SOC 2 Type 2 is not just asking whether your B2B SaaS company ran a penetration test once.
It is asking whether your security controls operated effectively over time.
That distinction matters.
A point-in-time pentest may show that your application was tested on one date. But a SaaS product changes constantly. New APIs ship, authentication logic changes, cloud infrastructure expands, and engineering teams push code through CI/CD every week. By the time the audit window ends, the system your vendor tested may no longer match the system your customers rely on.
This is why more SaaS teams are searching for AI penetration testing for B2B SaaS preparing for SOC 2 Type 2, PTaaS providers with retesting SLAs, and pentesting vendors that offer 48-hour delivery.
The goal is no longer just getting a PDF report.
The goal is proving three things clearly:
Vulnerabilities were actually tested, not just scanned
Exploitable issues were fixed and retested
Evidence exists for auditors, customers, and security reviews
For a fast-growing SaaS company, especially one selling into enterprise, SOC 2 Type 2 security testing needs to be continuous, evidence-driven, and connected to the way the product is built.
That is where AI penetration testing becomes valuable.
Not because “AI” sounds modern, but because strong AI pentesting can combine source code intelligence, external reconnaissance, authenticated testing, exploit validation, retesting, and compliance evidence into one repeatable workflow.
What SOC 2 Type 2 Actually Requires From Security Testing
SOC 2 Type 2 evaluates whether controls operated effectively over a period of time. This is different from SOC 2 Type 1, which focuses on whether controls are designed correctly at a point in time.
For B2B SaaS teams, penetration testing usually supports controls related to:
Logical access
Vulnerability management
Change management
Security monitoring
Risk remediation
Vendor and customer trust evidence
A weak pentest report may technically show that testing happened.
A strong SOC 2-ready pentest package shows:
What was tested
How it was tested
What was exploitable
What evidence proves exploitability
When the issue was found
When it was remediated
Whether the fix was retested
Which controls the finding maps to
What risk remains, if any
This is why simple vulnerability scans are often not enough.
SOC 2 auditors and enterprise customers want evidence that the security program can identify and remediate real risk. They do not want a long list of theoretical scanner alerts with no proof of impact.
Why Traditional Pentesting Often Falls Short For B2B SaaS SOC 2
Traditional manual pentesting still has value. Skilled testers can find nuanced logic flaws, authentication issues, and workflow abuse paths.
The problem is not manual testing itself.
The problem is that traditional pentesting often operates in a way that does not match SaaS development speed.
Common gaps include:
Testing happens once per year or once per quarter
Findings arrive weeks after testing
Retesting is slow or billed separately
Reports are not mapped clearly to compliance controls
Testers may not understand the codebase
Authenticated SaaS workflows are tested lightly
Cloud infrastructure and CI/CD exposure may be out of scope
For SOC 2 Type 2, these gaps matter because the audit period is continuous. Your product is not frozen during the audit. Your attack surface is changing throughout the observation window.
That means your security testing needs to prove ongoing control effectiveness, not just one-time testing.
How AI Penetration Testing Helps B2B SaaS Teams Prepare For SOC 2 Type 2
AI penetration testing helps B2B SaaS teams by making security testing faster, broader, more repeatable, and more connected to engineering workflows.
A strong AI pentesting program can continuously examine:
External attack surface
APIs and web applications
Authentication and authorization flows
SaaS role boundaries
Tenant isolation
Cloud infrastructure
CI/CD exposure
Source code patterns
Business logic workflows
The value is not just automation. The value is correlation.
AI-powered pentesting can connect signals across code, application behavior, cloud exposure, and real exploit paths. That matters because SaaS breaches rarely come from one isolated issue. They often come from a chain.
For example:
A public staging subdomain exposes an internal API
A JavaScript bundle leaks an endpoint
A weak authorization check allows IDOR
A tenant identifier can be modified
Customer data becomes accessible across accounts
A scanner may report fragments. A strong AI pentest should identify the attack path.
What AI Pentesting Should Test In A B2B SaaS Application
For a B2B SaaS company preparing for SOC 2 Type 2, the highest-risk areas are usually not generic CVEs. They are application-specific trust boundaries.
Authentication and session security
AI pentesting should test whether attackers can bypass login, reuse expired sessions, manipulate tokens, or abuse password reset flows.
This includes:
JWT validation flaws
Weak session expiration
Missing token revocation
Password reset token abuse
Single sign-on misconfiguration
MFA bypass paths
Authentication issues directly affect logical access controls and customer trust.
Authorization and role boundaries
Authorization is where many B2B SaaS breaches begin.
Pentesting should verify whether users can access actions or data outside their intended permissions.
This includes:
Admin endpoint access by standard users
Broken role-based access control
Privilege escalation
Organization owner abuse paths
Support role overreach
API-level authorization gaps
For SOC 2, this supports evidence that access controls are working as intended.
Tenant isolation
If your SaaS product is multi-tenant, tenant isolation is one of the most important areas to test.
AI pentesting should verify that one customer cannot access another customer’s data through:
IDOR
Modified tenant IDs
Unscoped database queries
Shared cache keys
Broken object-level authorization
Cross-tenant API access
For B2B SaaS, tenant isolation failure is often a critical security and compliance issue.
API and GraphQL security
Modern SaaS products are API-heavy.
Testing should cover:
REST APIs
GraphQL endpoints
Internal APIs exposed accidentally
API version drift
Mass assignment
Query abuse
BOLA
Rate limit bypass
Sensitive response fields
This is where AI pentesting for web application security becomes especially relevant.
Cloud infrastructure exposure
B2B SaaS companies often run on AWS, Azure, or GCP.
AI pentesting should test for:
Public storage buckets
Exposed databases
Misconfigured security groups
Public admin dashboards
Kubernetes exposure
CI/CD secrets
Metadata service abuse
IAM privilege escalation paths
Business logic abuse
Business logic vulnerabilities rarely show up in scanners.
AI pentesting should test workflows such as:
Subscription tier bypass
Seat limit bypass
Payment manipulation
Trial abuse
Invite flow abuse
Approval bypass
Export permission abuse
Report access manipulation
These issues matter because they often represent real SaaS business risk.
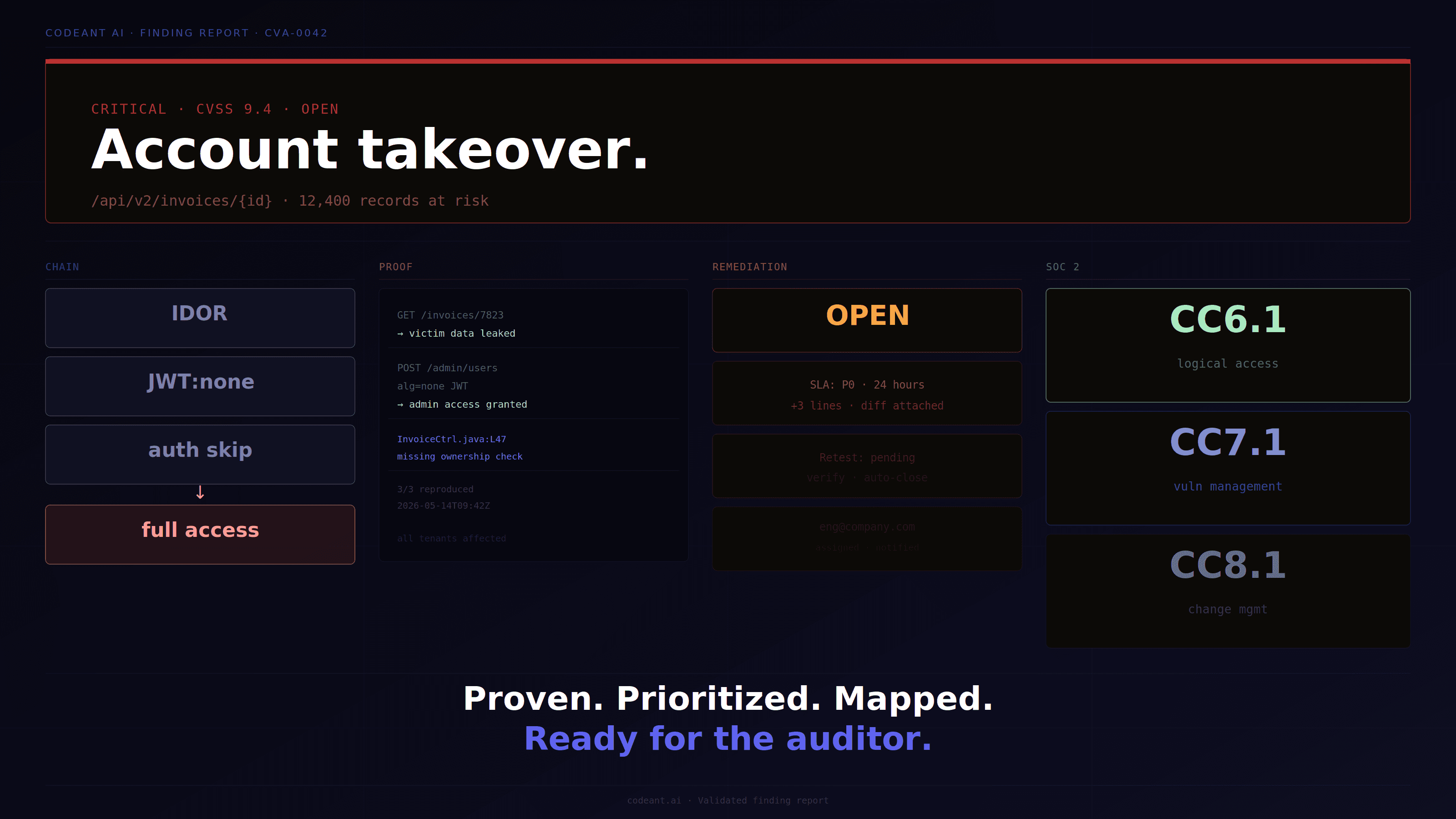
Why Proof Of Exploit Matters For SOC 2 Type 2
A SOC 2-ready pentest should not only say “this may be vulnerable.”
It should show what was proven.
Proof of exploit usually includes:
Affected endpoint
HTTP method
Request payload
User role used
Response evidence
Data exposed
Business impact
Reproduction steps
Severity rationale
Remediation guidance
This is valuable for three reasons.
First, engineering teams know exactly what to fix.
Second, auditors can see that the issue was real.
Third, customers reviewing your security program can trust that findings were not theoretical.
This is also where AI penetration testing should be clearly separated from vulnerability scanning. A scanner creates alerts. A pentest proves risk.
What “No Critical Findings, No Payment” Means In Pentesting
Some teams are now asking: What does “no critical findings, no payment” mean in pentesting?
The idea is simple. The vendor’s compensation is tied to validated high-impact findings rather than time spent or report volume.
This model changes incentives.
In a traditional fixed-fee engagement, the vendor gets paid whether or not serious vulnerabilities are found. In an outcome-aligned model, the vendor is rewarded when it confirms meaningful risk.
But buyers should be careful.
A “no critical findings, no payment” model only works if severity is transparent, evidence-backed, and agreed upon in advance.
A good agreement should define:
What counts as high or critical severity
Whether exploit chains count as critical
How severity is scored
What proof is required
How disputes are resolved
Whether low and medium findings are still reported
Whether retesting is included
For SaaS companies, this model can be attractive because it aligns spend with actual risk discovered. But it should never replace methodology quality.
Outcome-based pricing is only valuable when the testing is deep enough to find real issues.
Which Pentesting Vendors Offer 48-Hour Delivery?
The better question is not just which pentesting vendors offer 48-hour delivery.
The better question is:
What does the vendor deliver in 48 hours?
A fast scan is not the same as a fast pentest.
For SOC 2 and enterprise readiness, 48-hour delivery is only useful if it includes:
Validated findings
Proof of exploit
Clear severity
Affected assets
Remediation steps
Evidence export
Retesting path
A 48-hour report that only lists possible vulnerabilities may not help engineering, auditors, or customers.
Fast delivery matters most when:
A customer security review is blocking a deal
SOC 2 evidence is urgently needed
A critical release is going live
A new external asset was exposed
A breach concern needs validation
A remediation needs retest confirmation
For fast-growing SaaS teams, speed is important. But speed without validation creates false confidence.
What SLAs Leading PTaaS Providers Should Guarantee
When evaluating AI pentesting or PTaaS vendors for SOC 2 Type 2, ask about SLAs.
Leading providers should define SLAs for:
Engagement kickoff
Time to first finding
Critical finding notification
Final report delivery
Retest turnaround
Evidence package delivery
Support response time
Fix verification
For B2B SaaS, retesting SLA is especially important.
A finding without fast retesting can block:
SOC 2 audit closure
Enterprise procurement
Customer security questionnaires
Production launches
Compliance evidence requests
A strong SLA should make remediation measurable.
For example:
Critical findings reported immediately
Full report within 48 hours for scoped rapid tests
Retesting initiated within 24 hours after fix deployment
Evidence package delivered after verification
The exact numbers depend on vendor scope, but the principle is the same: testing is not complete until fixes are verified.
Best Pentest Platform For A CISO At A 200-Person SaaS Company
A 200-person SaaS company has different needs from a seed-stage startup and a 20,000-person enterprise.
At this stage, the company usually has:
Enterprise customers
SOC 2 Type 2 pressure
A growing engineering team
Multiple cloud environments
More APIs
More customer data
CI/CD velocity
Limited security headcount
The best pentest platform for a CISO at a 200-person SaaS company should support both execution and evidence.
It should provide:
Fast testing turnaround
Clear exploit validation
CI/CD integration
Cloud exposure testing
Authenticated SaaS workflow testing
Retesting
SOC 2-ready reporting
Engineering-friendly remediation details
This is why defensive plus offensive security matters.
A CISO does not only need to know what was found after deployment. They need to reduce what ships in the first place.
That means the ideal platform should connect:
Code review
CI/CD security
External reconnaissance
AI penetration testing
Exploit chaining
Retesting
Compliance reporting
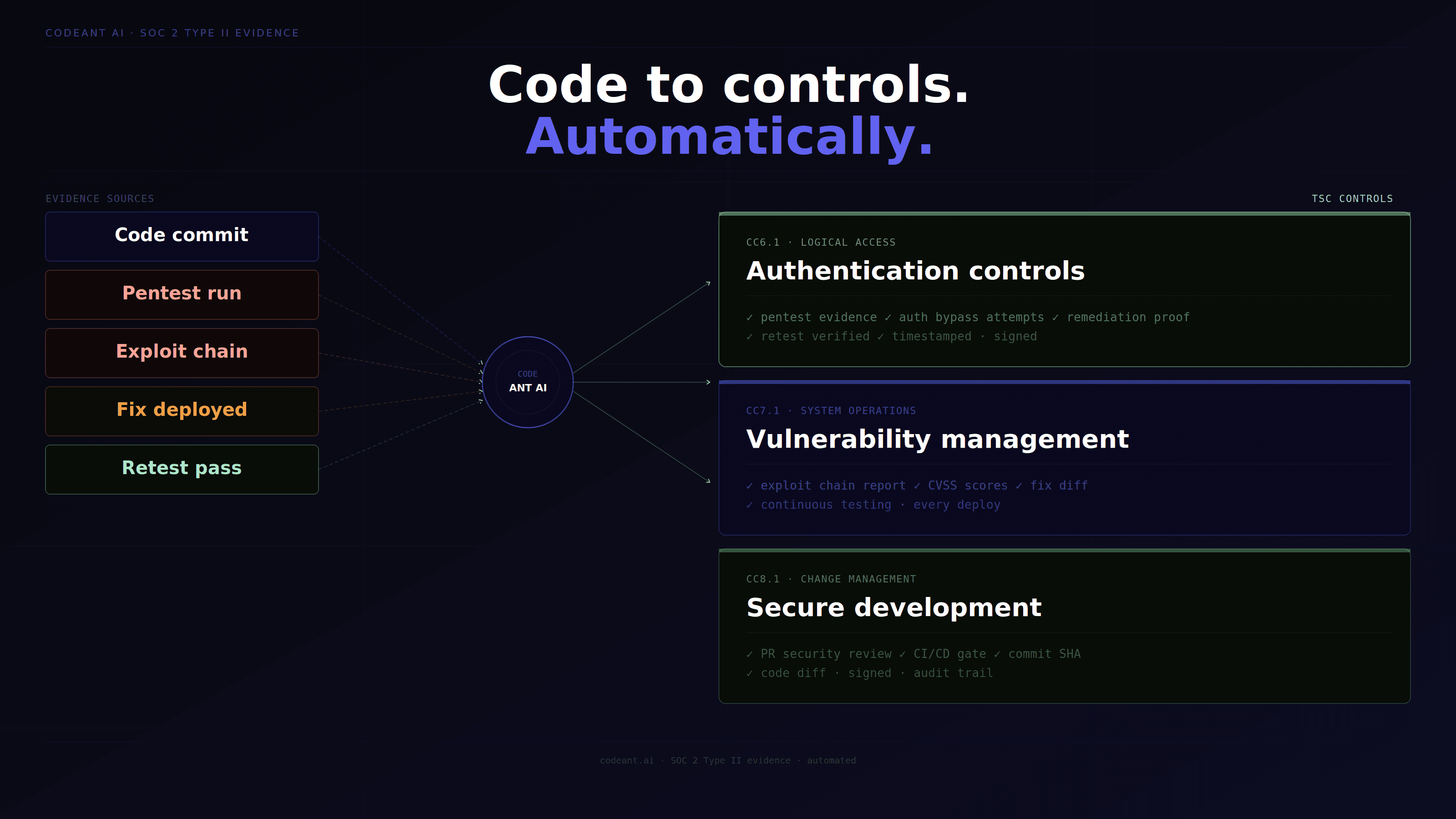
This is the model CodeAnt AI is built around.
Where CodeAnt AI Fits For SOC 2-Ready SaaS Pentesting
CodeAnt AI is not just a code review tool. It is not just a SAST product. It is not just a penetration testing product.
It is a complete, agent-based defensive and offensive security platform.
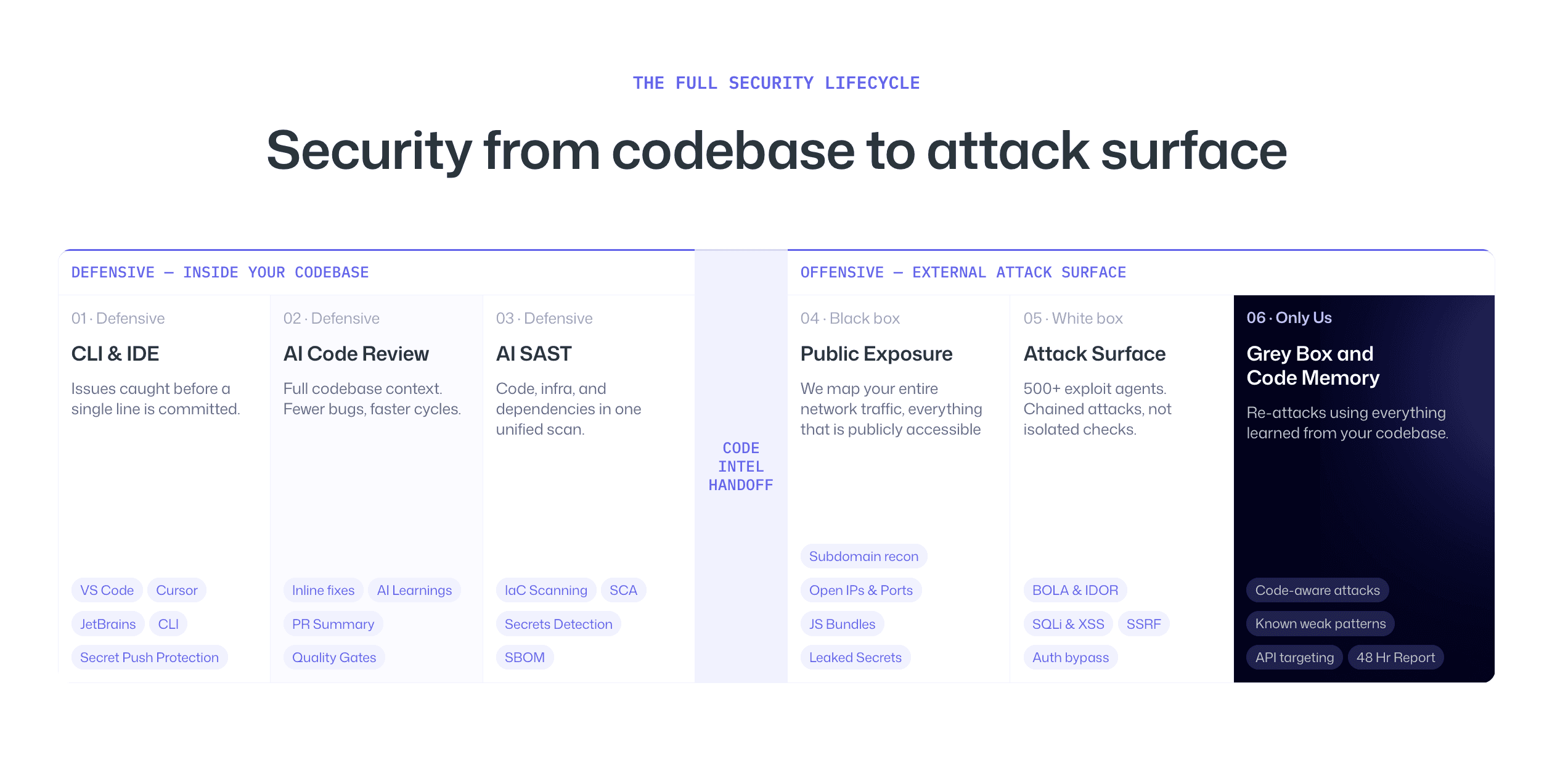
On the defensive side, CodeAnt integrates into CLI, IDEs, pull requests, and CI/CD pipelines. It helps developers catch security and quality issues as code is written and committed.
On the offensive side, CodeAnt examines the full public exposure of the application and tests it like an adversary would. It performs external reconnaissance, reads source code, uses defensive analysis as memory, runs gray box testing with code context, and constructs exploit chains.
The core advantage is simple:
The same platform that reviews code for insecure patterns in CI/CD is the one conducting reconnaissance against the external surface.
That means the offensive test does not start blind. It starts with knowledge of authentication patterns, data flows, insecure APIs, and recurring codebase risks.
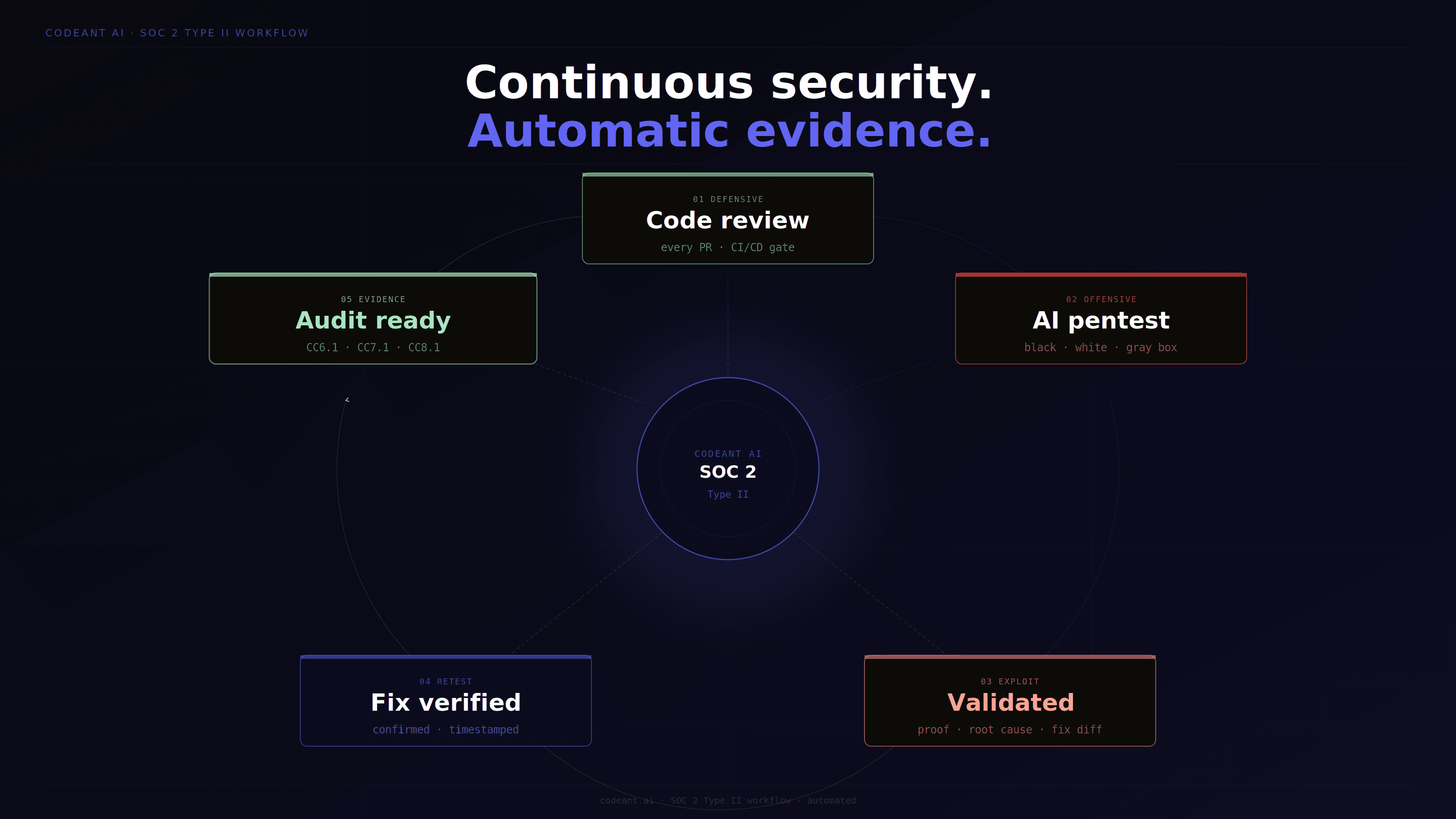
For SOC 2 Type 2, this matters because CodeAnt can support both sides of the evidence story:
Prevention through defensive code review
Validation through offensive testing
Proof of exploit
Remediation guidance
Retesting
Compliance-ready evidence
That is stronger than treating SAST, pentesting, and audit evidence as disconnected workflows.
AI Pentesting For Healthcare SaaS And HIPAA-Aligned Vendors
Healthcare SaaS teams have even stricter requirements because security failures may involve protected health information.
The testing scope should include all the SaaS security areas above, plus additional attention to:
PHI exposure
Access logging
Export controls
Role-based access to patient data
Tenant isolation
Admin access controls
Audit trail integrity
Data retention and deletion
Vendor evidence handling
Healthcare SaaS teams should ask vendors how test data is handled, how evidence is stored, how data deletion is confirmed, and whether reports avoid unnecessary reproduction of sensitive data.
A strong pentest report should describe sensitive exposure without over-collecting sensitive information.
AI Pentesting For Cloud Infrastructure Across AWS, Azure, And GCP
B2B SaaS companies increasingly run across cloud-native environments.
AI pentesting for cloud infrastructure should test more than public ports.
It should evaluate how exposed cloud assets interact with application logic and identity permissions.
Important areas include:
Public object storage
IAM permission paths
Exposed Kubernetes dashboards
Public databases
Secrets in CI/CD pipelines
SSRF to metadata services
Overexposed serverless functions
Misconfigured security groups
Exposed container registries
Cloud findings often become more serious when chained with application issues.
For example:
A public endpoint leaks a signed URL
The signed URL exposes customer exports
An IAM role allows broader bucket access
The attacker pivots from one file to full dataset exposure
This is why AI pentesting should connect cloud, code, and application context instead of testing each in isolation.
How Long Does An AI Pentest Take Vs A Manual One?
The timeline depends on scope, access, and methodology.
Manual pentests often take one to three weeks for testing, plus reporting time. Larger scopes may take longer.
AI-assisted pentesting can reduce time to first finding significantly because reconnaissance, test generation, and validation can run in parallel. Some vendors may deliver initial validated findings within 24 to 48 hours, depending on scope.
But speed should not be the only buying criterion.
Ask whether the timeline includes:
Setup
Reconnaissance
Authenticated testing
White box code analysis
Exploit validation
Report writing
Retesting
Evidence delivery
A fast AI pentest is valuable only if it produces validated, actionable findings.
How To Evaluate AI Pentesting Vendors For SOC 2 Type 2
Use this checklist before choosing a provider.
Does the vendor provide proof of exploit?
Does the vendor support authenticated SaaS testing?
Does the vendor test tenant isolation?
Does the vendor cover cloud infrastructure?
Does the vendor support CI/CD workflows?
Does the vendor provide retesting?
Does the vendor map findings to SOC 2 controls?
Does the vendor provide timeline documentation?
Does the vendor define clear SLAs?
Does the vendor handle sensitive test data safely?
Does the vendor offer continuous testing?
Does the vendor help prevent repeat findings?
If a vendor cannot answer these clearly, it may still provide useful testing, but it may not be the best fit for SOC 2 Type 2 readiness.
RFP Requirements For AI Penetration Testing
If you are writing an RFP for AI penetration testing, include specific requirements.
Do not ask only for “AI pentesting.”
Ask vendors to describe:
Testing methodology
Black box coverage
White box source code review
Gray box authenticated testing
Cloud infrastructure coverage
CI/CD integration
Exploit validation process
Severity scoring
Retesting SLA
Compliance evidence
Data handling
Reporting format
Timeline
Pricing model
Also, check out this interesting read on: Black Box vs White Box vs Gray Box Penetration Testing
Also ask for sample findings.
A vendor’s sample finding tells you more than their marketing page. Look for clarity, reproducibility, evidence, root cause, and remediation guidance.
Conclusion: Use AI Penetration Testing To Turn SOC 2 Evidence Into Real Security
SOC 2 Type 2 is not just about passing an audit.
For B2B SaaS companies, it is about proving that security controls work while the product keeps changing.
That means penetration testing has to evolve beyond one-time reports and generic scanner output. SaaS teams need exploit validation, authenticated testing, cloud coverage, retesting, and evidence that maps clearly to real risk.
AI penetration testing helps when it connects speed with depth. The best platforms do not just find issues faster. They understand how vulnerabilities move from code to deployment to exploitation.
This is where CodeAnt AI’s defensive and offensive model is especially strong. It reviews code continuously in CI/CD, tests the external attack surface with that code intelligence, validates exploit chains, and helps produce evidence that security teams can use for remediation, customers, and auditors.
If your SaaS team is preparing for SOC 2 Type 2, do not ask only whether a vendor can run a pentest.
Ask whether they can prove what is exploitable, verify what is fixed, and help prevent the same class of issue from shipping again.
Even best check out our AI penetration test that starts where others stop.
FAQs
What Is AI Penetration Testing For B2B SaaS Preparing For SOC 2 Type 2?
Which Pentesting Vendors Offer 48-Hour Delivery?
What SLAs Should Leading PTaaS Providers Guarantee?
What Does “No Critical Findings, No Payment” Mean In Pentesting?
What Is The Best Pentest Platform For A 200-Person SaaS Company Preparing For SOC 2?