A 200-person SaaS company has usually outgrown basic security tools, but it may not yet have a large enterprise security team.
That is exactly where pentesting decisions become difficult.
At this stage, the company is shipping quickly, selling into larger customers, preparing for or maintaining SOC 2 Type 2, managing cloud infrastructure, expanding APIs, and handling more sensitive customer data. The security team needs proof that real risks are being found and fixed, but engineering cannot slow down every time security testing is needed.
That is why more teams are searching for the best pentest platform for a CISO at a 200-person SaaS company, and PTaaS providers with clear SLAs.
A traditional annual pentest may not be enough anymore.
A basic vulnerability scanner is not enough either.
A 200-person SaaS company needs a pentest platform that can connect five things:
Code security
External attack surface testing
Cloud infrastructure testing
Exploit validation
Compliance-ready evidence
The best platform is not the one with the longest feature list. It is the one that matches how a modern SaaS company builds, deploys, sells, and gets audited.
Why 200-Person SaaS Companies Need A Different Pentest Model
A 200-person SaaS company is in an awkward security stage.
It is no longer small enough to rely on ad hoc testing, but it may not be large enough to have a fully staffed internal red team, AppSec team, cloud security team, and compliance function.
Security responsibilities are often split across:
A CISO or security lead
A small security engineering team
Platform engineers
DevOps
Compliance or GRC
Product engineering managers
At the same time, the company is likely facing pressure from:
Enterprise customer security reviews
SOC 2 Type 2 audits
Vendor risk questionnaires
Cloud security reviews
Insurance requirements
Board-level risk visibility
Faster product release cycles
This is why the old model breaks.
A once-a-year pentest creates a report, but the product changes every week. A scanner creates alerts, but does not prove exploitability. A manual consulting engagement may find real issues, but retesting and turnaround can be slow.
A growing SaaS company needs a pentest model that is faster, more continuous, more evidence-driven, and more connected to engineering.
What A Pentest Platform Must Prove At This Stage
For a 200-person SaaS company, the key question is not:
“Did we run a pentest?”
The real question is:
“Can we prove what an attacker can actually exploit, and can we show that it was fixed?”
A strong pentest platform should help answer:
What assets are exposed externally?
Which APIs are accessible?
Can users access data across tenants?
Can roles be escalated?
Are cloud assets exposed?
Are secrets leaking through CI/CD or JavaScript bundles?
Are vulnerabilities confirmed with proof of exploit?
Can fixes be retested quickly?
Can evidence be shared with auditors and customers?
This is the difference between pentesting as a checkbox and pentesting as a security operating model.
For fast-growing SaaS teams, the second one matters more.
Why Traditional Pentesting Often Falls Short
Traditional pentesting is valuable, especially when performed by skilled testers. But the model often struggles with SaaS velocity.
Common issues include:
Testing happens once or twice per year
Scope is frozen before the product changes again
Reports arrive late
Retests cost extra or take too long
Findings are disconnected from code
Cloud infrastructure is partially scoped
Authenticated SaaS workflows are not deeply tested
Business logic risks are underexplored
Evidence is not mapped cleanly to SOC 2 or customer requirements
For a SaaS company with frequent deployments, this creates a visibility gap.
The team may pass an annual pentest but still introduce serious vulnerabilities afterward.
This is why many CISOs now evaluate AI penetration testing, automated penetration testing, and continuous pentest tools for CI/CD pipelines instead of relying only on point-in-time assessments.
AI Penetration Testing Vs Manual Pentesting For SaaS Companies
AI-powered pentesting and manual pentesting are not the same.
Manual pentesting depends on human testers, time-boxed scope, and expert investigation. It is strong for nuanced workflows, unusual business logic, and creative abuse cases.
AI penetration testing improves speed, repeatability, and coverage by using automation, code intelligence, reconnaissance, and exploit validation to test more continuously.
Manual pentesting is strong when
The workflow is highly custom
Human judgment is needed
Edge cases require creative reasoning
The scope is sensitive or complex
Manual confirmation is required
AI pentesting is strong when
The product changes frequently
The attack surface is large
CI/CD releases happen often
Cloud assets appear continuously
Exploit validation must be repeated
Retesting needs to be fast
SaaS workflows need ongoing coverage
The best answer is not AI versus manual.
The best answer is a platform that brings automation, AI-assisted validation, and human-grade methodology into one workflow.
For a 200-person SaaS company, speed and evidence matter. AI pentesting helps when it proves exploitability, not when it simply generates more alerts.
Key Features The Best SaaS Pentest Platform Should Have
CI/CD Integration
A modern SaaS pentest platform should integrate with the way engineering ships software.
That means support for:
GitHub
GitLab
Bitbucket
Jenkins
CircleCI
Azure DevOps
Buildkite
Jira or Linear
CI/CD integration matters because security issues should be detected close to the moment they are introduced.
If a new API route is deployed, a new cloud service becomes public, or an authentication workflow changes, testing should not wait until the next annual assessment.
Defensive Code Intelligence
For SaaS teams, many serious vulnerabilities originate in code.
A platform should be able to understand:
Authentication logic
Authorization checks
API routes
Tenant scoping
User-controlled input
Dangerous sinks
Secrets and configuration risks
Insecure framework patterns
This is the defensive side of security.
It helps prevent vulnerabilities before they ship.
But the real power comes when this same intelligence improves offensive testing.
External Attack Surface Testing
A SaaS company’s external attack surface usually includes:
Main web application
Public APIs
GraphQL endpoints
Staging subdomains
Admin portals
Documentation portals
Cloud-hosted assets
Object storage links
Authentication services
Marketing and support systems
Third-party integrations
The platform should continuously map what is exposed and identify new attack paths as the company grows.
Authenticated SaaS Workflow Testing
Most serious SaaS vulnerabilities appear after login.
A strong pentest platform should test across roles such as:
Free user
Paid user
Admin
Organization owner
Support agent
Read-only user
API token user
This is how testers find:
IDOR
Broken object-level authorization
Privilege escalation
Cross-tenant access
Business logic abuse
JWT manipulation
Role boundary failures
For B2B SaaS, this is one of the most important testing areas.
Cloud Infrastructure Coverage
A 200-person SaaS company is usually cloud-native.
The platform should test cloud exposure across:
AWS
Azure
GCP
Kubernetes
Object storage
IAM permissions
Public databases
Security groups
CI/CD secrets
Serverless functions
Metadata services
Cloud security cannot be separated from application security.
A leaked token in an app can expose cloud assets. A cloud permission can amplify an application bug. A public bucket can turn a low-risk workflow bug into a customer data incident.
Exploit Validation
The platform must prove real risk.
A useful finding should include:
Affected endpoint
User role used
Request payload
Proof of exploit
Data accessed
Business impact
Root cause
Remediation steps
Retest status
Without proof, findings become arguments.
With proof, engineering teams can fix faster.
Retesting And Fix Verification
Retesting should not be treated as an afterthought.
A growing SaaS company needs fast verification because unresolved findings can block:
SOC 2 audits
Customer security reviews
Enterprise deals
Production releases
Internal risk approvals
A good platform should make retesting clear, fast, and included in the workflow.
Compliance-Ready Evidence
For SOC 2 Type 2, security evidence matters.
A pentest platform should provide:
Finding details
Proof of exploit
Timeline of remediation
Retest confirmation
Severity rationale
Control mapping
Evidence export
Final report package
The report should help security, engineering, auditors, and customers understand what happened and what was fixed.
Which Pentesting Vendors Offer 48-Hour Delivery?
Many fast-growing SaaS teams ask which pentesting vendors offer 48-hour delivery.
But the better question is:
“What is delivered in 48 hours?”
A 48-hour scanner report is not the same as a 48-hour pentest result.
Fast delivery is valuable only if it includes:
Validated findings
Proof of exploit
Clear severity
Reproduction steps
Business impact
Remediation guidance
Retesting path
For a 200-person SaaS company, speed matters when:
A deal is blocked by a customer security review
A SOC 2 evidence request is urgent
A new release needs validation
A critical exposure needs confirmation
A fix needs rapid retesting
Fast delivery is useful, but only when paired with real validation.
What SLAs Should A SaaS Pentest Platform Guarantee?
A good SaaS pentest platform should define clear SLAs.
Ask about:
Time to kickoff
Time to first finding
Critical finding notification
Full report delivery
Retest turnaround
Evidence delivery
Support response time
Remediation verification
For SaaS CISOs, retesting SLA is often the most important.
Finding a vulnerability is not enough. The security team needs to prove the fix worked.
A strong retesting SLA keeps remediation moving and helps avoid audit delays.
What “No Critical Findings, No Payment” Means
Some pentest providers use outcome-based pricing models such as no critical findings, no payment.
This can be attractive because it aligns vendor incentives with finding real risk.
But buyers should evaluate it carefully.
The agreement should clearly define:
What counts as critical
Whether exploit chains count
How CVSS is calculated
What proof is required
Whether high findings are included
Whether low and medium findings are still reported
Whether retesting is included
How disputes are handled
The model can work well when the methodology is deep and transparent.
But it should never reward exaggerating severity or ignoring non-critical findings that still matter.
For SaaS companies, the best version of this model focuses on validated, business-impacting risk.
Where CodeAnt AI Fits For A 200-Person SaaS Company
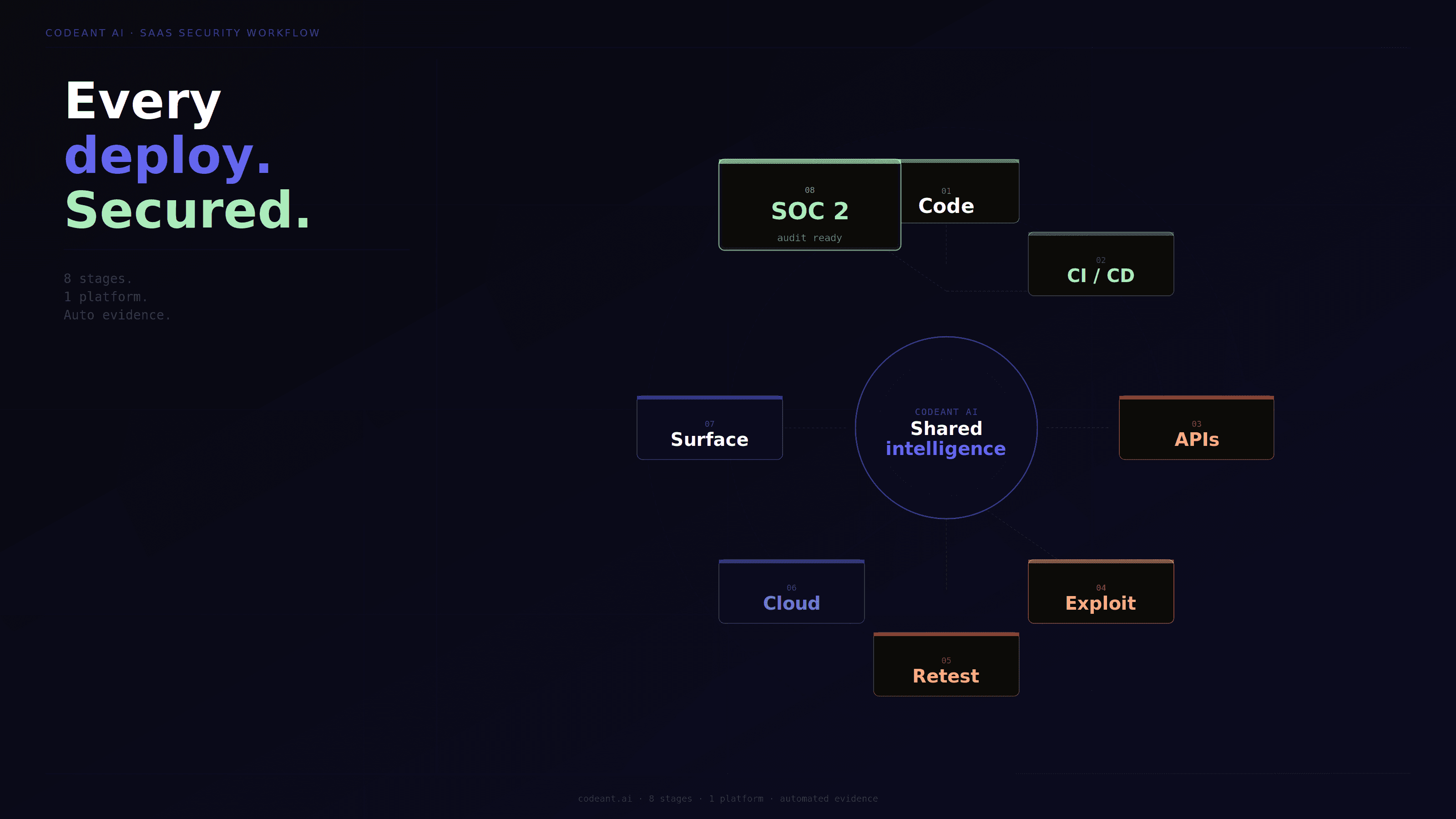
CodeAnt AI is a complete, agent-based defensive and offensive security platform.
This matters because a 200-person SaaS company needs both sides.
On the defensive side, CodeAnt integrates into CLI, IDEs, pull requests, and CI/CD pipelines. It helps developers fix security and quality issues as they write and commit code. It reviews the codebase for insecure patterns, risky APIs, authentication issues, and quality problems before they become production vulnerabilities.
On the offensive side, CodeAnt maps the public exposure of the application and tests it like an adversary would. It performs external reconnaissance, reads source code, learns from defensive analysis, runs gray box testing with code context, and constructs exploit chains.
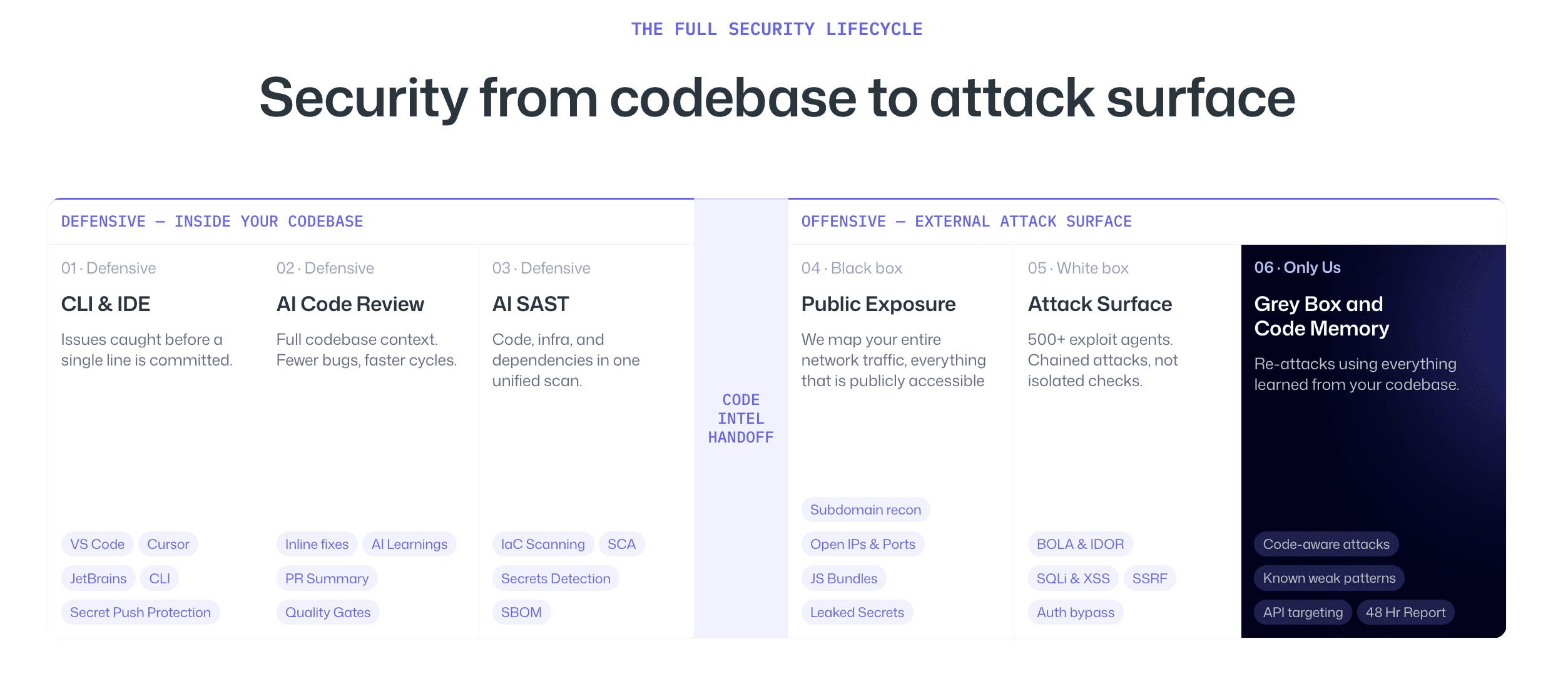
The core differentiator is simple:
The same platform that reviews your code for insecure patterns in CI/CD is the one conducting reconnaissance against your external surface, testing from the outside with inside knowledge.
That is especially valuable for SaaS companies because real attacks often move across code, APIs, cloud assets, identities, and authenticated workflows.
Most tools see only part of that picture. CodeAnt AI connects the parts.
Best Pentest Platform Decision Framework For SaaS CISOs
Use this framework when evaluating platforms.
If Your Biggest Risk Is | Look For |
|---|---|
Fast engineering velocity | CI/CD integration and continuous testing |
SOC 2 Type 2 readiness | Evidence packages, retesting, and control mapping |
SaaS authorization bugs | Authenticated gray box testing |
Cloud exposure | AWS, Azure, GCP, Kubernetes, and storage testing |
Customer security reviews | Proof of exploit and executive-ready reports |
Limited security headcount | Automation plus clear remediation guidance |
Repeat vulnerabilities | Defensive and offensive feedback loop |
Enterprise sales pressure | Fast delivery and retest SLAs |
The best platform is the one that matches your real risk surface.
Not every company needs the same tool.
But most 200-person SaaS companies need more than a basic scan or a once-a-year manual test.
Checklist: How To Choose A Pentest Platform For A 200-Person SaaS Company
Before choosing a vendor, ask:
Does it support AI penetration testing?
Does it support automated penetration testing?
Does it integrate with CI/CD?
Does it test authenticated SaaS workflows?
Does it test APIs and GraphQL?
Does it test cloud infrastructure?
Does it validate exploitability?
Does it provide proof of exploit?
Does it include retesting?
Does it define clear SLAs?
Does it support SOC 2 evidence?
Does it help prevent repeat vulnerabilities?
Does it combine defensive and offensive security?
If the platform cannot answer these, it may still be useful, but it may not be the right primary pentest platform for a scaling SaaS company.
Common Mistakes When Choosing A SaaS Pentest Vendor
Choosing based only on price
Cheaper testing can be useful for narrow scopes, but price alone does not tell you whether the vendor will find real risk.
A low-cost report that misses tenant isolation flaws, authentication bypasses, and cloud exposure can become expensive later.
Choosing based only on brand
A well-known vendor may be strong, but the fit still depends on your environment.
Ask whether they understand SaaS workflows, CI/CD velocity, cloud infrastructure, and SOC 2 evidence requirements.
Confusing scanning with pentesting
A scanner can identify potential issues.
Pentesting should validate whether those issues can actually be exploited.
Do not accept scanner output as a substitute for proof.
Ignoring retesting
A report without retesting leaves the most important question unanswered.
Was the risk actually fixed?
Separating code security from offensive testing
If code review and pentesting are disconnected, the same vulnerability classes may keep reappearing.
A better model feeds offensive findings back into defensive prevention.
Conclusion: Choose A Pentest Platform That Matches SaaS Speed
A 200-person SaaS company needs a pentest platform that can keep up with how the business actually operates.
That means fast testing, real exploit validation, authenticated SaaS workflow coverage, cloud infrastructure testing, retesting, and SOC 2-ready evidence.
But the strongest platforms go one step further.
They do not only find vulnerabilities after deployment. They help prevent them before they ship.
That is where CodeAnt AI’s defensive plus offensive model fits especially well. It reviews code in CI/CD, tests the external attack surface with code intelligence, validates exploit chains, and helps teams fix the root cause.
For a SaaS CISO, the right question is not just which vendor can run a pentest.
The better question is:
Can this platform prove what attackers can exploit, verify that fixes worked, and reduce the chance of the same issue shipping again?
That is the standard a growing SaaS company should use.
FAQs
What Is The Best Pentest Platform For A 200-Person SaaS Company?
What Should A SaaS CISO Look For In A Pentest Platform?
Which Pentesting Vendors Offer 48-Hour Delivery?
How Does AI-Powered Pentesting Help Fast-Growing SaaS Startups?
Do SaaS Companies Need Continuous Pentesting Or Annual Pentesting?