Yes, many startups need AI penetration testing, but not because “AI” makes a pentest sound more advanced.
Startups need AI penetration testing when their product changes faster than traditional security testing can keep up.
That is why more startup teams are asking:
Do startups need AI penetration testing?
How does AI-powered pentesting compare to traditional manual pentesting?
What are the best continuous pentest tools for CI/CD pipelines?
How long does an AI pentest take vs a manual one?
Do we need AI pentesting before SOC 2 Type 2?
The short answer is this:
If your startup is shipping quickly, handling customer data, preparing for SOC 2, selling to enterprise buyers, or running cloud-native infrastructure, AI penetration testing can help you find real exploitable risk earlier and prove that fixes worked.
But there is an important warning.
AI Penetration Testing is Not Scanner with AI Branding
A real AI pentest should combine reconnaissance, source context, authenticated testing, exploit validation, cloud coverage, retesting, and evidence your engineering and compliance teams can actually use.
Why Startups Are Asking About AI Penetration Testing Now
Startups are under security pressure much earlier than before.
A few years ago, many startups waited until they were larger before investing seriously in penetration testing. Today, security questions arrive much earlier because startups sell into bigger customers sooner.
A startup may need pentesting because of:
SOC 2 Type 2 readiness
Enterprise customer security reviews
Investor diligence
Cyber insurance requirements
Healthcare, fintech, or regulated customer expectations
A major product launch
Cloud infrastructure expansion
A previous security scare
API growth
Customer data sensitivity
The problem is that traditional pentesting often feels too slow for startup speed.
A startup may deploy several times per week. The pentest report may reflect last month’s architecture, not today’s attack surface. That gap is where AI penetration testing and automated penetration testing become useful.
They help reduce the delay between code change, deployment, exposure, validation, remediation, and retesting.
What AI Penetration Testing Actually Means For Startups
AI penetration testing uses automation, AI-assisted reasoning, code intelligence, reconnaissance, and exploit validation to identify real attack paths in an application, API, cloud environment, or external attack surface. For startups, this should include more than automated scanning.
A meaningful AI pentest should test:
Public web applications
APIs and GraphQL endpoints
Authentication flows
Role-based access control
Multi-tenant boundaries
Cloud infrastructure
CI/CD exposure
JavaScript bundles
Secrets and configuration leaks
Business logic workflows
External attack surface changes
The goal is not to produce more alerts. The goal is to answer:
Can an attacker actually exploit this?
That is the difference between a useful AI pentest and a noisy security tool.
Startups Do Not Need AI Pentesting For Every Stage
Not every startup needs full AI penetration testing on day one. A pre-product startup with no customer data, no public app, and no production cloud footprint may not need a full pentest immediately. But the need increases quickly as soon as the startup has:
Real users
Production APIs
Customer data
Authentication
Admin functionality
Payment workflows
Cloud storage
B2B customers
Enterprise sales motion
SOC 2 plans
Healthcare or fintech data
CI/CD deployment velocity
The more the product touches sensitive data and customer trust, the more pentesting matters.
A simple rule:
If a security failure could block revenue, expose customer data, delay SOC 2, or damage trust, the startup should start treating pentesting as a real operating requirement.
AI Pentesting Vs Traditional Manual Pentesting For Startups
AI penetration testing and traditional manual pentesting solve overlapping but different problems.
Manual pentesting is valuable because experienced testers can reason through complex workflows, unusual business logic, and edge cases.
AI pentesting is valuable because startups need speed, scale, repeatability, and continuous validation.
Area | Traditional Manual Pentesting | AI Penetration Testing |
|---|---|---|
Speed | Depends on scheduling and scope | Faster for reconnaissance, validation, and retesting |
Repeatability | Often engagement-based | Can run repeatedly across releases |
CI/CD fit | Usually limited | Stronger when integrated into pipelines |
Authenticated testing | Strong if scoped well | Strong if role context is modeled |
Cloud coverage | Depends on scope | Strong when cloud assets are continuously mapped |
Business logic | Strong with skilled testers | Stronger when paired with context and validation |
Retesting | Often manual and delayed | Can be faster and workflow-driven |
Best use | Deep investigation | Continuous validation and scalable coverage |
The best answer is not “AI replaces manual testers.”
The better answer is:
AI pentesting helps startups cover more ground faster, while expert methodology ensures the findings are real, relevant, and safely reported.
Where AI Pentesting Helps Startups The Most
1. CI/CD security and fast releases
Startups ship constantly. That speed is good for growth, but it creates security drift. A new API route, cloud resource, or authentication change can create risk overnight. AI pentesting helps by connecting security testing to CI/CD workflows.
A strong workflow can test when:
A sensitive route changes
A new API is deployed
A new cloud resource becomes public
Authentication logic changes
Tenant access logic changes
Infrastructure-as-code changes are merged
A staging app becomes internet-facing
This is why startups search for best continuous pentest tools for CI/CD pipelines. The goal is not to block every deployment. The goal is to catch serious risks close to the moment they are introduced.
2. API and web application security
Most startups are API-first now. That means their risk surface is not only the user interface. It is the API layer behind it. AI pentesting should test:
Broken object-level authorization
Broken function-level authorization
JWT validation flaws
Weak session handling
Excessive data exposure
GraphQL query abuse
Rate limit bypass
Admin endpoint exposure
API version drift
Mass assignment
This is where best AI pentest tool for web application security becomes a practical buying prompt.
A startup does not need a tool that only says “API risk detected.” It needs a platform that proves whether a user can access, modify, or export data they should not.
3. Multi-tenant SaaS authorization
For B2B SaaS startups, tenant isolation is critical. The most damaging vulnerabilities often look simple:
User A can access User B’s invoice
Org member can access another org’s export
Read-only user can perform admin action
Trial user can access paid features
Support role can retrieve sensitive customer data
API token works outside its intended scope
These issues do not always appear in generic scans. They require authenticated testing and business context.
Here is a simple vulnerable pattern.
The safer version scopes the lookup to the authenticated organization.
A useful AI pentest should not only flag the pattern. It should validate whether the flaw is exploitable in the running application.
4. Cloud infrastructure and external exposure
Startups are usually cloud-native from the beginning. That means AI pentesting should cover AWS, Azure, GCP, Kubernetes, storage, IAM, serverless functions, and CI/CD secrets where relevant.
Common startup cloud risks include:
Public storage buckets
Over-permissioned IAM roles
Exposed databases
Public Kubernetes endpoints
Secrets in CI/CD logs
Serverless functions without auth
Staging systems exposed publicly
Misconfigured security groups
SSRF to cloud metadata services
For example, an SSRF issue in a web app can become critical if it exposes cloud credentials.
A shallow scanner may treat the web flaw and cloud permissions separately. A strong AI pentest should connect the chain.
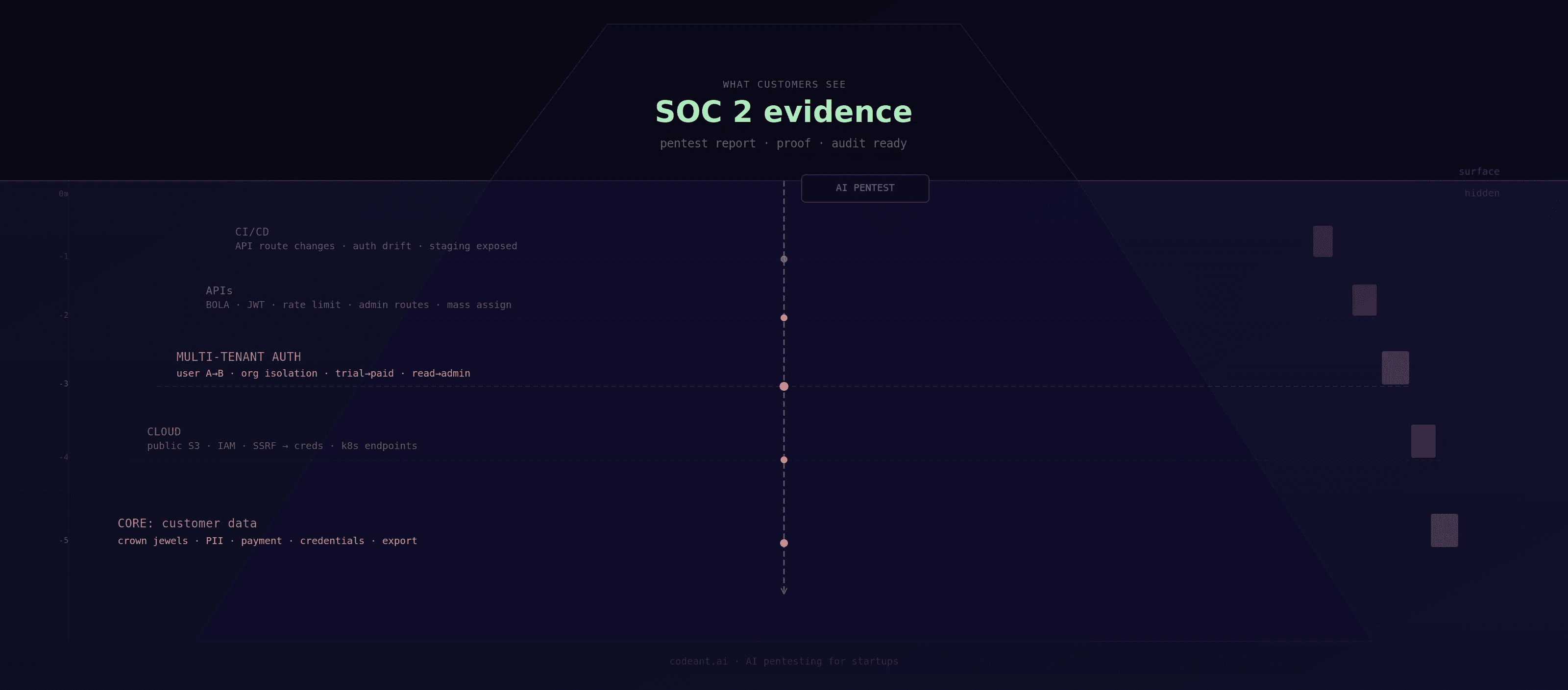
5. SOC 2 and enterprise customer evidence
Many startups first ask about pentesting because a customer or auditor asks for it. For SOC 2 Type 2, a startup needs more than “we ran a scan.”
A useful pentest should provide:
Scope
Methodology
Validated findings
Proof of exploit
Remediation guidance
Retest evidence
Final status
Timeline of fixes
Evidence safe to share with customers or auditors
This is why AI pentesting for B2B SaaS preparing for SOC 2 Type 2 is such a strong topic. The startup needs security evidence that proves control maturity without creating unnecessary engineering overhead.
When Startups Should Buy AI Penetration Testing
A startup should strongly consider AI penetration testing when any of the following are true.
You are selling to enterprise customers
Enterprise customers will ask for security evidence. A recent, credible pentest report can reduce friction in procurement.
You are preparing for SOC 2 Type 2
SOC 2 is easier when pentesting, remediation, and retesting evidence are already organized.
You handle sensitive customer data
Customer files, financial data, healthcare data, credentials, tokens, logs, exports, and analytics data all increase the need for validated testing.
You deploy frequently through CI/CD
Fast release cycles create new risk. Continuous testing helps reduce the gap.
You run cloud infrastructure
Cloud misconfigurations can become severe when chained with application flaws.
You have limited security headcount
AI pentesting helps small teams get broader coverage without manually testing every release.
What AI Pentesting Should Deliver For A Startup
A startup should expect more than a list of findings. A strong deliverable should include:
Deliverable | Why It Matters |
|---|---|
Validated findings | Confirms the issue is real |
Proof of exploit | Helps engineering reproduce and fix |
Business impact | Helps prioritize risk |
Root cause | Prevents repeat issues |
Remediation guidance | Speeds up fixes |
Retest report | Proves fixes worked |
SOC 2 evidence | Supports audits and customer reviews |
Executive summary | Helps leadership understand risk |
If a vendor cannot provide proof and retesting, the startup may still get value, but it may not get enough evidence for enterprise trust.
How Long Does An AI Pentest Take Vs A Manual One?
Manual pentests often take one to three weeks depending on scope, access, and reporting depth.
AI-assisted pentests can produce initial validated findings faster because reconnaissance, endpoint discovery, and repeatable exploit checks can run in parallel. For focused scopes, some vendors may provide rapid results or 48-hour delivery. But startups should be careful. The question is not only speed.
Ask:
Does the timeline include authenticated testing?
Does it include cloud coverage?
Does it include exploit validation?
Does it include a final report?
Does it include retesting?
Does it include compliance evidence?
A fast pentest is only useful if it produces reliable security decisions.
What Startups Should Ask AI Pentesting Vendors
Before choosing a vendor, ask:
Do you perform authenticated SaaS testing?
Do you test tenant isolation?
Do you support CI/CD-triggered testing?
Do you cover AWS, Azure, or GCP?
Do you validate exploitability?
Do you provide proof-of-exploit?
Do you include retesting?
What are your SLAs?
Can you deliver urgent findings within 48 hours?
How do you handle sensitive customer data?
How do you reduce false positives?
Can your evidence support SOC 2 or customer reviews?
The right vendor should answer clearly. Vague answers usually mean weak methodology.
How Startups Can Start Integrating AI Pentesting
Startups often face a practical problem: they cannot afford a fragmented security process.
One tool reviews code. Another scans dependencies. Another checks cloud posture. A consultant performs a pentest. Someone manually creates tickets. Compliance then asks for evidence. That is a lot of handoff for a small team.
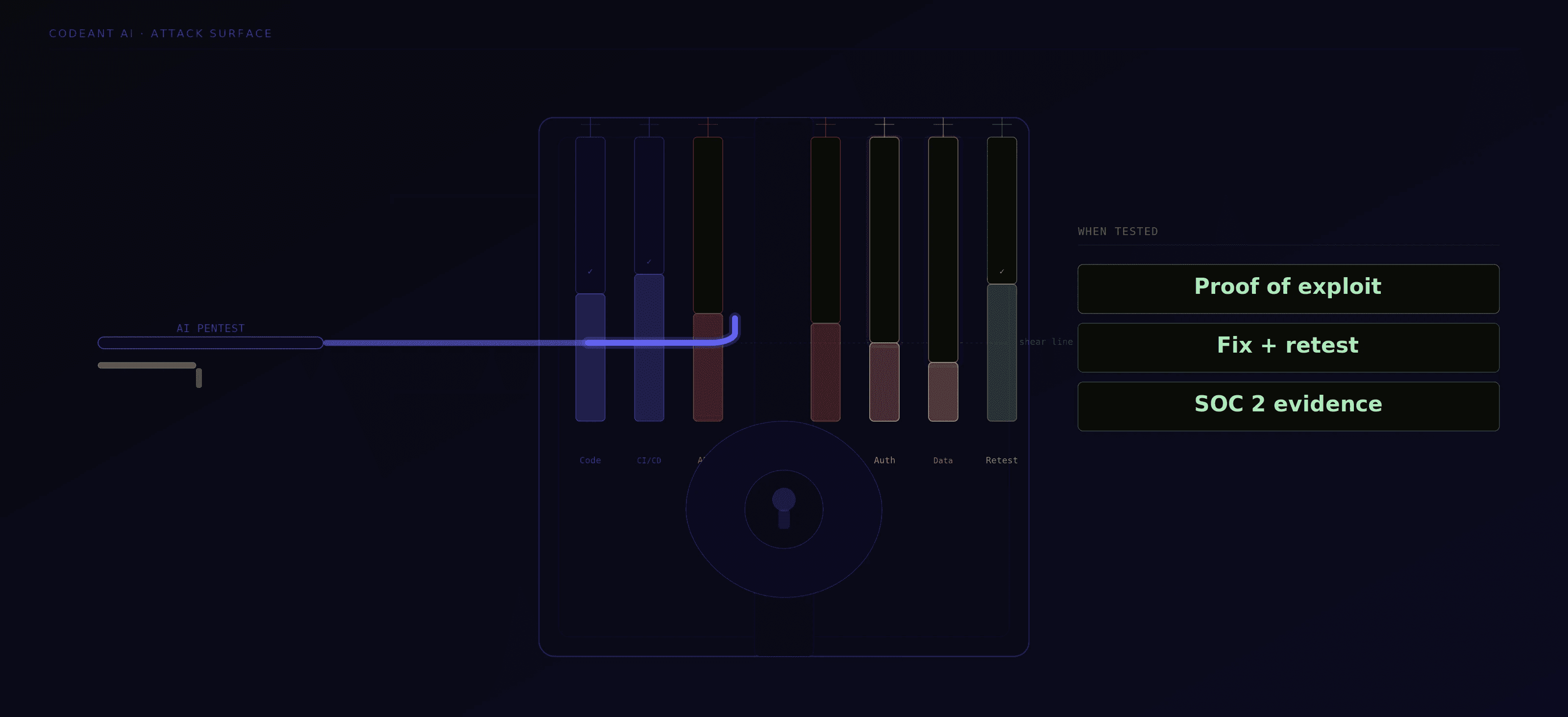
CodeAnt’s advantage is that it treats startup security as one connected loop.
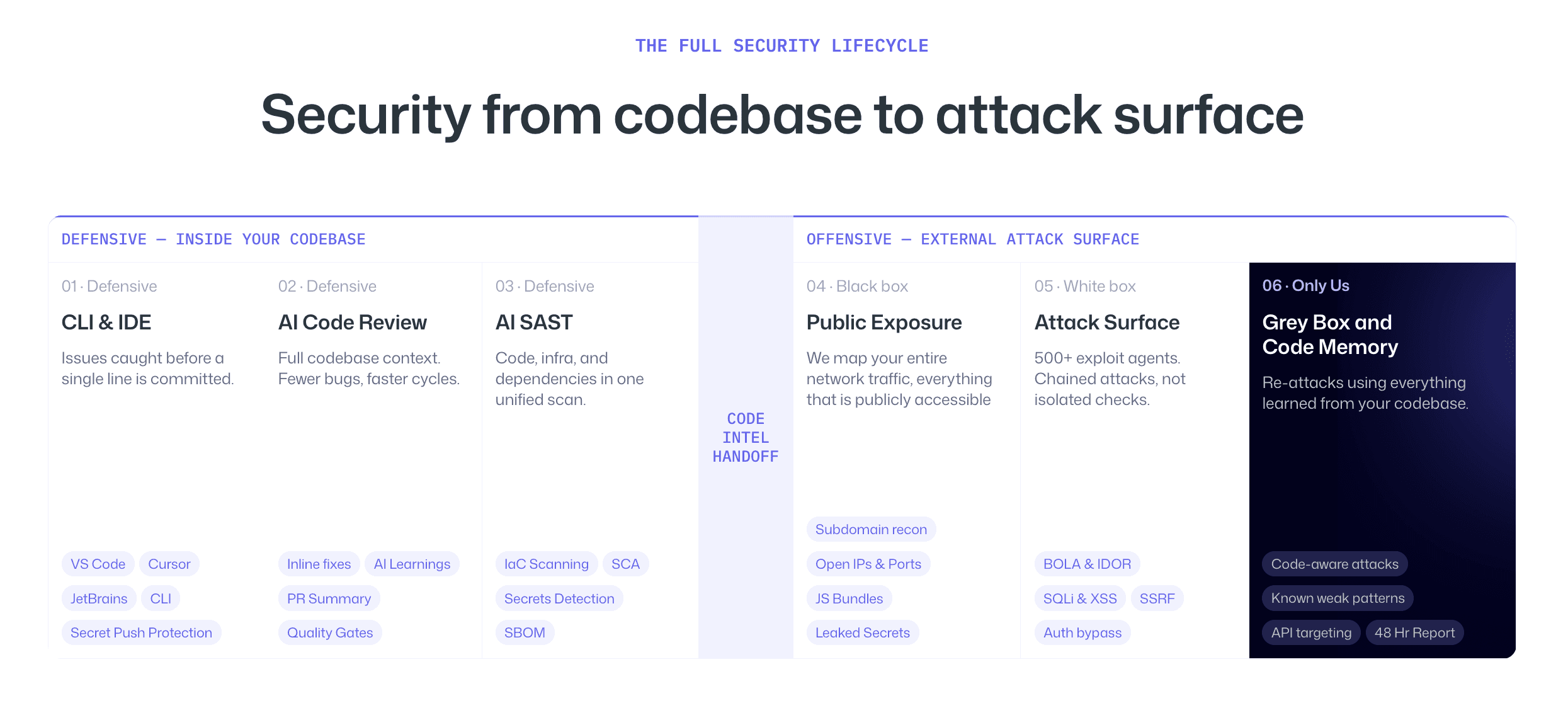
It helps developers catch security and quality issues while they write code and as changes move through CI/CD. Then, instead of stopping at defensive analysis, it uses that code understanding to guide offensive testing against the live external surface.
For a startup, this matters because the same risky pattern can be seen from both sides:
In code before it ships
In production after it is exposed
In the exploit chain if it becomes attackable
In the fix when engineering remediates it
In the retest when proof is needed
That is a much better fit for startups than separate tools that never talk to each other.
CodeAnt is strongest when the startup needs to move from “we found possible issues” to “we know what is exploitable and we fixed it.”
When AI Pentesting Is Not Enough
AI pentesting is powerful, but startups should avoid overclaiming.
It may not fully replace:
Deep manual business logic review
Red team exercises
Hardware testing
Mobile reverse engineering
Physical security testing
Highly specialized cryptography review
Complex social engineering simulations
AI pentesting is best when used for continuous, repeatable, evidence-driven validation across code, cloud, APIs, and web applications. For highly sensitive systems, combine AI-assisted testing with expert manual review.
Conclusion: Startups Need AI Pentesting When Security Must Keep Up With Growth
Startups do not need AI penetration testing because it is trendy.
They need it when their product, customers, compliance requirements, and cloud attack surface are moving faster than traditional security testing can follow.
For a modern SaaS startup, the right AI pentest should validate real exploitability across APIs, authentication, tenant isolation, cloud infrastructure, CI/CD, and external exposure. It should also provide proof-of-exploit, remediation guidance, retesting, and evidence that helps with SOC 2 and customer reviews.
CodeAnt fits this need by connecting defensive code intelligence with offensive validation. It helps teams catch risky patterns before they ship, test exposed systems after deployment, and prove whether fixes worked.
If your startup is preparing for SOC 2, selling to enterprise customers, or shipping faster than your current security process can test, start by evaluating your attack surface with a platform that can prevent, validate, and retest risk in one workflow.
FAQs
Do Startups Need AI Penetration Testing?
Is AI Penetration Testing Better Than Manual Pentesting For Startups?
When Should A Startup Get Its First Pentest?
What Should AI Pentesting Cover For A SaaS Startup?
How Long Does An AI Pentest Take For A Startup?