The Signature That Doesn't Actually Authorize Anything
A penetration test authorization letter signed by an IT manager is not authorization. It is a document that looks like authorization, provides the psychological comfort of authorization, and will not protect anyone if law enforcement gets involved or a dispute arises.
This is not a technicality. Legal authorization to conduct activities that would otherwise constitute unauthorized computer access requires a signatory who actually has the authority to grant that permission. An IT manager almost never does, they have operational access to systems but they don't own them, and they typically don't have delegated legal authority to waive the organization's rights against unauthorized access.
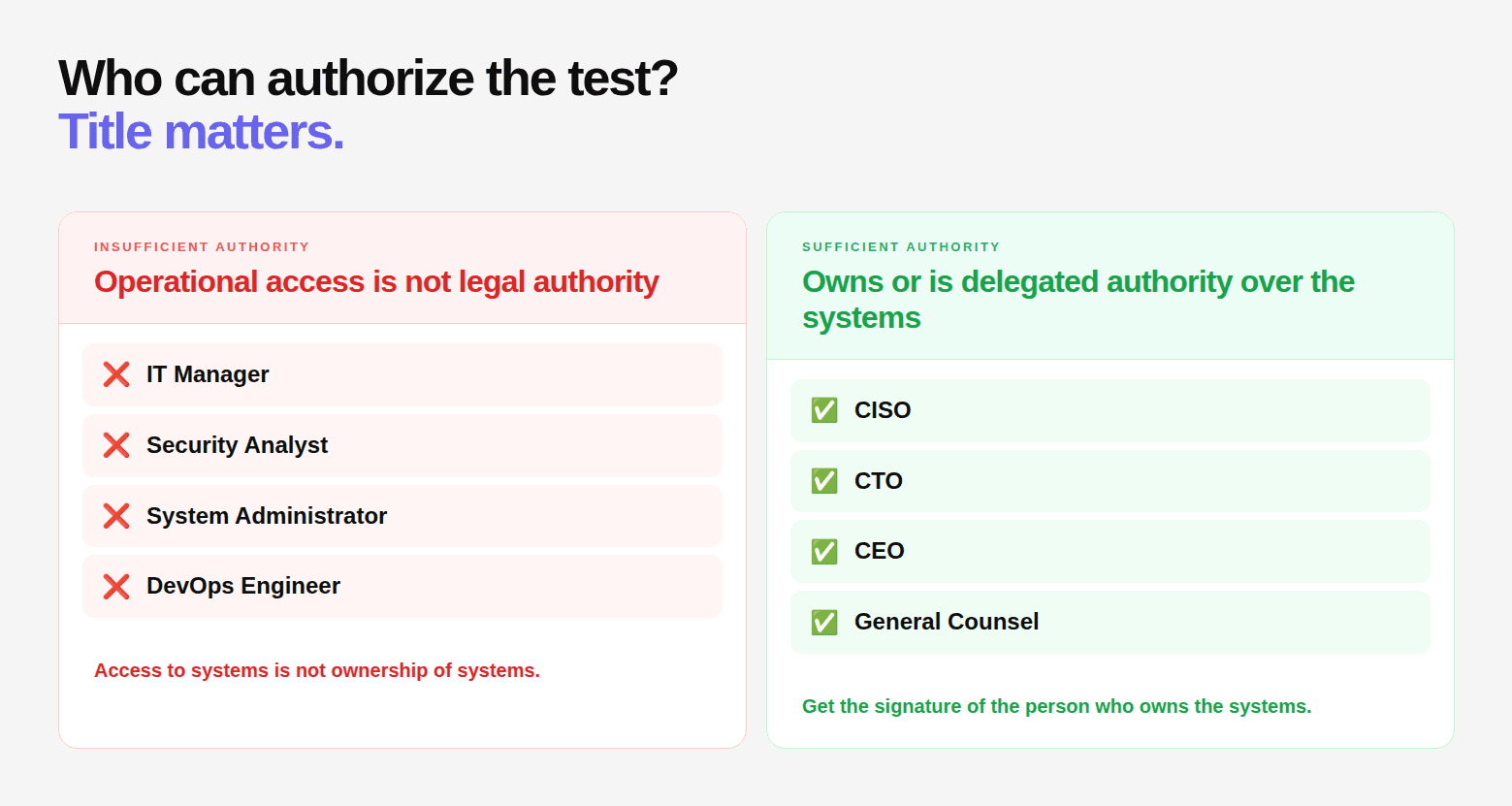
Getting the signing authority wrong is the second most common authorization letter mistake, after vague scope definition.
The Legal Standard
The Computer Fraud and Abuse Act and equivalent statutes require that access be authorized by someone who has the legal right to grant that authorization. Courts have interpreted this to mean the owner of the system, or someone expressly authorized by the owner to grant access.
In a corporate context, the "owner" of a system is the legal entity, the corporation. Authority to act on behalf of the corporation on matters with legal consequences flows from the board to executives to officers. An IT manager's authority covers operational decisions within their role. Waiving the organization's legal rights against unauthorized access is not within that role.
Authority By Organization Type
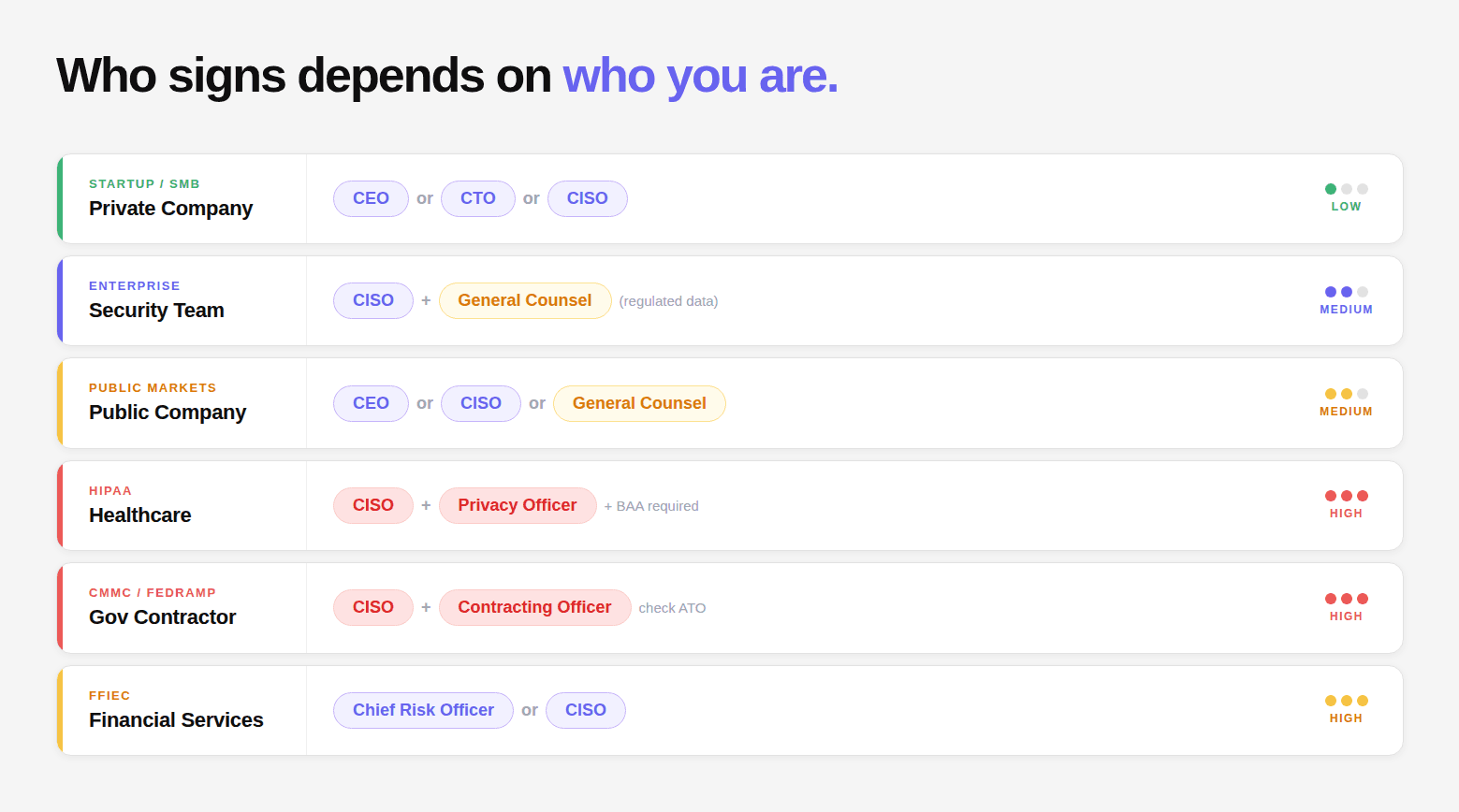
Private Company (startup, SMB, mid-market):
Minimum: CEO, CTO, or CISO. For small companies where one person holds multiple roles, whoever has explicit board-delegated authority to enter into contracts.
For systems containing customer PII: Add Legal Counsel co-signature. This matters both for legal protection and for regulatory defensibility, under GDPR and CCPA, data processing agreements for testing should be signed by someone with data governance authority.
Enterprise with a security team:
Minimum: CISO. For testing systems that touch payment data, financial records, or regulated data: CISO + General Counsel co-signature. For systems in regulated scope (PCI, HIPAA, SOC 2): document the signing authority clearly in the letter for audit evidence.
Public Company:
CEO, CISO, or General Counsel. Some public companies require board awareness (not necessarily board signature) for red team engagements or engagements that touch investor-sensitive systems. Check your company's authorization policy.
Healthcare Organization (HIPAA):
CISO + Privacy Officer co-signature for any testing that may access PHI. The Privacy Officer co-signature documents that HIPAA-specific data handling provisions were reviewed and approved. The testing firm should also sign a Business Associate Agreement (BAA) separately.
Government Contractor (CMMC, FedRAMP):
For systems processing Controlled Unclassified Information (CUI): the contracting officer may need to be involved. For FedRAMP-authorized systems, check whether your authorization to operate (ATO) requires prior government approval for third-party security testing. This varies by agency and contract.
Financial Services (FFIEC):
Chief Risk Officer or CISO signature. For engagements that touch systems in regulatory examination scope, regulatory findings may need to be disclosed, document this in the letter so the testing firm knows findings may reach regulators.
Delegation of Authority
If the appropriate C-suite officer cannot sign directly, written delegation is the correct solution. The delegation must:
Be in writing (email is insufficient, it must be a formal written document)
Specifically authorize the delegate to sign penetration testing authorization letters
Name the delegate by full name and title
Be signed by the original authorizing officer
Be attached to or referenced in the authorization letter
The delegation document itself should be retained alongside the authorization letter.
Co-Signature Requirements By System Type
System Type | Primary Signatory | Co-Signature Recommended |
|---|---|---|
Standard web application | CISO or CTO | Not required |
Customer PII system | CISO | Legal Counsel |
Payment card environment | CISO | CFO or Legal |
Health data (HIPAA) | CISO | Privacy Officer |
HR / employee data | CISO | HR Director or Legal |
Financial systems | CISO | CFO |
Government contract systems | CISO | Contracting Officer |
External-facing API | CTO or CISO | Not required |
Internal network (on-prem) | CISO | Not required |
What Happens When the Wrong Person Signs
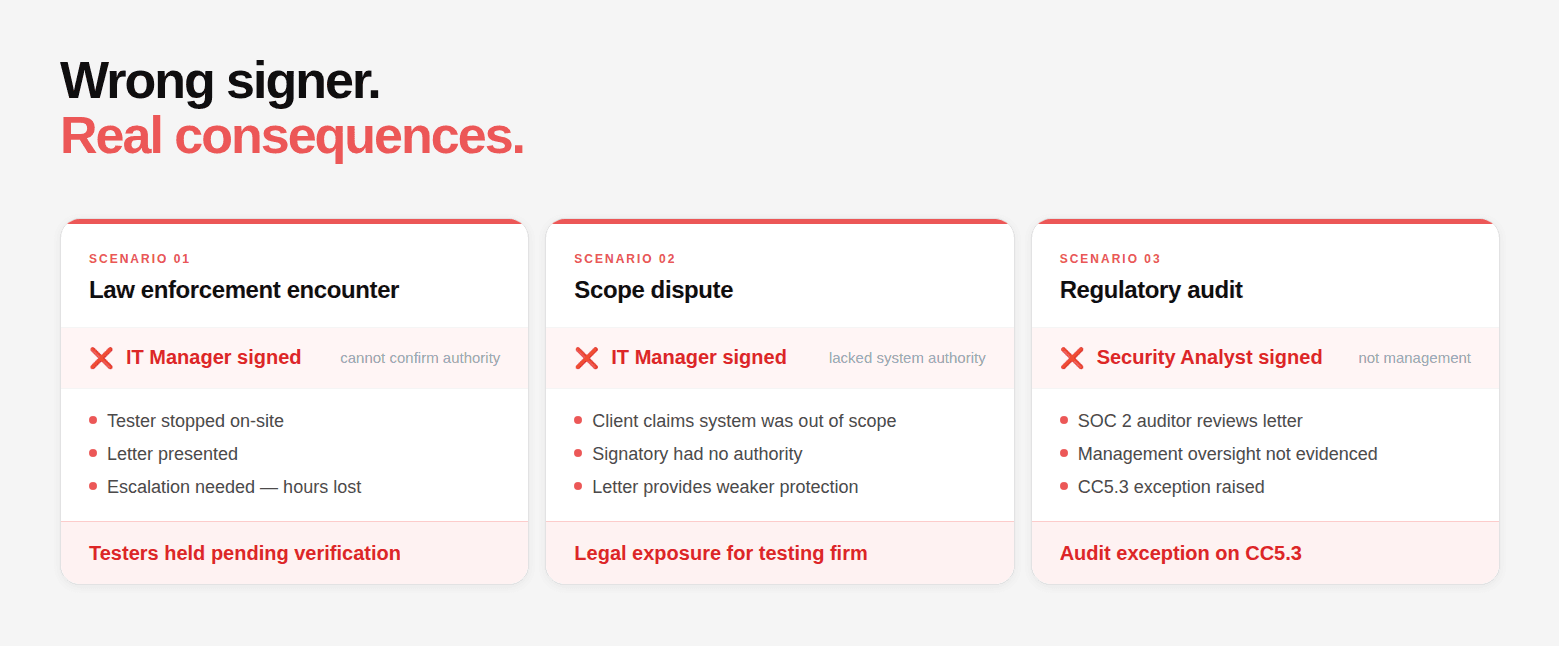
Scenario 1: Law enforcement encounter: Testing firm is stopped during a physical engagement. The letter is presented. Law enforcement calls the contact on the letter. The contact (an IT manager) has to escalate to find someone who can confirm authorization. That escalation takes time, potentially hours. During that time, testers remain in custody. A C-suite contact with clear authority resolves this in minutes.
Scenario 2: Scope dispute: A tester accesses a system that the client claims was out of scope. The client claims the IT manager who signed didn't have authority to include that system. The testing firm has a signed letter, but if the signatory genuinely lacked authority, the letter provides weaker protection than one signed by someone with clear authority. Court cases have turned on exactly this question.
Scenario: Regulatory audit: SOC 2 auditor reviews the penetration testing program. The authorization letter is signed by a security analyst. The auditor questions whether management appropriately reviewed and authorized the engagement, this is a CC5.3 evidence concern. A CISO or executive signature provides clear evidence of management oversight.
Red Team Engagements: Special Signing Authority Requirements
Red team engagements create a specific challenge: the people who would normally sign (CISO, security team) may be the people being tested. Signing authority for red team engagements must come from someone who is not part of the blue team being evaluated.
Typically: CEO or board member, with legal counsel as backup contact. The CISO who manages the security team being tested should not sign the authorization letter for their own team's red team evaluation. This both undermines the test's realism and creates a governance conflict.
Quick Reference Checklist
Before signing the authorization letter, verify:
[ ] Signatory is C-suite or has written delegation from C-suite
[ ] Signatory has reviewed and understands the scope in Section 3
[ ] Signatory has authority over all systems listed (not just some)
[ ] For regulated industries: appropriate co-signers are included
[ ] Emergency contact number on the letter is a direct mobile — not a desk phone
[ ] Signatory will be reachable during the entire testing window
[ ] For red team: signatory is not part of the blue team being tested
Signing Authority Is Not a Formality. It Is Legal Protection.
A penetration test authorization letter is only as strong as the person who signs it.
Everything in the document can be perfectly written. Scope can be precise. Techniques can be controlled. Emergency procedures can be airtight. But if the signatory does not have legal authority, the entire document becomes fragile when it is tested under pressure.
This is where most organizations get it wrong. They treat signing as a procedural step instead of a legal decision. The result is a document that works internally but fails when it matters most. During a law enforcement interaction, during a dispute, or during an audit.
The right signatory does three things. It validates that the organization has consciously approved the risk. It ensures the authorization holds up legally across jurisdictions. And it creates clear accountability at the level where decisions actually carry weight.
If there is any doubt, do not proceed with testing.
Escalate. Get the correct authority. Document delegation if needed. Add co-signers for regulated systems.
Because in penetration testing, authorization is not implied. It is proven by who signs.
FAQs
Can an IT manager sign a penetration test authorization letter?
Is a CISO always required to sign the authorization letter?
What if the authorized executive is not available to sign?
Are co-signatures mandatory for compliance frameworks like SOC 2 or HIPAA?
Who should sign for third-party or cloud-hosted systems?