Physical penetration testing feels simple on the surface. You define a location. You define techniques. You send testers to simulate real-world intrusion.
But unlike application or network testing, physical testing operates in an environment where control is shared. Multiple parties may have authority over the same space. Security responsibilities are often fragmented. Enforcement can happen in real time.
This creates a different kind of risk. Not technical risk. Not even operational risk. Legal and situational risk.
The kind that shows up when a tester is stopped, questioned, or detained and the authorization you assumed was sufficient is challenged in real time.
The Iowa Arrest Case That Changed How Physical Testing Is Done
In 2019, two penetration testers from Coalfire were arrested while conducting a physical security assessment of a courthouse in Iowa. They had an authorization letter. It was signed by the appropriate executive. The scope covered the facility.
What went wrong: the letter was authorized by the State Court Administration, which commissioned the assessment. But the courthouse was physically secured by the local Sheriff's office. The Sheriff's office had not been notified, did not consider themselves parties to any authorization, and arrested the testers on burglary charges.
The charges were eventually dropped, but only after a prolonged legal battle that involved the Governor's office, multiple attorneys, and weeks of legal limbo for the two testers.
The lesson: physical penetration testing requires authorization from every party who has legal responsibility for the physical spaces being tested. Not just the party who hired you.
Why Physical Penetration Testing Requires a Different Authorization Model
In application testing, authorization is usually binary. You own the system or you do not.
In physical environments, ownership and control are distributed. A single location may involve:
The organization occupying the space
The building owner or property manager
A contracted security service
Local law enforcement with jurisdiction
Shared tenants or restricted zones
Each of these parties may have the ability to challenge or stop testing activity. This means authorization is not a single signature. It is a coordination model.
Who Must Be Accounted For Before Testing Begins
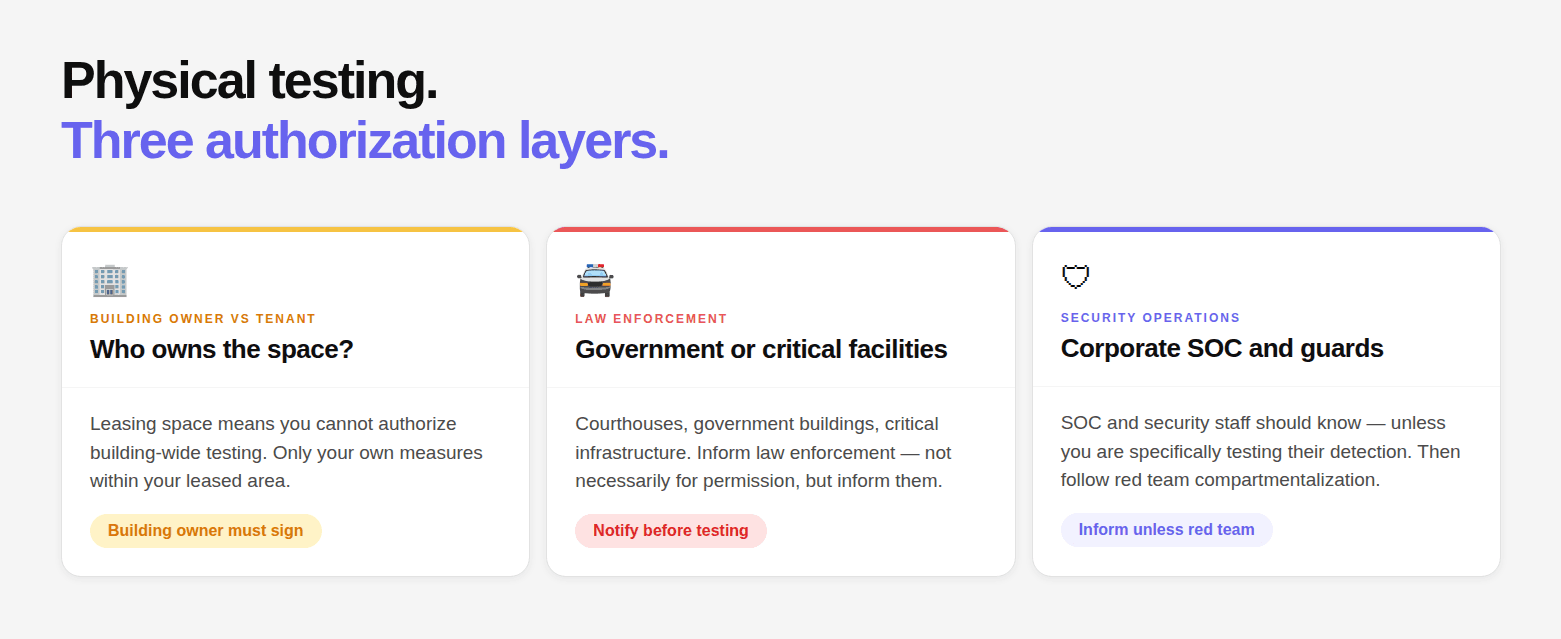
Building owner vs tenant: If your organization leases space rather than owns it, you likely cannot authorize physical security testing of the building itself. You can authorize testing of your own security measures within your leased space, but testing building-wide security (badge readers, elevator access, lobby security) requires the building owner or property manager.
Law enforcement: For any facility where law enforcement has a protective role (courthouses, government buildings, critical infrastructure), the law enforcement agency must be informed. Not necessarily asked for permission, but informed. The Coalfire case would have been resolved in minutes if the local Sheriff's office had known.
Security operations center (corporate): Your corporate SOC or security guard service should know the physical testing is occurring, unless you are specifically testing whether they detect and respond to physical intrusions (in which case, follow the red team compartmentalization approach).
Physical Scope: What Must Be Specified
Physical scope cannot be described in general terms. Phrases like “company offices” create ambiguity that becomes a problem in execution. A proper scope definition includes:
Exact addresses
Floor numbers and suite identifiers
Specific rooms or restricted zones
Explicit exclusions
Clear distinction between owned and shared spaces
It must also define allowed techniques such as tailgating, badge cloning, social engineering, and lock bypass methods. Anything not explicitly allowed should be considered out of scope.
The Get-Out-of-Jail Card: Design and Deployment
Every individual conducting physical testing must carry a physical authorization card. Not on their phone. On their person, in a location they can reach without reaching into a jacket (reaching into clothing during a law enforcement encounter creates escalation risk).
Card design requirements:
Organization letterhead
Engagement reference number (unique, verifiable)
Testing dates
24/7 emergency contact (mobile, not office)
Authentication code
Brief description ("authorized physical security assessment")
Contact person requirements:
Must be available by mobile, not desk phone
Must be senior enough to speak authoritatively to law enforcement
Must know the engagement is occurring and what is in scope
Must be prepared to receive calls at any hour during the testing window
Ideally: pre-contacted local law enforcement non-emergency line to inform them of the engagement
Card deployment:
Issued to every individual on the physical team before testing begins
Each tester confirms receipt
Card references the full authorization letter which should also be carried
Law Enforcement Pre-Notification
After the Iowa case, many experienced physical penetration testing teams now recommend proactive law enforcement notification as standard practice for any engagement that might result in police contact.
How to do it:
Contact the non-emergency number for the relevant law enforcement jurisdiction
Inform them that an authorized physical security assessment will be occurring at [address] between [dates]
Provide the engagement contact name and number
Ask for a confirmation number or officer name
Document this in the authorization letter
What to say: "We're a security firm conducting an authorized physical security assessment of [address] between [dates]. We wanted to inform you in advance in case any of our testers are reported as suspicious. Our authorization contact is [Name] at [Mobile]. Confirmation reference: [ID]."
Pre-notification doesn't mean permission. Law enforcement cannot authorize private security testing. Pre-notification is courtesy and risk management, not an authorization step.
Regulation by Jurisdiction
Physical security testing has jurisdiction-specific legal considerations beyond CFAA:
Trespass laws vary by state/country. Authorization from the building occupant may not defeat a trespass claim if the building owner hasn't authorized entry.
Wiretap / surveillance laws govern whether badge reader RFID skimming is legal in your jurisdiction.
Lock-picking laws vary significantly, some jurisdictions restrict possession of lock picks without a licensed locksmith credential.
Recording laws affect whether testers can record their activities for documentation.
Consult local counsel for any physical engagement that involves techniques beyond simple social engineering or tailgating.
Where Traditional Physical Authorization Breaks with AI Driven Testing
Physical testing is also evolving. AI is increasingly used in reconnaissance, pattern analysis, badge cloning simulations, and behavioral modeling.
This introduces new challenges.
Accelerate reconnaissance across physical and digital boundaries
Combine physical and digital attack paths
Interact with systems beyond the originally intended scope
Generate actions that were not explicitly planned
Traditional authorization models assume controlled human decision making. AI introduces speed and unpredictability. This creates gaps if authorization boundaries are not clearly defined.
Why This Matters Even More for AI Driven Penetration Testing
AI driven penetration testing introduces a new class of risk that traditional authorization models were not designed for.
Unlike manual testing, AI systems can autonomously explore systems, chain vulnerabilities, and interact with infrastructure at a scale and speed that makes unintended access more likely. This includes accessing out-of-scope systems, interacting with third-party services, or triggering cloud provider abuse detection mechanisms.
This makes clear authorization boundaries, defined scope, and documented procedures even more critical. Without strong authorization controls, AI driven testing can unintentionally cross legal and operational boundaries faster than a human tester could.
The authorization letter is no longer just a formality. It becomes the control layer that governs how AI systems are allowed to operate within defined limits.
How to Strengthen Physical Authorization for Modern Testing
To adapt to modern testing approaches, authorization documents should:
Identify all stakeholders with control over the environment
Define scope with exact physical boundaries
Include clear escalation and verification mechanisms
Account for both human and automated testing behavior
Align with local legal requirements
Ensure real-time verification capability
The objective is not to restrict testing. It is to ensure that when testing is challenged, it can be defended immediately and clearly.
Conclusion: Physical Authorization Fails When It is Treated as Internal Approval
Physical penetration testing does not operate in isolation. It operates in environments where authority is shared, enforcement is immediate, and assumptions are tested in real time.
Most failures do not happen because the authorization letter is missing. They happen because it is incomplete.
Because it covers the organization but not the building owner.
Because it defines scope but not shared spaces.
Because it assumes awareness where none exists.
Strong physical authorization is not about documentation.
It is about alignment.
Alignment between every party that has the ability to question, stop, or escalate the engagement.
When that alignment exists, testing proceeds as intended.
When it does not, the engagement stops at the first point of friction.
And in physical testing, that point is often not technical. It is human.
FAQs
Who needs to authorize a physical penetration test?
Is notifying law enforcement mandatory for physical testing?
What is a get-out-of-jail card and why is it important?
Why is physical scope definition more important than network scope?
Can authorization from the client alone protect testers legally?