In 2018, a penetration testing firm was hired by a regional bank to conduct a physical and network security assessment. The engagement was legitimate. The scope was approved.
On day two, the testers were detained by law enforcement after being reported as suspicious actors attempting to access a restricted area. What resolved the situation wasn’t intent. It was documentation. A signed authorization letter that clearly listed:
the individuals conducting the test
the facilities and systems in scope
the approved testing activities
the executive who authorized the engagement
Within an hour, the testers were released. Without that letter, they would have faced the same legal consequences as attackers. This is not an edge case. Every penetration test, whether it involves:
applications
networks
physical access
or social engineering
operates in a legal gray area. That gray area is resolved by one thing: explicit, written authorization.
Laws like the Computer Fraud and Abuse Act (US), the Computer Misuse Act (UK), and similar regulations globally all depend on a single condition: Was the access authorized? The authorization letter is what proves that it was. Beyond legal protection, this document defines how the engagement actually runs.
It answers critical operational questions:
What systems can be tested
Which techniques are permitted
Who must be notified if something breaks
What happens if a real breach is discovered
These are not administrative details. They determine whether your pentest produces actionable security findings, or turns into an incident. This guide covers everything required to create a proper authorization letter:
legal requirements
scope definition
cloud provider rules
third-party considerations
emergency procedures
and complete template language
By the end, you’ll know exactly how to create an authorization letter that protects your organization, your testers, and the engagement itself.
Related:
What is AI Penetration Testing? The Complete Deep-Dive Guide
What Is a CVSS Score? How Security Teams Use it to Prioritize
The Legal Foundation: Why Authorization Letters Exist
The Computer Fraud and Abuse Act (18 U.S.C. § 1030) is the primary US federal statute governing unauthorized computer access. Section (a)(2) prohibits accessing a computer without authorization or exceeding authorized access to obtain information. Section (a)(5) prohibits knowingly causing damage to a protected computer. Both provisions apply to penetration testers who act without explicit written authorization.
The key legal principle: good intent is not a defense under CFAA. A penetration tester who genuinely believes they are authorized, based on a verbal agreement or email exchange, but lacks formal written authorization, faces the same criminal exposure as a malicious attacker. Multiple court cases have turned on exactly this point, the absence of documented authorization transformed what the defendant believed was a legitimate security engagement into a criminal act.
Action | Without Authorization | With Proper Authorization |
|---|---|---|
Port scanning target systems | Potential CFAA §1030(a)(2) violation | Explicitly permitted |
Attempting login with test credentials | Potential CFAA §1030(a)(2) violation | Within defined scope |
Exploiting a vulnerability | CFAA §1030(a)(5)+ exposure | Within defined scope |
Accessing data via exploit | CFAA §1030(a)(2) felony risk | Within defined scope |
Intercepting network traffic | Wiretap Act (18 U.S.C. §2511) | Explicitly permitted |
Social engineering employees | May trigger state fraud laws | Explicitly permitted |
Physical security testing | Trespass / breaking & entering laws | Explicitly permitted |
Jurisdiction Considerations
Penetration testing engagements rarely operate in a single legal jurisdiction. Penetration testing laws vary by geography. The same activity may be legal in one jurisdiction and illegal in another unless properly authorized.
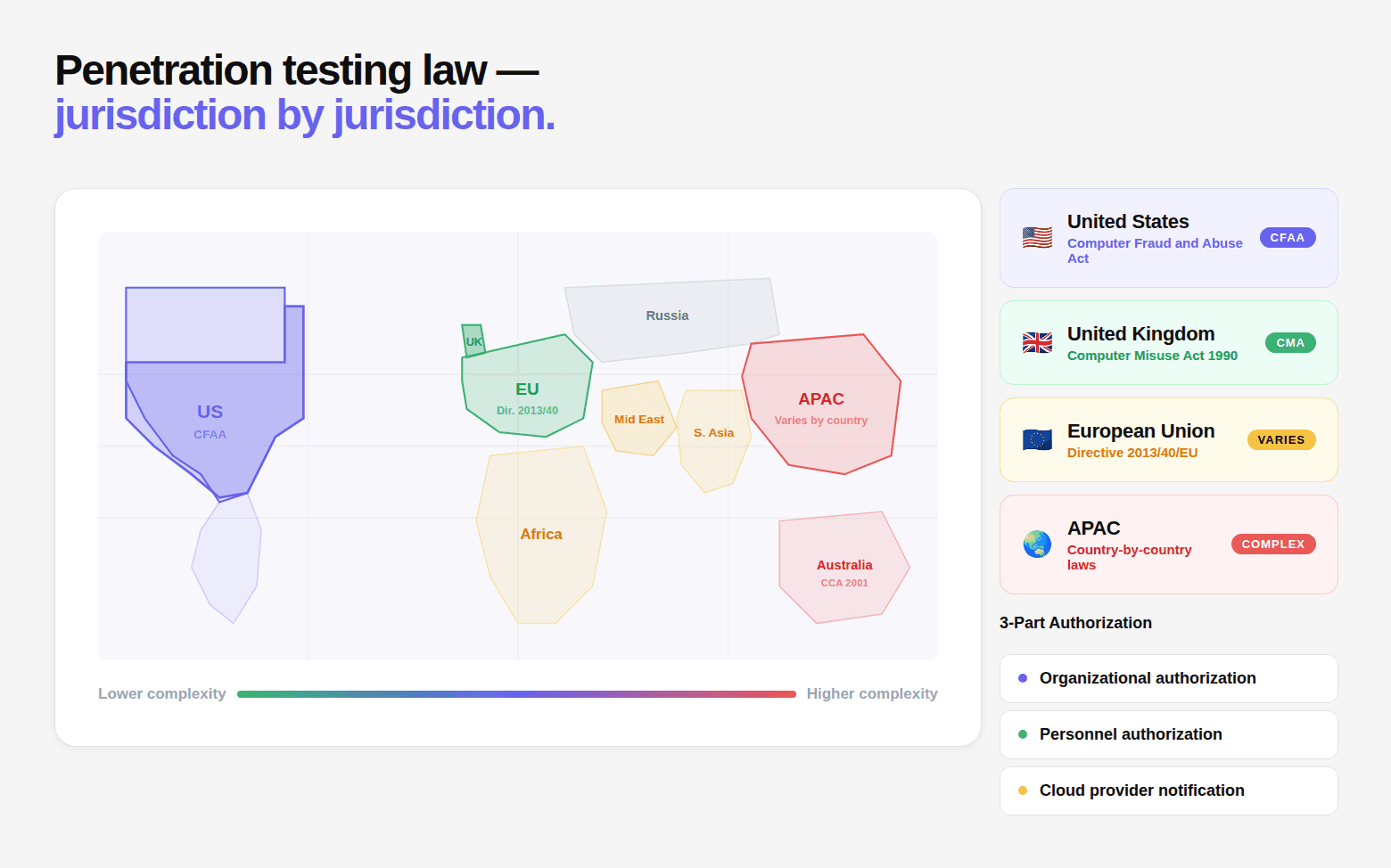
Legal Framework by Region:
Region | Primary Law | Key Legal Risk | Authorization Requirement |
|---|---|---|---|
United States | CFAA + state laws | Broad scope under CFAA §1030(a)(1)–(7) | Federal law covers all states if properly authorized |
United Kingdom | Computer Misuse Act 1990 | Unauthorized access (Section 1), modification (Section 3) | Must be authorized by system owner / data controller |
European Union | Member state laws + GDPR | Data handling risks under GDPR Article 32 | Must include data handling + minimization provisions |
What Changes in Each Region
🇺🇸 United States
CFAA applies broadly to unauthorized access and system interaction
Even benign testing can trigger violations without authorization
Federal coverage simplifies multi-state engagements
🇬🇧 United Kingdom
Computer Misuse Act focuses on:
unauthorized access
unauthorized modification
Authorization must come from:
system owner
or legally responsible entity (data controller)
🇪🇺 European Union
Legal requirements vary by country
GDPR introduces additional obligations:
minimize data collection
avoid storing personal data discovered during testing
Authorization should explicitly define:
data handling
retention policies
Multi-Jurisdiction Environments
If your systems or teams span regions, complexity increases significantly.
You must:
obtain jurisdiction-specific authorization (often via local counsel)
define which law governs the engagement (choice of law clause)
document where systems are physically hosted
evaluate cross-border testing risks
Example:
EU-based tester → testing US-hosted system
US-based tester → accessing EU data
These scenarios may introduce conflicting legal obligations.
Cloud-Hosted Systems (Critical Detail)
Cloud infrastructure adds another layer of legal ambiguity. Authorization must clearly specify:
where systems are physically hosted
which jurisdiction applies
Examples:
Cloud Region | Legal Consideration |
|---|---|
AWS | Primarily US law (CFAA applies) |
GCP | EU laws + GDPR obligations |
Multi-region deployments | Requires explicit legal clarification |
Authorization is not just about permission.
It must align with:
where systems are hosted
where testers operate from
which laws apply to both
Without this clarity, a valid pentest in one jurisdiction can become a legal violation in another.
The Parties: Who Must Sign and Why
A penetration test authorization letter is only valid if the right parties are involved. It’s not just about permission, it’s about who has the legal authority to grant it. A complete authorization involves three distinct parties.
1. The Authorizing Organization
This is the entity that owns or controls the systems being tested. Important nuance: This is not always the organization paying for the test. If systems are operated by:
subsidiaries
vendors
cloud providers
then each system owner must authorize testing.
Authority Requirements
Requirement | Details |
|---|---|
Minimum authority | C-suite executive or written delegation |
Recommended | CISO + CTO co-signature |
Additional Signatures by System Type
System Type | Additional Signatory | Why |
|---|---|---|
Customer data systems | Legal counsel | Data liability |
Payment systems | CFO or legal | Financial risk |
Health data systems | Privacy officer | HIPAA compliance |
Government systems | Contracting officer | Contractual obligation |
What the Signature Represents
A valid signature confirms:
authorization for testing activities
authority over listed systems
acceptance of risk and indemnification
agreement to defined scope
What is NOT Valid Authorization
IT manager approval alone
verbal approval
email without formal letter
implied approval via purchase order
If the signer does not have authority, the authorization does not hold.
2. The Penetration Testing Firm
The authorization must clearly define who is allowed to test. Not just the company, the individuals.
Required Information
Requirement | Details |
|---|---|
Legal entity name | Full company name |
Authorized individuals | All testers explicitly listed |
Engagement lead | Primary contact |
Insurance | Proof of E&O coverage |
Data handling | NDA / confidentiality terms |
Why Individual Naming Matters
law enforcement verification
scope accountability
cloud provider compliance
subcontractor control
Example Format
“The following individuals are authorized to conduct testing:
[Full Name], [Role] — [Employer]
[Full Name], [Role] — [Employer]
Additional individuals require written approval before testing.”
Third-Party System Operators (Most Missed)
You cannot authorize testing on systems you don’t control. Modern infrastructure includes:
cloud providers
SaaS platforms
hosting providers
CDNs
Each may require separate authorization or notification.
Cloud Providers
Provider | Requirement |
|---|---|
AWS | No pre-approval (most cases), but restrictions apply |
GCP | No pre-approval, notify if impact risk |
Azure | Rules of engagement + possible notification |
SaaS Platforms
If testing involves SaaS (e.g., Salesforce, Workday):
→ Vendor authorization is required
Hosting & Colocation
data centers may require notification
physical testing requires explicit approval
CDN Providers
Testing through CDNs can trigger protection systems.
Cloudflare, Fastly, Akamai may require notification
ISPs
Testing should stop at your infrastructure boundary. Beyond that → separate authorization required.
That said, authorization must align with:
system ownership
legal authority
third-party involvement
Miss any of these, and the authorization breaks.
Even with the right parties involved, authorization is incomplete without clear scope definition. And this is where most engagements fail.
The Technical Scope Definition: The Most Consequential Section
Scope ambiguity is the single most common source of disputes between penetration testing firms and their clients. "Test our web application" seems unambiguous until the tester begins testing APIs that serve the mobile application, which the client considers "out of scope." "Test our production environment" seems clear until the tester discovers that production shares a database with the HR system, which the client absolutely did not want tested.
Every ambiguity in scope definition will be resolved at the moment of maximum inconvenience — when a tester has found a vulnerability in a system that may or may not be in scope, or when a client is trying to explain to their board why the penetration testing firm accessed a system they thought was excluded.
Explicit scope definition requires three components:
In-scope enumeration: Everything that IS authorized for testing
Out-of-scope exclusion: Everything that is explicitly NOT authorized, even if adjacent to in-scope systems
Permitted techniques: What testing methods are authorized (and which require special approval)
In-Scope System Enumeration
For each system in scope, specify:
System identifier (IP, hostname, URL, ARN, etc.)
System type (web application, API, infrastructure, database, mobile, etc.)
Ownership confirmation (you own/control this system)
Environment (production, staging, QA, each must be listed if included)
Third-party notification status (cloud provider notified? Y/N)
Special handling (any systems with extra care requirements)
Example in-scope specification:
Out-of-Scope Exclusions
The following systems are explicitly EXCLUDED from testing and must NOT be accessed, probed, or tested in any way, even if discovered during testing:
SYSTEMS EXCLUSIONS:
Third-party production systems:
Stripe API (api.stripe.com): Stripe is not a party to this agreement
Salesforce (company.salesforce.com): third-party SaaS not authorized
Workday HR system (company.myworkday.com): HR data excluded
Any system whose IP or hostname is not in the in-scope list
Shared infrastructure:
52.14.88.155: third-party monitoring vendor agent
52.14.88.200: customer-managed server (not owned by Organization)
Specific data categories:
Live customer PII: access is limited to test accounts only
Financial transaction records: use test account transactions only
Employee personal data: HR systems are excluded
Network infrastructure beyond the specified scope:
ISP infrastructure upstream of the Organization's border router
BGP routing infrastructure
DNS resolvers not operated by the Organization
TECHNIQUE EXCLUSIONS (require separate written approval):
Denial of Service (DoS) attacks of any kind
Social engineering of employees (email phishing, vishing)
Physical penetration testing (badge cloning, tailgating)
Wireless network attacks
Testing that would require modification of production data
Testing that involves downloading more than [DEFINED AMOUNT] of customer records
TIMING EXCLUSIONS:
No testing between 18:00 UTC Friday and 06:00 UTC Monday (maintenance windows)
No testing during the following business-critical periods:
[List any planned high-traffic events, product launches, fiscal year-end]
WHAT HAPPENS IF TESTER DISCOVERS OUT-OF-SCOPE SYSTEM:
If the tester accidentally accesses or discovers an out-of-scope system:
Immediately cease interaction with the system
Notify the Engagement Contact within 4 hours
Document what was accessed and how
The tester shall not probe, exploit, or analyze the out-of-scope system further
The incident will be documented in the final report
Permitted Testing Techniques Matrix
The table below defines which techniques are allowed, restricted, or prohibited during the engagement.
Category | Technique | Status | Notes |
|---|---|---|---|
Reconnaissance | Passive OSINT | Permitted | No target interaction |
Active port scanning | Permitted | Normal intensity only | |
Service enumeration | Permitted | ||
Directory / path enumeration | Permitted | ||
Subdomain enumeration | Permitted | ||
Authentication | Login brute force | Limited | Max 10 attempts per account |
Password spraying | Limited | Max 3 passwords per account | |
Credential stuffing | Notify first | Contact engagement lead | |
MFA bypass testing | Permitted | ||
Session token analysis | Permitted | ||
Exploitation | Exploitation of findings | Permitted | In-scope systems only |
Privilege escalation | Permitted | Document all steps | |
Lateral movement | Notify first | Pre-approval required | |
Data exfiltration (simulated) | Limited | Test data only | |
Denial of Service | Any DoS technique | Prohibited | Requires separate agreement |
Rate limit testing | Limited | Low intensity only | |
Resource exhaustion | Prohibited | ||
Social Engineering | Employee phishing | Out of scope | Not included |
Phone / vishing | Out of scope | Not included | |
Injection | SQL injection testing | Permitted | Use test data |
Command injection | Permitted | Limited to proof-of-concept | |
Code injection | Permitted | No persistent modification | |
Persistence | Backdoor installation | Prohibited | Even temporary |
User account creation | Prohibited | Use provided test accounts | |
Config file modification | Prohibited | ||
Data modification | Prohibited | Read-only exploitation only |
Key Interpretation
Permitted → No additional approval required
Limited → Allowed with strict constraints
Notify first → Requires explicit approval before execution
Prohibited / Out of scope → Not allowed under any circumstance
Cloud Provider Authorization Requirements
AWS Penetration Testing Policy (Current as of 2026)
Amazon Web Services maintains a penetration testing policy that all customers must comply with. The key points:
AWS Penetration Testing Requirements:
WHAT DOES NOT REQUIRE PRIOR APPROVAL:
EC2 instances and RDS instances you own
API Gateway endpoints
Lambda functions
ECS/EKS workloads
Elastic Beanstalk environments
CloudFront distributions
Aurora databases
S3 buckets (your own)
AWS WAF testing
WHAT IS ALWAYS PROHIBITED (regardless of authorization):
DNS zone walking (Route53)
Denial of service attacks against any AWS infrastructure
Port flooding
Protocol flooding
Request flooding (unless pre-approved)
Simulated DDoS attacks
WHAT REQUIRES PRIOR APPROVAL (submit via AWS form):
Simulated DDoS testing
Load testing that might affect AWS infrastructure
Testing AWS-managed services in ways that affect other customers
AUTHORIZATION LETTER LANGUAGE FOR AWS:
"Testing is authorized against AWS Account [ID] owned and operated by [Organization Name]. Testing complies with the AWS Penetration Testing
Customer Service Policy in effect at the time of testing. Prohibited activities under the AWS policy are excluded from this engagement."
GCP Penetration Testing Policy
CURRENT POLICY POSITION:
Google does not require prior approval for penetration testing of GCP resources
you own. However:
REQUIREMENTS:
Testing must be limited to your own GCP resources
Testing that could affect other GCP customers is prohibited
Notify Google if you discover vulnerabilities in GCP itself (via Google's Vulnerability Reward Program)
Do not test Google's underlying infrastructure
PROHIBITED:
Testing that impacts shared GCP infrastructure
DoS/DDoS testing of any Google services
Testing systems you don't own that happen to be on GCP
AUTHORIZATION LETTER LANGUAGE FOR GCP:
"Testing is authorized against GCP Project(s) [Project-ID(s)] under billing account [Account-ID] owned by [Organization Name]. Testing complies with Google Cloud's Acceptable Use Policy and is limited to resources owned by [Organization Name]."
Microsoft Azure Penetration Testing Policy
CURRENT REQUIREMENT:
Microsoft requires customers to notify before conducting penetration tests against Azure resources using the Penetration Testing Rules of Engagement (PTROE) form.
TIMELINE:
Submit notification form at least 1-2 business days before testing begins
Keep testing within the approved timeline
Notify Microsoft if testing extends beyond approved window
WHAT REQUIRES NOTIFICATION:
Any penetration testing against Azure-hosted resources
Load testing that might impact Azure infrastructure
Security assessment of Azure Marketplace solutions you use
WHAT IS PROHIBITED:
Testing Azure infrastructure itself (only your resources)
DoS or DDoS testing
Testing affecting other Azure customers
Testing Azure management portals (portal.azure.com etc.)
AUTHORIZATION LETTER LANGUAGE FOR AZURE:"
Testing is authorized against Azure Subscription(s) [Subscription-ID(s)] owned by [Organization Name]. Microsoft has been notified via the Penetration Testing Rules of Engagement form (Notification Reference: [REF-NUMBER], submitted [DATE]). Testing complies with Microsoft's Penetration Testing Rules of Engagement and is limited to resources owned by [Organization Name]."
The Multi-Cloud Authorization Complexity Matrix
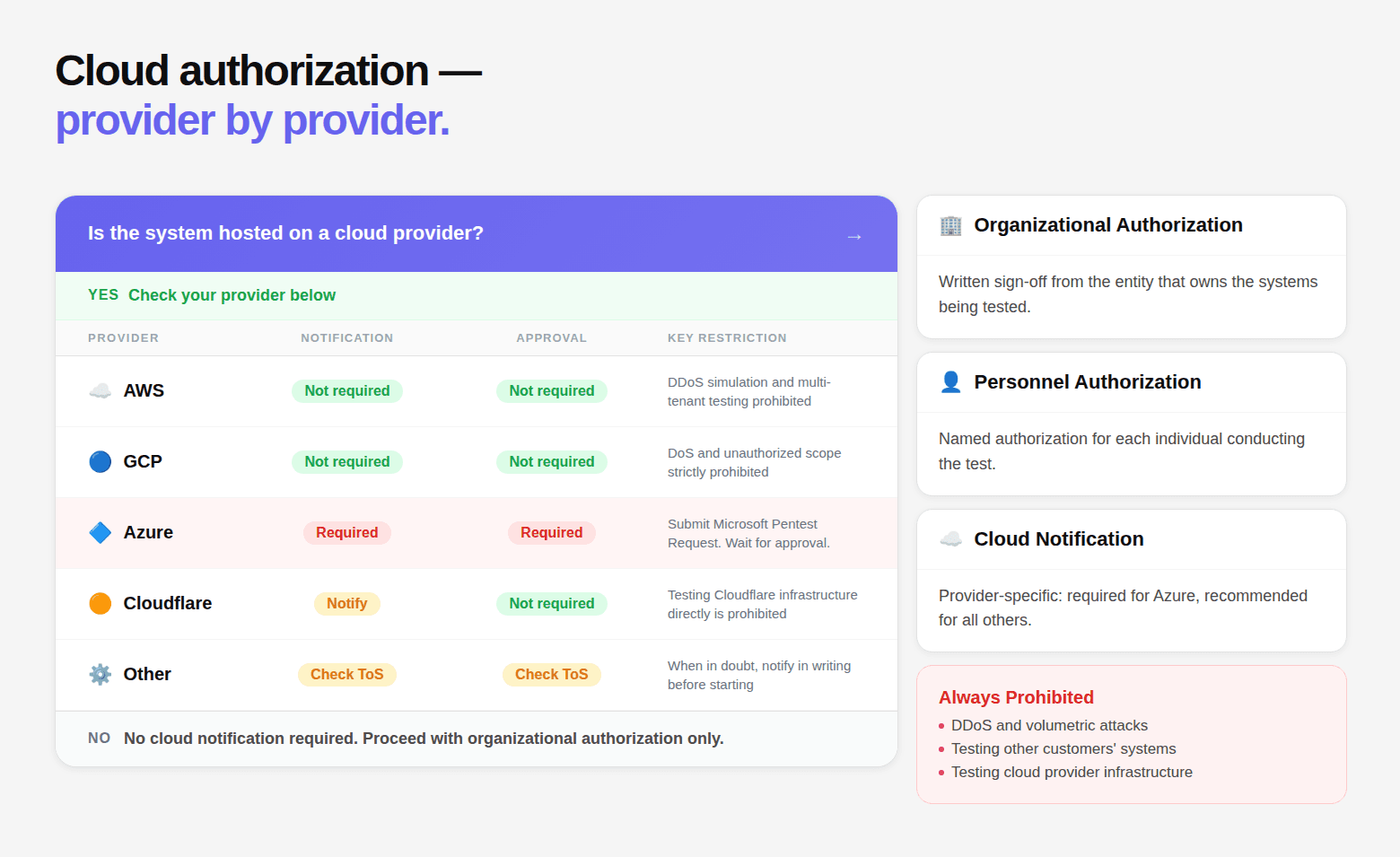
Cloud Provider | Prior Approval Required | Notification Required | Prohibited Activities | Current Policy URL |
|---|---|---|---|---|
AWS | No (for most services) | Recommended | DoS, DNS zone walking, Request flooding | aws.amazon.com/security/penetration-testing |
GCP | No | Recommended | DoS, cross-customer impact | cloud.google.com/terms/aup |
Azure | Via PTROE form | Yes — mandatory | DoS, Azure infrastructure, cross-customer | portal.msrc.microsoft.com |
Cloudflare | Contact required | Yes | DDoS simulation, upstream infrastructure | cloudflare.com/responsible-disclosure |
Fastly | Contact required | Yes | DDoS, testing Fastly edge infrastructure | N/A contact Fastly directly |
Heroku | No (for your apps) | Recommended | Platform infrastructure, other customer apps | devcenter.heroku.com |
DigitalOcean | No | Notify if extensive | DoS, cross-customer | digitalocean.com |
GitHub | For GitHub.com itself | N/A for repos | GitHub infrastructure | docs.github.com |
The Emergency Procedures Section: The Most Neglected Provision
Penetration testing involves real exploitation against real systems. Things go wrong:
1. Unintended Service Disruption
What happens: A vulnerability exploit causes unexpected system behavior, service crash, database outage, or resource exhaustion.
Without a procedure:
Unclear who to contact
Tester may continue unknowingly
Client may panic and halt testing
With a procedure:
Defined escalation path
Tester stops the triggering activity immediately
Engagement contact initiates response if required
2. Discovery of an Active Breach
What happens: Tester identifies signs of a real attacker, malware, unauthorized access, or ongoing data exfiltration.
Without a procedure:
Tester unsure whether to stop or continue
Client remains unaware of active compromise
With a procedure:
Immediate escalation
Testing halted in affected systems
Incident response and forensic preservation begin
3. Access to Out-of-Scope Sensitive Data
What happens: A vulnerability exposes data that should not be accessed, PII, financial records, or internal systems.
Without a procedure:
Tester risks violating scope
Client unaware sensitive data was exposed
With a procedure:
Immediate disengagement
Access path documented without further interaction
Client notified promptly
4. False Positive Security Alert
What happens: Testing activity triggers SIEM alerts, causing internal incident response activation.
Without a procedure:
Confusion between real attack and testing
SOC escalation disrupts engagement
With a procedure:
Emergency contact confirms testing activity
Predefined identifiers (e.g., code words) prevent escalation
5. Physical Security Detention
What happens: Tester is stopped by security or law enforcement during physical testing.
Without a procedure:
Legal exposure
Escalation into a real incident
With a procedure:
Authorization letter presented immediately
24/7 contact validates engagement
6. Third-Party Impact
What happens: Testing affects shared infrastructure or external systems.
Without a procedure:
Responsibility unclear
Potential legal or contractual issues
With a procedure:
Immediate cessation
Stakeholders notified
Incident documented
Why This Matters
Scenario Type | Risk Without Procedure | Outcome With Procedure |
|---|---|---|
Service disruption | Outage, panic | Controlled response |
Active breach | Missed attack | Immediate containment |
Data exposure | Scope violation | Safe handling |
SIEM alert | False escalation | Controlled validation |
Physical detention | Legal risk | Immediate clearance |
Third-party impact | Liability | Managed response |
The Emergency Procedures Specification
This section defines what happens when something goes wrong during testing.
7.1 Emergency Contact Chain
All parties must be reachable throughout the testing window.
Client Emergency Contacts: (Must respond within defined SLA - e.g., 30/60/120 minutes)
Role | Name | Phone | Mobile | Availability | |
|---|---|---|---|---|---|
Primary | [Name] | [Number] | [Mobile] | [Email] | 24/7 |
Secondary | [Name] | [Number] | [Mobile] | [Email] | Backup |
Testing Firm Contacts:
Role | Name | Phone | Mobile | |
|---|---|---|---|---|
Engagement Lead | [Name] | [Number] | [Mobile] | [Email] |
Technical Lead | [Name] | [Number] | [Mobile] | — |
7.2 Safe Word Protocol
A safe word system is used to immediately validate the engagement.
Safe Word:
[UNIQUE WORD](e.g., BLUEKITE)Used in:
SOC communications
incident validation
law enforcement interactions
Who Knows the Safe Word
[List individuals]
Law Enforcement Script
“This activity is part of an authorized security assessment.
The safe word for this engagement is [SAFE WORD].
Please contact [Name] at [Phone] to confirm authorization.”
7.3 Service Disruption Procedure
If testing causes or may cause disruption:
Immediate Response
Stop the triggering activity immediately
Notify client within [15 minutes]
Client Decision: Client determines next step:
continue testing
temporarily pause
terminate engagement
Follow-Up
document cause + technique
log client decision
trigger incident response if needed
Liability Note
in-scope actions → governed by agreement
prohibited actions → tester responsibility
7.4 Discovery of Active Third-Party Compromise
If evidence of a real attacker is found:
Immediate Action
stop testing in affected area
notify client within 4 hours
Testing Team Responsibilities
do not modify systems
preserve evidence
document findings
maintain logs
provide written summary
Strictly Not Allowed
contacting law enforcement
notifying third parties
public disclosure
continuing testing without approval
Key Principle: The client owns incident response decisions.
7.5 Accidental Access to Out-of-Scope Data
If restricted systems or data are accessed:
Immediate Action: stop interaction immediately
Within 4 Hours: Notify Client and provide:
what was accessed
how it happened
what data was seen (description only)
confirmation of disengagement
Tester Obligations:
do not retain or reuse data
delete automatically captured data
confirm deletion in writing
include incident in final report
Client may:
allow alternate testing path
terminate test case
7.6 Physical Security Emergencies (If Applicable)
If tester is detained:
Present physical authorization letter
Provide emergency contact
Client confirms engagement
Notify engagement lead within 1 hour
Required Items for Testers:
physical authorization letter
business card
valid photo ID
That said, emergency procedures are not optional.
They define:
how quickly incidents are contained
how risk is controlled
whether testing remains safe and legal
Without them, a controlled test can become a real incident.
Data Handling Provisions: The GDPR Dimension
Penetration testing is inherently data-exposing. To confirm vulnerabilities, testers often interact with live systems that contain real customer data, credentials, financial records, and internal business information. This is not incidental. It is part of how modern vulnerabilities are validated.
Because of this, the authorization letter must clearly define how data is handled during testing. Without explicit controls, testing itself can introduce regulatory risk.
6.1 Data Encountered During Penetration Testing
During a standard engagement, testers may encounter multiple categories of sensitive data as a direct result of valid exploitation paths.
Data Type | Typical Source |
|---|---|
User credentials | Authentication flaws and weak access controls |
Session tokens | Traffic interception and session analysis |
Personal data (PII) | IDOR and injection vulnerabilities |
Financial data | Business logic and authorization flaws |
API keys and service credentials | JavaScript bundles or repository history |
Internal business data | Authorization bypass |
Encrypted data | Captured traffic that may be decryptable |
Log files with user activity | Path traversal or log access vulnerabilities |
The presence of this data is evidence of risk. It is not a resource to be collected or retained.
6.2 GDPR and Data Protection Considerations
If testing involves personal data of EU data subjects, it is considered a data processing activity under GDPR. In this context:
the client remains the data controller
the testing firm operates as a data processor
This introduces specific legal and operational obligations.
Data Processing Agreement (DPA)
A DPA is required when personal data is accessed during testing. It must define:
purpose of processing
duration of access
nature of processing activities
categories of data involved
security safeguards
Data Minimization
Testing must limit access to the minimum data required to confirm a vulnerability. For example, validating exposure with a single record is sufficient. Extracting full datasets is not.
Purpose Limitation
Data accessed during testing may only be used for vulnerability validation. It must not be used for:
internal research
training data
demonstrations
reuse across engagements
Retention Limitation
Client data must not be retained beyond necessity.
default expectation is no retention beyond the engagement
maximum retention window may be defined as [30 / 60 / 90 days]
written confirmation of deletion is required
Data Subject Rights
The client retains responsibility for all data subject rights. The testing firm must ensure that testing activities do not:
interfere with these rights
bypass existing controls
create additional exposure
6.3 Transition to Operational Controls
The principles above must be enforced through explicit, testable rules. The following section defines how data is classified, handled, retained, and protected during the engagement.
Data Handling and Confidentiality
This section translates data protection principles into operational controls that govern the engagement.
Data Classification During Testing
The testing firm shall handle all data encountered during testing according to the following classification model:
Data Category | Handling Requirement |
|---|---|
Test account data | May be accessed and analyzed fully |
Real user PII | Confirm existence only. Do not copy or reproduce |
Payment card data | Confirm existence only. No reproduction |
Discovered credentials | Document existence. Rotate upon notification |
API keys and secrets | Notify client within 24 hours. Do not retain |
Business confidential data | Access only what is necessary. Document usage in report |
System credentials | Document access path. Do not store credentials |
Source code | May be analyzed. Do not reproduce significant portions |
Data Retention and Deletion
The testing firm commits to the following data handling practices.
Testing Artifacts
Includes screenshots, logs, and tool output.
retention period: [90 days after report delivery]
storage: encrypted systems within testing firm infrastructure
access: limited to engagement team members
Final Reports and Supporting Documents
retention period: [3 years for compliance purposes]
storage: encrypted and access-controlled
Client Data Encountered During Testing
retention: none beyond engagement
data must be deleted immediately upon discovery
Exception:
proof-of-concept evidence required for reporting may be retained temporarily
such evidence must be deleted within [30 days of report delivery]
Post-Engagement Requirements
Upon completion of the engagement, the testing firm will:
delete all client data from testing systems
provide written certification of deletion within [14 days]
confirm deletion from backup systems within [30 days]
Reporting and Disclosure
All findings are disclosed exclusively to the client through secure channels.
Approved Communication Methods
encrypted email
secure client portal
encrypted file transfer
in-person delivery where required
The Testing Firm Will Not
The testing firm agrees not to:
publish or discuss findings publicly without written approval
include findings in case studies without explicit consent
disclose the client as a customer without approval
reuse findings without anonymization
share or transfer client data to third parties
Bug Bounty Programs
Findings from this engagement will not be submitted to bug bounty programs by the testing firm. The client retains full discretion to disclose findings independently.
Non-Disclosure Obligations
The testing firm agrees to maintain confidentiality of:
the existence of the engagement
all findings and vulnerabilities
all client data accessed
system architecture and configurations
business processes observed during testing
Duration
Confidentiality obligations remain in effect for: [2 years] from the engagement completion date
Exceptions
Disclosure is permitted only if required by law or court order. Where legally allowed, the client will be notified in advance.
That said, data handling in penetration testing is not a secondary concern. It is a control layer that determines whether testing remains compliant, secure, and legally defensible. A well-defined data handling section ensures that vulnerabilities are identified without introducing new risk.
Complete Authorization Letter Template
This is the complete template ready for adaptation. Every section from Parts 1–6 synthesized into a single coherent document:
Special Circumstances: When Standard Letters Aren't Enough
Red Team Engagements
Red team engagements involve a restricted knowledge model — only specific individuals know the test is occurring. This creates complications for the authorization letter:
Supply Chain and Third-Party Testing
When the organization wants to test systems operated by its vendors or supply chain partners:
Government and Regulated Industry Special Requirements
Common Authorization Letter Mistakes and How to Avoid Them
The Ten Most Common Mistakes
Mistake | Why It's Dangerous | The Correct Approach |
|---|---|---|
Verbal authorization only | Provides zero legal protection | Always get written authorization before any testing begins |
Signing authority too low | IT manager cannot legally authorize | Require C-suite or delegated authority confirmation |
No named individuals | Anyone at the firm could claim authorization | List every authorized tester by full legal name |
Vague scope ("our systems") | Any system claimed is "ours" | Enumerate specific IPs, hostnames, URLs, account IDs |
No out-of-scope list | Adjacent systems get tested | Explicitly exclude everything not in scope |
Cloud provider notification omitted | Violates cloud ToS, potential account suspension | Check and document provider requirements before testing |
No emergency procedures | Disruptions become crises | Define escalation path for every scenario |
No data handling provisions | GDPR/regulatory exposure | Explicit provisions for each data category encountered |
Open-ended testing window | Tester can return indefinitely | Hard start and end dates with extension procedure |
No copy carried by testers | Law enforcement encounters become crises | Every tester carries a physical copy |
The Document Nobody Reads Until They Need It Desperately
The penetration test authorization letter is the document that nobody reads carefully during normal operations and everyone reads desperately when something goes wrong — when law enforcement shows up, when a service goes down during testing, when a tester accidentally accesses a system that shouldn't have been in scope, when a client disputes what was authorized.
At that moment — when the authorization letter is needed most — there are exactly two outcomes: the document is clear, specific, and complete, and the situation resolves quickly in everyone's favor; or the document is vague, incomplete, or absent, and lawyers get involved.
The difference between those two outcomes is the quality of the work done before testing began. Specific scope definitions, named individuals, signed by actual authority, cloud providers notified, emergency procedures defined, data handling addressed. None of this is difficult. None of it is expensive. All of it is the kind of preparation that separates professional security testing engagements from the ones that generate cautionary stories.
CodeAnt AI provides engagement documentation — including a complete authorization letter package — as a standard part of every penetration testing engagement. The letter is reviewed by the client's legal team before signing, cloud provider notifications are handled as part of engagement setup, and emergency contacts are verified as reachable before the first test packet is sent.
The engagement doesn't start until the paperwork is right. That's not bureaucracy — it's the foundation that makes everything else in the engagement meaningful.
Book a 30-minute scoping call. Testing starts within 24 hours. Book your call here.
Continue reading:
FAQs
Can we use email confirmation as authorization instead of a formal letter?
How specific does the scope need to be? Can we just say "all of company.com"?
We use AWS, GCP, and Azure. Do we need separate authorization for each?
What if our testing firm doesn't want to sign the authorization letter?
We're doing a bug bounty program, not a traditional pentest. Do we still need this?