A penetration test without a signed authorization letter is not a penetration test. It is unauthorized computer access. That distinction carries federal criminal charges in the US, prosecution under the Computer Misuse Act in the UK, and equivalent statutes in every other jurisdiction where testing is conducted.
This page gives you a complete, copy-ready authorization letter template, structured across 13 sections covering every element that protects your organization, your testing firm, and the engagement itself. Adapt it in under 20 minutes.
Why this document matters: In 2019, two Coalfire penetration testers were arrested during a physical security engagement in Iowa. They had authorization, but the letter didn't specify who had authority to authorize access to that particular facility. They spent hours in custody. A better-drafted letter would have resolved the situation in minutes.
Find full context in our Pentest Authorization Letter Complete Guide.
What the Template Covers
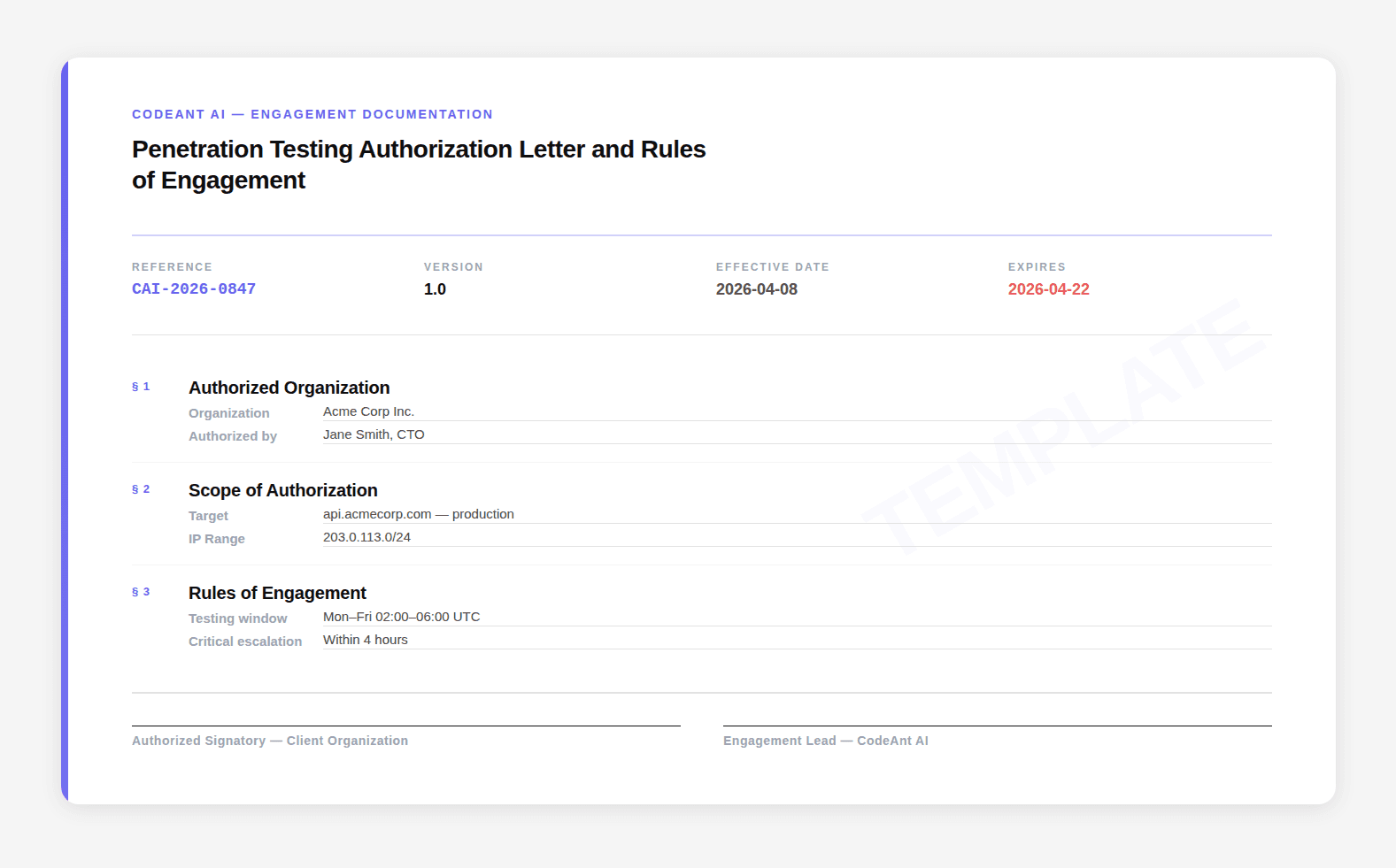
This template is organized into 13 sections. Each section addresses a specific legal, operational, or procedural requirement. You can use the full template or pull individual sections as needed.
Section | What It Covers | Required? |
|---|---|---|
1 | Parties, names, titles, contact info | Always |
2 | Engagement purpose and explicit authorization | Always |
3 | In-scope systems | Always |
4 | Out-of-scope exclusions | Always |
5 | Cloud provider authorization | If cloud-hosted |
6 | Permitted techniques matrix | Always |
7 | Testing window and timing | Always |
8 | Emergency procedures | Always |
9 | Data handling and GDPR provisions | Always |
10 | Deliverables | Always |
11 | Indemnification and liability | Always |
12 | Governing law | Always |
13 | Signatures | Always |
Find the complete template letter here:
What To Fill In Before Signing
Section 3: Scope is the most critical section to complete carefully. Vague scope is the single most common source of engagement disputes. Every system you want tested needs an explicit identifier. Everything you don't want tested needs to be in Section
Section 5: Cloud Provider Authorization needs to be completed before testing starts, not after. Azure requires PTROE form submission 1-2 business days in advance. If you skip this, you risk account suspension.
Section 8: Emergency Contacts must be real phone numbers for people who will actually answer at any hour during the testing window. Test the numbers before testing begins.
Section 13: Signatures must come from someone with actual authority. An IT manager's signature does not legally authorize penetration testing. It must be a C-suite officer or someone with written delegation from C-suite.
Don’t Start a Pentest Without This
A penetration test is not just a technical exercise, it is a legally sensitive operation that sits at the boundary of authorized security testing and criminal activity. The difference is not the tools used or the vulnerabilities found. The difference is the clarity of authorization.
This template is designed to remove that ambiguity. It translates legal intent into operational clarity, defining exactly what can be tested, how it can be tested, and what happens when something goes wrong. That is what protects both the organization and the testing team.
If you take one thing from this guide, make it this: scope and authorization are not paperwork, they are the foundation of a safe, effective penetration test.
Before you start your next engagement, take 20 minutes, fill this out properly, and get it signed by the right authority. Because the cost of skipping this step is not a failed test. It is legal exposure you cannot afford.
FAQs
Is a penetration test authorization letter legally required?
Who should sign a penetration testing authorization letter?
What happens if the scope is not clearly defined?
Do cloud providers require approval before penetration testing?
Can this template be reused for multiple engagements?