside rule-based detection. AI enhances and refines rule-based results.
CodeAnt AI is classified as AI-Native (Tier 3). AI is the primary detection mechanism, not an augmentation layer.
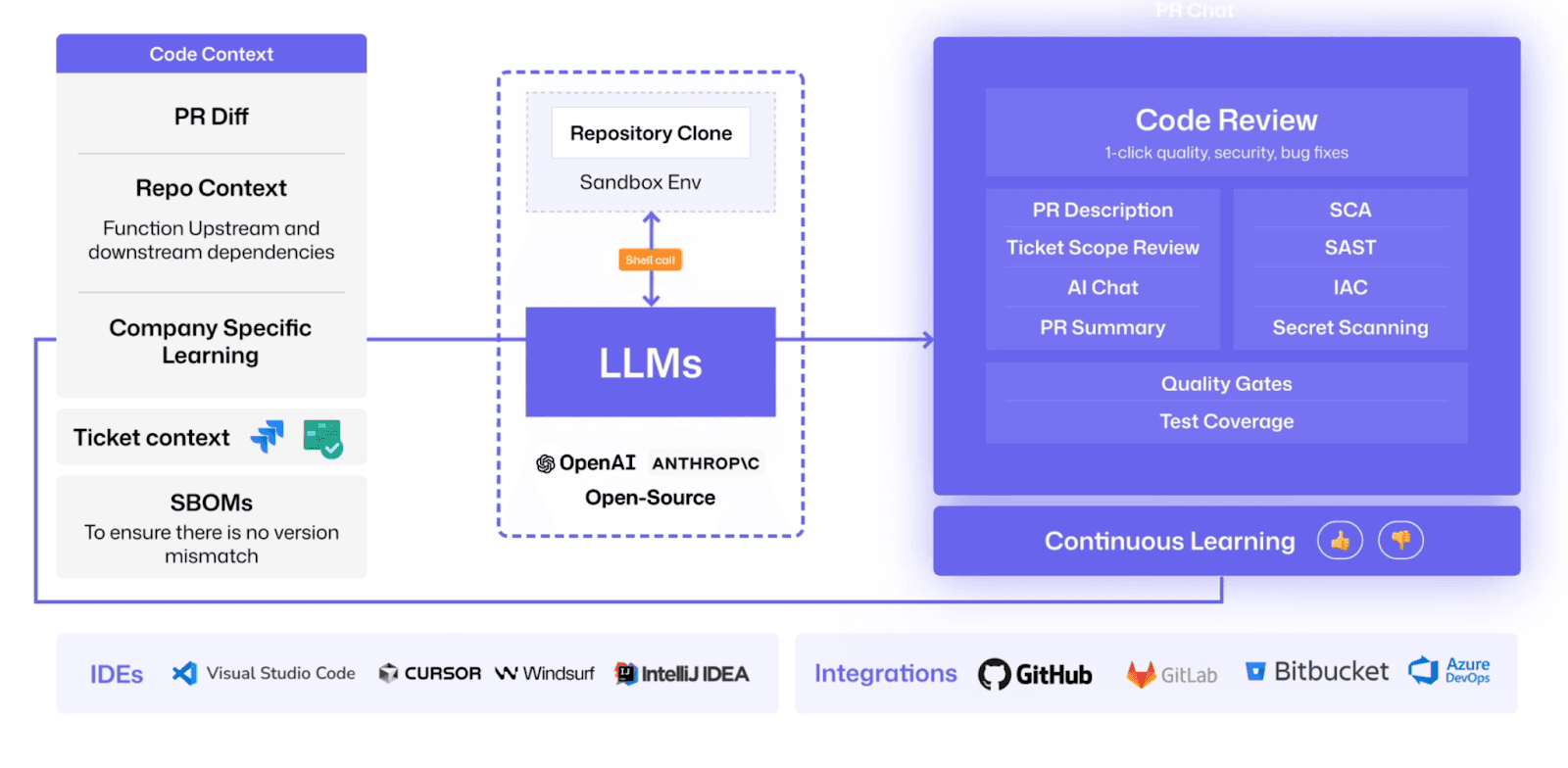
The practical difference appears in coverage for novel patterns. AI-Assisted tools are highly effective for well-known vulnerability classes where rule databases are mature.
AI-Native tools extend detection into areas where rules may not yet exist, including:
Vulnerabilities in AI-generated code
Complex multi-file taint flows
Business-logic flaws requiring semantic reasoning
Both tools scan code generated by assistants like Copilot. The distinction is architectural rather than a quality ranking. Snyk’s approach is proven and mature. CodeAnt AI’s AI-Native design targets the growing volume of AI-generated and novel code patterns in modern development.
Steps of Reproduction vs. Alert-Only Findings
When Snyk Code identifies a vulnerability, it provides:
A data flow visualization
CWE classification
Severity scoring
Snyk’s data flow view is clear and provides more context than many scanners.
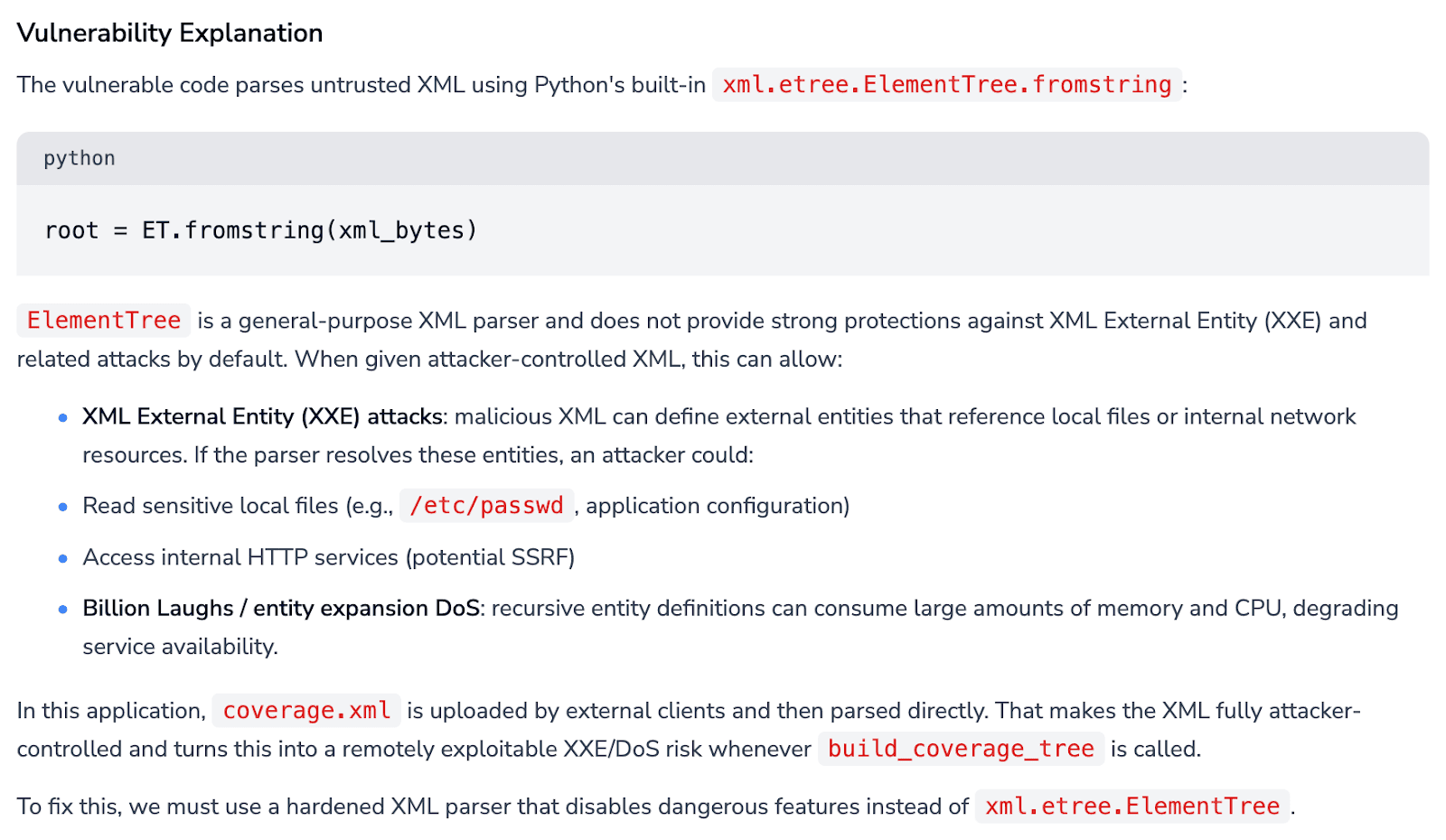
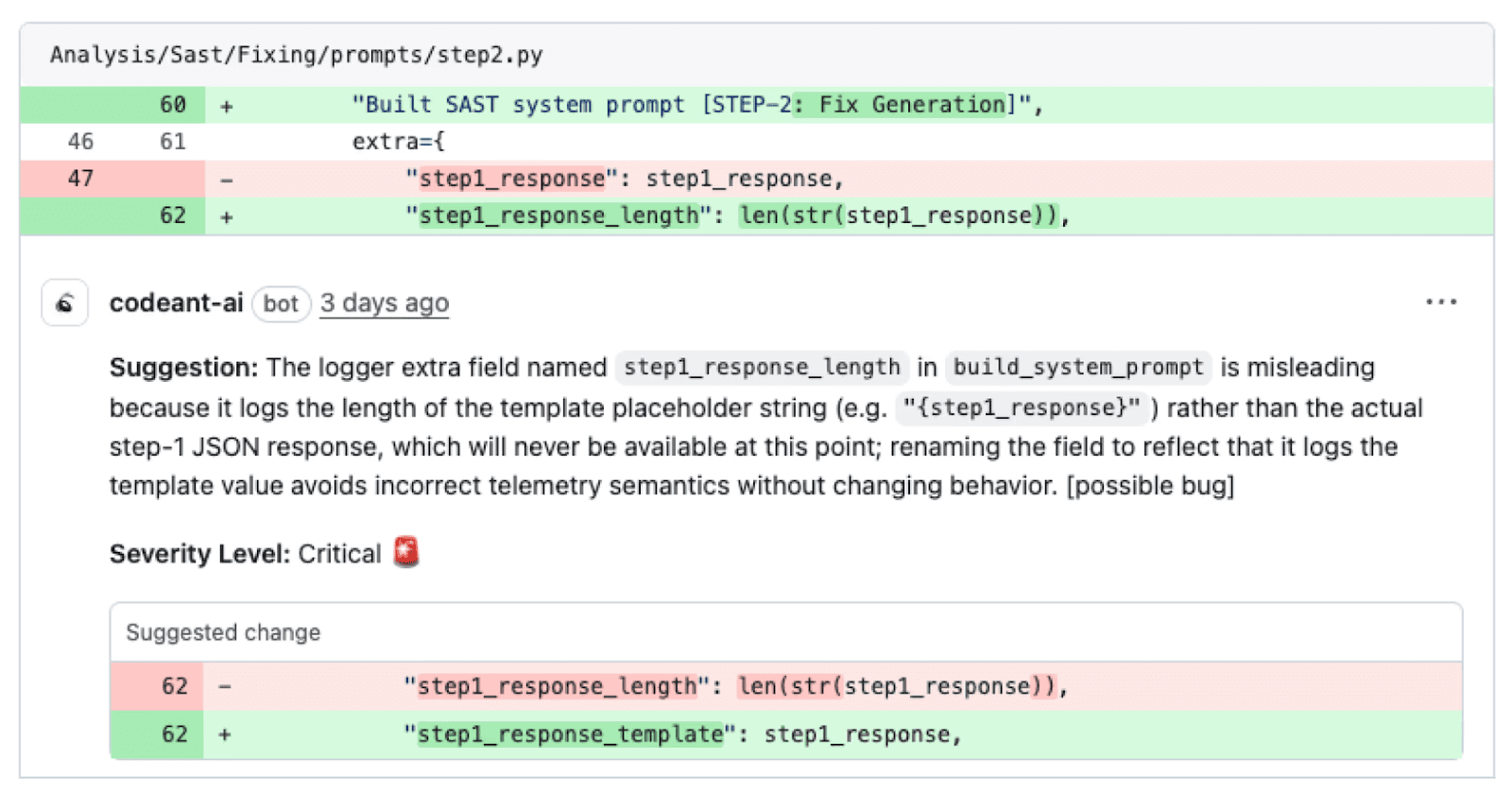
CodeAnt AI adds an additional layer: Steps of Reproduction for every finding, including:
Exact entry point
Complete taint flow across intermediate steps
Vulnerable sink
Concrete exploitation scenario proving triggerability
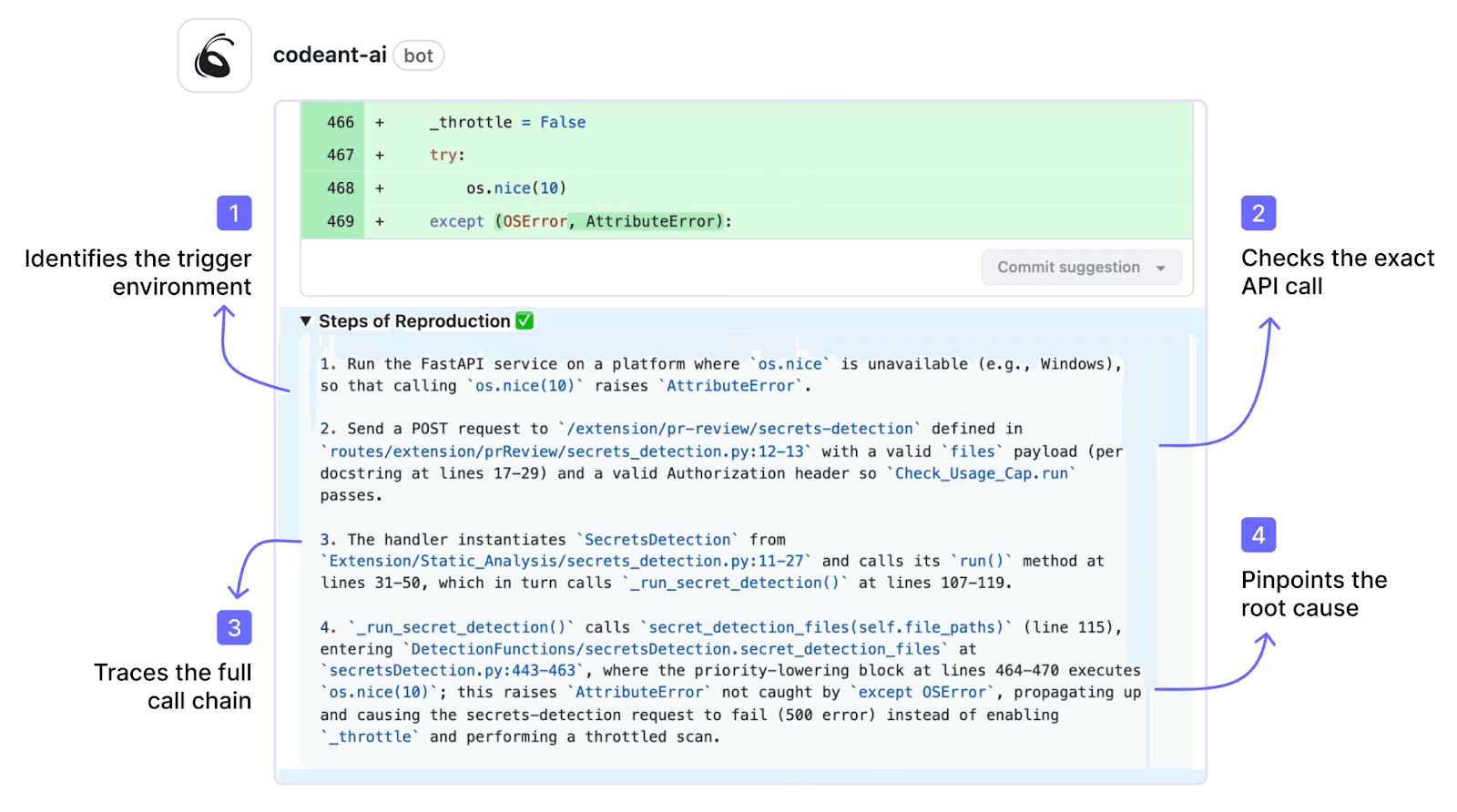
The difference is subtle but important:
Snyk shows where data flows.
CodeAnt AI proves how an attack works.
Evidence quality directly impacts remediation velocity.
When developers receive a reproducible exploitation scenario, validation is fast and resolution rates increase. When they receive a diagram and severity score, they must still determine exploitability within their context. That investigation increases review time and often results in findings being deferred.
PR-Native Code Review (Not Just Scanning)
Snyk Code integrates into pull requests by posting vulnerability findings. This is a security scanning workflow: scan → report → remediate.
CodeAnt AI extends the PR surface beyond scanning into AI-powered code review.
In addition to security findings, CodeAnt AI provides:
Line-by-line PR review for logic and maintainability
AI-generated PR summaries
Inline review comments
One-click committable fixes
In-PR chat to ask questions about the diff
This transforms the PR from a scan-report interface into an interactive review surface.
Snyk focuses on security scanning. Teams using Snyk typically pair it with:
GitHub native reviews
Code review tools like CodeRabbit
Manual peer review
CodeAnt AI consolidates scanning and code review into one workflow.
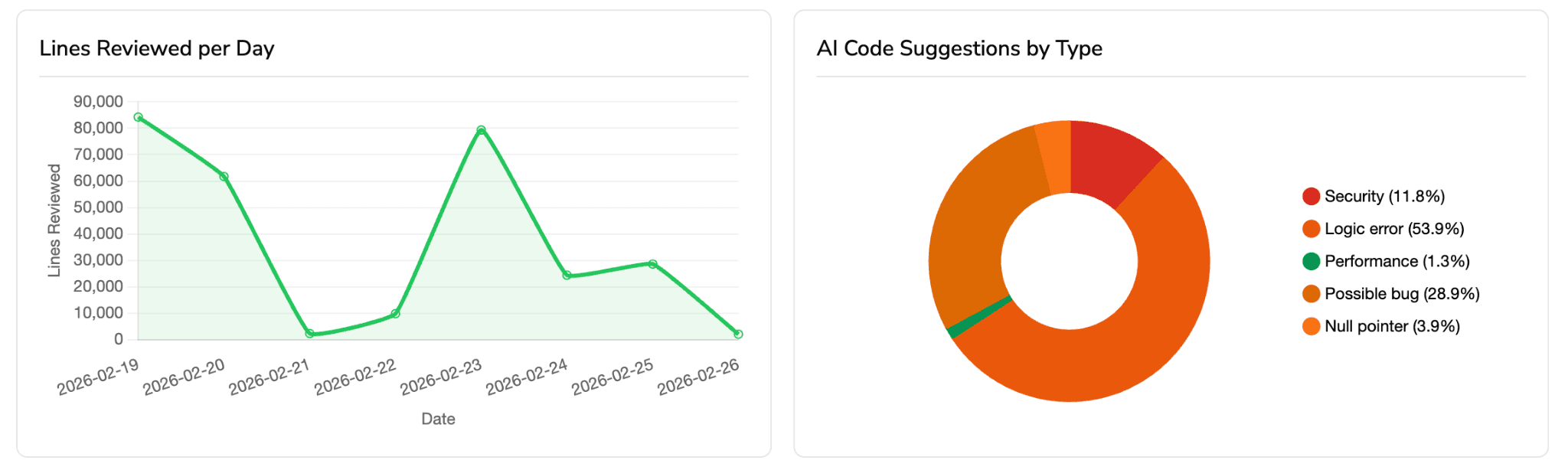
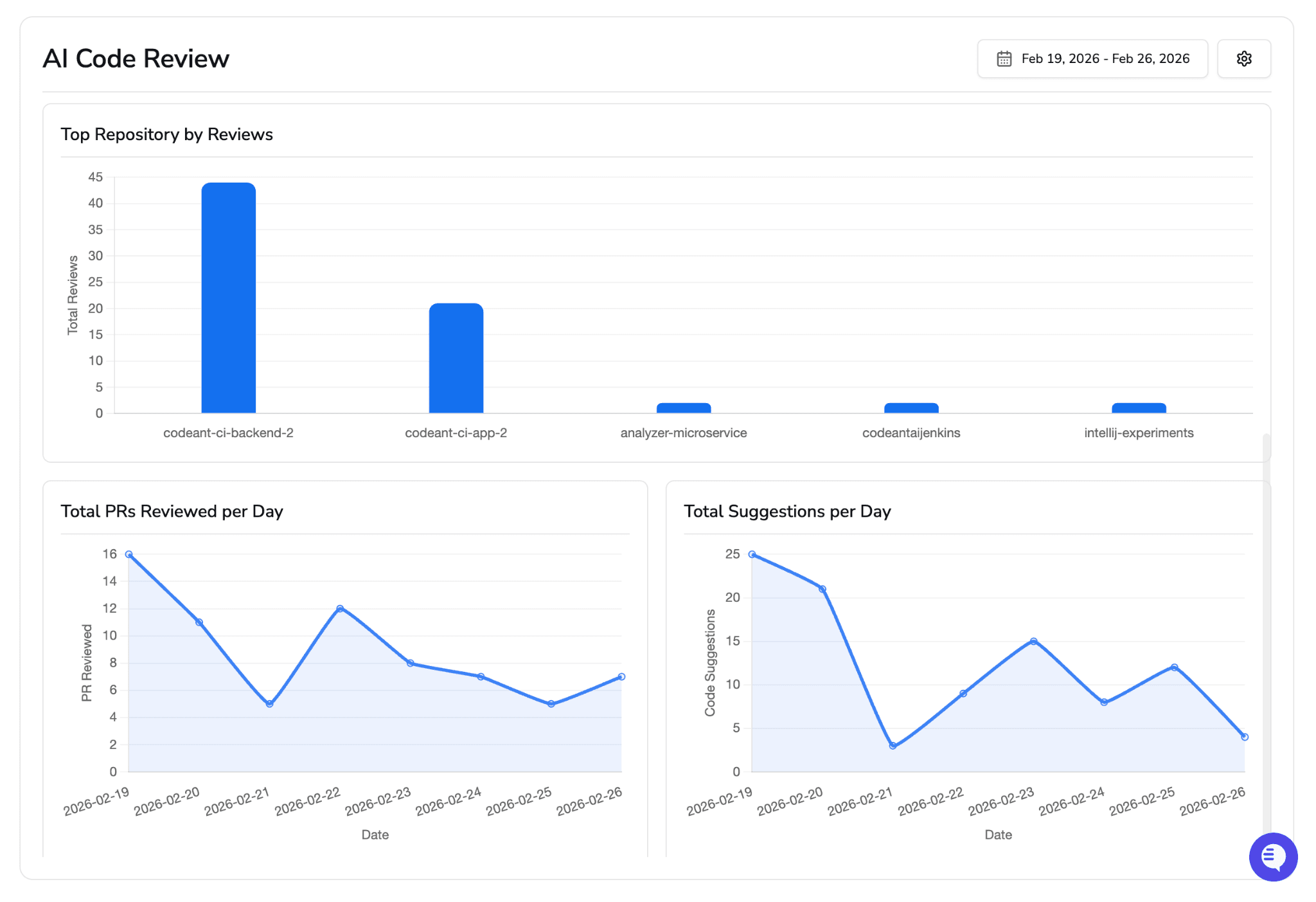
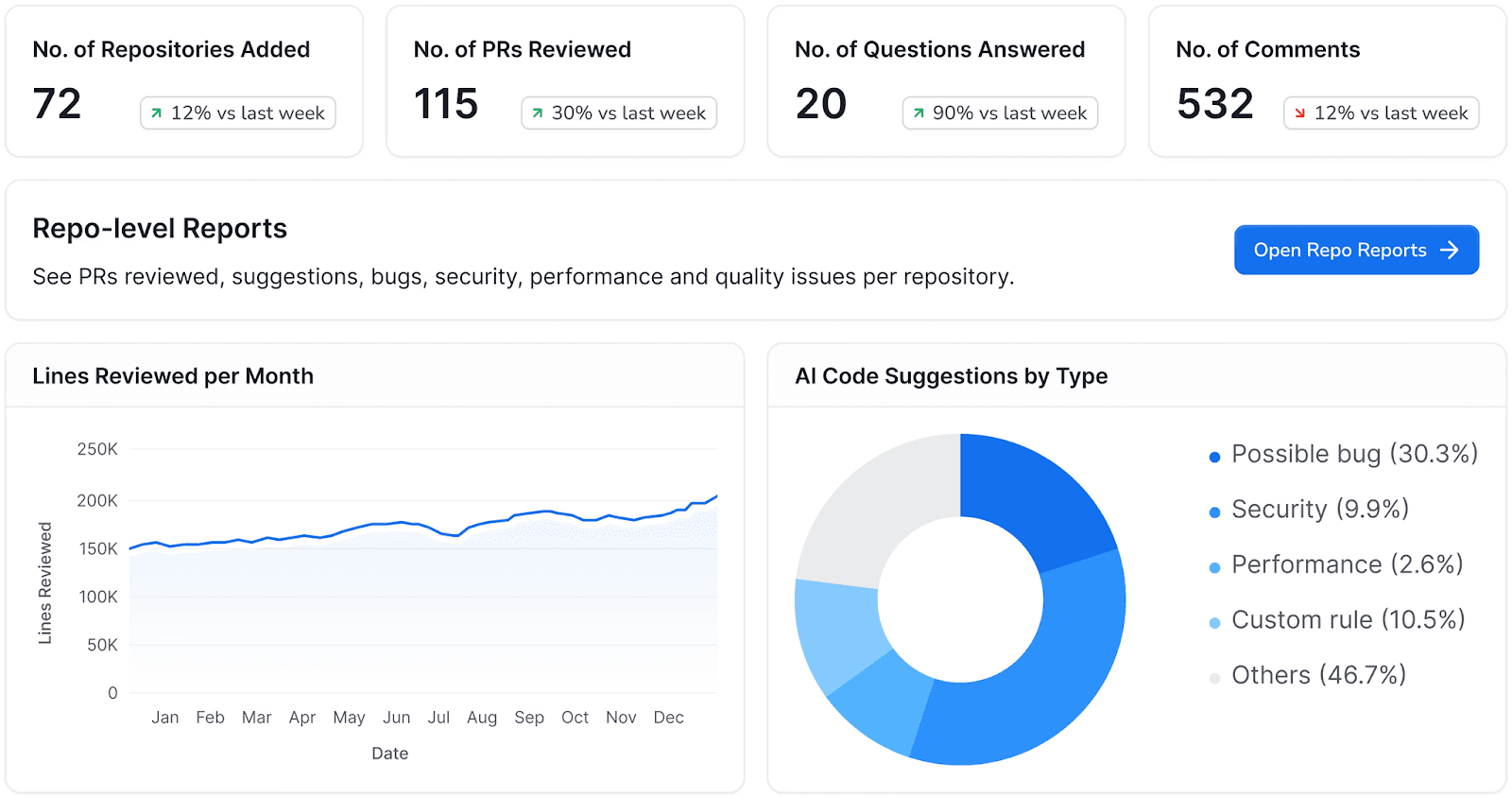
Developer Productivity Insights
CodeAnt AI includes developer productivity metrics that Snyk does not. DORA metrics (deployment frequency, lead time, change failure rate, mean time to recovery), PR cycle time tracking, SLA monitoring, and feature-level impact analysis by developer. These metrics help engineering managers identify bottlenecks, measure improvement, and communicate engineering health to stakeholders.
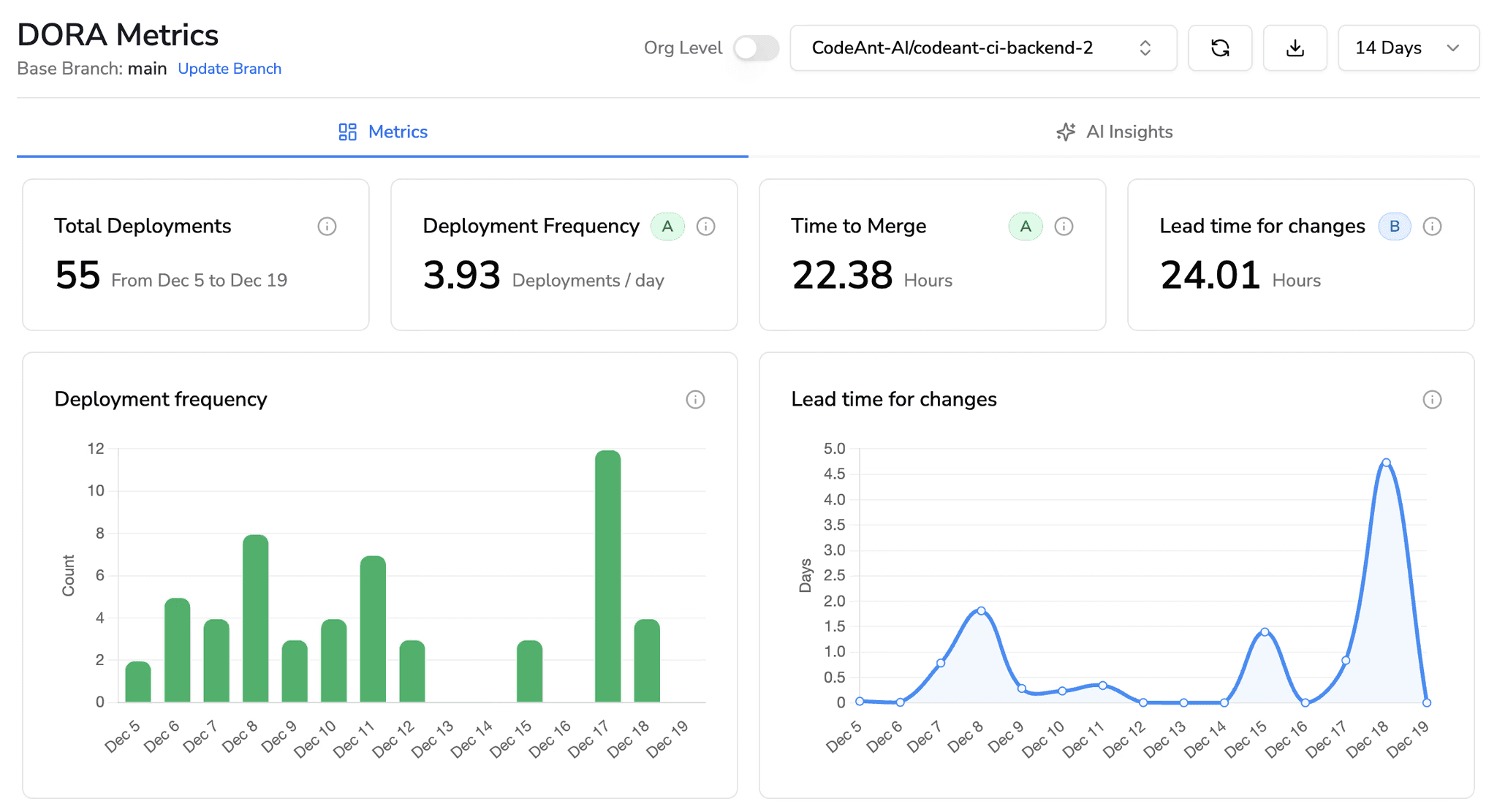
Snyk’s reporting focuses on security posture, vulnerability counts, remediation rates, and compliance status. This is valuable for security teams but does not address the broader engineering productivity question.
Feature-by-Feature Comparison
Feature | Snyk Code | CodeAnt AI |
Detection Accuracy | ||
SAST (first-party code) | ✓ (AI-Assisted, 20+ languages) | ✓ (AI-Native, 30+ languages) |
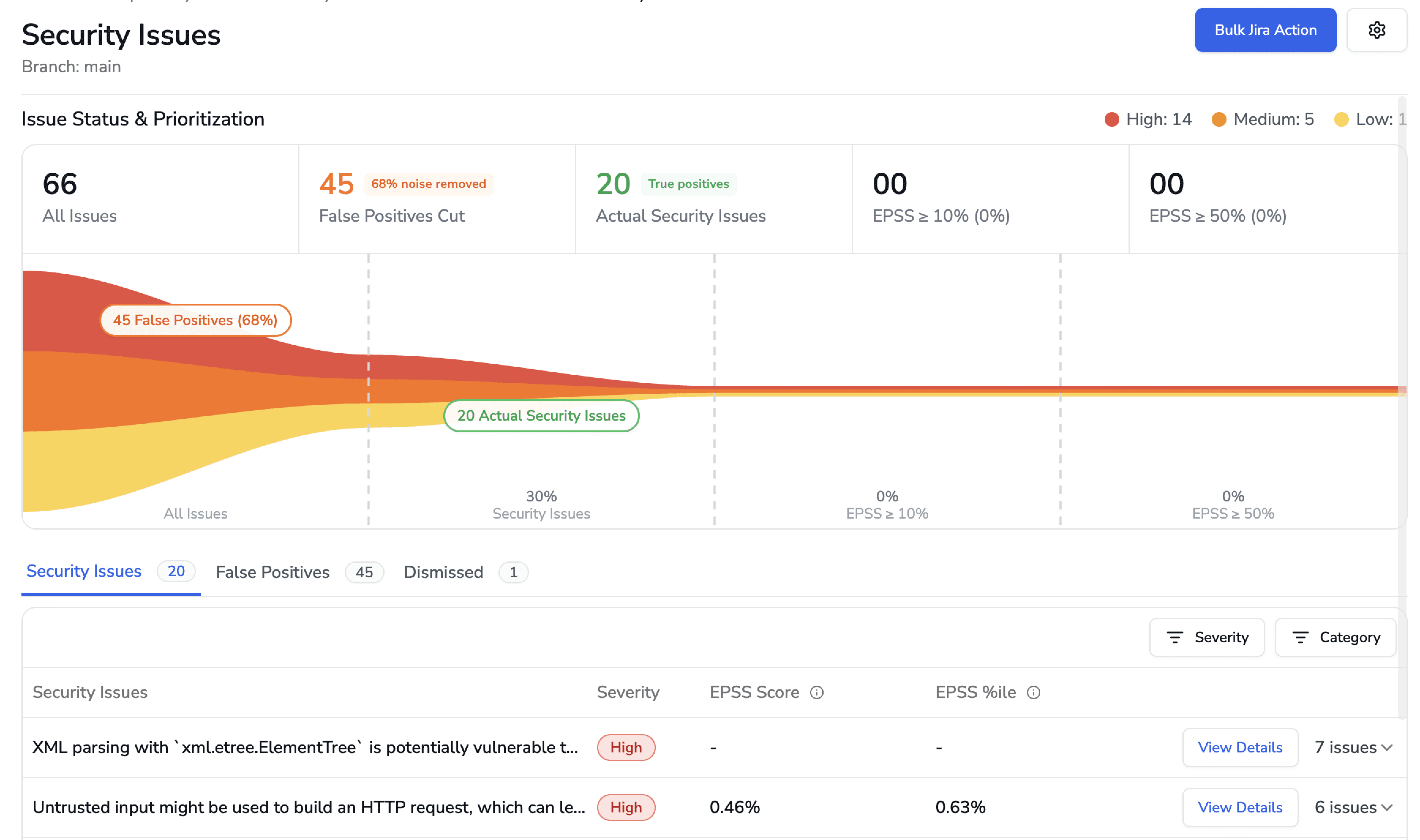
SCA (open-source dependencies) | ✓ platform’s core strength | ✓ (with EPSS scoring) |
Container scanning | ✓ | ✗ |
Secrets detection | ✓ | ✓ |
IaC scanning | ✓ | ✓ |
SBOM generation | ✓ | ✓ |
Cloud misconfiguration | ✗ | ✓ (AWS, GCP, Azure) |
Steps of Reproduction | ✗ | ✓ (every finding) |
AI Capabilities | ||
AI tier | AI-Assisted (Tier 2) | AI-Native (Tier 3) |
AI code review | ✗ | ✓ (line-by-line PR review) |
AI auto-fix | ✓ (Snyk Fix, opens separate fix PR) | ✓ (one-click committable fixes in existing PR) |
AI triage / false positive reduction | Partial (priority scoring) | ✓ (AI-native detection + reachability analysis) |
PR summaries | ✗ | ✓ |
Batch auto-fix | ✗ | ✓ (resolve hundreds of findings at once) |
Developer Experience | ||
Primary interface | Snyk dashboard + IDE + PR integration | PR-native (inline comments) |
CLI scanning | ✓ (mature CLI) | ✓ |
Pre-commit hooks (secret/credential/SAST blocking) | ✗ | ✓ (blocks before commit) |
IDE integration | ✓ (VS Code, IntelliJ, Eclipse, Visual Studio) | ✓ (VS Code, JetBrains, Visual Studio, Cursor, Windsurf) |
AI prompt generation for IDE fixes | ✗ | ✓ (generates prompts for Claude Code/Cursor) |
Inline PR comments | ✓ (scan results) | ✓ (review comments + findings + Steps of Reproduction + fix suggestions) |
One-click fix application | Partial (opens separate fix PR) | ✓ (committable suggestions in existing PR) |
Integrations | ||
GitHub | ✓ | ✓ |
GitLab | ✓ | ✓ |
Bitbucket | ✓ | ✓ |
Azure DevOps | ✓ | ✓ |
CI/CD pipelines | ✓ (broad — Jenkins, CircleCI, Travis, etc.) | ✓ (GitHub Actions, Jenkins, GitLab CI, Bitbucket Pipelines, Azure DevOps Pipelines) |
Jira integration | ✓ | ✓ (native) |
Pricing | ||
Free tier | Yes (limited tests/month; up to 5 users) | 14-day free trial |
Pricing model | Per contributing developer | Per user |
Starter price | $25/dev/mo (Team; max 10 devs) | $20/user/month (Code Security) |
Enterprise | Custom ($5K–$70K+/yr typical) | Custom |
Enterprise Readiness | ||
Deployment options | Cloud + Snyk Broker (hybrid proxy) | Customer DC (air-gapped), Customer Cloud (AWS/GCP/Azure), CodeAnt Cloud |
SOC 2 Type II | ✓ | ✓ |
HIPAA | ✗ | ✓ |
Zero data retention | ✗ | ✓ (available across all deployment models) |
SecOps dashboard | Security posture dashboard | ✓ (vulnerability trends, fix rates, team risk, OWASP/CWE/CVE mapping) |
Ticketing integration | Partial (Jira via third-party) | ✓ (Jira, Azure Boards, native) |
Audit-ready reporting | Security-focused reports | ✓ (PDF/CSV exports for SOC 2, ISO 27001) |
Attribution / risk distribution | ✗ | ✓ (repo-level and developer-level risk) |
Code quality analysis | ✗ | ✓ (code smells, duplication, dead code, complexity) |
Developer productivity metrics | ✗ | ✓ (DORA, PR cycle time, SLA tracking) |
Last verified: February 2026. Sources: Snyk documentation, Snyk pricing, CodeAnt AI documentation, CodeAnt AI pricing.
AI Capabilities Compared
Both tools market AI capabilities, but the architecture behind each differs meaningfully. This section unpacks what “AI” actually means in each platform.
Detection Approach
Snyk Code uses a hybrid approach: a proprietary AI engine (originally the DeepCode engine, which Snyk acquired in 2020) combined with traditional pattern matching rules. The AI component analyzes data flows and inter-file relationships, while the rule engine catches well-known vulnerability patterns. This AI-Assisted approach is effective because it combines the reliability of rules with the flexibility of ML-based analysis.
CodeAnt AI uses AI as the primary detection mechanism, the scanner reasons about code semantics and intent, not just patterns. This AI-Native approach is designed to detect vulnerability classes that rule databases have not yet cataloged, including novel patterns in AI-generated code and business-logic vulnerabilities that require contextual understanding.
Where this difference matters most: Snyk Code’s AI engine is strongest in well-documented vulnerability classes (OWASP Top 10, CWE Top 25) where training data is abundant. CodeAnt AI’s AI-native engine adds value in scenarios where patterns are novel, code flows are complex, or the vulnerability requires understanding what the code is supposed to do, not just what syntax it uses.
Auto-Fix Quality
Both tools offer AI-powered fix suggestions, but the delivery mechanism differs. Snyk Fix generates a fix and opens a new pull request with the remediation applied. This works well for SCA fixes (dependency version bumps) where the fix is a single line change. For SAST fixes (first-party code changes), the separate-PR model adds a step: the developer must review and merge the fix PR, then return to their original work.
CodeAnt AI generates fixes as committable suggestions within the existing pull request. The developer sees the vulnerability, the Steps of Reproduction, and the suggested fix, all inline in the same PR. They click “Apply Fix” and the change is committed directly.
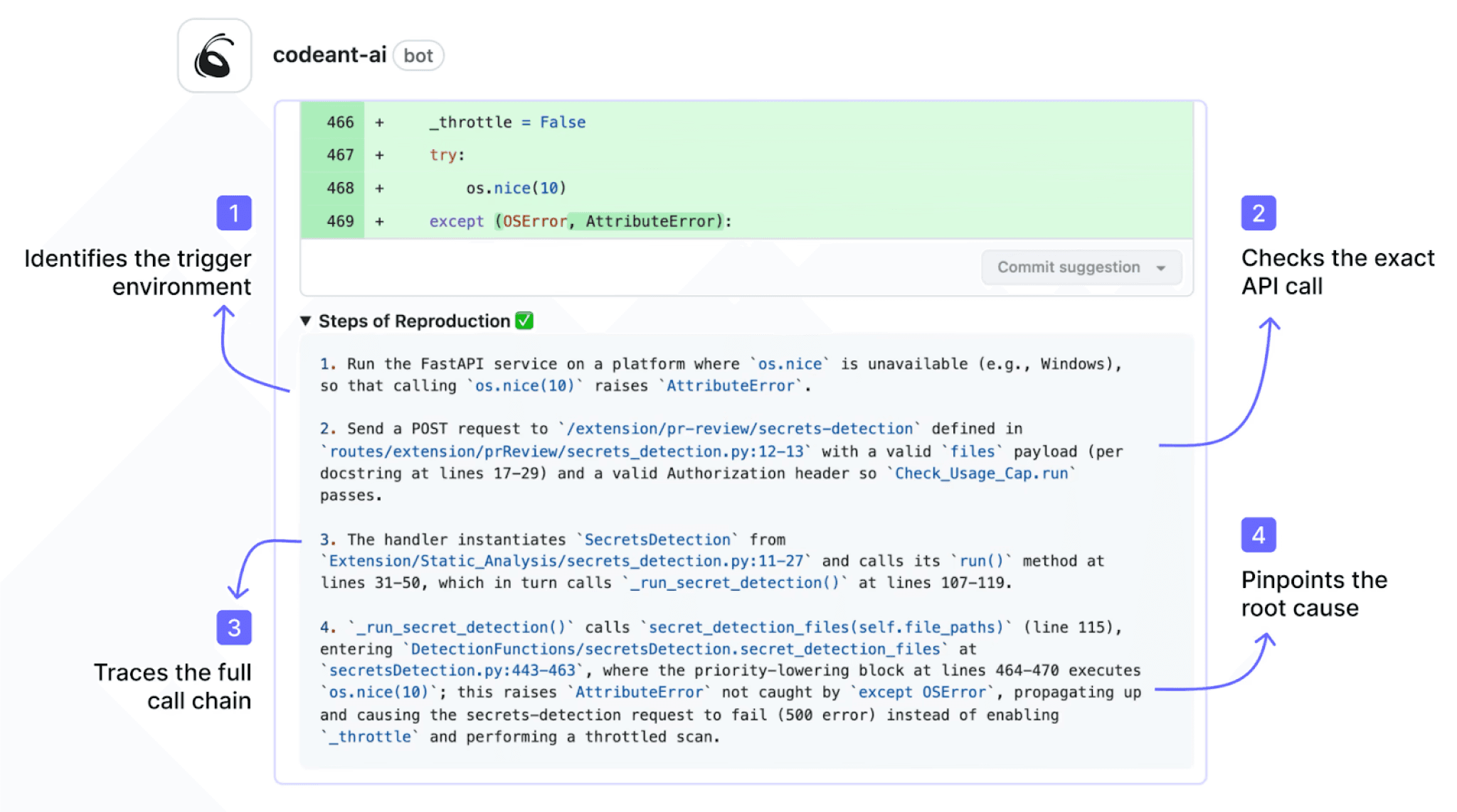
No separate PR, no additional merge step. This is a workflow difference that compounds: across dozens of findings per sprint, the per-finding time savings add up.
False Positive Handling
Snyk Code provides priority scoring and data flow visualization to help developers assess whether a finding is real. The data flow view shows the path from source to sink, which is helpful context. However, the developer still needs to interpret the data flow and determine exploitability themselves.
CodeAnt AI’s Steps of Reproduction go further: the tool provides a concrete exploitation scenario, specific input, specific code path, specific outcome (you can see the above figure), that makes the finding falsifiable. The developer does not need to interpret a data flow graph; they need to verify whether the stated conditions hold. This is a fundamentally faster validation process. For a deeper analysis of evidence-based false positive reduction, see how to reduce SAST false positives.
End-to-End Workflow Comparison (CLI → IDE → PR → CI/CD → SecOps)
Snyk integrates at multiple stages of the developer workflow: CLI, IDE, PR, and CI/CD, and does this well. This is not a case where the competitor covers one stage and CodeAnt AI covers five. The comparison here is about depth at each stage and coverage of the full lifecycle, including the stages Snyk does not reach.
Workflow Stage | Snyk | CodeAnt AI |
CLI + Pre-Commit | ✓ CLI scanning ( | ✓ CLI blocks secrets, credentials, API keys, tokens, and high-risk SAST/SCA issues before |
IDE | ✓ VS Code, IntelliJ, Eclipse, Visual Studio. Real-time scanning with inline findings and severity indicators. Well-designed plugins with good developer adoption. | ✓ VS Code, JetBrains (IntelliJ, PyCharm, WebStorm), Visual Studio, Cursor, Windsurf. In-context scanning with guided remediation and one-click fixes. AI prompt generation triggers Claude Code or Cursor to auto-fix specific vulnerabilities, turning the IDE into an active remediation surface, not just a notification layer. |
Pull Request | ✓ PR scanning with findings posted to PR. Scan results, not code review. Snyk Fix opens a separate PR for remediation, developer must review and merge the fix PR, then return to their work. | ✓ AI code review + security analysis on every PR. Line-by-line review. Steps of Reproduction for every security finding. One-click AI-generated fixes committed directly in the existing PR. PR summaries. Developer never leaves the PR, never merges a separate fix PR. |
CI/CD | ✓ Broad pipeline integration, Jenkins, GitHub Actions, GitLab CI, CircleCI, Travis CI, Bitbucket Pipelines, Azure DevOps. | ✓ GitHub Actions, Jenkins, GitLab CI, Bitbucket Pipelines, Azure DevOps Pipelines. Configurable policy gates by severity, CWE category, OWASP classification, and custom rules defined in plain English. |
SecOps / Compliance | Partial. Security posture dashboard with vulnerability counts, remediation rates, and compliance status. Jira integration available (via third-party or native depending on plan). No native Azure Boards integration. Limited audit-ready export. | ✓ Unified SecOps dashboard: vulnerability trends over time, TP/FP rates, fix rates, EPSS exploit prediction scoring, OWASP/CWE/CVE mapping, team and repo risk distribution. Native Jira and Azure Boards integration. Audit-ready PDF/CSV reports for SOC 2, ISO 27001. Attribution reporting identifies which repos and developers introduce more risk. |
Snyk covers four of the five security workflow stages: CLI, IDE, PR, and CI/CD, and it covers them well.
The CLI is mature and widely adopted.
IDE plugins are polished and developer-friendly.
PR scanning works reliably.
CI/CD integrations are broad and production-ready.
Compared to tools like SonarQube, which focus primarily on CI/CD and dashboard reporting, Snyk’s workflow breadth is a genuine strength.
Where CodeAnt AI Extends the Workflow
CodeAnt AI goes further in three key areas: pre-commit enforcement, PR experience, and the SecOps layer.
1. Pre-Commit Enforcement vs. Scan-and-Warn
Snyk’s CLI can scan code locally, but it does not block commits. A developer can run snyk test, review findings, and still push secrets or vulnerable code to Git.
CodeAnt AI enforces prevention through pre-commit hooks. High-risk issues, including credentials and secrets, are blocked before the commit succeeds.
For credential security, this distinction is critical:
Snyk detects leaked API keys in a PR.
CodeAnt AI prevents them from ever entering the repository.
This is the difference between detection and enforcement.
2. PR Scanning vs. PR Review
Snyk scans pull requests and posts vulnerability findings. This is a scanning workflow: scan → report → remediate.
CodeAnt AI transforms the PR into a full AI-powered review surface. It provides:
Line-by-line AI code review
Inline comments on logic and maintainability
Steps of Reproduction for every security finding
Committable fix suggestions (one-click apply directly in the PR)
Automated PR summaries
Snyk Fix generates remediation as a separate pull request, which introduces an additional merge step. CodeAnt AI applies fixes directly within the existing PR, eliminating the context switch.
The difference is structural:
Snyk performs PR scanning.
CodeAnt AI performs PR review.
3. Security Dashboard vs. SecOps Platform
Snyk provides a security dashboard focused on vulnerability counts, remediation rates, and overall posture. This is valuable for security teams tracking risk.
CodeAnt AI extends this into a full SecOps layer designed for enterprise compliance and audit workflows. It adds:
Vulnerability trends over time
True positive vs. false positive filtering
OWASP, CWE, and CVE mapping
Team and repository risk attribution
Native Jira and Azure Boards ticketing
Audit-ready PDF and CSV reports for SOC 2 and ISO 27001
For organizations operating under compliance requirements, this difference is significant.
Snyk provides scan data. CodeAnt AI provides audit evidence.
Deployment and Data Residency
For enterprises with strict data residency, air-gapped, or regulatory requirements, deployment architecture matters as much as detection capabilities.
Snyk offers a proxy agent that allows Snyk to integrate with self-hosted Git repositories without exposing source code directly to Snyk’s cloud. This is a hybrid model, scan processing still relies on Snyk’s cloud infrastructure, with the Broker mediating access. For many teams, Snyk Broker is a reasonable solution that provides a security boundary without requiring on-premises infrastructure.
However, Snyk does not currently offer a fully air-gapped deployment where all processing occurs within the customer’s network. Teams in defense, government, or highly regulated financial services that require complete network isolation cannot use Snyk for these environments.
CodeAnt AI offers three deployment models:
1. Customer data center (air-gapped)
CodeAnt AI deploys entirely within a customer’s on-premises infrastructure, including fully air-gapped environments with zero external network connectivity. No code, no metadata, no telemetry leaves the customer’s network. The full workflow, CLI pre-commit scanning, IDE integration, PR-native findings, CI/CD policy gates, and the SecOps dashboard, operates entirely within the customer’s infrastructure.
2. Customer cloud (AWS, GCP, Azure)
CodeAnt AI deploys within a customer’s own cloud environment (VPC). The customer retains full control over infrastructure, data, and network boundaries. Data stays within the customer’s cloud account.
3. CodeAnt AI cloud
Teams use CodeAnt AI’s hosted infrastructure, which is SOC 2 Type II certified and HIPAA compliant. This is the fastest deployment option, no infrastructure to manage.
Zero data retention is available across all three models, code is analyzed in memory and never persisted to disk, even temporarily.
Pricing Comparison
Dimension | Snyk | CodeAnt AI |
Pricing model | Per contributing developer | Per user |
Free option | Yes (limited tests per month; up to 5 users) | 14-day free trial |
Team/starter tier | $25/dev/mo (Team; max 10 devs) | $20/user/month (Code Security) |
Enterprise tier | Custom ($5K–$70K+/yr typical per Vendr data) | Custom |
100-dev annual cost estimate | ~$30,000/yr (SAST only, Ignite plan) | $24,000/yr (Entire Code Security) |
Includes AI code review | ✗ (not available at any tier) | ✓ |
Includes code quality | ✗ (not available at any tier) | ✓ |
Includes container scanning | ✓ (Snyk Container, additional product) | ✗ |
Includes SecOps Dashboard + Jira/Azure Boards | Partial (security dashboard; limited ticketing) | ✓ |
Pricing page | snyk.io/plans |
Which Should You Choose?
There is no universally “better” tool. The right choice depends on where your real risk lives, and where your current workflow breaks.
Choose Snyk if:
Open-source dependency risk is your primary concern
You need industry-leading SCA and container image scanning
You want the broadest integration ecosystem across IDEs and CI/CD
You qualify for Snyk’s free tier (up to 5 users)
You already use Snyk for SCA and want to add SAST without changing vendors
Snyk is strongest when your biggest exposure sits in third-party code and containers.
Choose CodeAnt AI if:
You want AI-native detection beyond pattern matching
You need evidence-backed findings with Steps of Reproduction
You want AI code review and security scanning in the same PR
You need built-in code quality without adding SonarQube
You want enforced pre-commit secret blocking
You require a SecOps dashboard with audit-ready compliance exports
You want developer productivity metrics (DORA, PR cycle time, SLA tracking)
You need air-gapped, customer-cloud, or zero-retention deployment
You want to consolidate Snyk + SonarQube + code review into one platform
CodeAnt AI is strongest when your risk sits in first-party application logic and developer workflow friction.
Snyk operates at the dependency and container layer. CodeAnt AI operates at the code and PR layer. They solve different security surfaces and can complement each other without major overlap.
Run CodeAnt AI on a repository Snyk already scans.
Compare:
Detection depth
Evidence clarity
Fix velocity
Developer engagement
See the difference for yourself: Run CodeAnt AI on a repo Snyk already scans — start your free 14-day trial →
For a broader view beyond these two tools, see our full 15-tool SAST comparison.
FAQs
How does SAST pricing compare between Snyk and CodeAnt AI?
Which SAST tool is better for AI-generated code security?
Can CodeAnt AI replace Snyk for SAST and code review?
Does Snyk Code provide Steps of Reproduction for vulnerabilities?
What is the difference between AI-native and AI-assisted SAST?















