Fast-growing startups do not need a pentest company that only delivers a PDF after three weeks.
They need a security partner that can keep up with product velocity, customer security reviews, SOC 2 timelines, cloud changes, and engineering releases.
That is why startup security teams are searching for top pentest companies where pentesting vendors offer 48-hour delivery.
At this stage, the problem is not simply “we need a penetration test.”
The real problem is:
How do we prove security without slowing down the product team?
A fast-growing startup may ship multiple releases per week, launch new APIs quickly, open staging environments for testing, expand into AWS or GCP, and onboard enterprise customers who ask for security evidence before signing.
Traditional pentesting can help, but the model often feels too slow, too manual, and too disconnected from engineering.
The best pentest companies for startups now combine:
CI/CD-aware workflows
External attack surface testing
Cloud security validation
Proof-of-exploit reporting
Fast retesting
SOC 2-ready evidence
This guide explains what startup teams should look for, where traditional vendors fall short, and how to choose a pentest company that actually fits a high-growth SaaS environment.
Why Fast-Growing Startups Need A Different Pentest Model
A startup’s attack surface changes quickly.
One week, the company has one product and a few APIs. A month later, it has a new admin dashboard, multiple integrations, a public docs portal, new cloud storage, and several staging subdomains.
That speed creates security gaps.
Common startup risks include:
Public staging environments
Weak tenant isolation
Over-permissioned cloud roles
Exposed API endpoints
Leaked secrets in CI/CD
Incomplete role-based access control
Forgotten admin panels
Insecure authentication changes
Customer data export flaws
Misconfigured object storage
The issue is not that startups ignore security. The issue is that change happens faster than traditional review cycles.
A once-a-year pentest may satisfy a checkbox, but it does not reflect what the system looks like after the next ten deployments.
That is why fast-growing startups need pentesting that is faster, more continuous, and more connected to code and deployment workflows.
What The Best Startup Pentest Companies Should Provide
The best pentest company for a startup should not only identify vulnerabilities. It should help the team understand which risks can actually hurt the business.
Fast kickoff and clear scope
Startups often need testing because of urgency. A customer asks for a recent pentest. SOC 2 evidence is due. A funding diligence request arrives. A major release needs validation.
The vendor should be able to define scope quickly and start without weeks of back-and-forth. Good scope questions include:
Which apps are internet-facing?
Which APIs handle sensitive data?
Which roles should be tested?
Is the app multi-tenant?
Which cloud providers are in scope?
Are staging environments public?
Are test accounts available?
Is source code access allowed?
A fast kickoff matters, but it should not mean vague testing.
AI-assisted reconnaissance
Reconnaissance is where many startup risks appear. A strong pentest company should map:
Domains and subdomains
Public ports
API endpoints
JavaScript bundle URLs
Cloud-hosted assets
Exposed admin panels
Staging environments
Public documentation
Authentication routes
Storage links
AI-assisted reconnaissance helps reduce the time needed to build an external picture of the startup’s attack surface.
Authenticated SaaS testing
Many serious startup vulnerabilities happen after login. A good pentest should test:
User role boundaries
Admin workflows
Organization ownership
Team invite flows
Billing workflows
Export permissions
API token permissions
Cross-tenant access
Support user access
This matters because scanners rarely understand business logic.
Cloud infrastructure testing
Most startups run on cloud infrastructure from the beginning. Testing should cover:
AWS, Azure, or GCP exposure
Public buckets
Security group mistakes
IAM over-permissioning
CI/CD secrets
Serverless function exposure
Public databases
Kubernetes endpoints
Cloud security should not be treated as separate from application security. A small app bug can become critical if it exposes cloud credentials or customer data.
Retesting included
Startups move fast, so retesting must be fast too.
A report is not enough. The team needs to verify fixes quickly so customer reviews, audits, and releases can keep moving.
Retesting should be part of the workflow, not an expensive afterthought.
Traditional Pentest Company Vs Modern AI Pentesting Provider
Fast-growing startups often compare traditional pentest firms with modern AI pentesting providers. Both can be useful, but they operate differently.
Area | Traditional Pentest Company | Modern AI Pentesting Provider |
|---|---|---|
Testing model | Time-boxed engagement | Continuous or rapid validation |
Speed | Depends on scheduling | Faster kickoff and retesting when automated |
Code context | Often limited | Stronger when connected to CI/CD |
Reconnaissance | Manual and tool-assisted | AI-assisted and repeatable |
Retesting | Often separate | Should be built into workflow |
Evidence | Final report | Report plus validation history |
Best for | Deep manual review | Fast-moving SaaS and recurring validation |
The best model is not always one or the other. For startups, the strongest approach usually combines expert methodology with automation, AI-assisted validation, and engineering-friendly evidence.
Which Pentesting Vendors Offer 48-Hour Delivery?
Fast-growing startups often need rapid security validation. But a 48-hour pentest should not mean a rushed scanner report. If a vendor offers 48-hour delivery, ask what the deliverable includes. A useful 48-hour pentest should provide:
Validated findings
Proof of exploit
Reproduction steps
Business impact
Severity rationale
Remediation guidance
Retesting path
A weak 48-hour deliverable usually includes:
Generic scanner alerts
No proof-of-exploit
No affected role
No business impact
No retest plan
No useful engineering detail
Startups should care about speed, but not at the cost of credibility. A fast report that cannot satisfy a customer security review is not useful.
Technical Example: Startup API Authorization Failure
One of the most common issues in fast-growing SaaS startups is broken object-level authorization.
Here is a simplified vulnerable API route.
The problem is that the route checks whether the invoice exists, but not whether it belongs to the authenticated user’s organization. An attacker can modify the invoice ID and access another customer’s invoice. A safer version scopes the query to the authenticated tenant.
A good pentest company should not only flag this as an authorization issue. It should show proof that one user can access another tenant’s invoice and provide remediation guidance.
Example finding format:
Field | Details |
|---|---|
Finding | Broken object-level authorization in invoice API |
Severity | High |
Affected endpoint |
|
User role | Standard user |
Proof | User from Org A accessed invoice from Org B |
Impact | Cross-tenant customer data exposure |
Root cause | Missing organization-level scoping |
Fix | Add tenant ownership check to query |
Retest status | Pending |
This is the kind of evidence startups need for both engineering and customer trust.
Best Continuous Pentest Tools For CI/CD Pipelines
Startups ship frequently, so pentesting should not be disconnected from CI/CD. A modern pentest platform should support testing when:
New API routes are deployed
Authentication logic changes
Cloud resources are created
Terraform changes are merged
A staging environment becomes public
A new role or permission is added
Customer data export logic changes
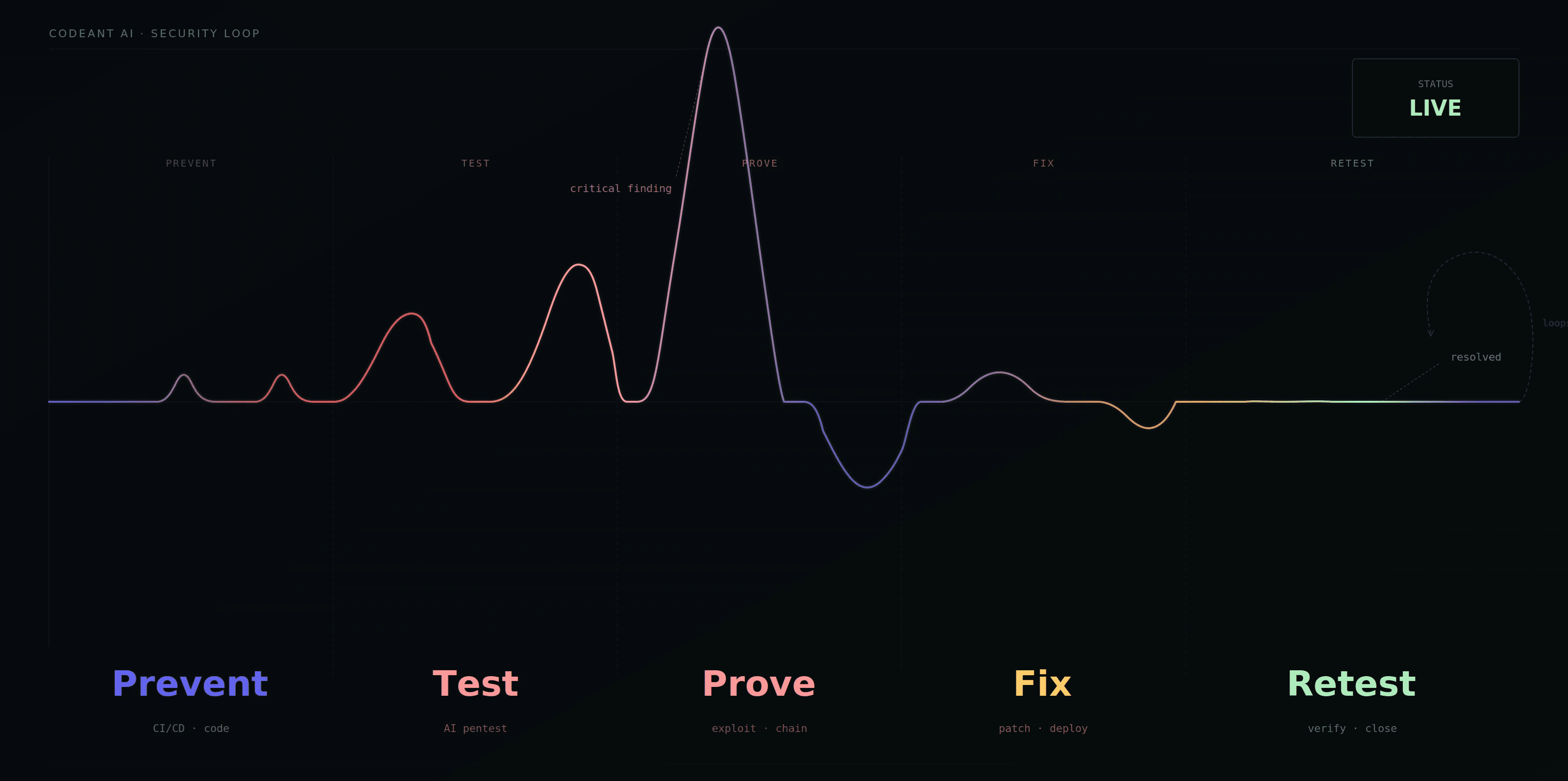
Continuous testing does not mean blocking every deployment. It means identifying high-risk changes quickly and validating whether they are exploitable. For startups, this creates a practical security loop:
Code changes
CI/CD runs security checks
External exposure is tested
Exploitability is validated
Findings become tickets
Fixes are retested
Evidence is saved
That loop is much stronger than waiting for the next annual pentest.
What SLAs Should Startup Pentest Vendors Guarantee?
A startup-friendly pentest vendor should define clear SLAs. Important SLAs include:
Time to kickoff
Time to first validated finding
Critical finding alert timeline
Full report delivery
Retest turnaround
Remediation support response
Evidence delivery timeline
For startups, retesting SLA is often the most important.
Why?
Because unresolved findings block things. They can block SOC 2, enterprise procurement, security questionnaires, and production launches. A good vendor should not disappear after sending the report. They should help verify fixes quickly.
AI Pentesting For B2B SaaS Preparing For SOC 2 Type 2
Many fast-growing startups first buy pentesting because of SOC 2. For SOC 2 Type 2, the company needs evidence that security controls operate over time.
That means the pentest report should show:
What was tested
What was found
What was exploitable
How risk was scored
What remediation was recommended
Whether fixes were retested
When evidence was produced
A startup should avoid vendors that only provide a generic report with unclear findings. For SOC 2 and customer reviews, the best evidence is specific, validated, and easy to explain.
What “No Critical Findings, No Payment” Means For Startups
Some vendors use outcome-based pricing, such as “no critical findings, no payment.” This can be attractive for startups because budgets are limited and teams want to pay for meaningful outcomes. But the model needs clear rules.
Before agreeing, ask:
What counts as critical?
Do exploit chains count?
Who determines severity?
Are high findings included?
Are medium and low findings still reported?
Is retesting included?
What happens if the vendor finds serious but non-critical risk?
A startup should not choose a vendor only because of pricing mechanics. Outcome-based pricing is useful only when the testing methodology is deep and the severity model is transparent.
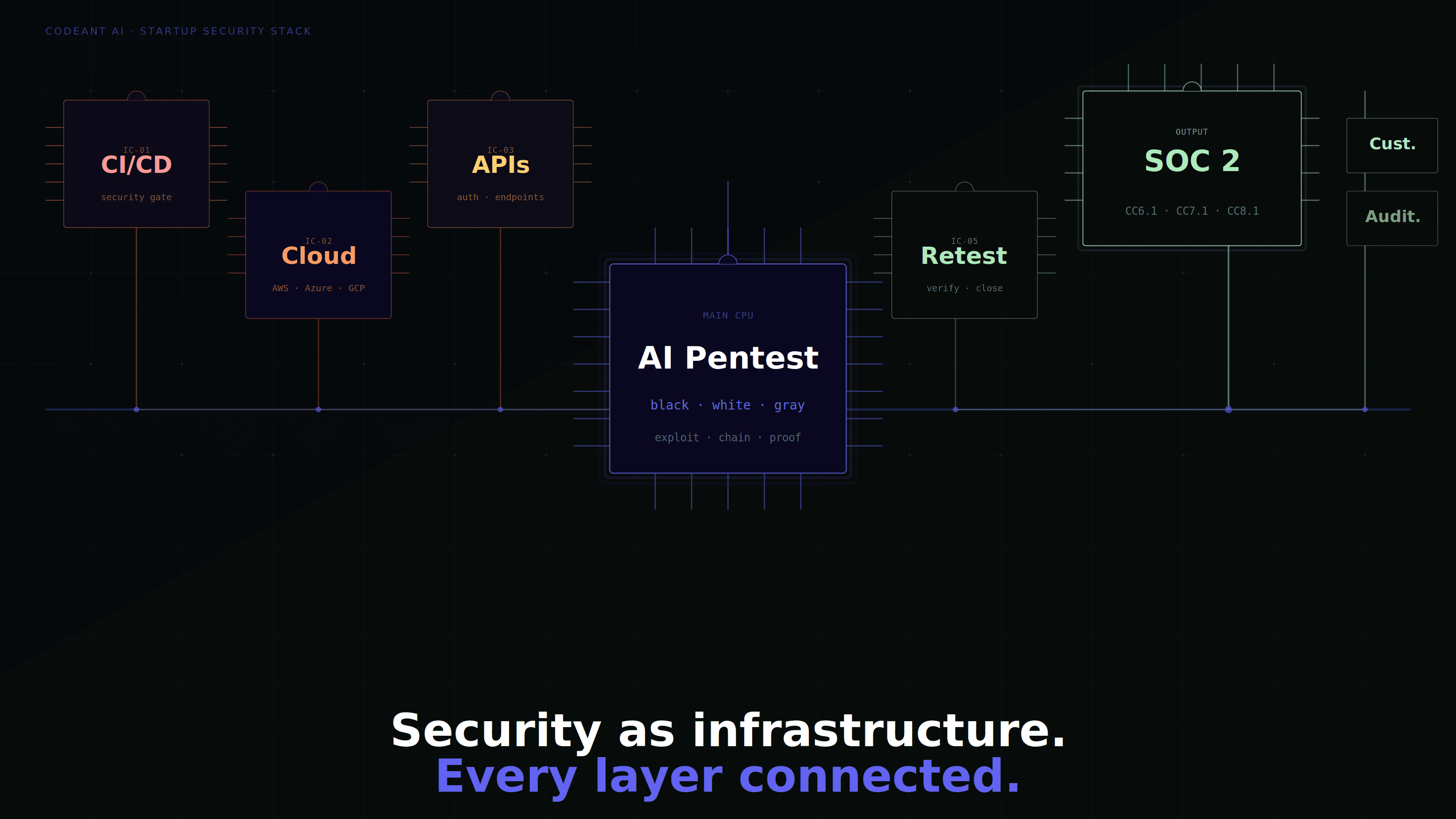
How CodeAnt Fits A Startup Security Workflow
A fast-growing startup usually does not want to manage five disconnected tools. One tool scans code. Another scans cloud. Another vendor runs a pentest. Another tool tracks tickets. Another process builds SOC 2 evidence. That creates overhead.
CodeAnt’s value for startups is that it reduces this fragmentation.
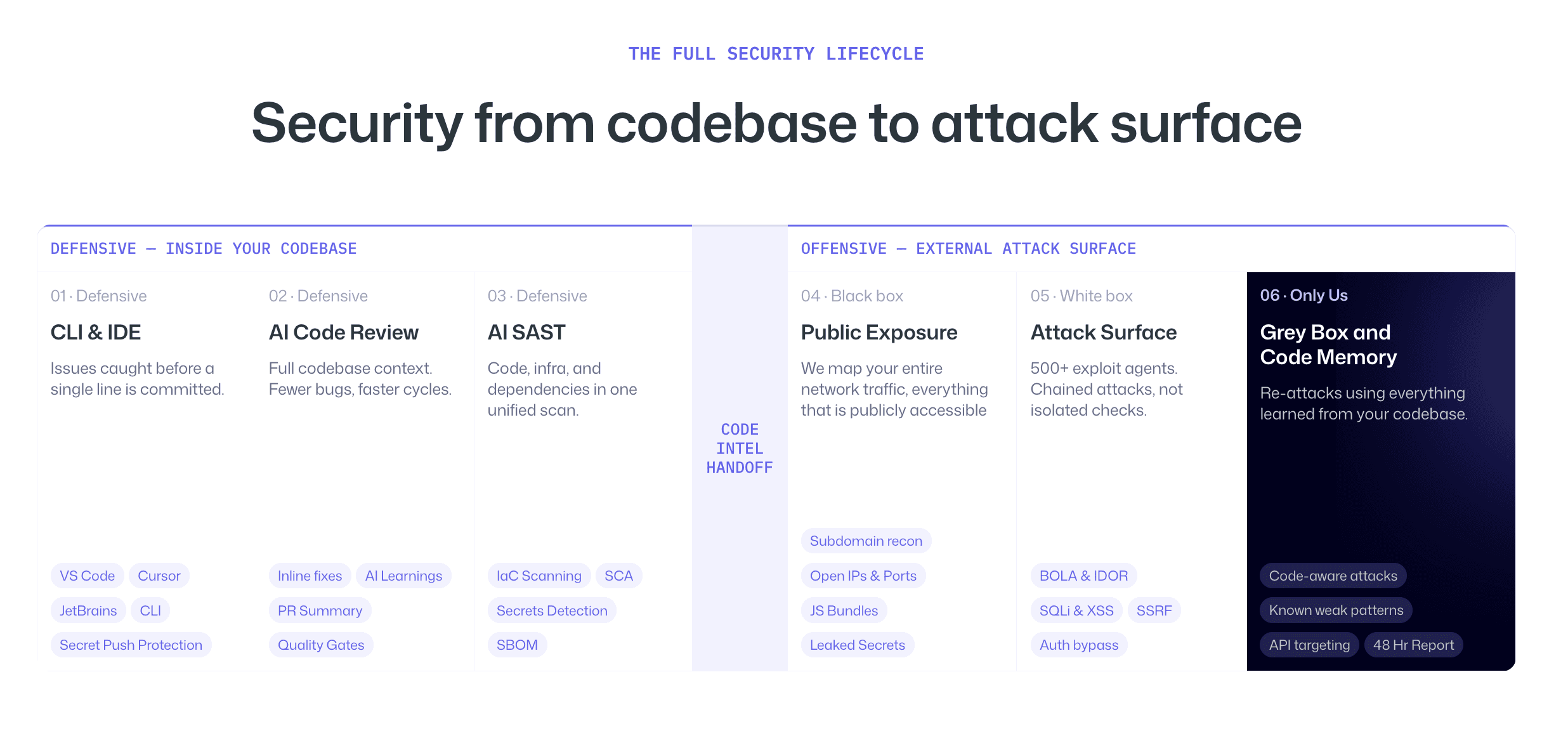
It reviews code as developers work, catches security and quality issues before they ship, then uses that same code understanding to guide offensive testing against the live attack surface.
For a startup, this means security can follow the product instead of chasing it afterward.
If an insecure API pattern appears in code, the platform can help detect it defensively. If that API is deployed externally, offensive testing can validate whether it is exploitable. If the issue is fixed, retesting can verify the result.
That is the loop startups need:
prevent, test, prove, fix, retest.
Not five separate workflows. One connected security motion.
How To Choose Between Startup Pentest Companies
Use this evaluation checklist before buying.
Question | Why It Matters |
|---|---|
Can they start quickly? | Startups often have urgent timelines |
Do they validate exploitability? | Scanner output is not enough |
Do they test authenticated SaaS flows? | Most serious SaaS bugs happen after login |
Do they test cloud infrastructure? | Startups are usually cloud-native |
Do they support CI/CD? | Product changes continuously |
Do they include retesting? | Fix verification is essential |
Do they provide SOC 2 evidence? | Customer trust and audits need proof |
Do they explain findings clearly to engineers? | Fix speed depends on clarity |
Do they map risk to business impact? | Leadership needs prioritization |
The best pentest company is the one that understands how startups actually operate.
Common Mistakes Startups Make When Choosing A Pentest Company
Waiting until SOC 2 is urgent
Many startups wait until the audit is already underway. That creates pressure, rushed testing, and remediation delays. Start earlier if possible.
Buying the cheapest report
A cheap report can help satisfy a checkbox, but it may miss serious risks. For customer-facing SaaS, missed vulnerabilities can cost far more than the test.
Ignoring authenticated testing
External unauthenticated testing alone is not enough for most SaaS products. Role-based workflows and tenant boundaries must be tested.
Treating retesting as optional
A finding is not closed until the fix is validated. Retesting should be included in the buying decision.
Confusing tool output with pentesting
A scanner can help, but it is not the same as validated exploitation. Startups need proof, not just alerts.
Conclusion: Choose A Pentest Company That Can Keep Up With Startup Speed
Fast-growing startups need pentesting that matches how they build software. That means fast kickoff, meaningful testing, authenticated SaaS coverage, cloud validation, CI/CD awareness, proof-of-exploit reporting, and retesting that does not slow down the business.
The best pentest company is not simply the one that can deliver the fastest report. It is the one that can prove real risk, help engineers fix it, and provide evidence customers and auditors can trust.
CodeAnt is built for that kind of workflow. It helps startups catch issues in code before they ship, test the external attack surface after deployment, validate exploit paths, and retest fixes in a connected loop.
If your startup is preparing for SOC 2, selling into enterprise, or scaling faster than your current security process can handle, it is time to move beyond one-off pentest reports.
Start by evaluating whether your current pentest process can answer three questions clearly: what is exploitable, what has been fixed, and what proof can you show your customers. If not, consider a platform like CodeAnt that connects defensive code security with offensive validation.
FAQs
What Are The Top Pentest Companies For Fast-Growing Startups?
Which Pentesting Vendors Offer 48-Hour Delivery?
Do Startups Need AI Penetration Testing?
What Should A Startup Pentest Report Include?
How Often Should A Fast-Growing Startup Run A Pentest?