Most vulnerabilities do not become breaches on their own. They become breaches when multiple weaknesses interact.
A broken authorization check
A predictable identifier
An over-permissioned cloud role. Individually, each may look medium severity
Combined, they become a critical attack path.
This is where traditional penetration testing often falls short. It tends to report isolated findings. Attackers exploit chained conditions.
That gap is why interest in AI penetration testing, and unified code security platforms has accelerated.
Security leaders are no longer only asking:
Can this tool detect vulnerabilities?
Can this pentest satisfy compliance?
They are asking harder questions:
How can I improve my codebase security continuously?
What are the key features of a modern code security platform?
What is the best security platform for enterprises handling real exploit risk?
Those are not scanner questions. They are architecture questions.
This guide explains:
What AI penetration testing actually is
How automated penetration testing differs from conventional testing
How modern platforms improve codebase security
What to look for in enterprise security platforms
How CodeAnt combines SAST and offensive security into one system
What Is AI Penetration Testing And How Does It Work
AI penetration testing applies autonomous reasoning, exploit automation, source code intelligence, and attack chain analysis to emulate how sophisticated adversaries discover and exploit vulnerabilities.
Unlike traditional assessments that often combine manual testing with point tools, AI-driven penetration testing can continuously:
Map attack surfaces
Build evidence-driven test queues
Execute targeted exploit agents
Validate exploitability
Model chained attack paths
Prioritize findings by actual impact
The difference is important.
Traditional testing often asks: Does a vulnerability exist?
AI penetration testing asks: Can this vulnerability be exploited, chained, and turned into a breach?
That distinction changes prioritization.
Why This Matters
Organizations do not suffer breaches because they missed another medium-severity scanner finding.
They suffer breaches because they missed exploit paths. That is what automated penetration testing is built to uncover.
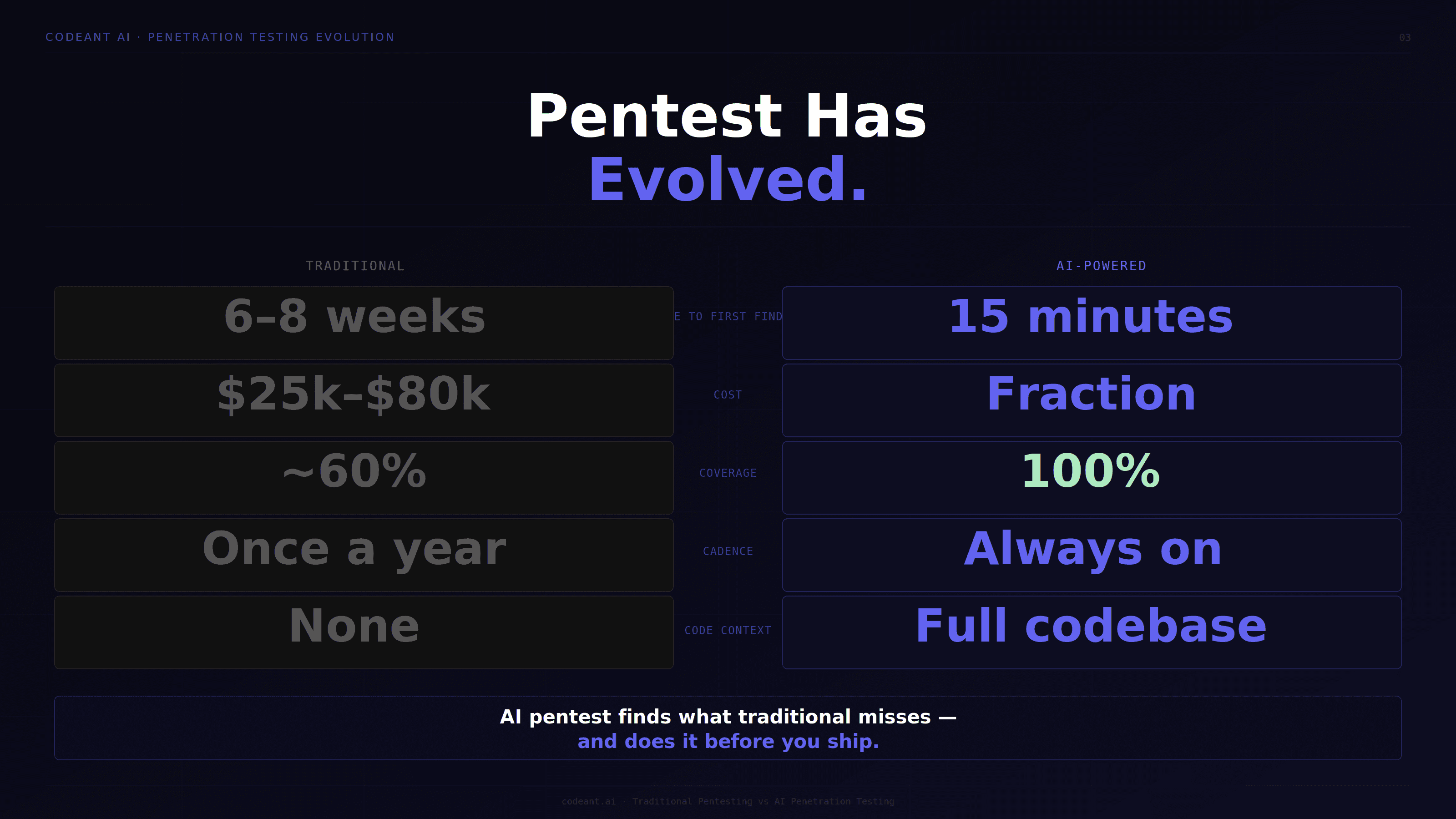
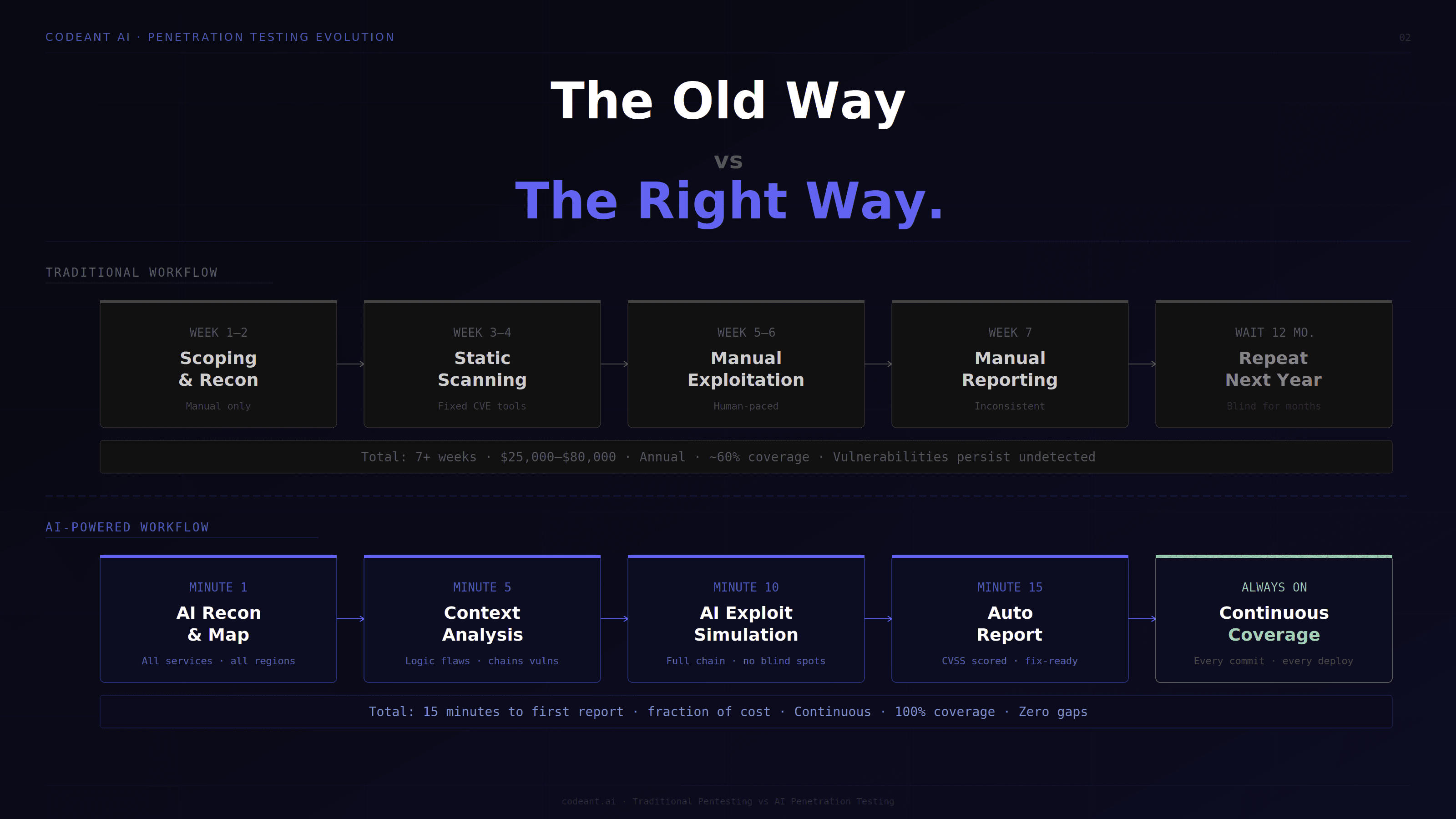
How Automated Penetration Testing Differs From Traditional Penetration Testing
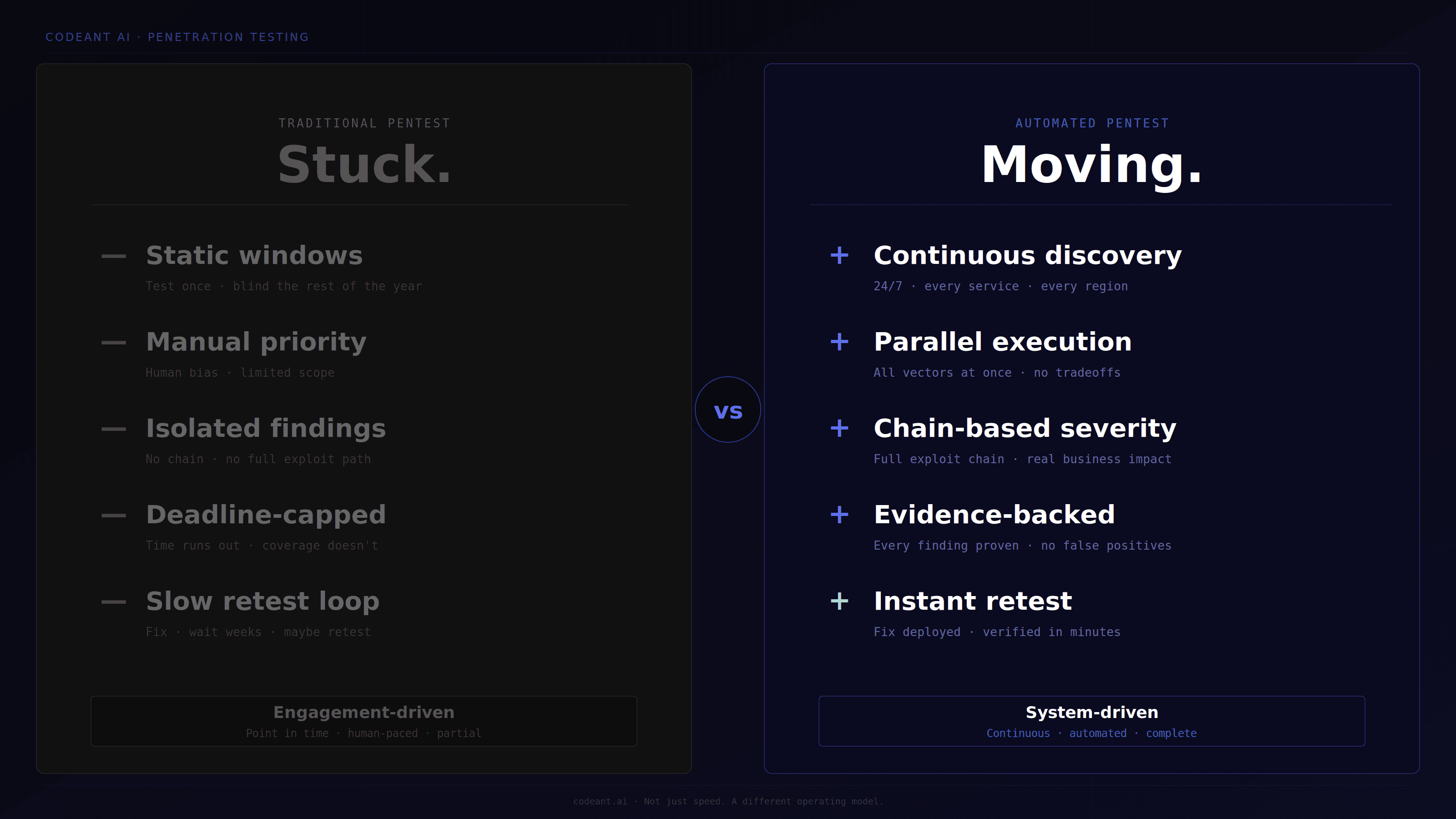
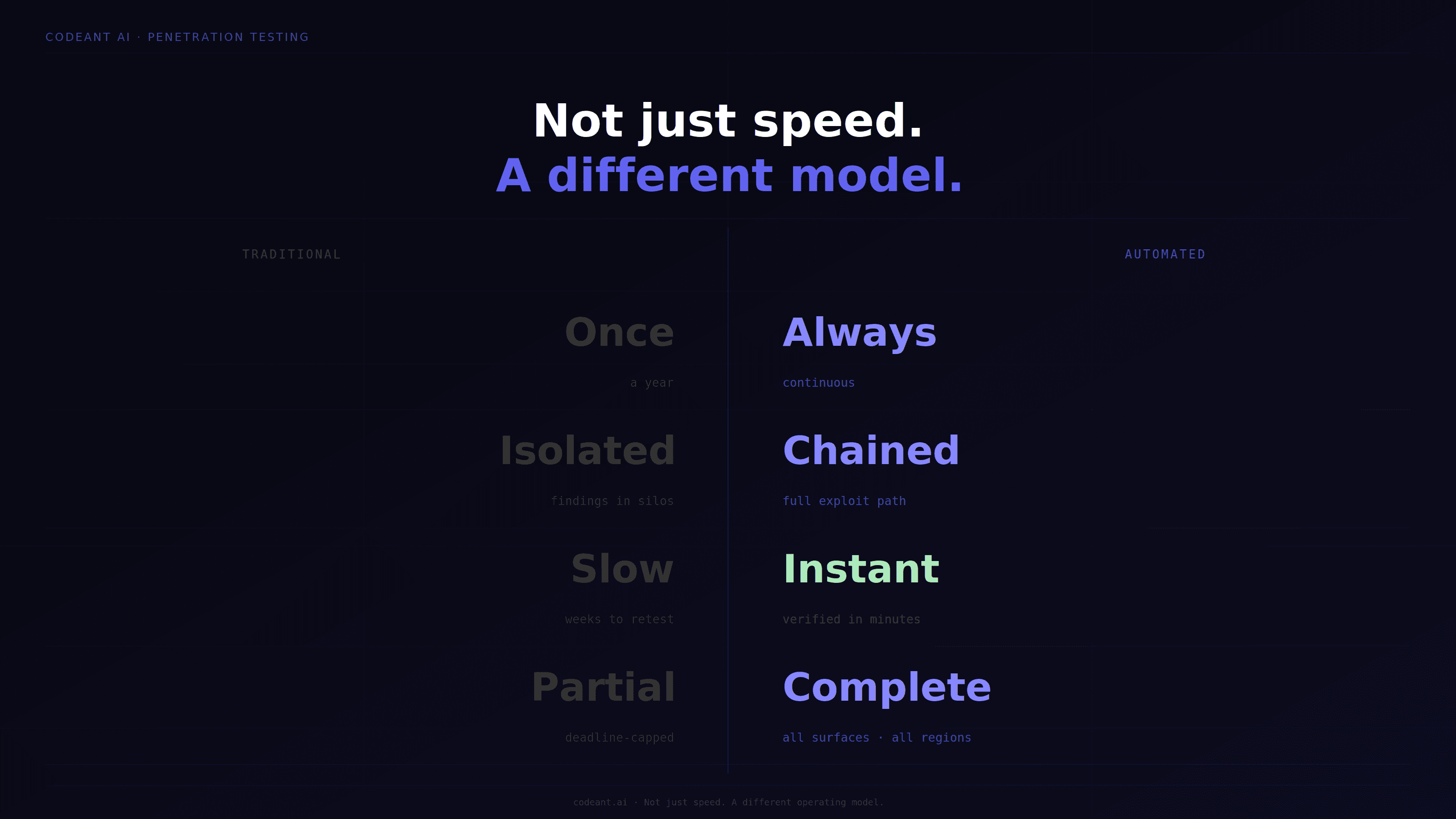
Traditional penetration testing is usually engagement-driven. While, automated penetration testing is system-driven.
Traditional Penetration Testing Often Struggles With
Static testing windows
Manual prioritization
Limited depth under time constraints
Findings reported in isolation
Slower remediation feedback loops
Automated Penetration Testing Improves
Continuous attack surface discovery
Parallel exploit execution
Evidence-backed validation
Chain-based severity analysis
Faster retesting and remediation verification
This is not simply speed. It is a different operating model.
Traditional Testing Example
A consultant reports:
IDOR issue
Weak session handling
Misconfigured CORS
Three medium findings. Backlog.
AI-Driven Testing Example
The system identifies:
CORS misconfiguration enables session theft
Session issue enables account takeover
IDOR enables cross-tenant access
One critical exploit chain. Different outcome.
How To Improve Your Codebase Security With AI-Driven Testing
Many teams ask:
How can I improve my codebase security beyond traditional SAST?
The answer is not adding more scanners. It is connecting prevention and validation.
Improve Codebase Security Through Three Layers…
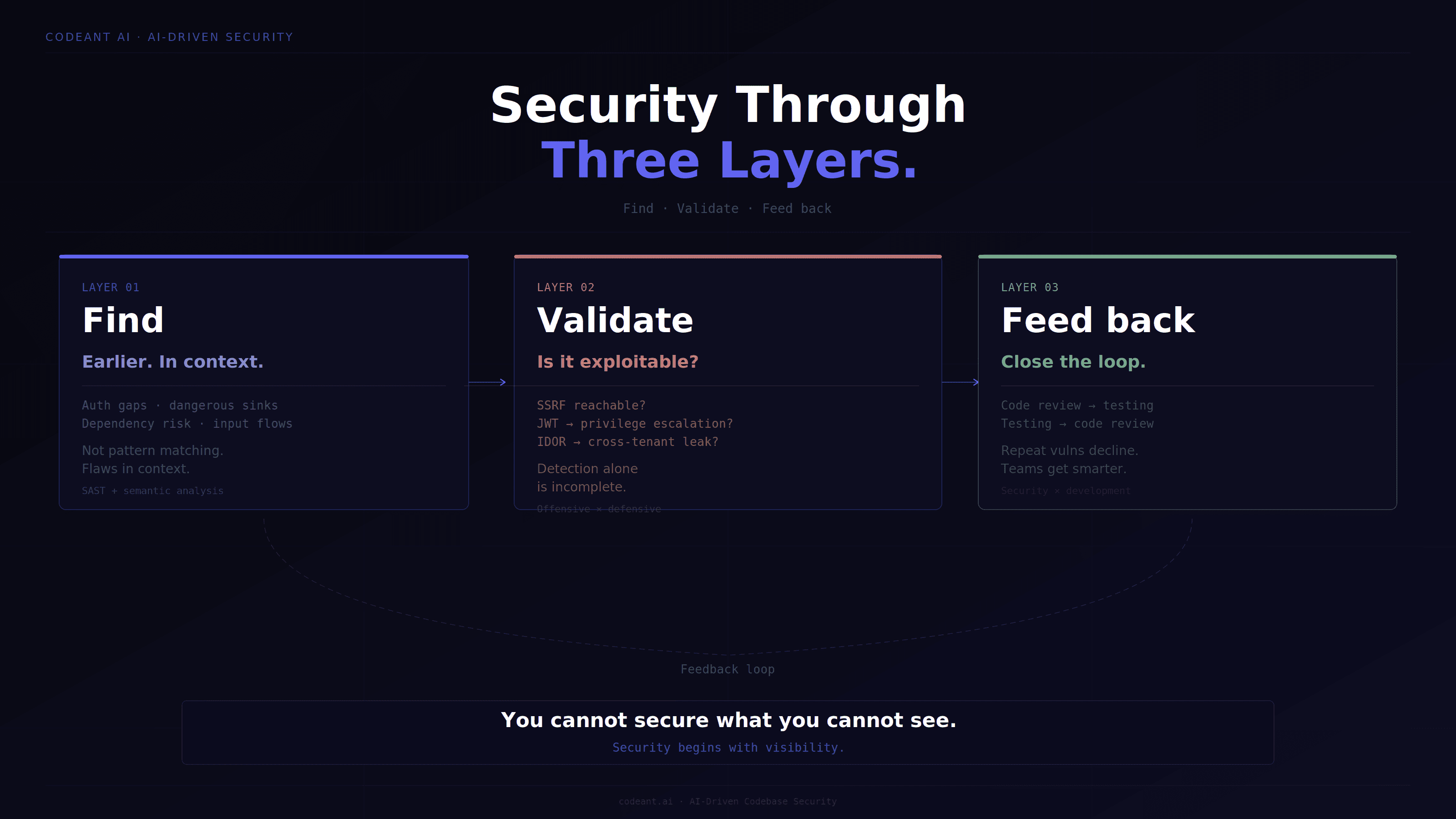
1. Find Vulnerabilities Earlier In Code
Strong platforms trace:
User-controlled inputs
Authentication logic
Authorization gaps
Dangerous sinks
Dependency risk
This goes beyond pattern matching. It finds flaws in context.
2. Validate Whether Code Weaknesses Are Exploitable
Detection alone is incomplete. Validation matters. Examples:
Is this SSRF actually reachable?
Can this JWT flaw escalate privileges?
Does this IDOR expose cross-tenant data?
This is where offensive testing sharpens defensive analysis.
3. Feed Exploit Findings Back Into Development
The strongest security programs create a feedback loop. Code review informs testing. Testing informs code review. That is how repeat vulnerabilities decline.
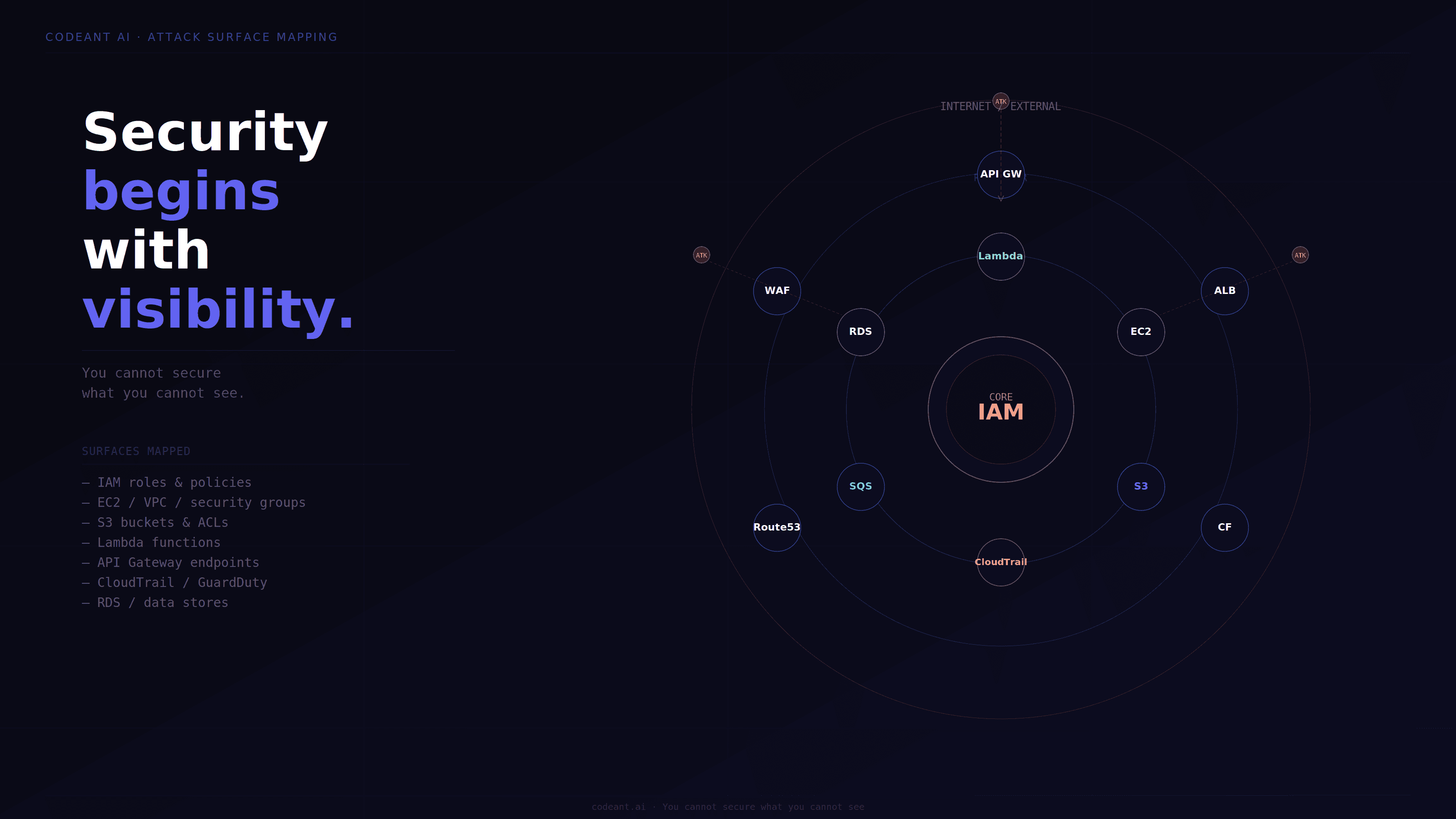
Phase 1: Reconnaissance And Attack Surface Mapping
Security begins with visibility. You cannot secure assets you do not know exist.
What AI-Driven Reconnaissance Covers
External attack surface mapping includes:
Subdomain enumeration
Certificate transparency log analysis
Cloud asset discovery
Port and service fingerprinting
DNS misconfiguration discovery
Public storage exposure testing
JavaScript endpoint extraction
Common discoveries:
Forgotten staging environments
Undocumented APIs
Public admin interfaces
Misconfigured cloud resources
Shadow infrastructure
This phase routinely finds exposure internal teams are not tracking.
→ Related: See our guide on PTaaS for how continuous models expand this further.
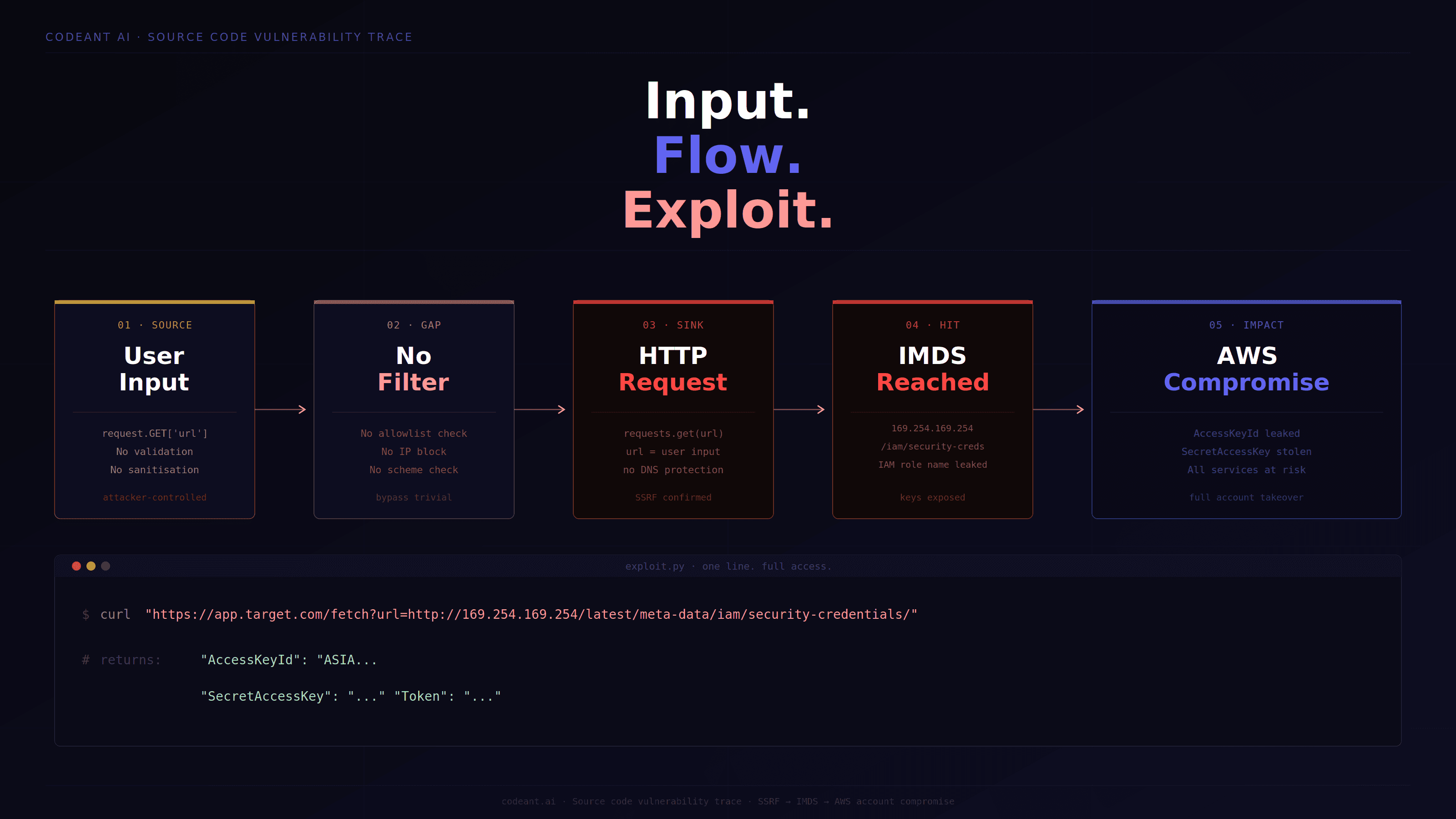
Phase 2: Source Code Intelligence For Deeper Security Testing
This is where AI penetration testing starts separating itself. This is not legacy SAST. This is code intelligence.
What Gets Analyzed
Coverage often includes:
Taint and dataflow analysis
Authentication path tracing
Authorization boundary analysis
Insecure API patterns
Hardcoded secrets detection
Dependency and software composition analysis
IaC review across Terraform, Kubernetes, and CI pipelines
What This Finds That Scanners Often Miss
Examples:
Middleware auth bypasses
Cross-function authorization gaps
Dangerous logic sequencing flaws
Hidden privilege escalation conditions
These are frequently breach-class issues. Not scanner noise.
Phase 3: JavaScript And Application Intelligence
Modern applications leak intelligence through the browser. Most teams underestimate how much. JavaScript bundle analysis can surface:
Internal APIs
Hardcoded credentials
Cloud endpoints
Feature flags
Hidden admin routes
Source maps exposing application logic
This often becomes the bridge between code analysis and offensive testing. It is also where many attack paths begin.
Phase 4: Targeted Exploit Construction And Automated Penetration Testing
This is not generic payload spraying. This is evidence-driven testing. Tests are built from what previous phases discovered.
Targeted Exploit Validation May Include
SQL injection validation
JWT manipulation testing
IDOR testing
Business logic abuse
SSRF exploitation
Authentication bypass attempts
WAF-aware payload evasion
Each test exists for a reason. Not because a scanner guessed. Because evidence suggested it.
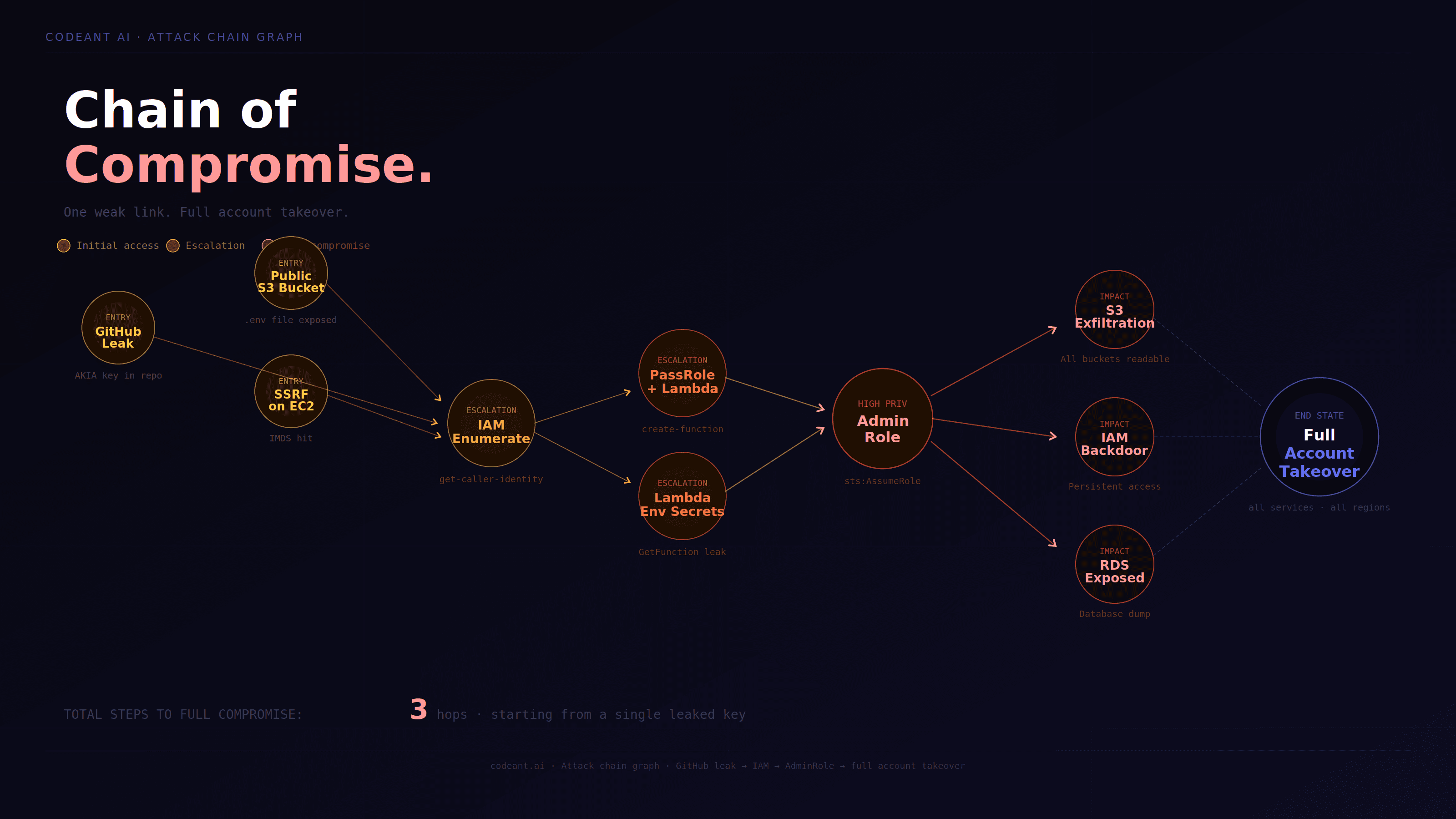
Phase 5: Attack Chain Analysis And Real-World Breach Simulation
This is one of the biggest gaps in conventional testing. Findings rarely exist alone. They interact.
Example Attack Chain
Individually:
Broken object authorization
Predictable identifiers
Missing tenant scoping
Together:
Cross-tenant breach. Critical.
What Mature Attack Chain Analysis Should Do
It should:
Correlate confirmed findings
Model exploit paths
Combine chained severity
Produce proof-of-impact
This changes remediation priorities dramatically.
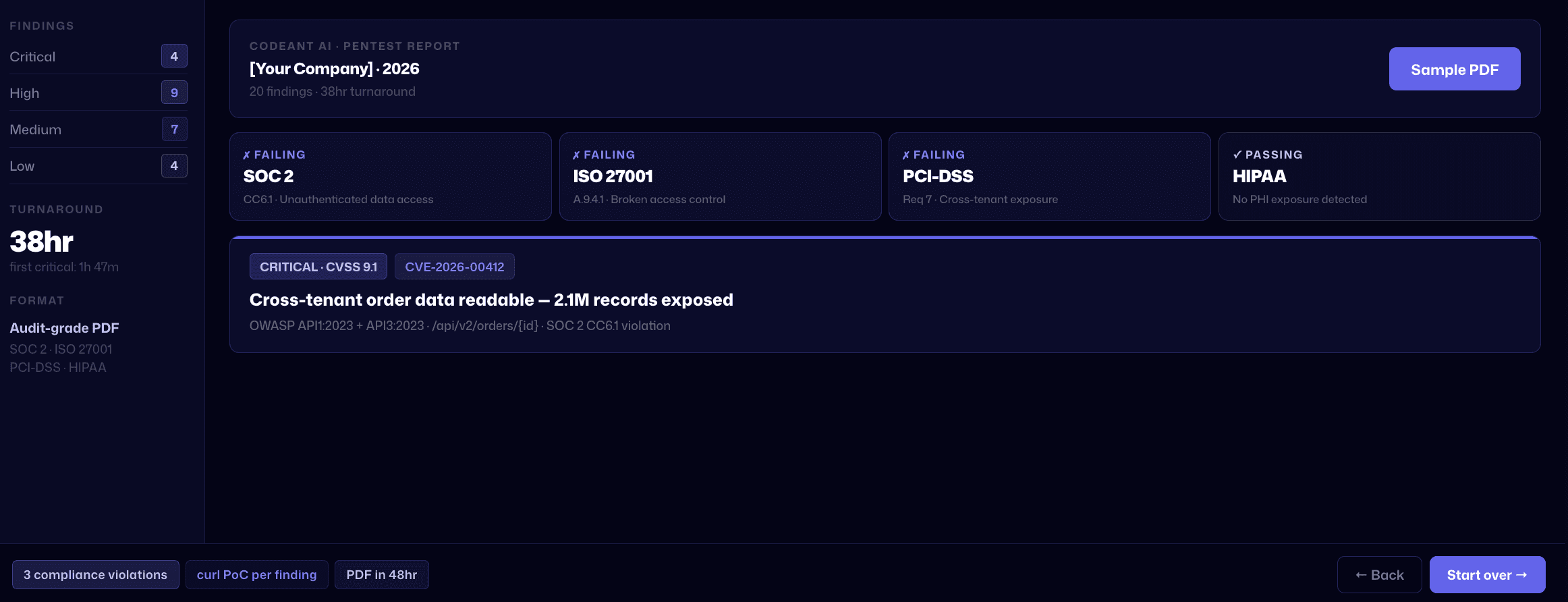
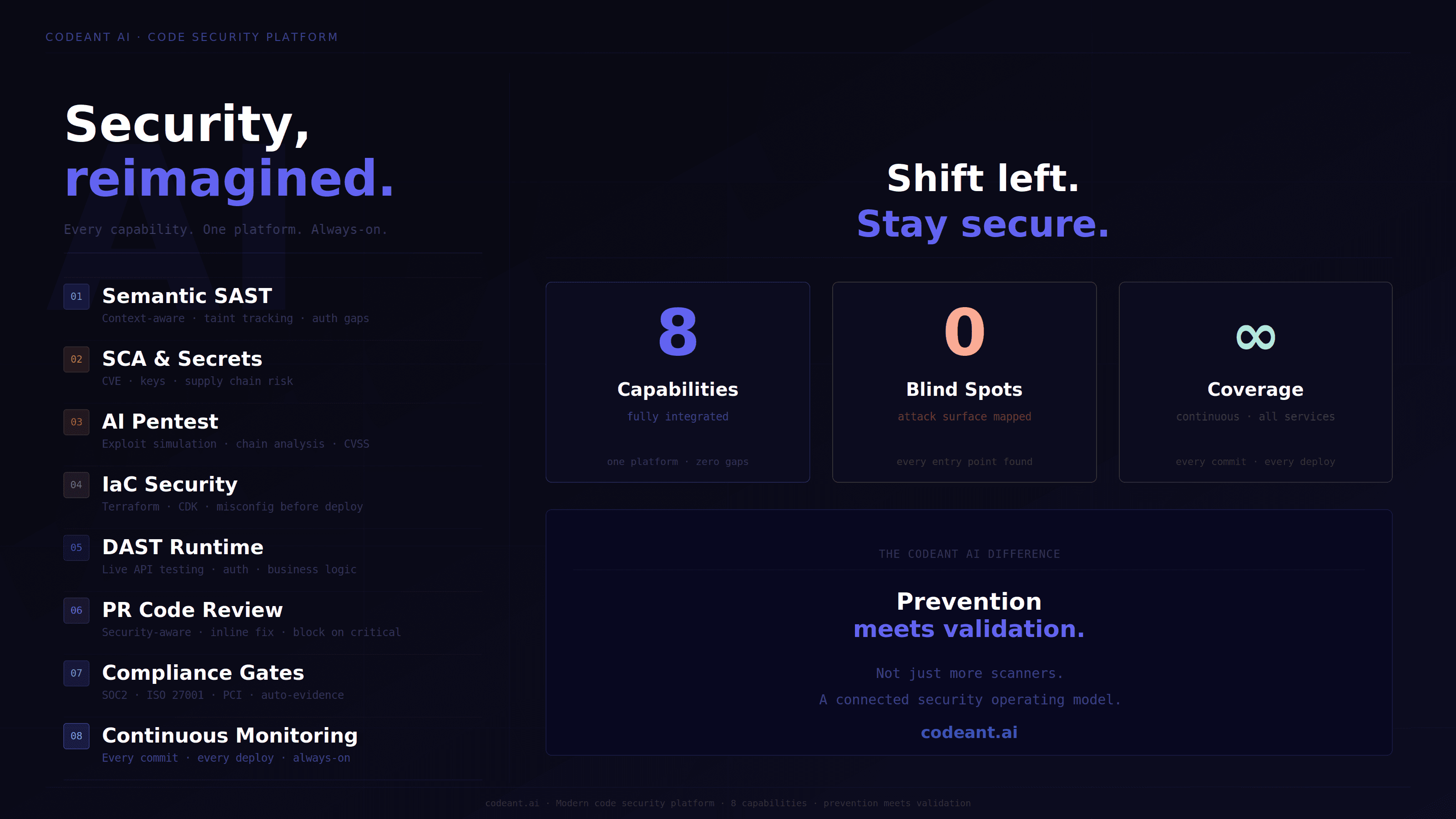
Key Features To Look For In A Code Security Platform
Teams evaluating the best code security platform for enterprises should look beyond scanners. Look for systems that combine prevention and validation.
Core Features That Matter
A modern code security platform should include:
SAST and code intelligence
AI penetration testing capabilities
Automated penetration testing workflows
Attack chain construction
Continuous exploit validation
Unlimited retesting
Unified defensive and offensive security coverage
If one side is missing, visibility is incomplete.
How To Evaluate A Code Security Platform
Before choosing a platform, ask:
Does it confirm exploitation or only flag possibilities?
Does it combine SAST and offensive validation?
Does it prioritize attack chains rather than isolated findings?
Does it support CI/CD integration and continuous feedback?
Does it provide compliance evidence, not just findings?
This checklist alone filters most vendors.
Why Enterprises Are Moving Toward Unified Offensive And Defensive Security Platforms
Most tools force tradeoffs.
Defensive or offensive.
Detection or validation.
Enterprises increasingly want both.
Defensive Security Answers
What vulnerabilities exist in code?
Offensive Security Answers
How could those weaknesses actually be exploited?
Unified Security Answers Both
That is the shift. And it matters. Because prevention without validation creates false confidence. Validation without code context creates blind spots. Real security increasingly requires both.
How CodeAnt AI Combines SAST And AI Penetration Testing
CodeAnt AI combines SAST-driven defensive security and offensive penetration testing in a single system.
On the defensive side, it integrates across:
IDEs
CLI workflows
CI/CD pipelines
It analyzes:
Insecure data flows
Authentication risks
Misconfigurations
Code vulnerabilities as they are introduced
On the offensive side, it conducts:
Attack chain validation
The advantage is shared intelligence. The platform testing exploit paths already understands weaknesses discovered in code. That changes depth.
Why That Matters
This means:
SSRF findings become validated cloud attack paths
Authorization flaws become modeled breach scenarios
Findings become exploit evidence, not hypotheses
That is a fundamentally different model.
AI Penetration Testing Vs Traditional Security Tools
Most security tooling sits in one category:
Scanner tools
Point SAST tools
Conventional pentest vendors
Unified platforms aim to bridge those silos.
Comparison Snapshot
Capability | Traditional Tools | Unified Platform |
|---|---|---|
Code Intelligence | Partial | Deep |
Exploit Validation | Limited | Yes |
Attack Chains | Rare | Core capability |
Continuous Retesting | Often separate | Integrated |
Defensive + Offensive Coverage | Split | Unified |
This is often where enterprise evaluations shift.
Best Security Platform For Enterprises: What Actually Matters
The best security platform for enterprises is rarely the one with the longest feature list. It is the one that reduces real exploit risk.
Prioritize platforms that:
Improve codebase security continuously
Validate exploitability
Connect findings into attack paths
Support compliance evidence needs
Unify prevention and testing
That is increasingly where enterprise buying decisions are moving.
Conclusion: Improve Codebase Security With Unified AI Penetration Testing
Modern software changes too quickly for disconnected security tools.
The strongest security programs now combine:
Source code intelligence
Exploit chain analysis
Unified defensive and offensive testing
That is where AI penetration testing is changing the model. It is not just about detecting more vulnerabilities. But about identifying what actually matters.
CodeAnt AI pushes this further by connecting SAST, exploit validation, and continuous testing in a single system.
If your current tooling can generate findings but cannot model real attack paths, it may be time to evaluate a platform built to do both.
Meanwhile, give our automated penetration testing a try for FREE!!
FAQs
What Is AI Penetration Testing?
How Does Automated Penetration Testing Improve Codebase Security?
How Can I Improve My Codebase Security Beyond Traditional SAST?
What Are Key Features Of A Modern Code Security Platform?
What Is The Best Code Security Platform For Enterprises?















