Why most penetration testing comparisons get it wrong?
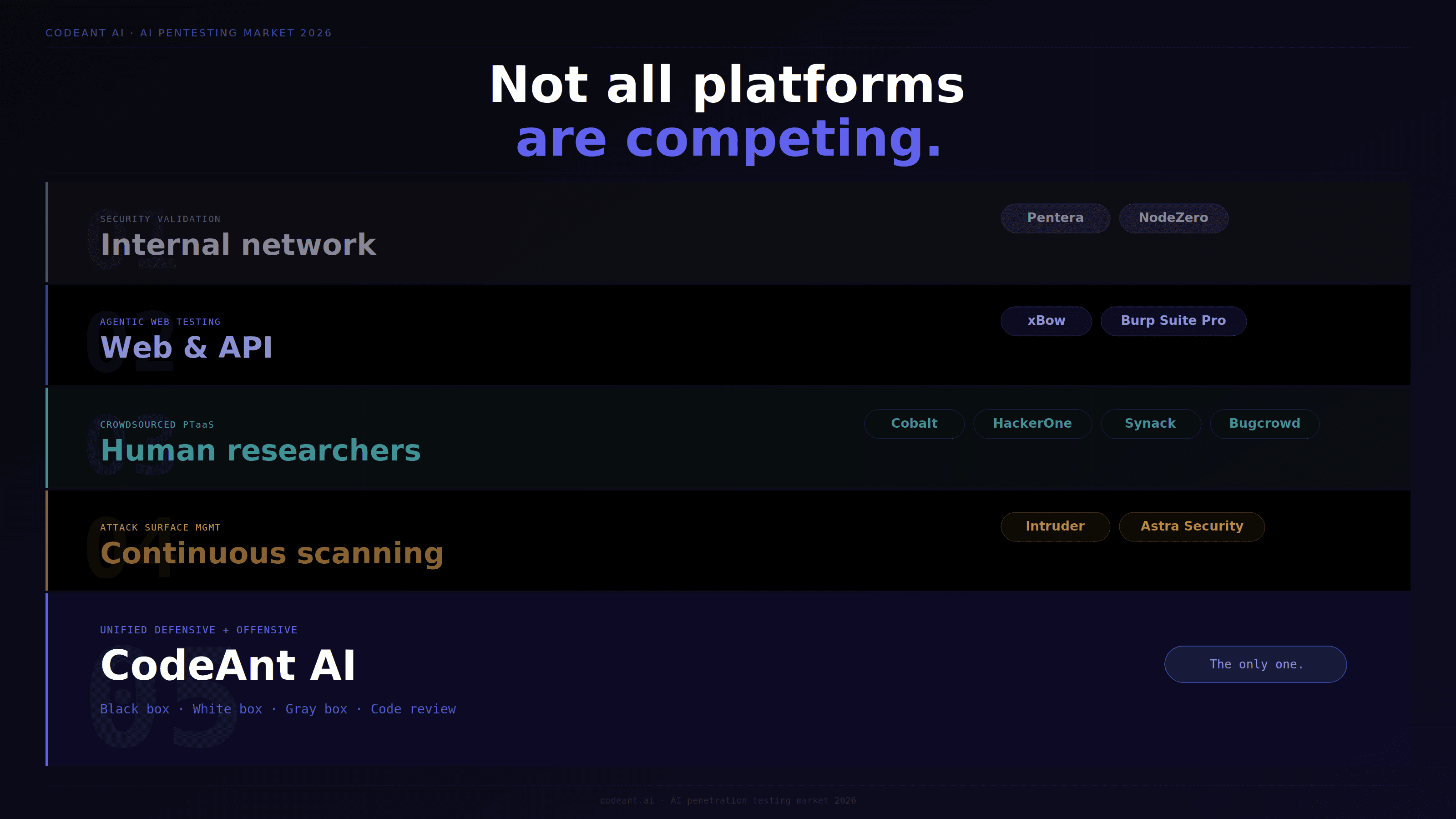
Every "best AI pentesting tools" list published in 2026 makes the same mistake. It ranks platforms against each other as if they are competing for the same use case. They are not.
Pentera and NodeZero are built for internal network validation.
xBow is built for autonomous web application testing. Intruder is a continuous attack surface scanner.
Cobalt and HackerOne are crowdsourced human testing platforms.
Synack is vetted human researchers for government and regulated enterprise.
CodeAnt AI is the only platform on this list that operates on both sides of the security equation, the same code intelligence reviewing your pull requests for insecure patterns is also conducting reconnaissance and exploit chain construction against your external attack surface.
Comparing these as interchangeable penetration testing alternatives is like comparing a cardiologist to a neurologist because both are doctors. The right question is not which platform is best. It is which platform answers the security question your organization most urgently needs answered.
This guide covers every major platform in detail:
what each actually does
what it structurally cannot find
real pricing
who it is right for
who it is wrong for
No sponsored rankings. No vague capability claims. The information buyers need to make the right decision.
How to Read This Guide
The AI penetration testing market in 2026 spans four distinct categories. Understanding which category a platform belongs to is the prerequisite for any useful comparison.
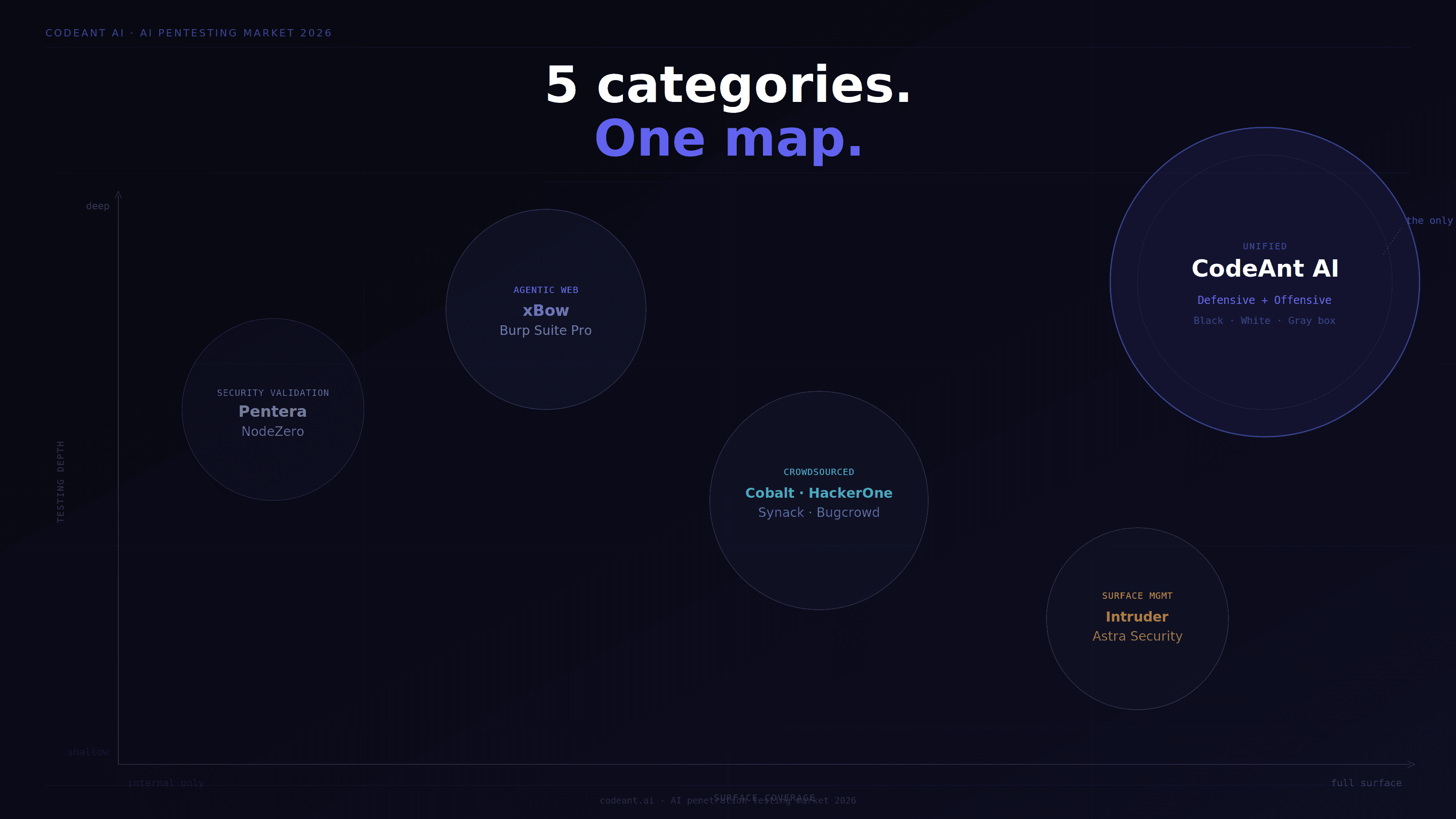
Category 1: Automated security validation platforms: Pentera, NodeZero (Horizon3.ai). Focused on internal network infrastructure, Active Directory, lateral movement, and credential validation. Best for enterprise teams needing continuous internal control validation.
Category 2: Agentic AI web application testing: xBow, Burp Suite Pro. Focused on autonomous web and API vulnerability discovery. Best for teams needing deep web application coverage with AI-driven exploit chaining.
Category 3: Crowdsourced PTaaS: Cobalt, HackerOne, Synack, Bugcrowd. Human researchers augmented by AI for platform management and triage. Best for organizations wanting human judgment at scale with flexible engagement models.
Category 4: Continuous attack surface management: Intruder, Astra Security. Scanner-based continuous monitoring for external exposure. Best for teams needing ongoing CVE-to-infrastructure mapping without deep methodology testing.
Category 5: Unified defensive and offensive platforms: CodeAnt AI. The only platform combining continuous defensive code review with full-spectrum offensive penetration testing (black box, white box, gray box) on the same intelligence layer.
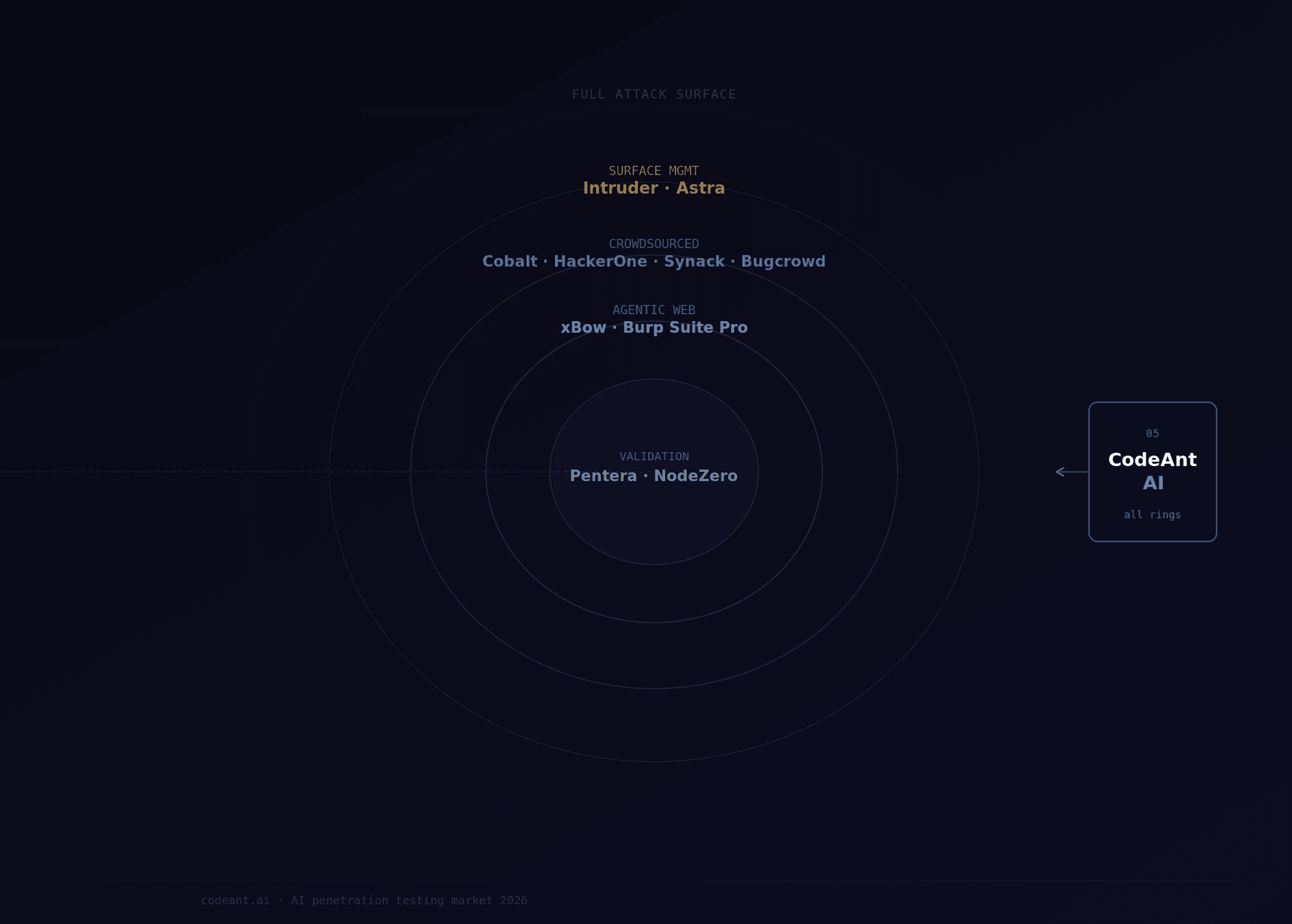
Understanding which category you actually need eliminates most of the buying confusion before any feature comparison begins.
Master Comparison Table: Best Penetration Testing Tool in 2026
Platform | Category | Black box | White box | Gray box | JS bundle analysis | Attack chain construction | Defensive code review | SOC 2 evidence package | Pricing model |
|---|---|---|---|---|---|---|---|---|---|
CodeAnt AI | Unified defensive + offensive | ✅ Full | ✅ Full | ✅ Full | ✅ Yes | ✅ Cross-track chains | ✅ Yes — CI/CD integrated | ✅ Complete (8 docs) | Pay only for high/critical findings |
Pentera | Automated security validation | ⚠️ Limited | ❌ No | ⚠️ Limited | ❌ No | ✅ Internal network paths | ❌ No | ⚠️ Partial | ~$46,000–$50,000/yr subscription |
NodeZero (Horizon3.ai) | Automated security validation | ⚠️ Limited | ❌ No | ⚠️ Limited | ❌ No | ✅ Network attack chains | ❌ No | ⚠️ Partial | ~$35,000/yr subscription |
xBow | Agentic web app testing | ✅ Web only | ❌ No | ⚠️ Limited | ❌ No | ✅ Web app chains | ❌ No | ⚠️ Partial | $4,000–$6,000/test |
Cobalt | Crowdsourced PTaaS | ✅ Yes | ❌ No | ✅ Yes | ❌ No standard | ⚠️ Tester-dependent | ❌ No | ✅ Yes | Credit-based, $65K–$100K+/yr |
HackerOne | Crowdsourced PTaaS | ✅ Yes | ❌ No | ✅ Yes | ❌ No standard | ⚠️ Tester-dependent | ❌ No | ✅ Yes | Per-engagement + bounty pools |
Synack | Vetted crowdsource | ✅ Yes | ❌ No | ✅ Yes | ❌ No standard | ⚠️ Tester-dependent | ❌ No | ✅ Yes | Enterprise subscription, premium pricing |
Intruder | Continuous ASM scanner | ✅ External only | ❌ No | ❌ No | ❌ No | ❌ No | ❌ No | ❌ Scanner output only | $1,188–$4,788+/yr |
Astra Security | Scanner + manual | ✅ External | ❌ No | ⚠️ Limited | ❌ No | ❌ No | ❌ No | ⚠️ Partial | $5,999–$9,999/yr |
Burp Suite Pro | Manual web testing toolkit | ✅ Manual | ❌ No | ✅ Manual | ❌ No standard | ❌ No automated | ❌ No | ❌ No | $449/yr per user |
Platform 1: CodeAnt AI
Category: Unified defensive and offensive security platform
Best for: SaaS teams handling customer data, SOC 2 compliance, continuous deployment environments
Pricing: Free for low and medium findings. Pay only when high or critical issues are confirmed. Unlimited retests included.
CodeAnt AI is the only platform in this comparison that operates on both sides of the security program simultaneously. The defensive layer reviews every pull request in CI/CD for insecure patterns, authentication configurations, data flows to dangerous sinks, insecure API patterns, dependency vulnerabilities, in full codebase context, not just the changed lines. The offensive layer conducts full-spectrum penetration testing across three parallel tracks informed by that code intelligence.
What makes it structurally different from every other platform:
When the system that has spent months reviewing your authentication middleware for insecure patterns is the same system conducting external reconnaissance, the offensive engagement is fundamentally deeper. It already knows your authentication patterns, your middleware configuration, your data flows, and your dangerous sinks before the first probe is sent. An adversary with persistent inside knowledge of your codebase testing your external surface is the most accurate simulation of how sophisticated real-world attacks actually operate.
The black box track starts from a domain name only. DNS enumeration across 150+ subdomain patterns, Certificate Transparency log queries, full TCP port scanning, cloud asset enumeration (S3, Azure Blob, GCP, exposed CI/CD dashboards, container registries), and JavaScript bundle analysis. JS bundle analysis alone — downloading and analyzing every compiled JS file for hardcoded secrets, internal endpoints, and infrastructure references, is a capability no other platform on this list runs systematically as part of black box methodology. Hardcoded secrets are verified live against the API before reporting: a Stripe key is tested against the Stripe API to confirm it is active and what permissions it grants.
The white box track traces every user-controlled input from HTTP entry to every dangerous sink across the entire codebase. The authentication configuration for every framework is read end-to-end, Spring Security filter chains, Express.js middleware ordering, Django permission classes. Git history is scanned separately from the current HEAD, finding credentials committed and deleted that remain fully recoverable from version control.
The gray box track tests every role boundary, every identifier-accepting endpoint for IDOR, every critical workflow for step-bypass attacks, and every JWT for signature validation failures. Business logic testing, subscription tier abuse, price manipulation, checkout workflow bypass, concurrent request race conditions, runs systematically across every authenticated flow.
Real findings from recent engagements:
476,000 healthcare records confirmed exposed via open Cognito signup → admin panel chain.
742 million person records accessible via GraphQL introspection and BOLA.
27,255 CRM contacts embedded in a client-facing JS bundle.
Enterprise customer lists at Fortune 500 vendor platforms. Production credentials in public source maps.
Researcher credentials: 87 published CVEs. VulnCheck CNA partner. CVSS 10.0 (CVE-2026-29000, pac4j-jwt) and CVSS 9.8 (CVE-2026-28292, simple-git) on public record in the NVD. MSRC submissions at CVSS 9.8 and 9.1. Verifiable by any auditor in minutes. Check out more here: https://www.codeant.ai/security-research
SOC 2 evidence package: Complete retest report confirming verification in the production environment, timeline documentation per finding, data deletion certificate, compliance mapping to specific TSC control IDs (CC6.1, CC6.6, CC7.1), estimated regulatory penalty exposure per finding across SOC 2, ISO 27001, HIPAA, GDPR, PCI-DSS, and Cert-In. All included as standard deliverables, not add-ons.
Platform 2: Pentera
Category: Automated security validation
Best for: Enterprise teams needing continuous internal network control validation
Pricing: ~$46,000–$50,000/year subscription. Typical enterprise spend ~$120,000/year per verified analyst data.
Pentera is the category leader in automated security validation for internal network infrastructure. It deploys an agent inside your network perimeter and continuously simulates what an adversary who has breached the perimeter would do: credential sniffing and cracking, lateral movement across network segments, Active Directory attack paths, privilege escalation, and ransomware resilience testing against real-world strains including LockBit and BlackCat.
Where it excels: Internal network validation at enterprise scale. Continuous credential exposure assessment. Active Directory attack path visualization. Ransomware resilience validation. Agentless deployment across enterprise environments once the platform agent is installed.
Where it structurally cannot go: No white box source code analysis. No JavaScript bundle analysis. No gray box business logic testing for application-layer flows. G2 and Gartner reviewers consistently note external testing is limited — one Gartner review states directly: "you are limited to specific testing scenarios." No defensive code review integration. No data deletion certificate as a standard deliverable.
SOC 2 note: Strong for validating internal controls relevant to CC6.3 (access modification) and network-layer CC6.6 findings. Coverage gaps on application-layer CC6.1 authentication bypass and CC7.1 business logic vulnerabilities mean SaaS teams typically need to supplement Pentera with an application security engagement for complete SOC 2 Type II evidence.
Platform 3: NodeZero (Horizon3.ai)
Category: Automated security validation
Best for: Enterprise infrastructure teams needing continuous network penetration testing
Pricing: ~$35,000/year. Approximately £40 per IP address annually for networks up to 2,500 IPs.
NodeZero was founded by former US Special Operations and National Security veterans and has executed over 170,000 pentests across approximately 4,000 organizations with zero production downtime. It dynamically traverses networks to chain together exploitable weaknesses, misconfigurations, weak credentials, CVEs, into multi-step attack paths that demonstrate real business impact, not just theoretical risk.
Where it excels: Network and infrastructure attack path chaining. Continuous autonomous network testing. Proven at scale. No web application or source code analysis.
Where it structurally cannot go: Similar to Pentera, no white box, no JS bundle analysis, no application-layer gray box testing, no defensive code review. Does not generate full SOC 2 compliance reports including data deletion certificates per verified analyst data.
Platform 4: xBow
Category: Agentic AI web application testing
Best for: Teams needing autonomous web application testing with validated findings
Pricing: $4,000–$6,000 per test. Enterprise continuous testing at custom pricing.
Founded by Oege de Moor, creator of GitHub Copilot and GitHub Advanced Security, it deploys thousands of short-lived parallel agents, each tackling a narrow scoped objective with fresh context, coordinated by a persistent global attack surface manager. Its critical differentiator: it separates AI exploration from deterministic exploit verification, driving an exceptionally low false positive rate.
Where it excels: Autonomous web application vulnerability discovery with deterministic exploit validation. Very low false positive rates. Fast. Microsoft Copilot and Sentinel native integration. Self-service entry point at $4,000 per test.
Where it structurally cannot go: Web applications only, no network testing, no infrastructure testing, no cloud security beyond web surface. No source code analysis. No defensive code review integration. No SOC 2 data deletion certificate as standard. No business logic testing depth comparable to gray box methodology. If you choose xBow for web application testing, you still need separate tools for network, infrastructure, and cloud.
Platform 5: Cobalt
Category: Crowdsourced PTaaS
Best for: Fast-moving DevOps teams needing on-demand human-tested assessments
Pricing: Credit-based. Small deployments $65,000–$100,000 annually. Negotiation possible with competitive quotes.
Cobalt's platform launches new tests in as little as 24 hours by matching your target to vetted researchers from its community. Real-time reporting and direct tester communication align well with agile workflows. The credit model provides flexibility for teams with variable testing needs across the year.
Where it excels: Fast launch, human validation, broad coverage across web, API, mobile, and network. Flexible credit consumption model. Strong for compliance-driven assessments with human-validated findings.
Where it structurally cannot go: Tester quality is variable, you are matched to a researcher, not a dedicated team. No source code analysis as a standard service. No defensive code review integration. Different tester on each engagement means no accumulated code intelligence. Chain construction quality depends on the individual tester assigned. SOC 2 reports can require post-processing to align with specific auditor expectations per competitive analysis data.
Platform 6: HackerOne
Category: Crowdsourced PTaaS + bug bounty
Best for: Organizations wanting combined pentest and continuous bug bounty program
Pricing: Per-engagement plus bounty pools. Enterprise programs start at significant investment, enterprise pricing reported at the high end of the PTaaS market.
HackerOne operates the largest hacker-powered security platform globally, with over 1.5 million security researchers. Its pentest service (HackerOne Pentest) matches vetted testers to your specific asset type and compliance needs. The combination of formal pentest engagements and continuous bug bounty programs provides the broadest possible researcher coverage.
Where it excels: Massive researcher pool. Bug bounty integration for continuous coverage. FedRAMP capabilities for government requirements. Compliance-ready reporting for major frameworks.
Where it structurally cannot go: No source code analysis as standard. No defensive code review integration. Tester quality variable across the researcher pool. High cost at enterprise scale, reported monthly pricing at the very high end of the market. No systematic JS bundle analysis or cloud asset enumeration as standard black box methodology.
Platform 7: Synack
Category: Vetted crowdsourced testing Best for: Government agencies, defense contractors, highly regulated enterprises Pricing: Enterprise subscription, premium pricing. Typically 10–20% above Cobalt for comparable scope.
Synack operates the Synack Red Team (SRT), a highly vetted community of global security researchers screened more rigorously than any other crowdsourced platform. Its platform combines human expertise with machine learning for automated reconnaissance and scaling, while human researchers focus on complex logical vulnerabilities. FedRAMP authorization makes it the platform of choice for government and defense organizations.
Where it excels: Highest-vetting standards in crowdsourced testing. FedRAMP authorized. Strong for government, defense, and highly regulated industries with specific compliance requirements around tester vetting. Continuous testing capability with human depth.
Where it structurally cannot go: Premium cost limits accessibility. No source code analysis as standard. No defensive code review integration. Same crowdsourced quality variability as other human-researcher platforms, though the vetting process narrows it significantly. For most SaaS companies without government or defense requirements, the premium over Cobalt is difficult to justify.
Platform 8: Intruder
Category: Continuous attack surface management scanner
Best for: Teams needing continuous external CVE-to-infrastructure mapping
Pricing: $1,188–$4,788+/year depending on target count and plan.
Intruder is an international cybersecurity company providing continuous vulnerability scanning for external attack surfaces. It keeps a live inventory of your external exposure and flags newly-published CVEs against your software inventory in near-real time. Clean UX, actionable prioritization, simple setup.
Where it excels: Continuous external monitoring. Fast CVE coverage. Clean reporting. Accessible price point. Good for teams that need ongoing awareness of their external posture without deep methodology testing.
Where it structurally cannot go: This is a scanner, not a penetration testing platform. It does not confirm exploitation. Findings are potential vulnerabilities based on version detection and signature matching — not confirmed exploits with working proof-of-concept. SOC 2 auditors will not accept Intruder output as penetration testing evidence. No authenticated gray box testing, no source code analysis, no business logic testing, no attack chain construction. For teams that understand this distinction and need the specific function Intruder provides, it works well. For teams that think it satisfies penetration testing requirements, it does not.
Platform 9: Astra Security
Category: Scanner with manual pentest add-on
Best for: Budget-conscious SMBs needing continuous automated scanning with periodic manual validation
Pricing: $5,999–$9,999/year. Automated scanning from $199/month.
Astra provides 2,500+ automated security tests with a manual pentest add-on component. Its dashboard allows vulnerability visualization and team assignment. CI/CD, Slack, and Jira integrations support developer-workflow integration. For startups and small teams that need a starting point for compliance without significant budget, Astra offers accessible coverage.
Where it excels: Accessible pricing. Broad automated test coverage. Clean dashboard. OWASP and SANS 25 alignment. Good starting point for teams in early compliance stages.
Where it structurally cannot go: Manual testing component is lighter than dedicated pentest firms. Complex business logic and sophisticated authentication flows require deeper testing than the Astra model provides per competitive analysis. No source code analysis. No defensive code review integration. Compliance reports require supplementation for SOC 2 Type II auditor evidence on application-layer controls.
Platform 10: Burp Suite Pro
Category: Manual web application testing toolkit
Best for: Skilled security researchers conducting in-house manual assessments
Pricing: $449/year per user.
Burp Suite Pro is the industry-standard web application testing toolkit. In the hands of a skilled security researcher, it remains the most powerful web application testing tool available. The InQL extension adds GraphQL testing capability. The scanner adds automated vulnerability detection. For in-house security teams with pentest expertise, it is an essential component of any web application assessment toolkit.
The critical distinction: Burp Suite is a tool, not a managed engagement. It does not conduct a penetration test, a human uses it to conduct a penetration test. There is no methodology, no chain construction, no compliance reporting layer, no retest workflow. The quality of findings depends entirely on the operator's expertise. For teams without in-house pentest expertise, Burp Suite is a toolkit they cannot productively use. For teams with expertise, it is irreplaceable. It is not a competitor to managed platforms, it is what skilled researchers use within managed platforms.
Pricing Comparison of Best Penetration Testing Tools Everyone Wants
Platform | Pricing model | Entry cost | Enterprise cost | What drives cost |
|---|---|---|---|---|
CodeAnt AI | Pay per high/critical finding | $0 if only low/medium found | Scales with findings severity | Actual risk found, not time spent |
Pentera | Annual subscription | ~$46,000/yr | ~$120,000/yr | Asset count, feature modules |
NodeZero | Annual subscription | ~$35,000/yr | Custom | IP count, environment size |
xBow | Per-test + enterprise | $4,000/test | Custom continuous | Test count, asset scope |
Cobalt | Credit-based annual | $65,000/yr | $100,000+/yr | Credits consumed, test count |
HackerOne | Per-engagement + bounty | Custom | Very high | Researcher scope, bounty pool |
Synack | Enterprise subscription | Premium | Premium+ | Continuous coverage scope |
Intruder | Annual subscription | $1,188/yr | $4,788+/yr | Target count, scan frequency |
Astra Security | Annual subscription | $5,999/yr | $9,999/yr | Test scope, manual add-ons |
Burp Suite Pro | Annual per user | $449/user/yr | Scales with team | User count |
What each platform finds and misses: the honest breakdown
The most useful information for any buyer is not what a platform claims to cover, it is what it structurally cannot find, regardless of how the engagement is scoped.
Vulnerabilities only CodeAnt AI finds on this list:
Middleware authentication bypasses in source code (Express.js ordering, Spring Security exclusions) that produce normal HTTP responses externally
Hardcoded credentials in Git history, committed and deleted, still recoverable
JS bundle secrets verified live against APIs before reporting
Business logic vulnerabilities at the resolver level (GraphQL BOLA, mass assignment)
Dataflow injection tracing from HTTP entry to dangerous sink across function call chains
Staging vs. production bundle comparison surfacing forgotten API endpoints
Vulnerabilities only Pentera and NodeZero find on this list:
Internal network lateral movement paths
Active Directory credential attack paths
Ransomware resilience gaps
Internal service credential exposure across network segments
Complex privilege escalation across enterprise infrastructure
Vulnerabilities xBow finds better than most:
Novel web application attack patterns through autonomous agent reasoning
Parallel exploit validation at scale with low false positive rates
Web application zero-days requiring creative agentic reasoning
What scanners (Intruder, Astra automated tier) find:
Known CVEs on externally accessible software versions
Basic misconfiguration patterns
Public S3 bucket access
Missing security headers
TLS/SSL configuration issues
What scanners do not find (and cannot be used to claim they found):
Confirmed exploitation of any finding
Business logic vulnerabilities
Authentication bypass that requires code-level analysis
IDOR across authenticated flows
Any vulnerability requiring human or AI reasoning beyond signature matching
Choosing the Right Penetration Platform: Decision Framework
Answer these four questions before evaluating any platform:
Question 1: What is your primary attack surface?
Internal network infrastructure → Pentera or NodeZero
Web applications and APIs → CodeAnt AI, xBow, Cobalt, HackerOne
External surface continuous monitoring → Intruder, Astra
Full stack (application + cloud + code) → CodeAnt AI
Question 2: What is your primary compliance requirement?
SOC 2 Type II with complete evidence package → CodeAnt AI (only platform with data deletion certificate as standard, specific TSC control mapping, and unlimited retests included)
FedRAMP / government compliance → Synack
Compliance starting point for SMB → Astra, Intruder
PCI-DSS with deep manual testing → Cobalt, HackerOne, CodeAnt AI
Question 3: Do you need defensive coverage alongside offensive testing?
Yes, code review in CI/CD + penetration testing on one platform → CodeAnt AI only
No, offensive testing only → any of the above based on attack surface
Question 4: What is your budget model?
Pay only for actual risk found → CodeAnt AI
Fixed annual subscription regardless of findings → Pentera, NodeZero, Intruder, Astra
Credit-based flexibility → Cobalt, xBow
Variable per-engagement → HackerOne, Synack
The Question Every Penetration Testing Comparison Skips
What happens after a finding is confirmed?
Finding a vulnerability is the beginning, not the end. The most important question in evaluating any platform is what happens between "finding confirmed" and "finding verified as remediated."
CodeAnt AI: Unlimited retests included until every finding is confirmed remediated in the production environment. Re-engagement opens within 24 hours of fix deployment. The retest report is a standard deliverable, finding-by-finding verification status, production environment confirmation, remediation evidence. The data deletion certificate is issued on engagement close.
Pentera: Retesting available through the continuous validation model. Remediation tracking through Pentera Resolve (added via DevOcean acquisition). No separate retest report as a standard compliance deliverable.
NodeZero: Remediation verification available. No standard data deletion certificate.
xBow: Findings require manual remediation. No automated remediation workflow. No standard retest report structure for compliance evidence.
Cobalt: Retesting included in credit model. Real-time reporting and tester communication enable faster remediation cycles. SOC 2 reports may require post-processing for specific auditor requirements.
HackerOne/Synack: Retesting handled by researchers. Variable turnaround depending on researcher availability. Strong compliance reporting for major frameworks.
Intruder/Astra: Rescanning available. Not a retest report, a rescan confirming a CVE is no longer present. SOC 2 auditors do not treat scanner rescans as retest evidence for penetration test findings.
For more on the specific methodologies each platform uses, see AI penetration testing methodology. For pricing details by test type, see penetration testing cost. For SOC 2 evidence requirements, see SOC 2 penetration testing requirements.
The Complete Guide to AI Penetration Testing Platforms: What the Right Choice Actually Looks Like
The AI penetration testing market in 2026 is genuinely innovative across multiple categories.
NodeZero and Pentera have made internal network validation faster and more continuous than anything that existed five years ago.
xBow has demonstrated that AI-driven agents can outperform individual human researchers on public bug bounty leaderboards.
Cobalt and HackerOne have made human pentesting accessible at scales previously requiring large in-house security teams.
None of them do what CodeAnt AI does, because none of them start from the premise that the most accurate offensive testing comes from the platform that already understands your code.
The vulnerabilities that cause SaaS data breaches in 2026 are not the ones that show up in network scan reports. They are the authentication bypass buried in a middleware configuration that produces a 200 response to every external probe. The hardcoded credential in the JavaScript bundle every user downloads. The IDOR across your customer record dataset that requires knowing your data model to find systematically. The business logic gap in an authenticated workflow that no scanner has a signature for.
Finding those requires the combination of defensive code intelligence and offensive testing methodology that only a unified platform provides. The offensive engagement is deeper because it arrives already knowing what the defensive review has been flagging for months. The defensive review is more accurate because it is validated by what the offensive engagement confirms is actually exploitable.
That is the difference between buying a penetration testing tool and operating a security program.
→ Start with a free external scan from one URL. No payment until high or critical findings are confirmed. For full-spectrum coverage across black box, white box, and gray box with a complete SOC 2 evidence package, book a scoping call and testing begins within 24 hours.
FAQs
What penetration testing tools do security teams actually use in 2026?
Which penetration testing platform is best for SOC 2 compliance?
What is the difference between PTaaS and traditional penetration testing?
What is the difference between automated pentesting and a vulnerability scanner?
What is the best AI penetration testing platform in 2026?















