Two different security problems. Two different platforms…
When security teams evaluate Pentera against CodeAnt AI, they are often comparing automated penetration testing tools that are solving genuinely different problems, and choosing the wrong one for their actual situation.
Pentera is an automated security validation platform built for enterprise internal network testing. It answers one question with remarkable efficiency: do your internal security controls, firewalls, endpoint detection, Active Directory policies, credential management, hold up when an adversary is already inside the perimeter? It simulates lateral movement, privilege escalation, and credential attacks across internal infrastructure continuously and at scale.
CodeAnt AI is a defensive and offensive security platform built for SaaS teams. It answers a different question: what can an adversary do to your application, your APIs, your cloud infrastructure, and your codebase, whether they are approaching from the outside with no prior access, exploiting your application as a legitimate user, or reading your source code after obtaining repository access? And it does this on both sides simultaneously, the same platform that reviews your code for insecure patterns in CI/CD is the one conducting external reconnaissance and exploit chain construction.
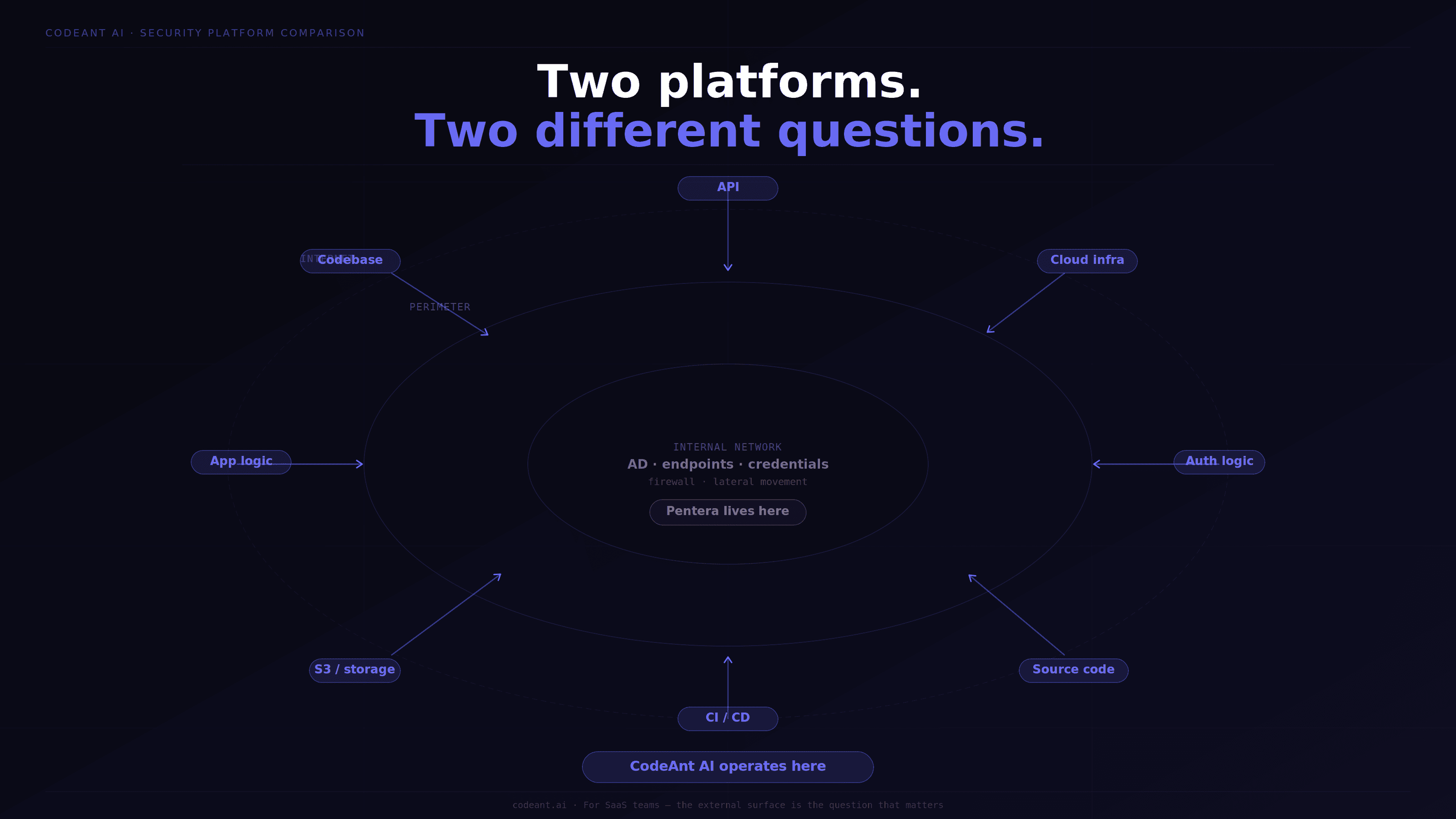
Neither platform makes the other irrelevant. But for most SaaS teams, particularly those handling customer data, preparing for SOC 2, or shipping code on a continuous deployment cadence, the security question that matters most is not whether internal controls block lateral movement. It is whether the application, the API, the cloud storage, and the authentication logic are exploitable from the outside.
This comparison covers what each platform actually does, where each structurally cannot go, how pricing compares, what compliance auditors accept from each, and which fits which security program.
What Pentera Actually Does
Pentera's core product is automated security validation focused on internal network infrastructure. It deploys an agent inside your network perimeter and continuously simulates what an adversary with internal access would do:
credential sniffing and cracking
lateral movement across network segments
Active Directory attack paths
privilege escalation through misconfigured internal services
ransomware resilience testing
Pentera has expanded into cloud testing (Pentera Cloud for AWS and Azure) and surface testing (Pentera Surface for external attack surface monitoring). These are meaningful additions. But the core architectural identity remains internal network validation, which is where the platform was built, where its methodology is deepest, and where the findings are most reliable.
Where Pentera structurally cannot go:
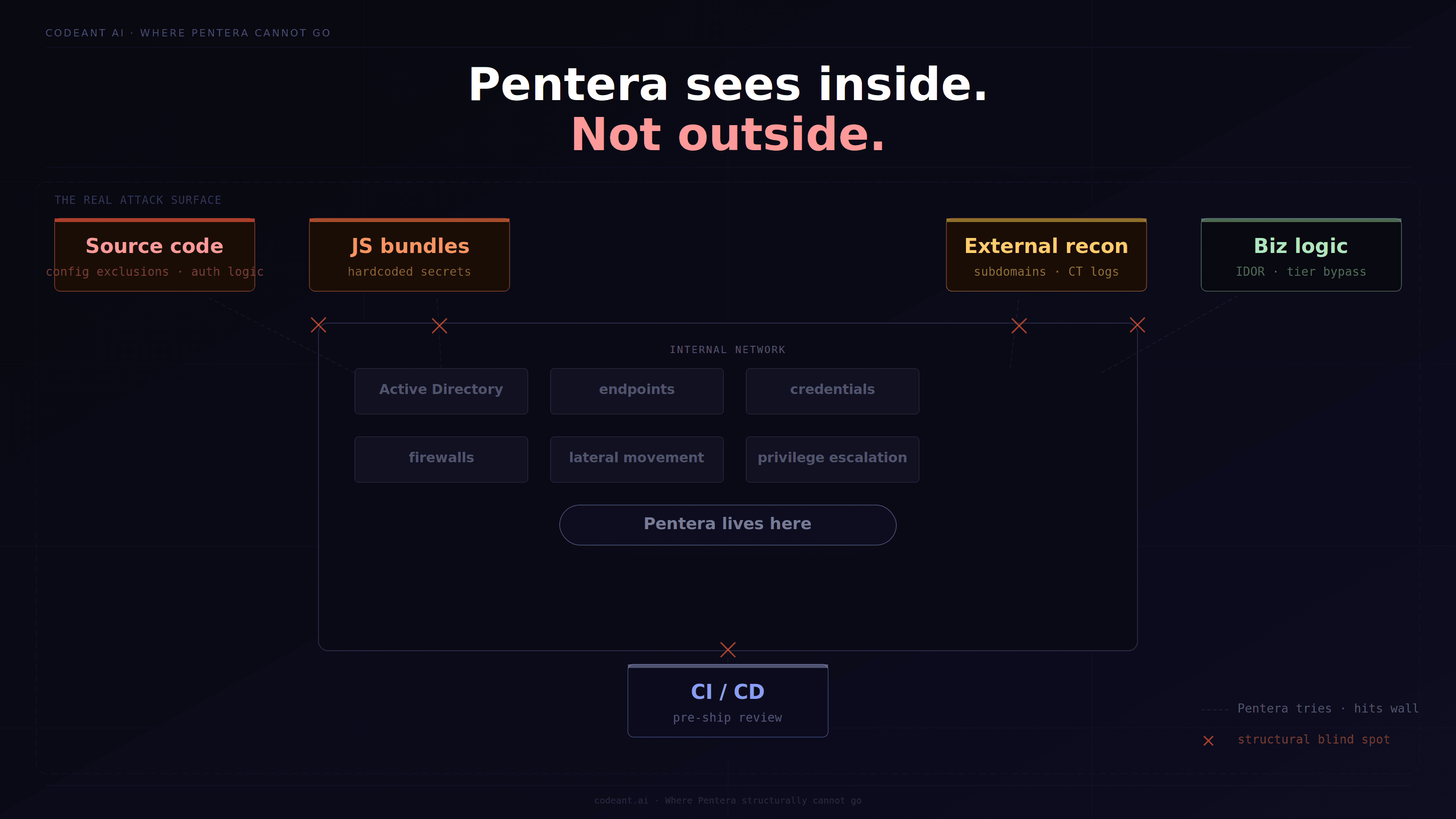
Based on G2 reviews, Gartner feedback, and verified product documentation, these are Pentera's confirmed limitations for SaaS application security:
No white box source code analysis. Pentera does not read your source code, trace data flows, or find authentication configuration vulnerabilities that produce no anomalous external signal. A Spring Security filter chain that excludes
/api/v2/**from all security filters produces a 200 response to unauthenticated requests, and Pentera flags it because the endpoint returns data without credentials. But it cannot tell you the root cause is a configuration exclusion, what other endpoints are affected by the same pattern, or provide a remediation diff. That requires reading the code.No JavaScript bundle analysis. Modern SaaS applications ship megabytes of compiled JavaScript that routinely contains hardcoded API keys, internal endpoint references, and infrastructure information. Pentera does not download and analyze JS bundles as part of its methodology.
No gray box business logic testing. Pentera tests whether your internal controls block lateral movement. It does not test whether a free-tier user in your SaaS application can call premium endpoints directly, whether IDOR vulnerabilities exist across your customer record dataset, or whether your checkout workflow can be bypassed by calling the confirmation endpoint directly. These require authenticated testing with understanding of the application's intended behavior.
Limited black box external coverage. Multiple G2 and Gartner reviewers note that Pentera's external testing capability is limited compared to its internal network depth. One Gartner review notes directly: "you are limited to specific testing scenarios where you will be triggering a blackbox, greybox or a small number of more specific tests." External attack surface reconnaissance, subdomain enumeration, CT log queries, cloud asset discovery, JS bundle analysis, is not Pentera's core methodology.
No defensive code review integration. Pentera is an offensive-only platform. It does not review pull requests, flag insecure patterns in CI/CD pipelines, or maintain a continuous record of security decisions across the development process. The defensive half of the security program, catching vulnerabilities before they ship, requires a separate tool.
What CodeAnt AI Actually Does
CodeAnt AI operates as a unified defensive and offensive security platform the only platform in this comparison where both functions share the same code intelligence.
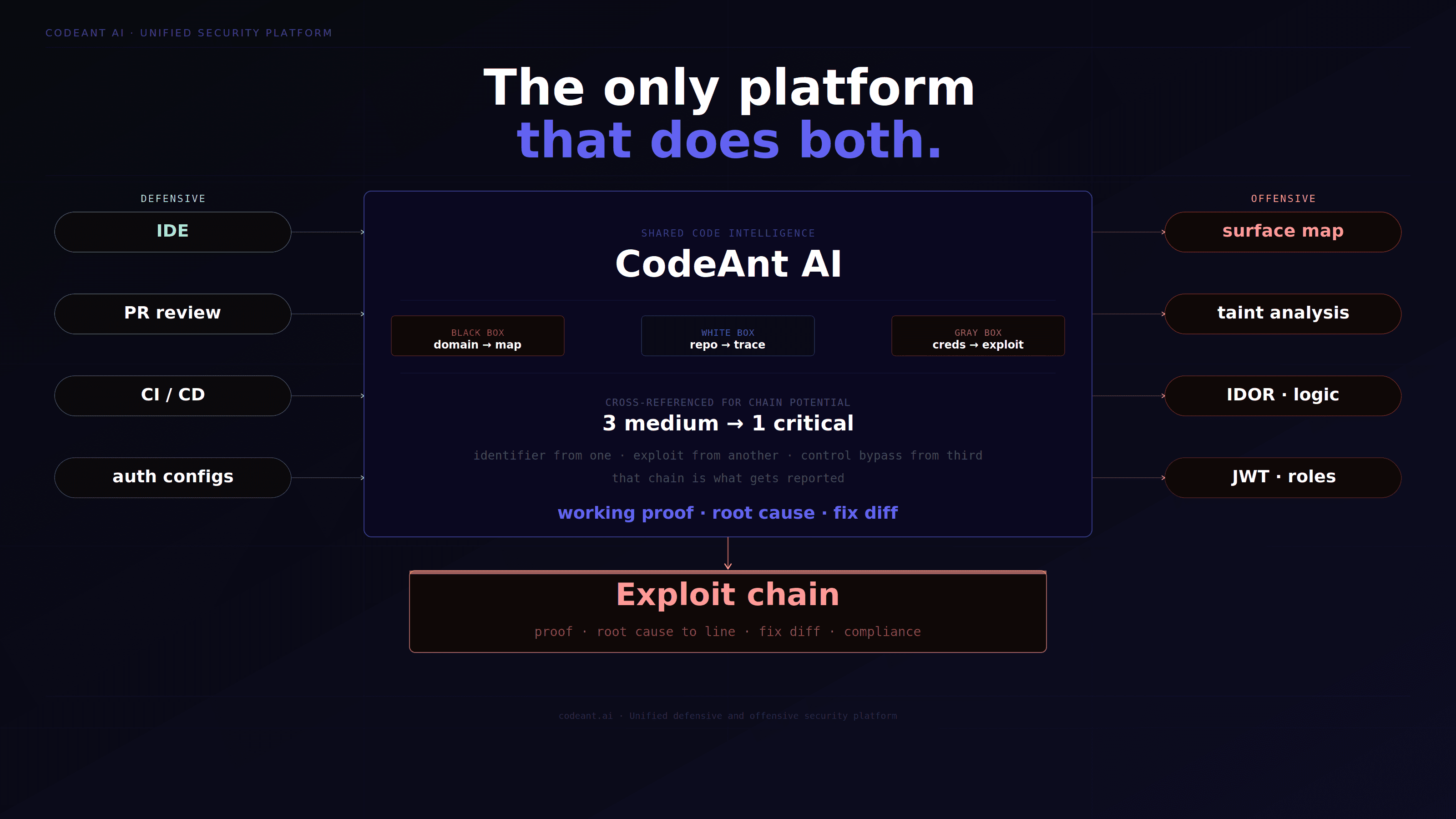
On the defensive side, it integrates from the IDE through CI/CD pipelines, reviewing every pull request for insecure patterns in full codebase context:
authentication configurations
data flow to dangerous sinks
insecure API patterns
dependency vulnerabilities
The same intelligence that flags a Spring Security misconfiguration in a pull request is the intelligence that informs the offensive engagement.
On the offensive side, it conducts full-spectrum automated penetration testing across three parallel tracks:
Black box track
Starting from a domain name only. External surface mapping via DNS enumeration across 150+ subdomain patterns, Certificate Transparency log queries, full TCP port scanning, cloud asset enumeration (S3, Azure Blob, GCP, exposed CI/CD dashboards), and JavaScript bundle analysis extracting hardcoded secrets and internal endpoints. Every endpoint discovered is tested unauthenticated with the full battery of authentication bypass patterns.
White box track
With read-only repository access. Every authentication configuration read end-to-end. Every user-controlled input traced to every dangerous sink (raw SQL queries, shell commands, template rendering, file operations). Every configuration file scanned for secrets. Git history scanned for historical credentials, including ones committed and deleted that remain recoverable from version control.
Gray box track
With test credentials for each user role. Systematic IDOR testing across every identifier-accepting endpoint. Privilege escalation testing on every admin endpoint with standard user credentials. JWT manipulation testing for signature validation failures. Business logic testing across every critical workflow, step-bypass attacks, concurrent request race conditions, subscription tier abuse, price manipulation.
Every finding from every track is cross-referenced for chain potential. Three medium findings that individually get deprioritized combine into a critical chain when one provides the identifier another needs to exploit, and the third removes the final access control. That chain is what gets reported, with working proof-of-exploit, root cause to file and line, a remediation diff, and compliance mapping to specific TSC control IDs.
Feature Comparison of Best AI Penetration Testing Tool: CodeAnt AI vs Pentera
Feature | CodeAnt AI | Pentera |
|---|---|---|
Pricing model | Free for low and medium findings. Pay only when high or critical issues are confirmed. | ~$46,000–$50,000/year subscription. Billed regardless of findings. |
Incentive alignment | Only paid when serious vulnerabilities are found. Every hour spent is directed at finding your worst vulnerability. | Paid per subscription regardless of severity or volume of findings confirmed. |
Time to first finding | First critical finding typically within 24 hours. Full report within 48 hours. | Results delivered over days to weeks depending on engagement scope. |
Black box external testing | Full methodology: subdomain enumeration, CT logs, cloud assets, JS bundle analysis, unauthenticated endpoint testing, CORS testing, exploit chaining. | Limited. Gartner reviewers note testing is constrained to specific scenarios. Pentera Surface covers external attack surface monitoring. |
White box source code analysis | Yes — full dataflow tracing, authentication configuration analysis, Git history scanning, secrets in config files. Root cause to file and line. | No. Not a capability of the platform. |
Gray box authenticated testing | Yes, systematic IDOR, privilege escalation, JWT manipulation, business logic testing across all role boundaries. | Limited. Focuses on internal network lateral movement, not application-layer authenticated flows. |
JavaScript bundle analysis | Yes, 30+ secret pattern types, live verification of every confirmed secret, staging vs. production comparison. | No. Not part of the methodology. |
Attack chain construction | Every engagement produces multi-step chains. Three to four vulnerabilities chained to show the actual breach path. Example: open Cognito signup → admin panel → production database → 476K patient records. | Attack path visualization for internal network lateral movement. Not cross-track chain construction. |
Defensive code review | Yes, IDE integration, PR review, CI/CD pipeline gates. Same platform as offensive testing. | No. Offensive-only platform. |
Proof-of-exploit per finding | Yes, exact endpoint, HTTP method, parameter, working curl command, before and after code fix. | Validated attack paths with remediation priority. Finding format less granular at code level. |
Root cause to file and line | Yes, specific file, class, method, line number for every code-level finding. | No, network and infrastructure findings, not code-level root cause. |
Retest | Unlimited retests included. Re-engagement opens within 24 hours of fix deployment. | Retesting available. Included in subscription. |
SOC 2 evidence package | Complete: retest report, timeline documentation, data deletion certificate, compliance mapping to specific TSC control IDs (CC6.1, CC6.6, CC7.1). | Compliance reporting available. Does not include data deletion certificate as standard. Mapping is less granular on application-layer controls. |
Regulatory penalty mapping | Yes, estimated regulatory penalty exposure per finding across SOC 2, ISO 27001, HIPAA, GDPR, PCI-DSS, Cert-In. | No per-finding penalty mapping. |
Researcher track record | 87 published CVEs. VulnCheck CNA partner. CVSS 10.0 (CVE-2026-29000) and CVSS 9.8 (CVE-2026-28292) on public record. MSRC submissions at CVSS 9.8 and 9.1. | Not publicly disclosed. |
Throughput | 15–20 full engagements per week. AI-powered, not headcount-constrained. | Continuous validation within customer environments. Scale varies by deployment. |
Internal network testing | Not the primary focus. External, application, and cloud attack surface. | Core strength. Internal network, Active Directory, credential management, lateral movement. |
Deployment model | No deployment required. Testing begins from a domain name within 24 hours of engagement start. | Requires on-premises agent deployment. Initial setup takes hours to days. |
What Each Penetration Testing Platform Would Find on the Same Target
This is the most direct way to understand the difference. On a typical SaaS application, here is what each platform would and would not find:
Scenario: SaaS application running on AWS, React frontend, Node.js API, multi-tenant data model
Finding type | CodeAnt AI | Pentera |
|---|---|---|
Hardcoded Stripe live key in JS bundle | ✅ Found, JS bundle analysis, key verified live against Stripe API | ❌ Not found, not in methodology |
Express.js middleware ordering bypass (admin routes registered before auth middleware) | ✅ Found, white box reads routing configuration | ❌ Not found, produces normal 200 response externally |
IDOR across customer record dataset | ✅ Found, gray box systematic IDOR enumeration | ❌ Not found, requires authenticated application testing |
S3 bucket with public read access containing customer exports | ✅ Found, cloud asset enumeration | ✅ Found, Pentera Surface covers this |
Cross-tenant data access via IDOR chain | ✅ Found, gray box + chain construction | ❌ Not found, application layer, not network layer |
Exposed Jenkins dashboard with default credentials | ✅ Found, external recon | ✅ Found, Pentera Surface or internal scan |
Internal Active Directory lateral movement path | ❌ Not primary focus | ✅ Found, core Pentera strength |
Credential sniffing on internal network | ❌ Not in scope | ✅ Found, core Pentera strength |
Ransomware resilience validation | ❌ Not in scope | ✅ Found, Pentera Ransomware Readiness module |
JWT signature validation failure | ✅ Found, gray box auth testing | ❌ Not found, application-layer auth testing |
Secrets in Git history (deleted credentials still recoverable) | ✅ Found, white box Git history scan | ❌ Not found, requires repository access |
SQL injection via dataflow trace | ✅ Found, white box dataflow analysis | ❌ Not found, network-layer platform |
Pricing of Penetration Testing Tools: What You Actually Pay
Pentera: Subscription-based, approximately $46,000–$50,000 per year based on Gartner and G2 analyst data. Priced for large enterprise environments. Requires on-premises agent deployment. The subscription covers continuous testing within the deployed environment.
CodeAnt AI: Low and medium severity findings are free. You only pay when high or critical issues are confirmed. This aligns engagement cost directly with actual risk discovered. The firm that only gets paid when it finds serious vulnerabilities has a structural incentive to look harder, every engagement hour is directed at finding your worst vulnerability, not at billing you for a scan that returns nothing critical.
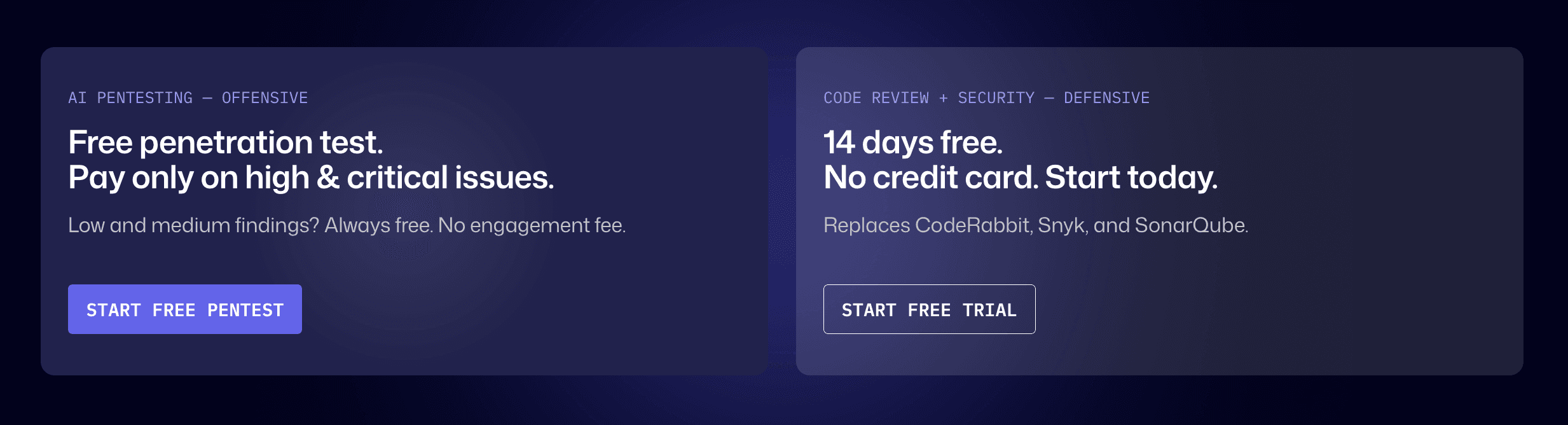
Unlimited retests are included at no additional cost until every confirmed finding is verified remediated in the production environment. The complete SOC 2 evidence package, retest report, timeline documentation, data deletion certificate, compliance mapping, is a standard deliverable on every engagement.
SOC 2 Compliance: What Auditors Accept from Each
For SaaS teams preparing for SOC 2 Type II, this section is what actually determines which platform satisfies the audit.
What SOC 2 Type II auditors require for CC7.1:
Working proof-of-exploit per finding (not scanner output, confirmed exploitation)
Findings mapped to specific TSC control IDs (CC6.1, CC6.6, CC7.1, not generic "SOC 2" references)
Retest report confirming verification in the production environment
Timeline documentation (discovery date, remediation date, verification date per finding)
Data deletion certificate confirming test data destroyed after engagement
CodeAnt AI produces all five as standard engagement deliverables. The compliance mapping goes to specific control IDs. The data deletion certificate is issued on every engagement close.
Pentera produces strong compliance reporting for internal network controls. Its coverage of CC6.6 (external threat protection) is limited by the platform's external testing depth, and CC6.1 application-layer authentication controls are outside its core methodology. The data deletion certificate is not a standard Pentera deliverable. For SaaS teams needing application-layer evidence for SOC 2, IDOR, authentication bypass, business logic vulnerabilities, a Pentera report alone will create audit gaps that require supplementation.
For the complete SOC 2 evidence package requirements, see SOC 2 penetration testing requirements.
Who Should Choose Pentera
Pentera is the right choice when your primary security concern is internal network resilience and enterprise infrastructure validation. Specifically:
Large enterprise environments with complex internal network infrastructure, Active Directory domains, many internal services, complex lateral movement paths, where continuous internal validation produces measurable risk reduction. Organizations that need to prove to a security operations team that ransomware would be blocked, that credential attacks would be detected, and that lateral movement is contained.
Organizations that already have a strong application security program covering web application testing, source code review, and cloud security, and need to add the internal network layer to complete their security posture.
Security teams with the budget for a ~$50,000/year subscription and the infrastructure team to manage on-premises agent deployment.
Who Should Choose CodeAnt AI
CodeAnt AI is the right choice when your primary attack surface is a SaaS application handling customer data, your team ships code continuously, and your security requirements include both the offensive validation that compliance frameworks require and the defensive coverage that prevents vulnerabilities from shipping in the first place. Specifically:
SaaS teams preparing for SOC 2 Type I or II who need working proof-of-exploit per finding, a formal retest report, and compliance-mapped evidence without paying for findings that turn out to be low severity. Engineering teams that want the defensive and offensive security programs on the same platform, where the code intelligence from PR reviews informs what the penetration testing targets, and the offensive findings calibrate what the defensive review flags.
Teams that need 48-hour report turnaround rather than weeks-long engagements. Teams where the pricing model, paying only for high and critical findings, aligns security testing cost with actual risk discovered rather than time spent.
Choose Automated Penetration Testing Based on Your Actual Risk Surface
Pentera and CodeAnt AI are both strong platforms, but they answer fundamentally different security questions.
Pentera focuses on internal network validation. It tests whether an attacker already inside your environment can move laterally, escalate privileges, and bypass infrastructure controls.
CodeAnt AI focuses on what most SaaS teams are exposed to every day — whether your application, APIs, cloud assets, and authentication logic can be exploited from the outside or by a legitimate user.
That distinction matters.
Because most real-world breaches in SaaS environments do not start with internal lateral movement. They start with application-layer vulnerabilities, authentication bypasses, and exposed cloud assets.
This is where modern AI penetration testing go beyond traditional validation.
CodeAnt does not just test controls. It finds, validates, and chains real vulnerabilities across your entire stack.
👉 If you want to move beyond validation and understand what an attacker can actually do to your system, start by evaluating your external and application attack surface the way it will be tested in the real world.
→ Start with a free external scan from one URL. We show you what is visible from the public internet, JS bundle secrets, exposed endpoints, cloud misconfigurations, before any payment is required.
For a full-spectrum engagement covering black box, white box, and gray box testing with a complete SOC 2 evidence package, book a scoping call and testing begins within 24 hours.
FAQs
What is a Pentera alternative for SaaS companies?
How much does Pentera cost compared to CodeAnt AI?
Is Pentera good for SOC 2 compliance?
Can Pentera find web application vulnerabilities?
What is the difference between CodeAnt AI and Pentera?















