A 48-hour pentest sounds attractive when a customer security review is blocking a deal, a SOC 2 audit needs evidence, or a production release needs fast validation.
But here is the catch.
Not every vendor promising fast delivery is delivering the same thing.
Some deliver a scanner report. Some deliver a lightweight vulnerability assessment. Some deliver a human-reviewed PTaaS report. Some deliver validated proof-of-exploit findings with remediation guidance and a retesting path.
Those are very different outcomes.
So the real question is not only which pentesting vendors offer 48-hour delivery.
The better question is:
What should a 48-hour pentest actually include to be useful for security, engineering, compliance, and customer trust?
For modern SaaS teams, fast delivery only matters if the output is accurate, exploitable, and actionable. A fast report full of unvalidated findings creates noise. A fast report with confirmed exploit paths helps teams fix real risk quickly.
This guide explains what 48-hour pentest delivery means, when it makes sense, what to ask vendors, and how AI penetration testing and automated penetration testing can reduce turnaround time without turning pentesting into shallow scanning.

What 48-Hour Pentest Delivery Actually Means
48-hour delivery does not always mean the same thing across vendors.
In some cases, it means the vendor can start testing within 48 hours. In other cases, it means initial findings are delivered within 48 hours. Some vendors use it to describe a complete report turnaround for a narrow scope.
Before choosing a provider, clarify which version they mean.
A real 48-hour pentest delivery model should define:
Time to kickoff
Time to first validated finding
Time to critical alert
Time to full report
Time to retest after remediation
Time to final evidence package
For a security team, these timelines matter differently.
A critical vulnerability should not wait for the final report. If a vendor confirms an authentication bypass, exposed customer data, or cloud credential leak, the team should receive immediate notification.
The full report can follow.
This is the difference between fast communication and rushed reporting.
When A 48-Hour Pentest Makes Sense
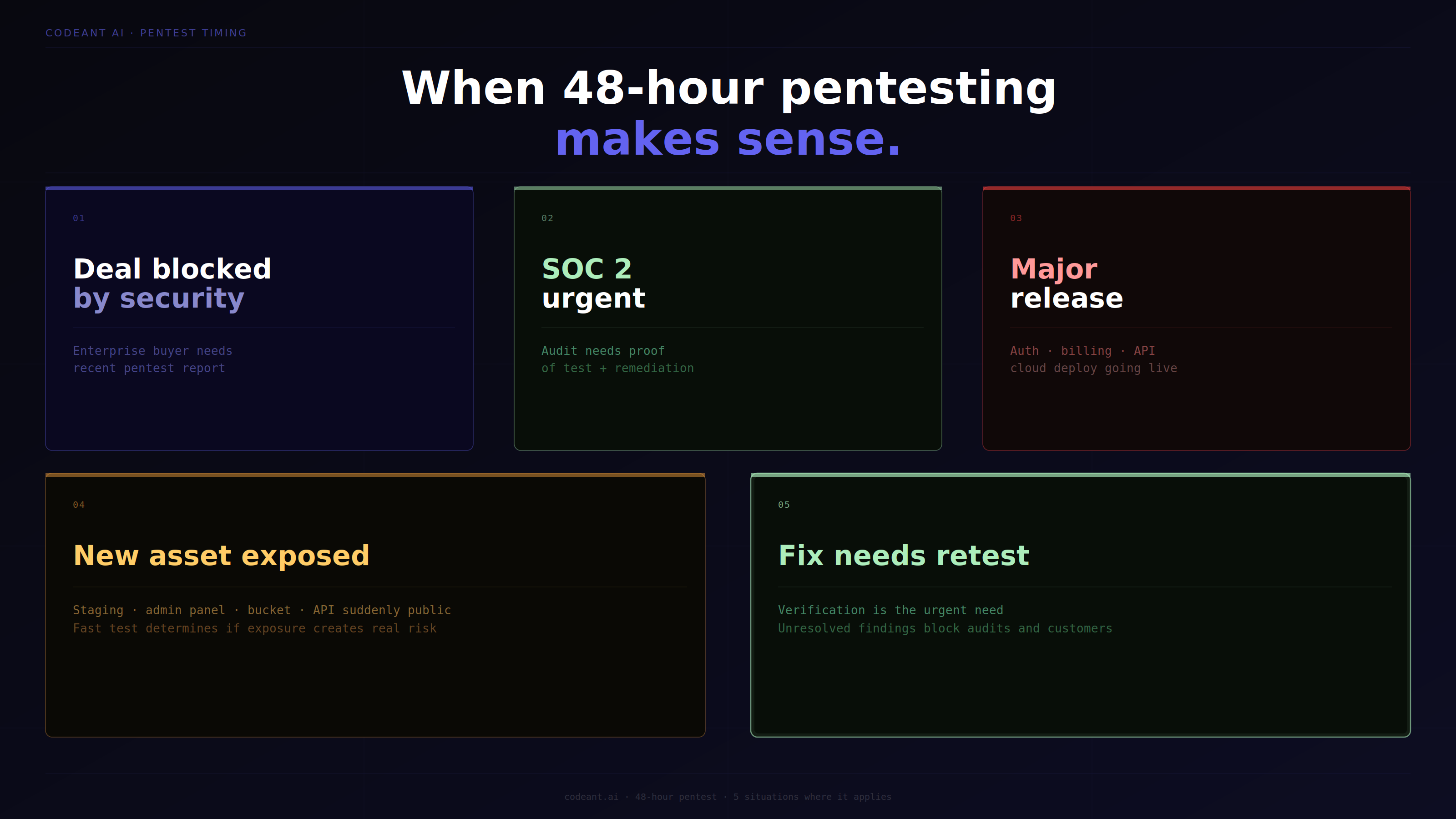
A rapid pentest is not always the right model. Some systems need deeper testing over a longer period.
But 48-hour pentesting can be very useful in specific situations.
Customer security review is blocking a deal
Enterprise buyers often ask for recent pentest evidence before signing.
If the company does not have a recent report, a 48-hour pentest can help unblock procurement. But the report must include credible scope, methodology, findings, remediation status, and retest plans.
SOC 2 evidence is urgently needed
A SaaS team preparing for SOC 2 may need to show that penetration testing was performed and that findings were addressed.
A fast pentest can support the audit, especially when paired with proof-of-exploit and retesting evidence.
A major release needs security validation
If a new authentication flow, billing workflow, API gateway, or cloud deployment is going live, a rapid test can validate the highest-risk areas before or immediately after launch.
A new external asset was exposed
If a staging app, admin panel, storage bucket, API, or cloud service becomes public, fast testing can determine whether the exposure creates real risk.
A fix needs retest confirmation
Sometimes the urgent need is not initial testing. It is verification.
A 48-hour retest SLA may be more valuable than a 48-hour first report because unresolved findings often block audits and customer approvals.
What A Fast Pentest Should Include
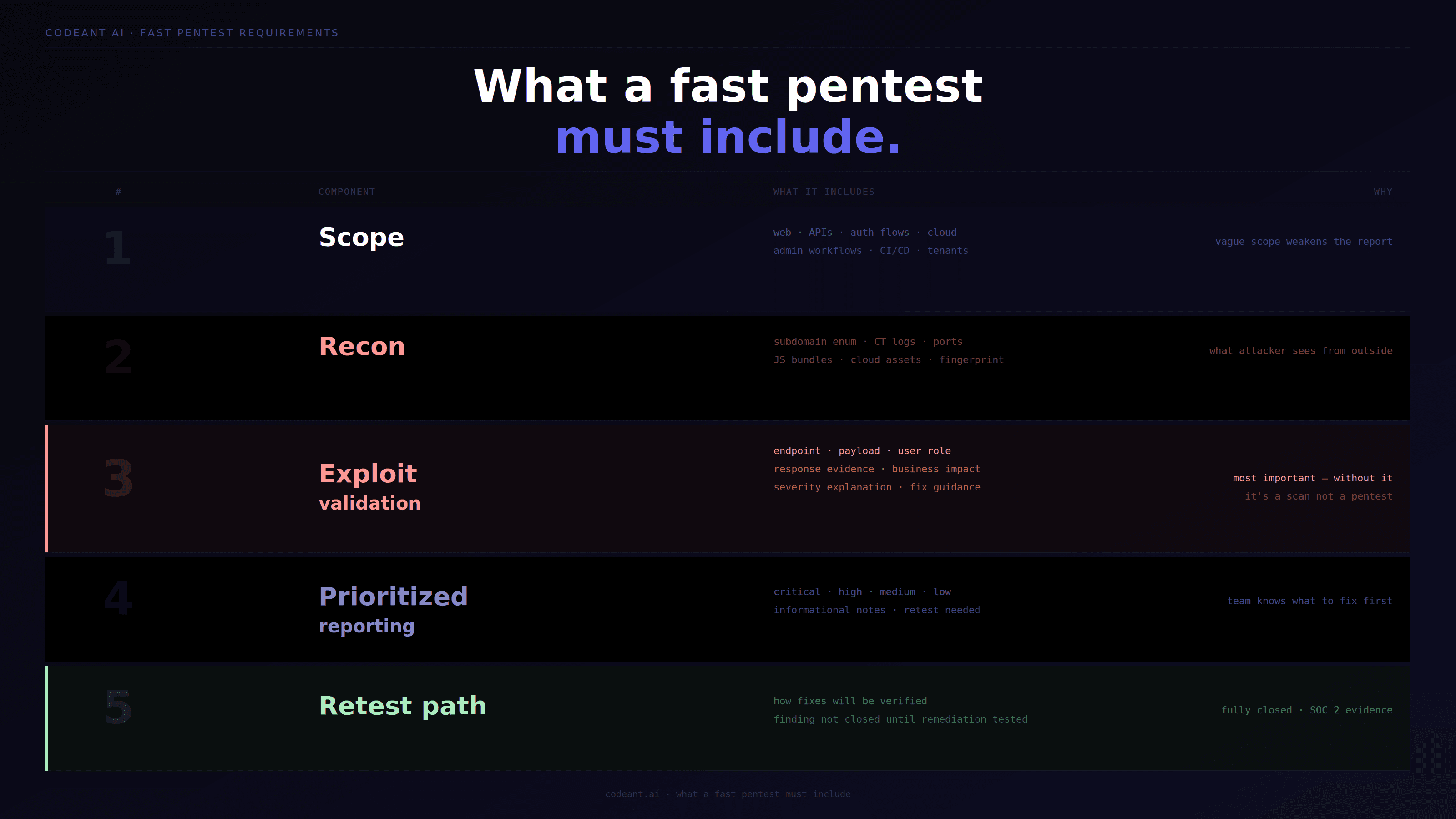
A fast pentest should not mean a thin pentest.
Even under a compressed timeline, the vendor should provide evidence that the testing was meaningful.
Clear scope
The vendor should define what was tested.
This may include:
Web application
APIs
Authentication flows
Cloud assets
External attack surface
Specific release changes
Admin workflows
Tenant boundaries
CI/CD exposure
A vague scope weakens the value of the report.
Reconnaissance
Even a 48-hour pentest should include reconnaissance.
For external testing, this may involve:
Subdomain discovery
Certificate Transparency review
Public port exposure
API endpoint discovery
JavaScript bundle analysis
Public cloud asset discovery
Technology fingerprinting
Reconnaissance helps testers understand what an attacker can see from outside.
Exploit validation
This is the most important part.
The vendor should confirm whether findings are exploitable.
A useful finding should include:
Affected endpoint
Request method
User role used
Payload or test condition
Response evidence
Business impact
Severity explanation
Remediation guidance
Without exploit validation, the report may be closer to a scan than a pentest.
Prioritized reporting
Fast pentest reports should not bury security teams in noise.
They should clearly separate:
Critical findings
High findings
Medium findings
Low findings
Informational observations
Retest requirements
A fast report is useful only when the team knows what to fix first.
Retesting path
The vendor should explain how fixes will be verified.
A finding is not fully closed until remediation is tested.
What A 48-Hour Pentest Should Not Be
A 48-hour pentest should not be a rebranded scanner export.
Scanner reports can be useful, but they are not the same as penetration testing.
Watch out for vendors that only provide:
Long CVE lists without proof
Generic severity scores
No affected user role
No reproduction steps
No business impact
No retesting workflow
No explanation of exploitability
No evidence safe enough for auditors
If the vendor cannot prove what was exploitable, the report may not satisfy engineering, customers, or compliance teams.
Fast does not mean shallow.
Fast should mean focused.
How AI Penetration Testing Enables Faster Delivery
AI penetration testing can reduce delivery timelines because parts of the testing workflow can run in parallel.
A strong AI pentesting workflow can accelerate:
Reconnaissance
Endpoint discovery
Attack surface mapping
Test generation
Payload variation
Source-assisted analysis
Exploit validation
Finding correlation
Retest verification
This does not mean AI replaces methodology.
It means repetitive and high-volume testing steps can move faster, allowing testers and security teams to focus on impact.
For example, an AI-assisted system can rapidly inspect JavaScript bundles for endpoints, map unauthenticated routes, identify suspicious API patterns, and correlate them with code-level authorization checks.
That is very different from simply running a scanner.
The strongest AI pentesting platforms combine automation with context.
Automated Penetration Testing Vs 48-Hour Manual Testing
Automated penetration testing and fast manual testing can both support 48-hour delivery, but they operate differently.
Area | Automated Penetration Testing | Fast Manual Pentesting |
|---|---|---|
Speed | High for repeatable workflows | Depends on tester availability |
Coverage | Strong for known patterns and large surfaces | Strong for nuanced logic |
Consistency | Repeatable across releases | Varies by engagement |
Retesting | Can be fast and continuous | May depend on scheduling |
Business logic depth | Needs good context | Strong with skilled testers |
Best use | CI/CD, external attack surface, repeat testing | Custom flows, complex abuse cases |
For SaaS teams, the ideal model often combines both.
Automation speeds up discovery and validation. Human judgment helps interpret business impact and edge cases.
What SLAs Matter More Than The 48-Hour Claim
The phrase “48-hour delivery” sounds simple, but buyers should ask for specific SLAs.
Critical finding notification SLA
If a critical issue is found, the vendor should notify you immediately.
Not at the end of the report cycle.
Report delivery SLA
This defines when you receive the written report.
Make sure it includes validated findings, not only automated output.
Retest SLA
This is one of the most important SLAs.
Ask how quickly the vendor will verify fixes after your team deploys remediation.
Evidence delivery SLA
For SOC 2 or customer reviews, ask when the final evidence package will be available.
This may include:
Final report
Retest report
Finding status
Screenshots or request evidence
Severity rationale
Scope and methodology
Support response SLA
If engineering has questions about remediation, the vendor should be available quickly.
A report without responsive support slows down fixing.
48-Hour Pentesting For SOC 2 And Customer Security Reviews
A 48-hour pentest is often requested because a deadline exists.
For SOC 2, the company may need evidence that security testing occurred and that findings were remediated.
For enterprise customer reviews, the buyer may ask for:
Recent pentest report
Scope confirmation
Critical finding status
Retest evidence
Remediation summary
Methodology explanation
A fast report can help only if it is credible. That means the report should explain:
What was tested
How testing was performed
What was confirmed
What was fixed
What remains open
Whether retesting passed
A generic PDF full of scanner findings will not carry the same weight.
How CodeAnt AI Approaches Fast AI Pentesting
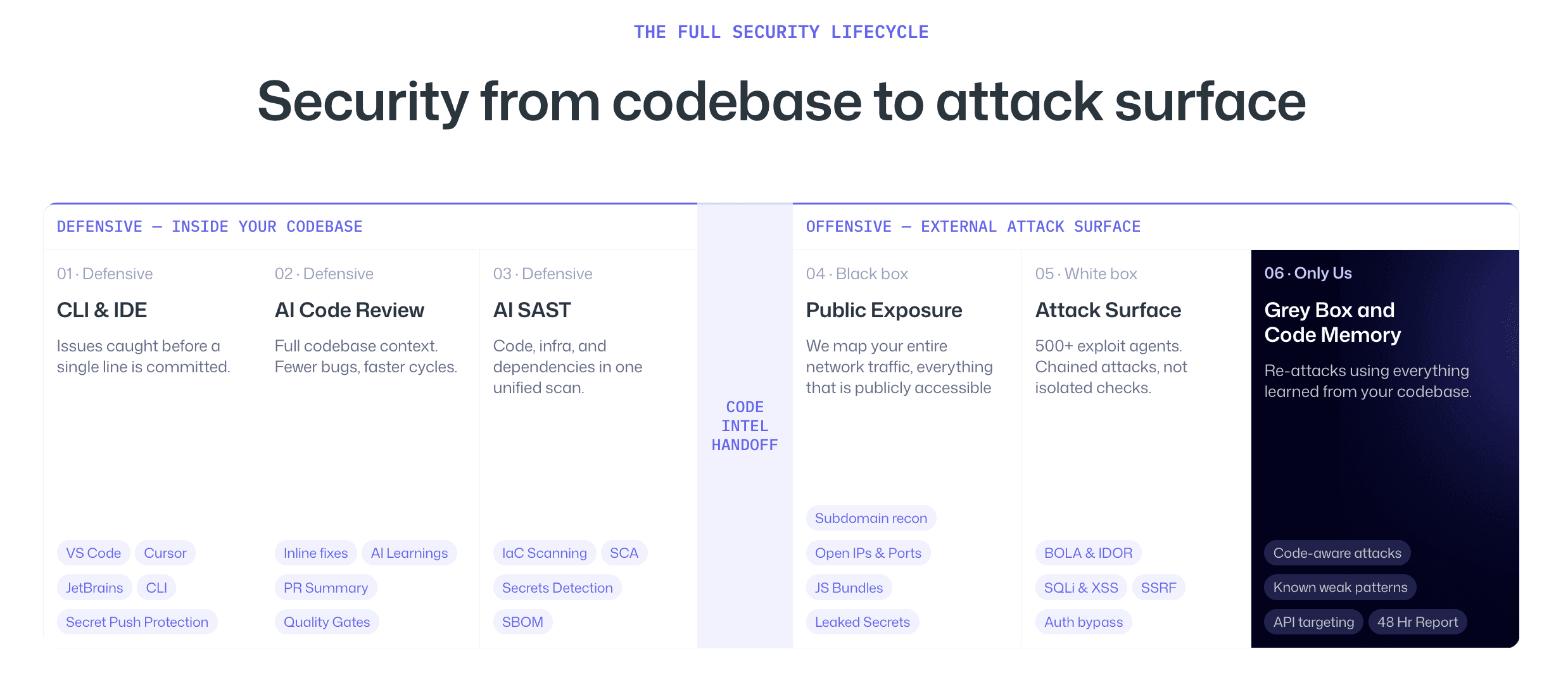
CodeAnt AI is not just a code review tool, not just a SAST product, and not just a penetration testing service.
It is a defensive plus offensive security platform.
That matters for 48-hour delivery because speed depends heavily on context.
On the defensive side, CodeAnt already reviews code across IDEs, CLI workflows, pull requests, and CI/CD pipelines. It learns insecure patterns, risky APIs, authentication logic, data flows, and recurring codebase issues.
On the offensive side, CodeAnt maps the external attack surface, performs reconnaissance, uses source code intelligence, runs gray box testing, and validates exploit chains.
The advantage is that offensive testing does not start cold.
The same platform that reviews code for insecure patterns in CI/CD is also testing the external surface with inside knowledge.
That can make fast testing deeper because the platform already understands where risk may exist.
For a SaaS team under pressure, that distinction matters. A fast external-only scan may find exposed assets. A defensive plus offensive platform can connect exposed assets to code paths, authentication logic, and real exploitability.
How To Evaluate Vendors Claiming 48-Hour Delivery
Use this checklist before choosing a provider.
Does 48-hour delivery mean kickoff, first finding, or full report?
Is exploit validation included?
Are critical findings reported immediately?
Is authenticated testing included?
Are APIs tested?
Is cloud exposure tested?
Are CI/CD secrets or leaked credentials checked?
Is retesting included?
Is a formal retest report provided?
Is evidence safe for SOC 2 or customer reviews?
Are findings mapped to business impact?
Does the vendor provide remediation guidance?
Does the vendor offer support after the report?
If the vendor cannot answer these clearly, the 48-hour claim may not mean much.
Sample 48-Hour Pentest Finding Format
A fast pentest finding should still look professional and actionable.
Field | Example |
|---|---|
Finding | Broken object-level authorization in invoice API |
Severity | High |
Affected endpoint |
|
User role | Standard organization member |
Proof | User from Org A accessed invoice belonging to Org B |
Impact | Cross-tenant data exposure |
Evidence | Request and response excerpt with sensitive fields redacted |
Root cause | Missing tenant ownership check |
Remediation | Enforce tenant scope on invoice lookup |
Retest status | Pending |
This format is useful because it gives engineering and compliance teams the same source of truth.
When 48-Hour Delivery Is Not Enough
Some scopes should not be compressed too far.
A full enterprise assessment across multiple products, cloud accounts, internal networks, mobile apps, and complex business workflows may need more time.
48-hour delivery is best for:
Focused web app testing
API testing
Specific release validation
External exposure checks
Retesting
Narrow compliance evidence gaps
Urgent customer review support
It may not be enough for:
Large enterprise red team exercises
Full internal network compromise simulation
Complex multi-region cloud audits
Deep business logic testing across many workflows
Thick client or hardware testing
The best vendors will tell you when 48 hours is appropriate and when it is not.
Conclusion: Fast Pentesting Only Matters If It Proves Real Risk
A 48-hour pentest can be valuable, but only when speed does not replace depth.
The goal is not to receive a fast PDF. The goal is to understand what can actually be exploited, how serious it is, how to fix it, and how quickly the fix can be verified.
For SaaS teams, SOC 2 audits, customer security reviews, and urgent release timelines, fast delivery can make a real difference. But the deliverable must include validated findings, proof of exploit, remediation guidance, and a clear retesting path.
This is where AI penetration testing and automated penetration testing can help. They reduce the time spent on repetitive discovery and validation while preserving focus on real attack paths.
CodeAnt’s defensive plus offensive model strengthens this further by connecting code intelligence with external testing. The platform does not just scan what is visible. It tests the external surface with context from the codebase and CI/CD.
If a vendor promises 48-hour delivery, ask one thing before signing:
Will you deliver validated risk, or just fast output?
Also, to sort your doubts you can try our AI penetration test that starts where others stop!
FAQs
Which Pentesting Vendors Offer 48-Hour Delivery?
Is A 48-Hour Pentest Enough For SOC 2?
How Is AI Penetration Testing Faster Than Manual Pentesting?
What Should A 48-Hour Pentest Report Include?
What Is The Difference Between Fast Pentesting And Vulnerability Scanning?